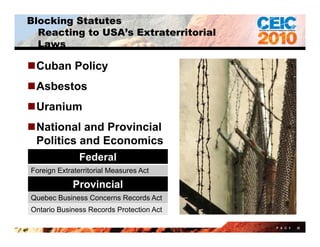
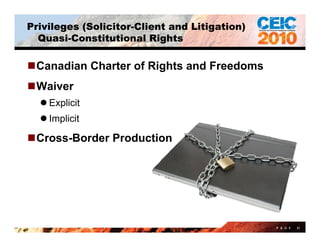
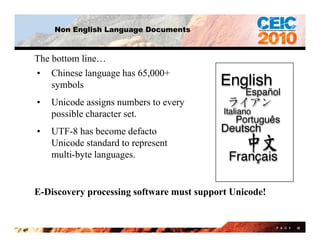
The panel discussed international eDiscovery issues including differing privacy standards and blocking statutes across jurisdictions, trends toward increased privacy protections in the US and Europe, and practical challenges of cross-border eDiscovery such as dealing with non-English languages and legacy IT systems. Proportionality, risk mitigation strategies, and continued communication were presented as ways to address these challenges.






















![Non English Language Documents
Printable ASCII Characters
0123456789abcdefg
hIjklmnopqrstuvwx
yz
ABCDEFGHIJKLM
NOPQRSTUVWXYZ
~ ! @ # $ % ^ & * ( ) _ + ` -= =
[ ] { } | ; ’: ” , . / < > ?
P A G E 36](https://image.slidesharecdn.com/ceic2010internationalpanel-100601143701-phpapp02/85/CEIC-2010-international-panel-37-320.jpg)


















![Privacy in Hong Kong
Two sources of privacy protection
Personal Data (Privacy) Ordinance
Common law (generally applies only to information which has the necessary quality of
confidence, was imparted in confidence, and used without authorization to the detriment of the
party communicating it (Coco v AN Clark (Engineers) Ltd. [1969] RPC 41).
Under Personal Data (Privacy Ordinance), “personal data” is defined as any data
(a) relating directly or indirectly to a living individual,
(b) from which it is practicable for the identity of the individual to be directly or indirectly
ascertained, and
(c) in a form in which access to or processing or use of the data is practicable.
The use of personal data (including collection, processing and transfer) must be
consistent with the purpose for which the data were originally collected or
directly related to it, otherwise the prior consent of the employee must be sought
and obtained.
Beware a newly enacted section 33 of the Privacy Ordinance – which may not yet
be in force – which prohibits the transfer of personal data outside Hong Kong
and unclear if consent overcomes that.
P A G E 66](https://image.slidesharecdn.com/ceic2010internationalpanel-100601143701-phpapp02/85/CEIC-2010-international-panel-67-320.jpg)