CdaSpirometryTestStandardization - May_Hl7InternationalNews
•
0 likes•228 views
Articulo sobre el estándar de información médica CDA R2 de espirometría forzada desarrollado por el CCI y la OFSTI, publicado en la edición de mayo del 2011 en la revista HL7 Internacional.
Report
Share
Report
Share
Download to read offline
Recommended
May HL7 News - Cda spirometry tests standardizations

This document discusses the standardization of spirometry test data using Clinical Document Architecture (CDA) R2. It details the creation of a CDA R2 data model and implementation guide for spirometry tests by a multidisciplinary team. The goal is to normalize spirometry data formats from different devices to improve integration with hospital information systems and interoperability. The first implementation of the CDA R2 spirometry standard integrated data from two manufacturer devices into an open-source integration framework called EI2Med. Pilot projects are underway to validate the standardization and integration of spirometry tests.
Articulo CDA Spirometry Tests Standardization (explanation implementation) ...

Articulo realizado para la revista de HL7 Europa, donde se explica como se esta implementando el CDA R2 de espirometria (diseñado por la Oficina de Estandares e Interoperabilidad) a nivel de los diferentes centros de Cataluña.
System for monitoring electro-medical equipment installed at home

The technology concerns a remote monitoring system for electromedical devices installed in a patient's home that includes a series of functional modules coupled to at least one electromedical device, capable of detecting the operating status of the device
Manel domingo forum_cis - jornada interoperabilidad - pcd

Presentación expuesta durante la ponencia realizada en el Jornada de Interoperabilidad de IHE del 18/04/2012 en Barcelona.
Antilope_CatalanInteroperabilityStateOfTheArt_ManelDomingo

The document discusses Catalonia's system for approving healthcare systems, devices, and services for interoperability. It aims to improve quality of care, make information management more competitive, and efficiently exchange information by integrating devices and systems. This requires setting standards for interoperability and an approval process. The Office of Standards and Interoperability manages the certification process to validate that systems meet requirements and reduce costs and risks while boosting confidence in solutions.
IOT BASED HEALTH MONITORING SYSTEM FOR COVID 19 PATIENT

This document describes an Internet of Things (IoT)-based health monitoring system for COVID-19 patients. The system measures patients' pulse rate, body temperature, and oxygen saturation using sensors connected to an Arduino Uno microcontroller. These vital signs are displayed on an LCD screen and sent to a mobile app for remote monitoring. The system was tested on 5 human subjects and was able to quickly obtain and store health data. Compared to other systems, this IoT-based approach could be very useful for monitoring COVID-19 patients during the ongoing pandemic. It allows for remote patient monitoring which can help reduce costs and free up hospital space for more critical cases.
IRJET- A Novel Survey to Secure Medical Images in Cloud using Digital Wat...

This document proposes a novel technique that combines encryption and digital watermarking to securely transmit medical images over public networks like the cloud. The algorithm divides images into regions of interest and non-interest, and embeds cryptographic watermarks and patient data in the non-interest regions before transmission. At the receiver end, the watermarks and data can be extracted to authenticate the image and verify that it has not been tampered with. The algorithm was tested on medical images and provided security, integrity and authenticity of transmitted medical information.
Health Informatics- Module 2-Chapter 2.pptx

Medical Information Structuring: Analysing and Designing Structure of healthcare information systems, Architectures of Information Systems.
Recommended
May HL7 News - Cda spirometry tests standardizations

This document discusses the standardization of spirometry test data using Clinical Document Architecture (CDA) R2. It details the creation of a CDA R2 data model and implementation guide for spirometry tests by a multidisciplinary team. The goal is to normalize spirometry data formats from different devices to improve integration with hospital information systems and interoperability. The first implementation of the CDA R2 spirometry standard integrated data from two manufacturer devices into an open-source integration framework called EI2Med. Pilot projects are underway to validate the standardization and integration of spirometry tests.
Articulo CDA Spirometry Tests Standardization (explanation implementation) ...

Articulo realizado para la revista de HL7 Europa, donde se explica como se esta implementando el CDA R2 de espirometria (diseñado por la Oficina de Estandares e Interoperabilidad) a nivel de los diferentes centros de Cataluña.
System for monitoring electro-medical equipment installed at home

The technology concerns a remote monitoring system for electromedical devices installed in a patient's home that includes a series of functional modules coupled to at least one electromedical device, capable of detecting the operating status of the device
Manel domingo forum_cis - jornada interoperabilidad - pcd

Presentación expuesta durante la ponencia realizada en el Jornada de Interoperabilidad de IHE del 18/04/2012 en Barcelona.
Antilope_CatalanInteroperabilityStateOfTheArt_ManelDomingo

The document discusses Catalonia's system for approving healthcare systems, devices, and services for interoperability. It aims to improve quality of care, make information management more competitive, and efficiently exchange information by integrating devices and systems. This requires setting standards for interoperability and an approval process. The Office of Standards and Interoperability manages the certification process to validate that systems meet requirements and reduce costs and risks while boosting confidence in solutions.
IOT BASED HEALTH MONITORING SYSTEM FOR COVID 19 PATIENT

This document describes an Internet of Things (IoT)-based health monitoring system for COVID-19 patients. The system measures patients' pulse rate, body temperature, and oxygen saturation using sensors connected to an Arduino Uno microcontroller. These vital signs are displayed on an LCD screen and sent to a mobile app for remote monitoring. The system was tested on 5 human subjects and was able to quickly obtain and store health data. Compared to other systems, this IoT-based approach could be very useful for monitoring COVID-19 patients during the ongoing pandemic. It allows for remote patient monitoring which can help reduce costs and free up hospital space for more critical cases.
IRJET- A Novel Survey to Secure Medical Images in Cloud using Digital Wat...

This document proposes a novel technique that combines encryption and digital watermarking to securely transmit medical images over public networks like the cloud. The algorithm divides images into regions of interest and non-interest, and embeds cryptographic watermarks and patient data in the non-interest regions before transmission. At the receiver end, the watermarks and data can be extracted to authenticate the image and verify that it has not been tampered with. The algorithm was tested on medical images and provided security, integrity and authenticity of transmitted medical information.
Health Informatics- Module 2-Chapter 2.pptx

Medical Information Structuring: Analysing and Designing Structure of healthcare information systems, Architectures of Information Systems.
Telemedicine Circuits Based On Standards

The document discusses Medting, a new online platform for sharing medical images and cases. Medting allows physicians and researchers to exchange clinical content for purposes like peer review, teaching, and second opinions. It provides tools for organizing content and connecting clinicians worldwide. The founders believe Medting can help improve healthcare by facilitating collaboration and the spread of medical knowledge through collective sharing of images and cases.
Hl7 news 201105051

A la pàgina 3 es pot llegir l'article "CDA: Spirometry Test Standardization" escrit per Manel Domingo i Matias Lizana del CCI.
Generation of cda xml schema from dicom images using hl7 standard 2

This document discusses generating CDA/XML schemas from DICOM images using the HL7 standard. It describes how HL7 CDA can be used to interface DICOM and HL7 formats. The process involves extracting data from DICOM images stored in a PACS archive, generating CDA-XML documents from the extracted data, and transmitting patient information summaries using HL7 messages. The research aims to improve interoperability between medical software applications and enable sharing of patient data.
IRJET- An Information Forwarder for Healthcare Service and analysis using Big...

This document proposes a system for collecting and analyzing healthcare big data using cloud computing. It discusses how healthcare data is growing rapidly in volume and variety due to data from various sources like sensors, and how traditional storage and processing may not be suitable. The proposed system has three layers - a data acquisition layer to collect data from sensors, a transmission layer to send the data to the cloud, and a computational layer in the cloud to analyze and classify the data using clustering and fuzzy rule-based classifiers. This would allow real-time remote healthcare by efficiently storing and processing the large amounts of heterogeneous healthcare data in the cloud. Evaluation metrics like response time, accuracy, cost and false positives are used to compare the proposed system to existing techniques.
The Cloud Computing Approach for Secured Health Maintenance Record of Patient...

This document describes a cloud-based system for securely storing and accessing patient health records. The system uses attribute-based encryption techniques to encrypt health records when stored in the cloud. When patients or doctors need access to records, they generate attribute tokens that allow decrypting relevant encrypted records. The system aims to improve healthcare access in rural areas by allowing records to be accessed remotely via the cloud without losing security. It outlines the system architecture involving companies that store records, a cloud server to host records, a semi-trusted authority that generates keys, and clients (patients and doctors).
IoT Based Patient Monitoring System

This document describes an IoT-based patient monitoring system that collects a patient's vital signs like heartbeat, temperature, ECG, oxygen level, and other data using sensors. The data is sent to a cloud platform called ThingSpeak and can be accessed through a mobile application. This allows medical staff to remotely monitor patients in real-time. Key benefits of the system include reduced errors, decreased costs by reducing visits, better patient experience through continuous monitoring, and ability to provide quick treatment if abnormalities are detected. The system uses a NodeMCU microcontroller along with sensors like a pulse oximeter, temperature sensor, and ECG sensor to collect and transmit the health data.
IRJET - Review on Classi?cation and Prediction of Dengue and Malaria Dise...

1. The document reviews machine learning algorithms for classifying and predicting malaria and dengue diseases based on patient symptoms and blood cell images. It proposes a system using Naive Bayes for classification based on symptoms and Convolutional Neural Network (CNN) for image-based classification of blood cell images.
2. The system architecture takes in patient symptom and image data, uses Naive Bayes to classify based on symptoms, then uses CNN on blood cell images to confirm the disease prediction as malaria or dengue.
3. The proposed system aims to provide fast and accurate prediction of diseases with similar symptoms like malaria and dengue using machine learning algorithms instead of traditional methods for improved diagnosis.
IRJET- A Survey on-Security for using Pervasive Healthcare Monitoring Sys...

This document discusses security issues in using mobile cloud computing for pervasive healthcare monitoring systems. It first introduces how mobile devices and cloud computing are being used to remotely monitor patient health metrics. However, transmitting sensitive patient data over networks poses security and privacy risks. The document then examines different approaches for securing such systems, including using encryption keys for authentication and communication protection between wireless sensor nodes, hospitals, and mobile apps. It also discusses challenges in securing data and devices across the various tiers of healthcare cloud and mobile computing architectures. Overall, the document analyzes how security can be improved for remote mobile healthcare monitoring systems that leverage cloud-based approaches.
Research Journal

All submitted research articles are subjected to immediate rapid screening by the editors, in consultation with the Editorial Board or others working in the field as appropriate, to ensure they are likely to be of the level of interest and importance appropriate for the journal. ijerst offers a fast publication schedule whilst maintaining rigorous peer review; the use of recommended electronic formats for article delivery expedites the process.
Paper Publication

IJERST offers a fast publication schedule whilst maintaining rigorous peer review; the use of recommended electronic formats for article delivery expedites the process. International Journal of Engineering Research and Science & Technology (IJERST) is an international online journal in English published Quarterly. All submitted research articles are subjected to immediate rapid screening by the editors, in consultation with the Editorial Board or others working in the field as appropriate, to ensure they are likely to be of the level of interest and importance appropriate for the journal.
peer reviewed journals 

scope of a journal in the field of Information Technology and Computer Engineering. This journal accepts various types of articles, including research articles, review articles, and short communications.
Dicom 2010[1]![Dicom 2010[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Dicom 2010[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
DICOM is a standard for handling, storing, transmitting and printing medical imaging information. It defines a file format and network communication protocol to allow integration of imaging systems from different manufacturers into a PACS. DICOM facilitates interoperability between medical devices by specifying protocols, commands, information that can be exchanged and storage services for medical images and related data. The goals are compatibility between systems and improved workflow efficiency in healthcare.
IRJET- Hiding Sensitive Medical Data using Encryption

This document summarizes a research paper about securely hiding sensitive medical data using encryption. The paper proposes a system that distributes a patient's data across multiple encrypted data servers. It uses Paillier cryptosystems to allow statistical analysis of the encrypted patient data without compromising privacy. The system includes wireless medical sensors that monitor patients and transmit encrypted data to a database. It uses an access control system and statistical analysis protocols that employ Paillier encryption to allow authorized users like doctors to access and analyze the encrypted patient data without revealing its contents. The goal is to protect sensitive medical information from privacy breaches while still enabling useful analysis of aggregated patient data.
Dynamic Medical Machine

This document describes a dynamic medical machine that is deployed in rural areas without easy access to doctors. The machine contains sensors like a temperature sensor, heart rate sensor, and ultrasonic sensor to monitor patients' vital signs. It is connected to a doctor via video and audio calls to allow virtual consultations. Based on the doctor's diagnosis and prescription, the machine automatically dispenses the appropriate medicines to the patient. This aims to make healthcare more accessible for common illnesses in remote locations while reducing costs.
Real-time Heart Pulse Monitoring Technique Using Wireless Sensor Network and ...

This summarizes a document describing a real-time heart pulse monitoring system using a wireless sensor network and mobile application. The proposed system measures a patient's heart pulse using an infrared sensor. It then amplifies and filters the signal before sending it over a network using an Arduino board and Ethernet shield. The heart pulse values are displayed on both a computer-based and smartphone-based application in real-time. The system was tested on 10 people of varying ages, genders, and health statuses, and the results were within normal heart pulse ranges according to medical standards.
A FRAMEWORK FOR THE INTERCONNECTION OF CONTROLLER AREA NETWORK (CAN) BASED CR...

Patient monitoring helps increasing the mortality by timely notification of exceeding vital signs. By using the vital sign data the critical care staff can make necessary life saving interventions. This requires the underlying network to be very robust so that timely and error free information flow can be guaranteed. Moreover there is a need for a cost effective and robust network technology for continuous and real- time vital signs monitoring in resource constraint settings in developing countries. In this paper we proposed a system of hospitals with interconnected intensive care units. Each intensive care unit employs Controller Area Network (CAN) as underlying technology for networking of bedside units. The data of these bedside units can be communicated with other hospital using higher level protocols such as Ethernet. This allow the hospital staff to share the health information of the patients with the specialized staff in another hospital to provide better cure to the patient and consequently can increase the mortality.
Exploring information exchange opportunities between Industry and the TGA

The TGA is undertaking a Business Improvement Program to update their systems and processes. As part of this, they are starting an Adverse Event Management project to improve how adverse event reports are collected, processed, and analyzed for medicines, vaccines, and medical devices. They outlined the current reporting systems, volumes and formats, and are seeking industry input on capabilities and needs to help design new reporting formats that meet stakeholder and international standards. Interested parties can register for the project by email.
UG 2016 Final Project.pdf

This document discusses utilizing common information models to integrate distribution software in utilities. It describes how utilities traditionally used separate "siloed" software applications that were difficult to integrate. Two strategies for improvement are outlined: 1) using a common integration platform for all software interfaces, and 2) reducing the number of applications by standardizing on a small set of vendor solutions. Adopting a common information model can simplify the process of mapping data between different software applications by providing a standardized framework.
A Proposed Security Architecture for Establishing Privacy Domains in Systems ...

Information and communication technology (ICT) are becoming a natural part in healthcare. Instead of keeping patient information inside a written file, you can find all information stored in an organized database as well defined files using a specific system in almost every hospital. But those files sometimes got lost or information was split up in files in different hospitals or different departments so no one could see the whole picture from this point we come up with our idea. One of this paper targets is to keep that information available on the cloud so doctors and nurses can have an access to patient record everywhere, so patient history will be clear which helps doctors in giving the right decision. We present security architecture for establishing privacy domains in e-Health bases. In this case, we will improve the availability of medical data and provide the ability for patients to moderate their medical data. Moreover, e-Health system in cloud computing has more than one component to be attacked. The other target of this paper is to distinguish between different kinds of attackers and we point out several shortcomings of current e-Health solutions and standards, particularly they do not address the client platform security, which is a crucial aspect for the overall security of systems in cloud. To fill this gap, we present security architecture for establishing privacy domains in e-Health infrastructures. Our solution provides client platform security and appropriately combines this with network security concepts.
Secret key generation

1) The document proposes a three-stage cryptographic model to securely transmit secret keys generated from a patient's ECG signal for authentication of implanted medical devices (IMDs).
2) In the first stage, a 128-bit secret key is generated from the patient's ECG signal and encrypted with it.
3) In the second stage, the encrypted ECG signal is hidden inside an image using steganography.
4) In the third stage, the image is watermarked for identification before transmission between the IMD and medical practitioner's system. This provides security against eavesdropping, spoofing, and avoids pre-sharing secret keys.
InforSalud 2014 - Marcos de Interoperabilidad su relevancia en la normalizac...

Comunicación realizada para InforSalud 2014 respecto la relevancia de la existencia y el diseño de los marcos de interoperabilidad basados en estándares de información médica. Cuyo objetivo es obtener procesos asistenciales modelados y un entorno sanitario normalizado.
InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...

InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...Manel Domingo Falcón
El documento describe el marco de interoperabilidad WIFIS diseñado para facilitar la gestión telemática de procesos asistenciales entre centros sanitarios públicos y privados en Cataluña. WIFIS define procesos clínicos como derivaciones y citas basados en estándares como HL7 para permitir la comunicación interoperable entre sistemas. Se ha aplicado con éxito entre el Hospital Comarcal Sant Jaume y CETIR, y actualmente se implementa en MC MUTUAL para comunicarse con proveedores. El objetivo es establecer un estándar queMore Related Content
Similar to CdaSpirometryTestStandardization - May_Hl7InternationalNews
Telemedicine Circuits Based On Standards

The document discusses Medting, a new online platform for sharing medical images and cases. Medting allows physicians and researchers to exchange clinical content for purposes like peer review, teaching, and second opinions. It provides tools for organizing content and connecting clinicians worldwide. The founders believe Medting can help improve healthcare by facilitating collaboration and the spread of medical knowledge through collective sharing of images and cases.
Hl7 news 201105051

A la pàgina 3 es pot llegir l'article "CDA: Spirometry Test Standardization" escrit per Manel Domingo i Matias Lizana del CCI.
Generation of cda xml schema from dicom images using hl7 standard 2

This document discusses generating CDA/XML schemas from DICOM images using the HL7 standard. It describes how HL7 CDA can be used to interface DICOM and HL7 formats. The process involves extracting data from DICOM images stored in a PACS archive, generating CDA-XML documents from the extracted data, and transmitting patient information summaries using HL7 messages. The research aims to improve interoperability between medical software applications and enable sharing of patient data.
IRJET- An Information Forwarder for Healthcare Service and analysis using Big...

This document proposes a system for collecting and analyzing healthcare big data using cloud computing. It discusses how healthcare data is growing rapidly in volume and variety due to data from various sources like sensors, and how traditional storage and processing may not be suitable. The proposed system has three layers - a data acquisition layer to collect data from sensors, a transmission layer to send the data to the cloud, and a computational layer in the cloud to analyze and classify the data using clustering and fuzzy rule-based classifiers. This would allow real-time remote healthcare by efficiently storing and processing the large amounts of heterogeneous healthcare data in the cloud. Evaluation metrics like response time, accuracy, cost and false positives are used to compare the proposed system to existing techniques.
The Cloud Computing Approach for Secured Health Maintenance Record of Patient...

This document describes a cloud-based system for securely storing and accessing patient health records. The system uses attribute-based encryption techniques to encrypt health records when stored in the cloud. When patients or doctors need access to records, they generate attribute tokens that allow decrypting relevant encrypted records. The system aims to improve healthcare access in rural areas by allowing records to be accessed remotely via the cloud without losing security. It outlines the system architecture involving companies that store records, a cloud server to host records, a semi-trusted authority that generates keys, and clients (patients and doctors).
IoT Based Patient Monitoring System

This document describes an IoT-based patient monitoring system that collects a patient's vital signs like heartbeat, temperature, ECG, oxygen level, and other data using sensors. The data is sent to a cloud platform called ThingSpeak and can be accessed through a mobile application. This allows medical staff to remotely monitor patients in real-time. Key benefits of the system include reduced errors, decreased costs by reducing visits, better patient experience through continuous monitoring, and ability to provide quick treatment if abnormalities are detected. The system uses a NodeMCU microcontroller along with sensors like a pulse oximeter, temperature sensor, and ECG sensor to collect and transmit the health data.
IRJET - Review on Classi?cation and Prediction of Dengue and Malaria Dise...

1. The document reviews machine learning algorithms for classifying and predicting malaria and dengue diseases based on patient symptoms and blood cell images. It proposes a system using Naive Bayes for classification based on symptoms and Convolutional Neural Network (CNN) for image-based classification of blood cell images.
2. The system architecture takes in patient symptom and image data, uses Naive Bayes to classify based on symptoms, then uses CNN on blood cell images to confirm the disease prediction as malaria or dengue.
3. The proposed system aims to provide fast and accurate prediction of diseases with similar symptoms like malaria and dengue using machine learning algorithms instead of traditional methods for improved diagnosis.
IRJET- A Survey on-Security for using Pervasive Healthcare Monitoring Sys...

This document discusses security issues in using mobile cloud computing for pervasive healthcare monitoring systems. It first introduces how mobile devices and cloud computing are being used to remotely monitor patient health metrics. However, transmitting sensitive patient data over networks poses security and privacy risks. The document then examines different approaches for securing such systems, including using encryption keys for authentication and communication protection between wireless sensor nodes, hospitals, and mobile apps. It also discusses challenges in securing data and devices across the various tiers of healthcare cloud and mobile computing architectures. Overall, the document analyzes how security can be improved for remote mobile healthcare monitoring systems that leverage cloud-based approaches.
Research Journal

All submitted research articles are subjected to immediate rapid screening by the editors, in consultation with the Editorial Board or others working in the field as appropriate, to ensure they are likely to be of the level of interest and importance appropriate for the journal. ijerst offers a fast publication schedule whilst maintaining rigorous peer review; the use of recommended electronic formats for article delivery expedites the process.
Paper Publication

IJERST offers a fast publication schedule whilst maintaining rigorous peer review; the use of recommended electronic formats for article delivery expedites the process. International Journal of Engineering Research and Science & Technology (IJERST) is an international online journal in English published Quarterly. All submitted research articles are subjected to immediate rapid screening by the editors, in consultation with the Editorial Board or others working in the field as appropriate, to ensure they are likely to be of the level of interest and importance appropriate for the journal.
peer reviewed journals 

scope of a journal in the field of Information Technology and Computer Engineering. This journal accepts various types of articles, including research articles, review articles, and short communications.
Dicom 2010[1]![Dicom 2010[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Dicom 2010[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
DICOM is a standard for handling, storing, transmitting and printing medical imaging information. It defines a file format and network communication protocol to allow integration of imaging systems from different manufacturers into a PACS. DICOM facilitates interoperability between medical devices by specifying protocols, commands, information that can be exchanged and storage services for medical images and related data. The goals are compatibility between systems and improved workflow efficiency in healthcare.
IRJET- Hiding Sensitive Medical Data using Encryption

This document summarizes a research paper about securely hiding sensitive medical data using encryption. The paper proposes a system that distributes a patient's data across multiple encrypted data servers. It uses Paillier cryptosystems to allow statistical analysis of the encrypted patient data without compromising privacy. The system includes wireless medical sensors that monitor patients and transmit encrypted data to a database. It uses an access control system and statistical analysis protocols that employ Paillier encryption to allow authorized users like doctors to access and analyze the encrypted patient data without revealing its contents. The goal is to protect sensitive medical information from privacy breaches while still enabling useful analysis of aggregated patient data.
Dynamic Medical Machine

This document describes a dynamic medical machine that is deployed in rural areas without easy access to doctors. The machine contains sensors like a temperature sensor, heart rate sensor, and ultrasonic sensor to monitor patients' vital signs. It is connected to a doctor via video and audio calls to allow virtual consultations. Based on the doctor's diagnosis and prescription, the machine automatically dispenses the appropriate medicines to the patient. This aims to make healthcare more accessible for common illnesses in remote locations while reducing costs.
Real-time Heart Pulse Monitoring Technique Using Wireless Sensor Network and ...

This summarizes a document describing a real-time heart pulse monitoring system using a wireless sensor network and mobile application. The proposed system measures a patient's heart pulse using an infrared sensor. It then amplifies and filters the signal before sending it over a network using an Arduino board and Ethernet shield. The heart pulse values are displayed on both a computer-based and smartphone-based application in real-time. The system was tested on 10 people of varying ages, genders, and health statuses, and the results were within normal heart pulse ranges according to medical standards.
A FRAMEWORK FOR THE INTERCONNECTION OF CONTROLLER AREA NETWORK (CAN) BASED CR...

Patient monitoring helps increasing the mortality by timely notification of exceeding vital signs. By using the vital sign data the critical care staff can make necessary life saving interventions. This requires the underlying network to be very robust so that timely and error free information flow can be guaranteed. Moreover there is a need for a cost effective and robust network technology for continuous and real- time vital signs monitoring in resource constraint settings in developing countries. In this paper we proposed a system of hospitals with interconnected intensive care units. Each intensive care unit employs Controller Area Network (CAN) as underlying technology for networking of bedside units. The data of these bedside units can be communicated with other hospital using higher level protocols such as Ethernet. This allow the hospital staff to share the health information of the patients with the specialized staff in another hospital to provide better cure to the patient and consequently can increase the mortality.
Exploring information exchange opportunities between Industry and the TGA

The TGA is undertaking a Business Improvement Program to update their systems and processes. As part of this, they are starting an Adverse Event Management project to improve how adverse event reports are collected, processed, and analyzed for medicines, vaccines, and medical devices. They outlined the current reporting systems, volumes and formats, and are seeking industry input on capabilities and needs to help design new reporting formats that meet stakeholder and international standards. Interested parties can register for the project by email.
UG 2016 Final Project.pdf

This document discusses utilizing common information models to integrate distribution software in utilities. It describes how utilities traditionally used separate "siloed" software applications that were difficult to integrate. Two strategies for improvement are outlined: 1) using a common integration platform for all software interfaces, and 2) reducing the number of applications by standardizing on a small set of vendor solutions. Adopting a common information model can simplify the process of mapping data between different software applications by providing a standardized framework.
A Proposed Security Architecture for Establishing Privacy Domains in Systems ...

Information and communication technology (ICT) are becoming a natural part in healthcare. Instead of keeping patient information inside a written file, you can find all information stored in an organized database as well defined files using a specific system in almost every hospital. But those files sometimes got lost or information was split up in files in different hospitals or different departments so no one could see the whole picture from this point we come up with our idea. One of this paper targets is to keep that information available on the cloud so doctors and nurses can have an access to patient record everywhere, so patient history will be clear which helps doctors in giving the right decision. We present security architecture for establishing privacy domains in e-Health bases. In this case, we will improve the availability of medical data and provide the ability for patients to moderate their medical data. Moreover, e-Health system in cloud computing has more than one component to be attacked. The other target of this paper is to distinguish between different kinds of attackers and we point out several shortcomings of current e-Health solutions and standards, particularly they do not address the client platform security, which is a crucial aspect for the overall security of systems in cloud. To fill this gap, we present security architecture for establishing privacy domains in e-Health infrastructures. Our solution provides client platform security and appropriately combines this with network security concepts.
Secret key generation

1) The document proposes a three-stage cryptographic model to securely transmit secret keys generated from a patient's ECG signal for authentication of implanted medical devices (IMDs).
2) In the first stage, a 128-bit secret key is generated from the patient's ECG signal and encrypted with it.
3) In the second stage, the encrypted ECG signal is hidden inside an image using steganography.
4) In the third stage, the image is watermarked for identification before transmission between the IMD and medical practitioner's system. This provides security against eavesdropping, spoofing, and avoids pre-sharing secret keys.
Similar to CdaSpirometryTestStandardization - May_Hl7InternationalNews (20)
Generation of cda xml schema from dicom images using hl7 standard 2

Generation of cda xml schema from dicom images using hl7 standard 2
IRJET- An Information Forwarder for Healthcare Service and analysis using Big...

IRJET- An Information Forwarder for Healthcare Service and analysis using Big...
The Cloud Computing Approach for Secured Health Maintenance Record of Patient...

The Cloud Computing Approach for Secured Health Maintenance Record of Patient...
IRJET - Review on Classi?cation and Prediction of Dengue and Malaria Dise...

IRJET - Review on Classi?cation and Prediction of Dengue and Malaria Dise...
IRJET- A Survey on-Security for using Pervasive Healthcare Monitoring Sys...

IRJET- A Survey on-Security for using Pervasive Healthcare Monitoring Sys...
IRJET- Hiding Sensitive Medical Data using Encryption

IRJET- Hiding Sensitive Medical Data using Encryption
Real-time Heart Pulse Monitoring Technique Using Wireless Sensor Network and ...

Real-time Heart Pulse Monitoring Technique Using Wireless Sensor Network and ...
A FRAMEWORK FOR THE INTERCONNECTION OF CONTROLLER AREA NETWORK (CAN) BASED CR...

A FRAMEWORK FOR THE INTERCONNECTION OF CONTROLLER AREA NETWORK (CAN) BASED CR...
Exploring information exchange opportunities between Industry and the TGA

Exploring information exchange opportunities between Industry and the TGA
A Proposed Security Architecture for Establishing Privacy Domains in Systems ...

A Proposed Security Architecture for Establishing Privacy Domains in Systems ...
More from Manel Domingo Falcón
InforSalud 2014 - Marcos de Interoperabilidad su relevancia en la normalizac...

Comunicación realizada para InforSalud 2014 respecto la relevancia de la existencia y el diseño de los marcos de interoperabilidad basados en estándares de información médica. Cuyo objetivo es obtener procesos asistenciales modelados y un entorno sanitario normalizado.
InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...

InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...Manel Domingo Falcón
El documento describe el marco de interoperabilidad WIFIS diseñado para facilitar la gestión telemática de procesos asistenciales entre centros sanitarios públicos y privados en Cataluña. WIFIS define procesos clínicos como derivaciones y citas basados en estándares como HL7 para permitir la comunicación interoperable entre sistemas. Se ha aplicado con éxito entre el Hospital Comarcal Sant Jaume y CETIR, y actualmente se implementa en MC MUTUAL para comunicarse con proveedores. El objetivo es establecer un estándar queInforSalud 2013 - Gobernanza Interoperabilidad CPS - Manel Domingo

La Carpeta Personal de Salud de Cataluña (CPS) proporciona acceso a los registros médicos de los ciudadanos y servicios relacionados con la salud. Se diseñó un marco de interoperabilidad para garantizar que los servicios externos se comuniquen de manera normalizada con la CPS. El marco incluye perfiles de identificación, comunicación, publicación y portabilidad que los servicios deben cumplir para integrarse a la CPS de forma homologada. Actualmente, servicios de empresas como Roche, Medical Guard y Sanofi están disponibles a
InforSalud 2011 - Presentación EI2Med - Manel Domingo

Presentación realizada en InforSalud 2011, respecto el entorno de integración de software libre EI2Med, desarrollado en el Centro de Competencias de Integración.
EI2Med es un entorno de integración orientado a integrar procesos asistenciales a través de dispositivos médicos, que gracias a EI2Med podrán comunicarse con cualquier sistema de información mediante estándares de información médica.
InforSalud 2011 - ENTORNO ABIERTO DE INTEGRACION DE SERVICIOS PARA PROCESOS A...

InforSalud 2011 - ENTORNO ABIERTO DE INTEGRACION DE SERVICIOS PARA PROCESOS A...Manel Domingo Falcón
Comunicación realizada en InforSalud 2011, respecto el entorno de integración de software libre EI2Med, desarrollado en el Centro de Competencias de Integración.
EI2Med es un entorno de integración orientado a integrar procesos asistenciales a través de dispositivos médicos, que gracias a EI2Med podrán comunicarse con cualquier sistema de información mediante estándares de información médica.
InforSalud 2014 - Marcos de Interoperabilidad y WIFIS - Manel Domingo

Este documento describe la importancia de los marcos de interoperabilidad para la normalización de los entornos sanitarios. Explica cómo los marcos modelan procesos asistenciales utilizando estándares de información médica y establecen reglas de negocio y roles. Además, resume la experiencia positiva del marco WIFIS en Cataluña, que ha demostrado ahorros de costes y mayor eficiencia en la gestión de procesos como derivaciones y citas entre centros.
More from Manel Domingo Falcón (6)
InforSalud 2014 - Marcos de Interoperabilidad su relevancia en la normalizac...

InforSalud 2014 - Marcos de Interoperabilidad su relevancia en la normalizac...
InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...

InforSalud 2014 - Comunicación Wifis, marco de interoperabilidad aplicable al...
InforSalud 2013 - Gobernanza Interoperabilidad CPS - Manel Domingo

InforSalud 2013 - Gobernanza Interoperabilidad CPS - Manel Domingo
InforSalud 2011 - Presentación EI2Med - Manel Domingo

InforSalud 2011 - Presentación EI2Med - Manel Domingo
InforSalud 2011 - ENTORNO ABIERTO DE INTEGRACION DE SERVICIOS PARA PROCESOS A...

InforSalud 2011 - ENTORNO ABIERTO DE INTEGRACION DE SERVICIOS PARA PROCESOS A...
InforSalud 2014 - Marcos de Interoperabilidad y WIFIS - Manel Domingo

InforSalud 2014 - Marcos de Interoperabilidad y WIFIS - Manel Domingo
Recently uploaded
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/temporal-event-neural-networks-a-more-efficient-alternative-to-the-transformer-a-presentation-from-brainchip/
Chris Jones, Director of Product Management at BrainChip , presents the “Temporal Event Neural Networks: A More Efficient Alternative to the Transformer” tutorial at the May 2024 Embedded Vision Summit.
The expansion of AI services necessitates enhanced computational capabilities on edge devices. Temporal Event Neural Networks (TENNs), developed by BrainChip, represent a novel and highly efficient state-space network. TENNs demonstrate exceptional proficiency in handling multi-dimensional streaming data, facilitating advancements in object detection, action recognition, speech enhancement and language model/sequence generation. Through the utilization of polynomial-based continuous convolutions, TENNs streamline models, expedite training processes and significantly diminish memory requirements, achieving notable reductions of up to 50x in parameters and 5,000x in energy consumption compared to prevailing methodologies like transformers.
Integration with BrainChip’s Akida neuromorphic hardware IP further enhances TENNs’ capabilities, enabling the realization of highly capable, portable and passively cooled edge devices. This presentation delves into the technical innovations underlying TENNs, presents real-world benchmarks, and elucidates how this cutting-edge approach is positioned to revolutionize edge AI across diverse applications.5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
dbms calicut university B. sc Cs 4th sem.pdf

Its a seminar ppt on database management system using sql
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Azure API Management to expose backend services securely

How to use Azure API Management to expose backend service securely
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Inconsistent user experience and siloed data, high costs, and changing customer expectations – Citizens Bank was experiencing these challenges while it was attempting to deliver a superior digital banking experience for its clients. Its core banking applications run on the mainframe and Citizens was using legacy utilities to get the critical mainframe data to feed customer-facing channels, like call centers, web, and mobile. Ultimately, this led to higher operating costs (MIPS), delayed response times, and longer time to market.
Ever-changing customer expectations demand more modern digital experiences, and the bank needed to find a solution that could provide real-time data to its customer channels with low latency and operating costs. Join this session to learn how Citizens is leveraging Precisely to replicate mainframe data to its customer channels and deliver on their “modern digital bank” experiences.
AWS Cloud Cost Optimization Presentation.pptx

This presentation provides valuable insights into effective cost-saving techniques on AWS. Learn how to optimize your AWS resources by rightsizing, increasing elasticity, picking the right storage class, and choosing the best pricing model. Additionally, discover essential governance mechanisms to ensure continuous cost efficiency. Whether you are new to AWS or an experienced user, this presentation provides clear and practical tips to help you reduce your cloud costs and get the most out of your budget.
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

Predictive maintenance is a proactive approach that anticipates equipment failures before they happen. At the forefront of this innovative strategy is Artificial Intelligence (AI), which brings unprecedented precision and efficiency. AI in predictive maintenance is transforming industries by reducing downtime, minimizing costs, and enhancing productivity.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI, built on the robust SAP Business Technology Platform (SAP BTP), is the latest and most advanced version of our AI development, reaffirming our commitment to delivering top-tier AI solutions. Skybuffer AI harnesses all the innovative capabilities of the SAP BTP in the AI domain, from Conversational AI to cutting-edge Generative AI and Retrieval-Augmented Generation (RAG). It also helps SAP customers safeguard their investments into SAP Conversational AI and ensure a seamless, one-click transition to SAP Business AI.
With Skybuffer AI, various AI models can be integrated into a single communication channel such as Microsoft Teams. This integration empowers business users with insights drawn from SAP backend systems, enterprise documents, and the expansive knowledge of Generative AI. And the best part of it is that it is all managed through our intuitive no-code Action Server interface, requiring no extensive coding knowledge and making the advanced AI accessible to more users.
System Design Case Study: Building a Scalable E-Commerce Platform - Hiike

This case study explores designing a scalable e-commerce platform, covering key requirements, system components, and best practices.
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
Recently uploaded (20)
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...
WeTestAthens: Postman's AI & Automation Techniques

WeTestAthens: Postman's AI & Automation Techniques
JavaLand 2024: Application Development Green Masterplan

JavaLand 2024: Application Development Green Masterplan
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Azure API Management to expose backend services securely

Azure API Management to expose backend services securely
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe
leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...

leewayhertz.com-AI in predictive maintenance Use cases technologies benefits ...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...
System Design Case Study: Building a Scalable E-Commerce Platform - Hiike

System Design Case Study: Building a Scalable E-Commerce Platform - Hiike
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Dandelion Hashtable: beyond billion requests per second on a commodity server

Dandelion Hashtable: beyond billion requests per second on a commodity server
CdaSpirometryTestStandardization - May_Hl7InternationalNews
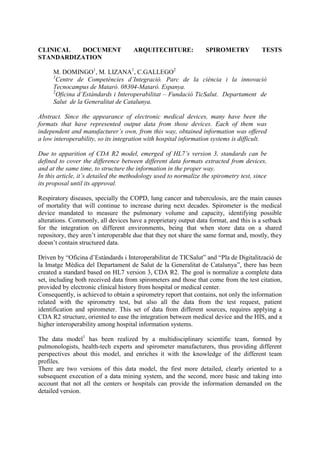
- 1. CLINICAL DOCUMENT ARQUITECHTURE: SPIROMETRY TESTS STANDARDIZATION M. DOMINGO1, M. LIZANA1, C.GALLEGO2 1 Centre de Competències d’Integració. Parc de la ciència i la innovació Tecnocampus de Mataró. 08304-Mataró. Espanya. 2 Oficina d’Estàndards i Interoperabilitat – Fundació TicSalut. Departament de Salut de la Generalitat de Catalunya. Abstract. Since the appearance of electronic medical devices, many have been the formats that have represented output data from those devices. Each of them was independent and manufacturer’s own, from this way, obtained information was offered a low interoperability, so its integration with hospital information systems is difficult. Due to apparition of CDA R2 model, emerged of HL7’s version 3, standards can be defined to cover the difference between different data formats extracted from devices, and at the same time, to structure the information in the proper way. In this article, it’s detailed the methodology used to normalize the spirometry test, since its proposal until its approval. Respiratory diseases, specially the COPD, lung cancer and tuberculosis, are the main causes of mortality that will continue to increase during next decades. Spirometer is the medical device mandated to measure the pulmonary volume and capacity, identifying possible alterations. Commonly, all devices have a proprietary output data format, and this is a setback for the integration on different environments, being that when store data on a shared repository, they aren’t interoperable due that they not share the same format and, mostly, they doesn’t contain structured data. Driven by “Oficina d’Estàndards i Interoperabilitat de TICSalut” and “Pla de Digitalització de la Imatge Mèdica del Departament de Salut de la Generalitat de Catalunya”, there has been created a standard based on HL7 version 3, CDA R2. The goal is normalize a complete data set, including both received data from spirometers and those that come from the test citation, provided by electronic clinical history from hospital or medical center. Consequently, is achieved to obtain a spirometry report that contains, not only the information related with the spirometry test, but also all the data from the test request, patient identification and spirometer. This set of data from different sources, requires applying a CDA R2 structure, oriented to ease the integration between medical device and the HIS, and a higher interoperability among hospital information systems. The data model1 has been realized by a multidisciplinary scientific team, formed by pulmonologists, health-tech experts and spirometer manufacturers, thus providing different perspectives about this model, and enriches it with the knowledge of the different team profiles. There are two versions of this data model, the first more detailed, clearly oriented to a subsequent execution of a data mining system, and the second, more basic and taking into account that not all the centers or hospitals can provide the information demanded on the detailed version.
- 2. After the data model generation, there are generated a set of normative and technological artifacts, to facilitate the standard implantation: CDA R2 Spirometry implementation guide2: Contains the norms to follow to implement CDA R2 correctly, with mandatoriness of each field, as well as its content. There have been realized two versions also from this guide, referred to both versions of data model. CDA R2 XML formatted templates: A set of CDA R2 spirometry templates, ready to be used in any implementation. There exist templates for both versions, basic and detailed. XSL Style sheet: File needed to visualize spirometry CDA R2, which follows a standard style sheet for CDA-HL7 presentation. Figure 1. Visualization of spirometry report CDA R2 Using spirometry CDA R2, allows that the resulting reports can be shared through different hospital HIS, and execute data mining services, that are very important for medical research processes. Also it’s important to note that the doctor can view the spirometry digitally, from his workstation, and watch the tests history for each patient. The first implantation of the CDA R2 spirometry standard has been done through an open- source integration framework called EI2Med, based on Mirth Connect, in which many tools have been developed to ease generation and integration between CDA R2 spirometry standard and HIS.
- 3. The manufacturers and spirometry models that have been integrated at the moment with the integration framework EI2Med, and that they have cooperate on this first spirometry standard implementation, are: “EasyOne” from NDD and “DatosSpir Micro A” from Sibel. Nowadays, are being carried out some pilot jobs in collaboration with different public hospitals of Catalonia, to validate the normalization and integration technology of the spirometry tests, to be approved shortly by “Oficina d’Estàndards i Interoperabilitat de TicSalut del Departament de Salut de la Generalitat de Catalunya”. Referencias [1] T. Salas, M. Domingo, y F. Burgos. Data model of the CDA R2 spirometry standard to the “Departament de Salut de la Generalitat de Catalunya”. 2010. [2] M. Domingo, M. Lizana y D. Kaminker. CDA R2 spirometry implementation guide to the “Departament de Salut de la Generalitat de Catalunya”. 2010.
