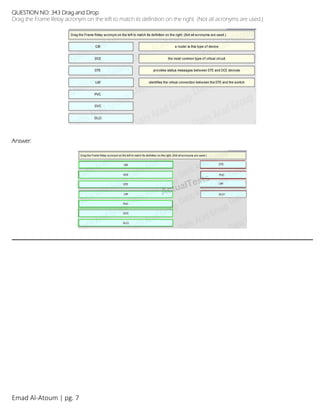
The document contains 341 multiple choice questions from the CCNA Routing & Switching 200-120 exam. The questions cover topics such as NAT, routing protocols, VLANs, IPv6, routing, switching, and network security. Sample questions ask about types of NAT addresses, the danger of permit any entries in NAT access lists, and protocols like HSRP, OSPF, EIGRP, and VRRP. The document is broken into 6 pages with explanations for some answers.