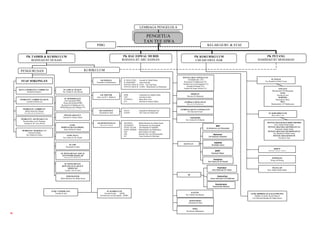
Carta organisasi1 pdf
- 1. LEMBAGA PENGELOLA PENGETUA TAN TEE HWA PIBG KELAB GURU & STAF PK TADBIR & KURIKULUM PK HAL EHWAL MURID PK KOKURIKULUM PK PETANG ROZINAH BT HUSAIN ROHANA BT ABU HASSAN CHEAM SWEE HAR HAMIDAH BT MOHAMAD PK KOKURIKULUM PENGURUSAN KURIKULUM DATIN CHEAM SWEE HAR PENYELARAS TINGKATAN Norrehabt Jani (T5) SU SUKAN GK BAHASA B. MALAYSIA : Fauziah bt Abdul Ghani STAF SOKONGAN Vasantha a/p Muthusamy B. INGGERIS : Anna Getrude Rozilawati bt Mahmood (T4) Nor Raudah bt Mohd Yunus PENYELARAS B. CINA: Lim Eng Seng Krishnaveny a/p Karuppiah (T3) PENYELARAS B. TAMIL: Muniammal a/p Batumalai Zuraida bt Osman (T2) Suriani Bt Zainal Abidin (T1) VINCENT KETUA PEMBANTU TADBIR N22 SU JADUAL WAKTU Muniammal A/P Batumalai Ramlah bt Hassan Nur Afizah bt Abu Hassan ANNE GK TEKVOK KHB : Arpannah a/p Appala Naidu DISIPLIN Mastura bt Mohamad Norreha bt Jani Anne a/p M.V. Mathews ERT : Norreha bt Jani MARTHA PEMBANTU TADBIR N22 (KUP) SU PEPERIKSAAN PA/PD/EA : Bong How Lian Hanimah bt Masri Lim Eng Seng (SPM) ICT : Harnida bt Zaman Zahari Latifah bt Mohd Nor LEMBAGA PENGAWAS PIUS Wang Jok Kheng (PMR) Mastura bt Mohamad Manimekalai A/P Muthusamy Rozilawati bt Mahmood (T4) Mohd Mazwan bin Othman (T2) PEMBANTU TADBIR N17 Nordalila bt Ismoi (T1) LEMBAGA KETUA TINGKATAN Mohd Najib bin Ahmad GK SAINS/MAT MATE :. Sarimah bt Mohamad Nor Siti Hasrina bt Sairi Nur Munira bt Mohd Nor Kamaliah bt Saad SAINS : Fitri Yanti bt Abdul Jalil SU KOKURIKULUM PENYELARAS ICT Bong How Lian Harnida bt Zaman Zahari SMM/BMM PEMBANTU AM PEJABAT N4 Nor Azlina bt Ab Razak Roselin Mary a/p S. Packiam Zarinah bt Ab. Aziz (KUP) GK KEMANUSIAAN SEJARAH : Mohd Muzlimi bin Mohd Junoh PENYELARAS BADAN BERUNIFORM GURU Suraya bt Zainal GEOGRAFI : Krishnaveny a/p Karuppiah Noor Zalida Mohd Zahari BKP PERPUSTAKAAN/MEDIA PEND. ISLAM : Siti Radziah bt Abdullah PENYELARAS KELAB PERSATUAN Krishnaveny a/p Karuppiah Arpannah Appala Naidu Intan Safinas bt Johari PEND. MORAL : Manimekalai a/p Muthusamy PEMBANTU MAKMAL C17 PENYELARAS KELAB PERMAINAN Nafisah bt Jaafar PSV Intan Safinas bt Johari PJK : Kamala Devi a/p Subramaniam Baitulmal Nor Raudah bt Mohd Yunus Nur Qistina bt Zamri GURU DATA PENYELARAS KOSTUM PS : Noor Fazillay bt Mat Said Siti Radziah Abdullah Nor Azlina bt Ab. Razab Norreha bt Jani KWAPM SU LDP BANTUAN Nordalila Ismoi Kamaliah bt Saad RIMUP SPBT Harnida Zaman Zahari SU PENGURUSAN ASET & Hanimah Masri INVENTORI SEKOLAH Munirah bt Mohd Nor KOPERASI Kebajikan Wang Jok Kheng Nor Azlina bt Ab Razab SU PENGURUSAN KEWANGAN & AKAUN SEKOLAH Kesihatan MAJALAH Latifah Nor bt Alias Ainil Shahnaz M. Sham Noor Zalida Mohd Zahari 3K WEB MASTER Kebersihan Mohd Muzlimi bin Mohd Junoh Anna Gertrude A.M Nathnan Keselamatan Sagunthala Maniam GURU CEMERLANG SU KURIKULUM Norreha bt Jani Norreha bt Jani (SPM) KANTIN GURU BIMBINGAN & KAUNSELING Krishnaveny a/p Karuppiah (PMR) Nur Afizah Abu Hassan Madiha @ Sarah Aisyah Mansor Cik Halwatul Raudha Bt Abdul Karim KEDAI BUKU Hanimah bt Masri PPDA Rozilawati Mahmmod se
