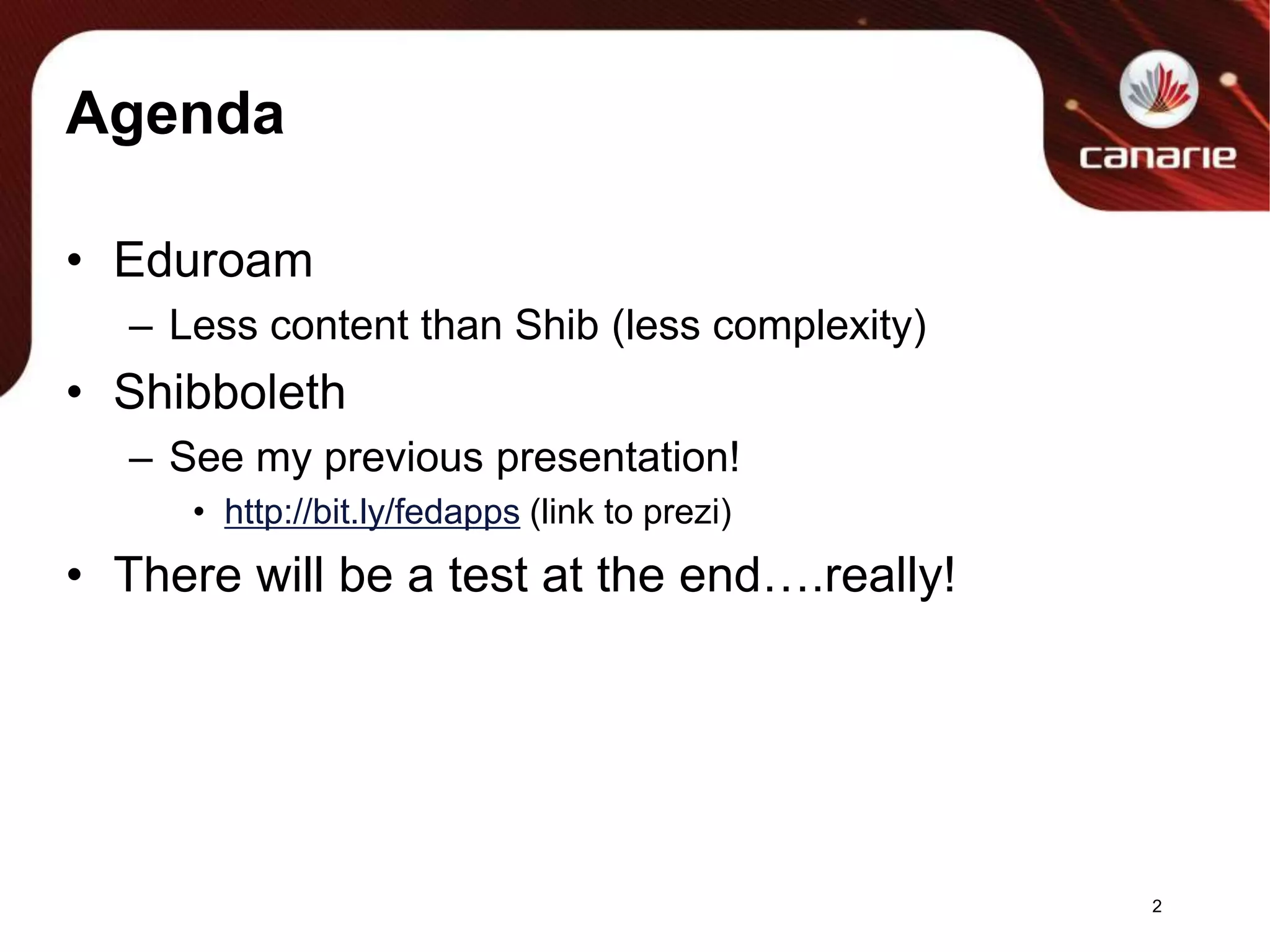
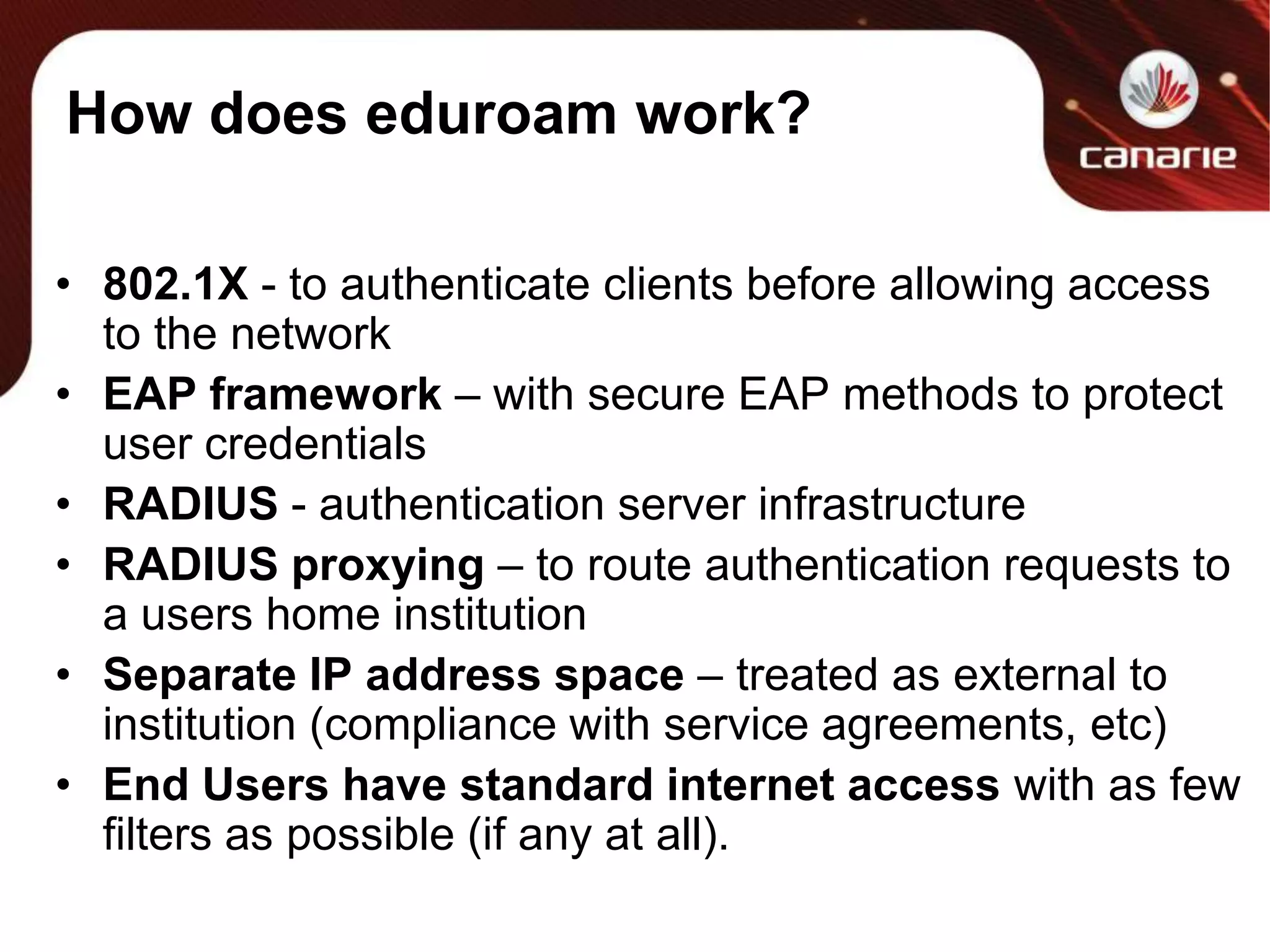
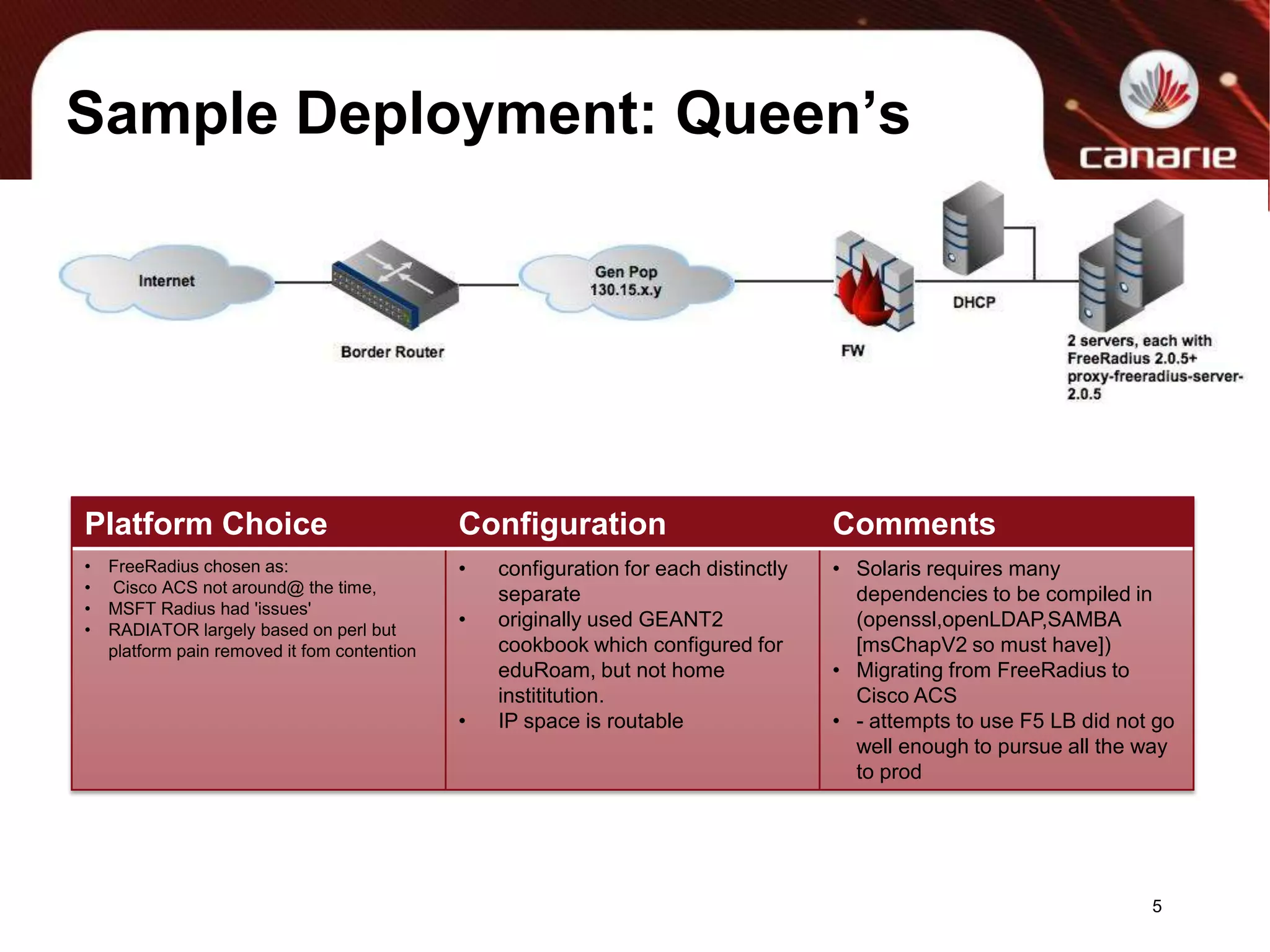
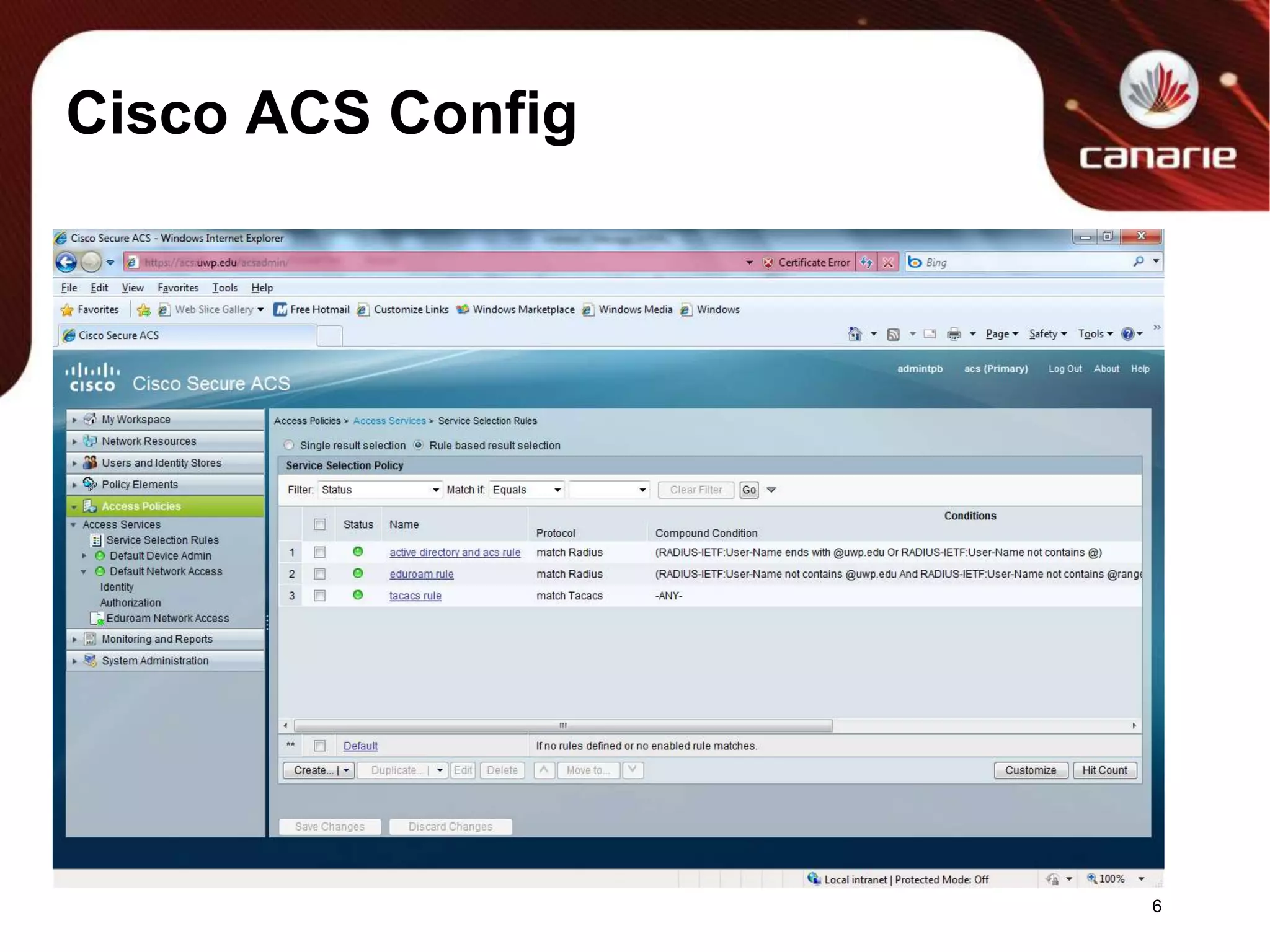
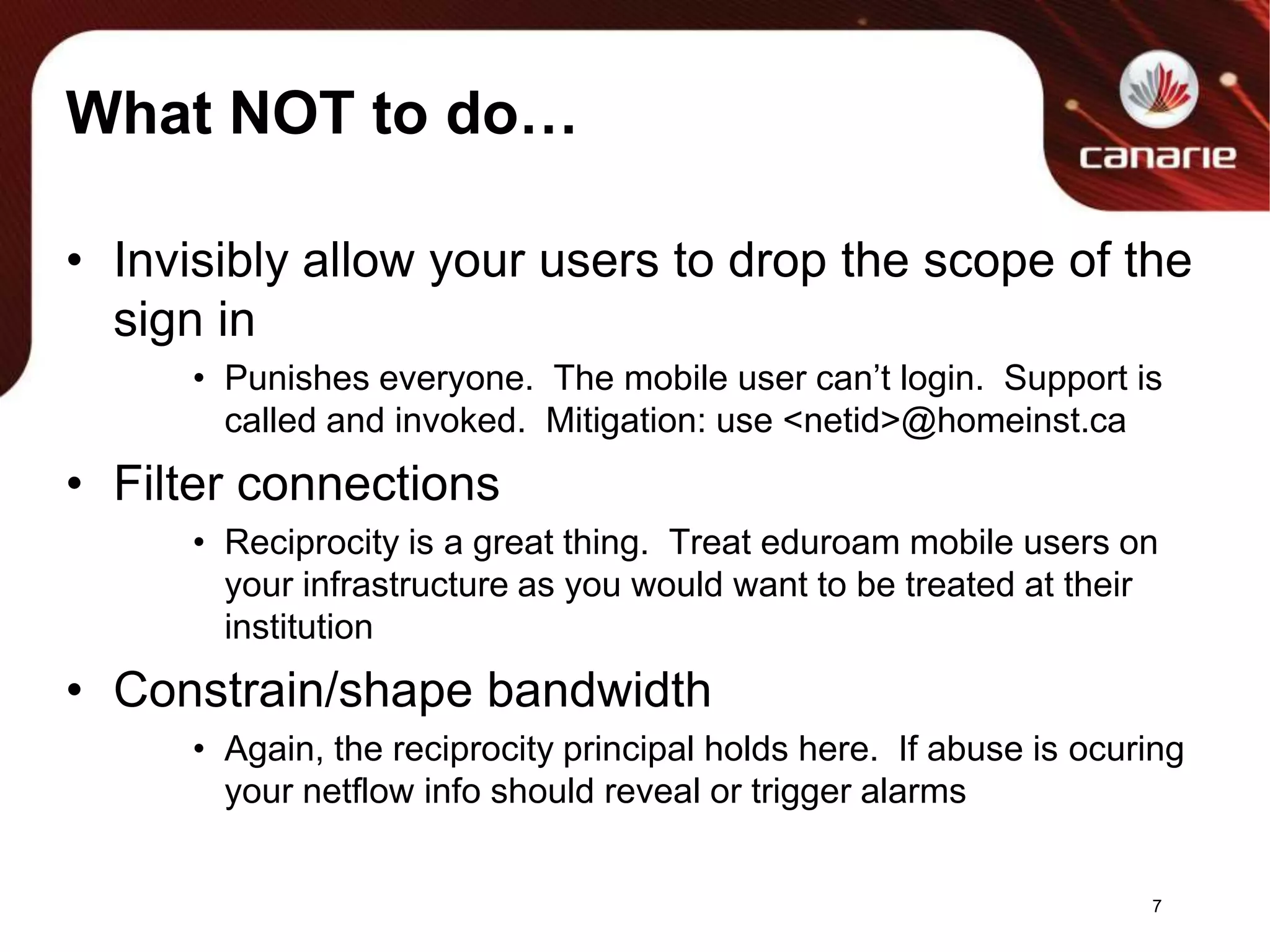
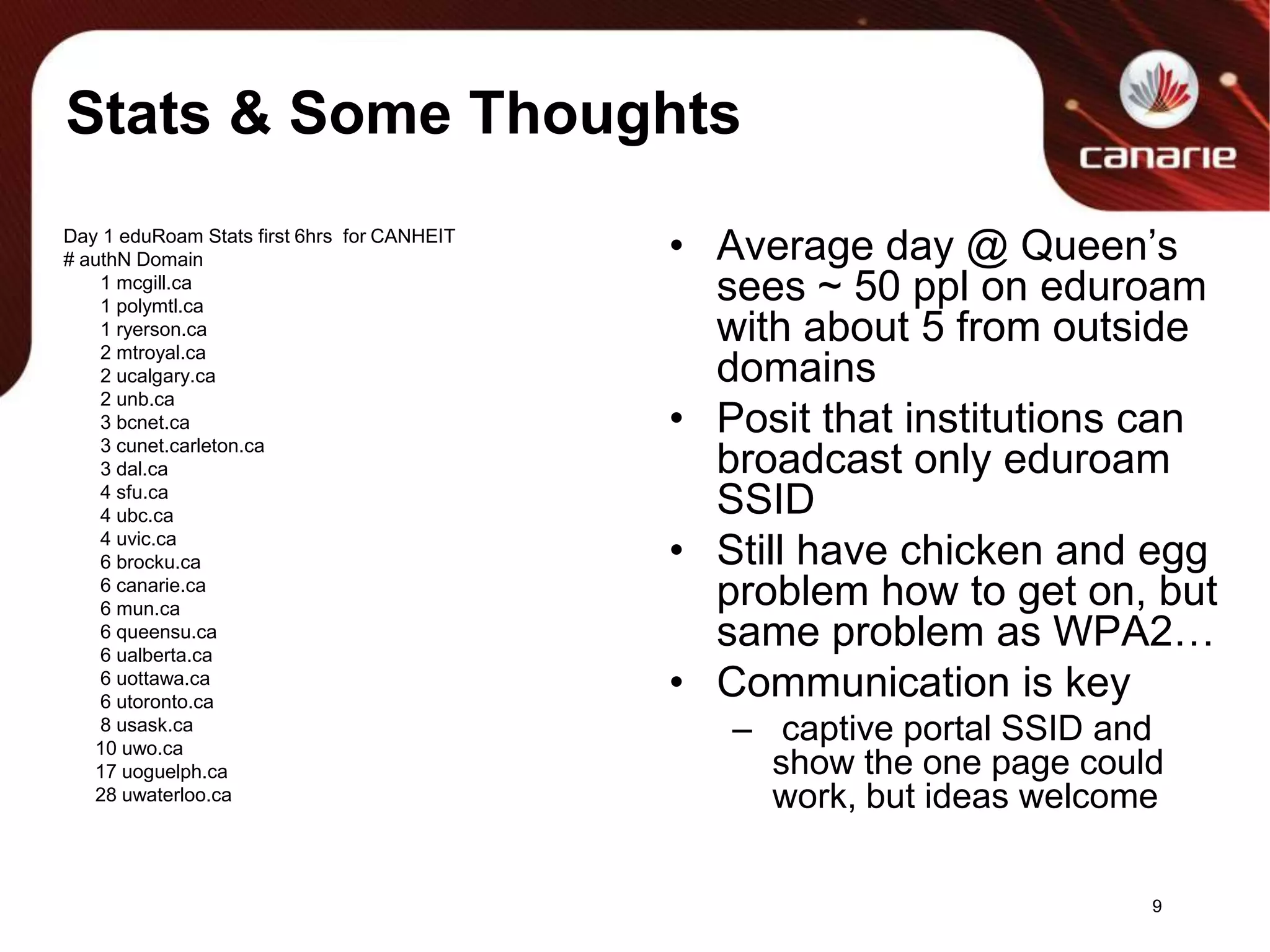
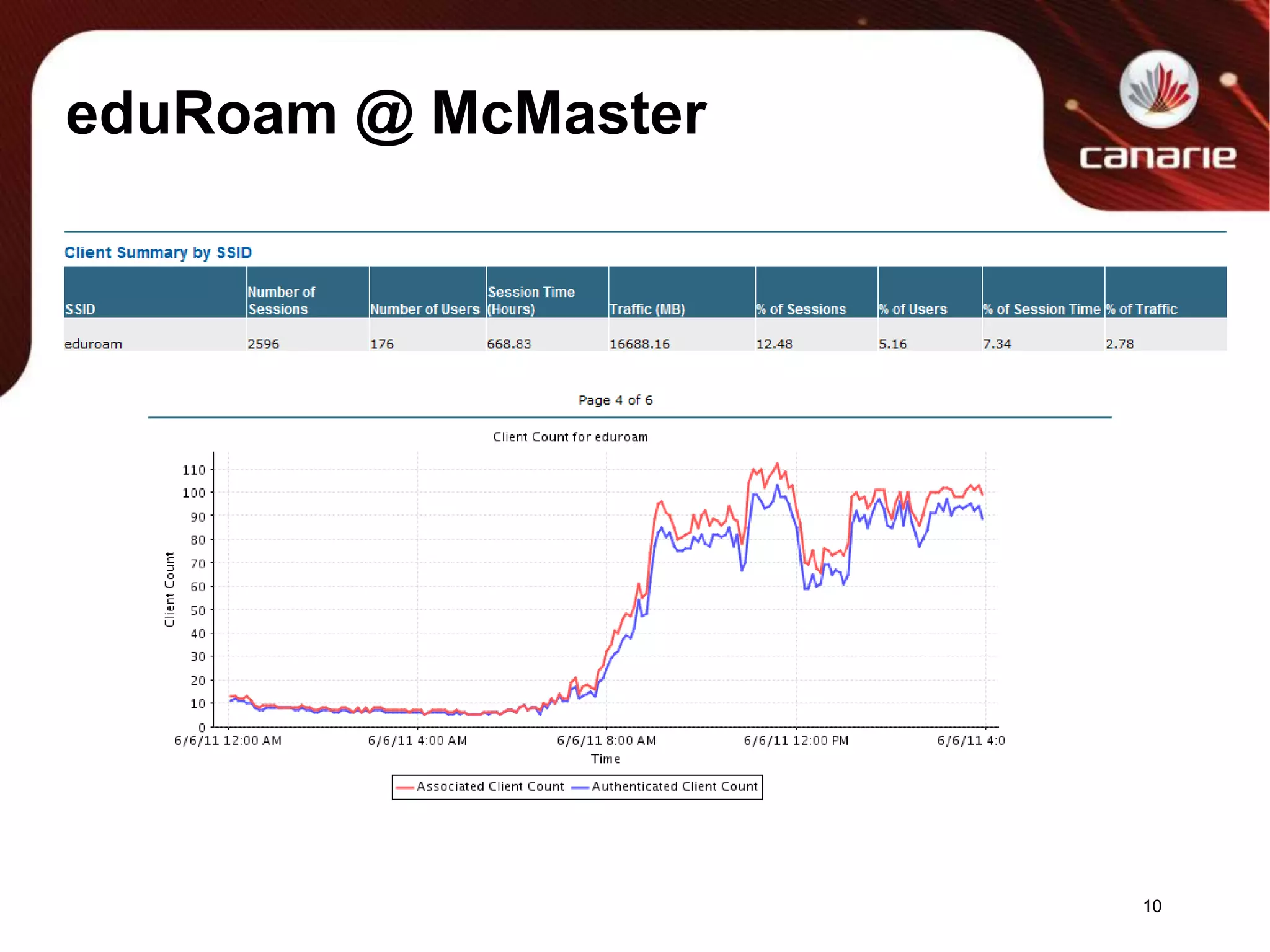
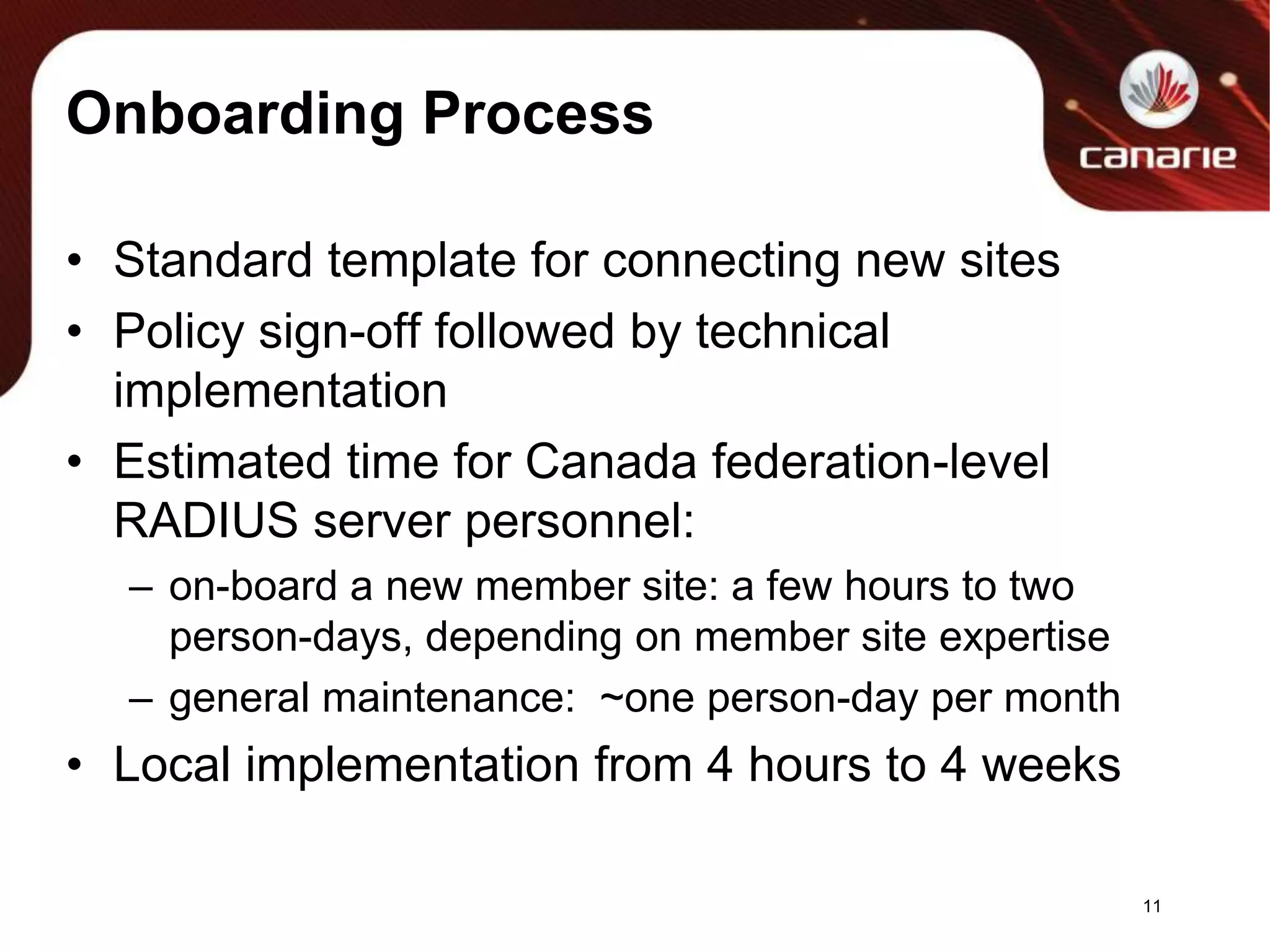
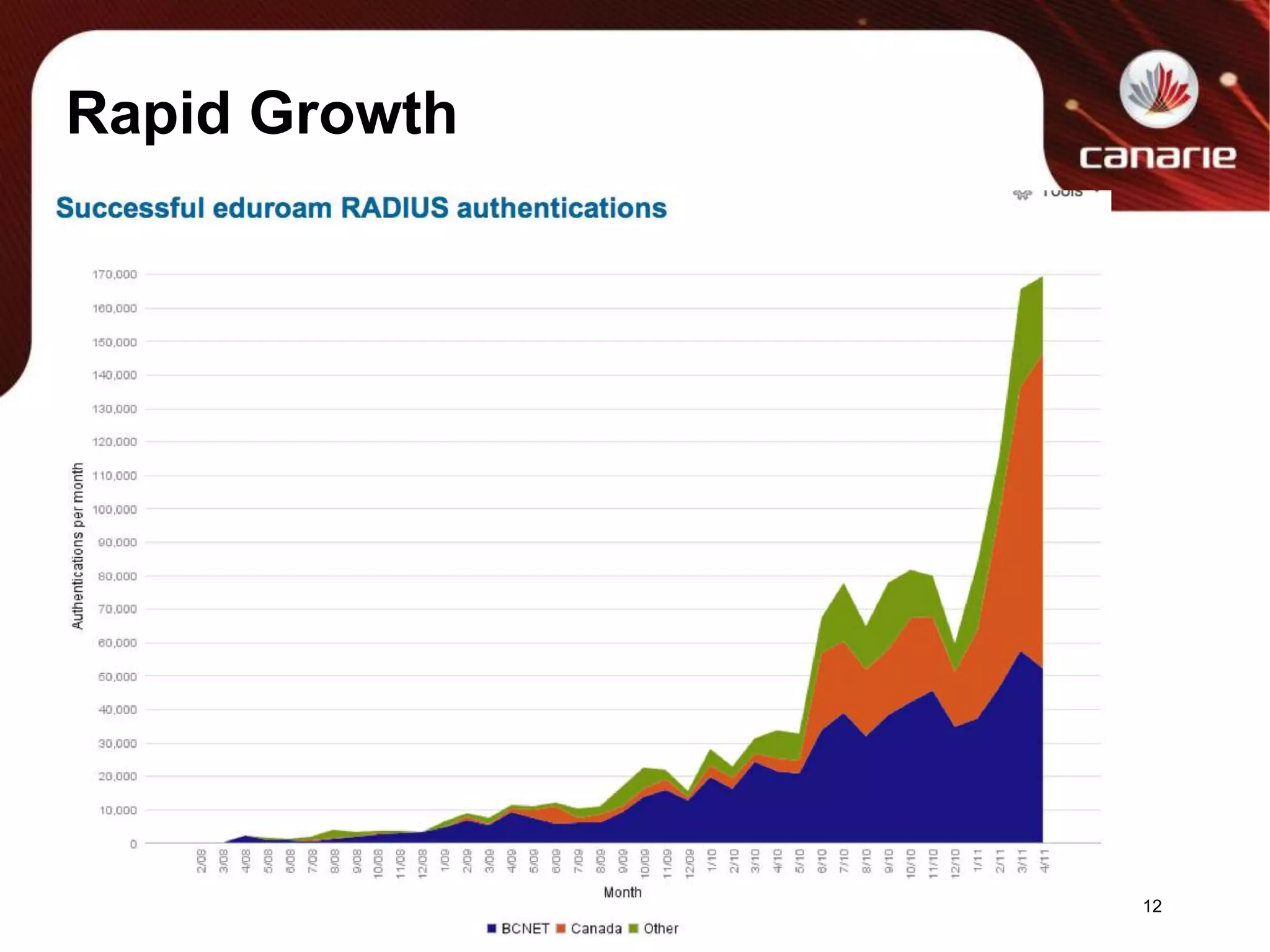
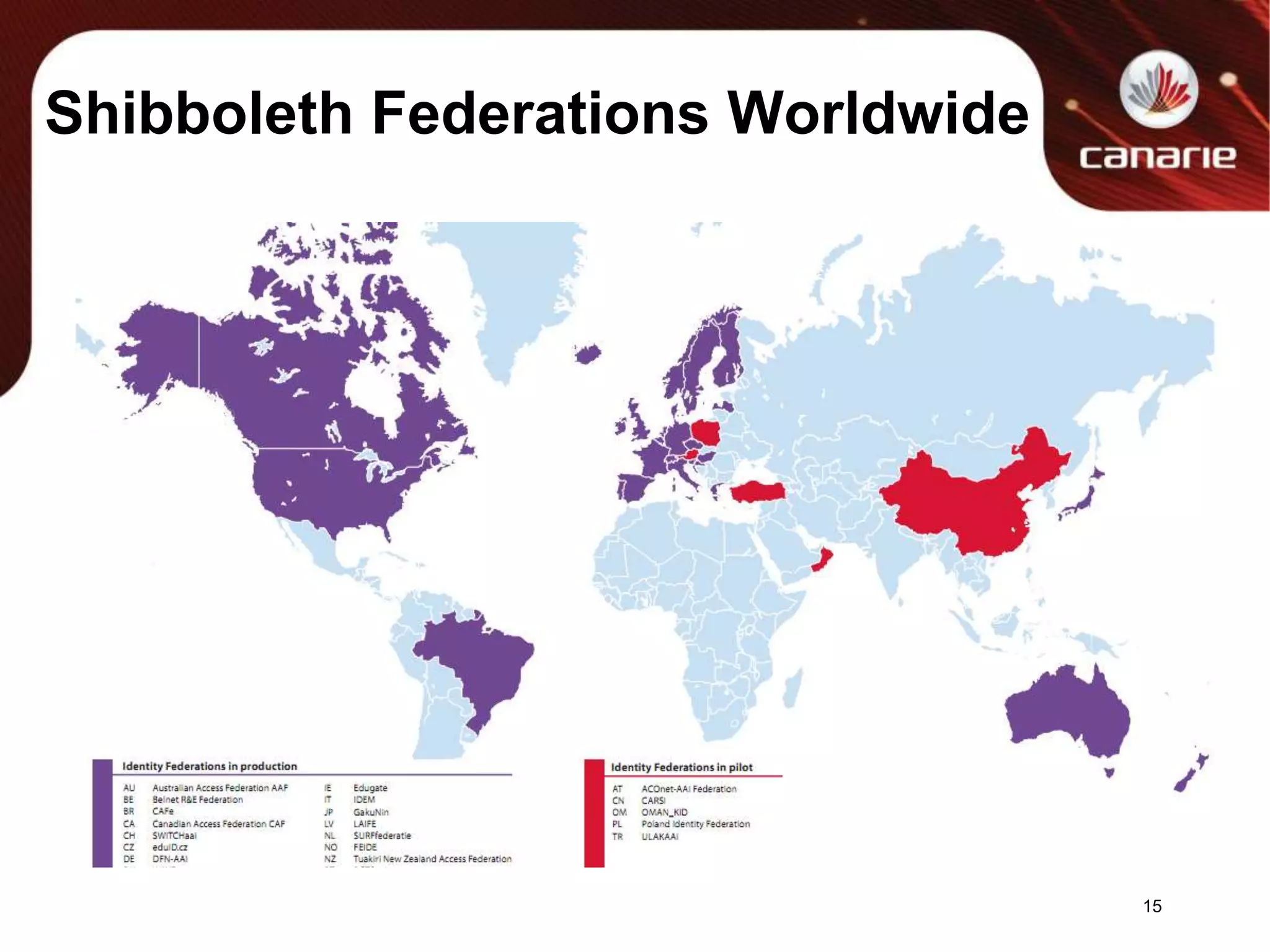
The document discusses eduroam and Shibboleth federations. It provides an overview of eduroam including how authentication works using 802.1X and RADIUS. Stats are presented on early eduroam usage in Canada. Recommendations are made for institutions implementing eduroam including not filtering or shaping bandwidth. Concerns around NATing are discussed. The onboarding process for new eduroam sites is outlined. Growth stats for eduroam in Canada and the US are presented. Questions about eduroam and Shibboleth federations are solicited from attendees.

![Virtual Organization pt 2CAF is an environment where VO’s flourish:Virtual Organizations typically form around Service Provider(s) with IdPs providing consumers & complying to attribute profiles to participateAutonomy is retained by the VO & it’s members to focus on the topic -CAF focus is on the ‘dialtone’ infrastructure for collaboration – IdP & Sp management practices and operations and middleware elements–Examples in Canada are:•Regional Learning Management Systems•Transcript or Application managementResearch 'desktops' that aggregate tools for researchersTechniques to implement on SP end:Use the Shib2.xml & other configurations to whitelist participants[1]Consider using eduPersonEntitlement to express fine grain filtering at the application level:eduPersonEntitlement: urn:mace:washington.edu:confocalMicroscopeeduPersonEntitlement: http://publisher.example.com/contract/GL12[1] https://wiki.shibboleth.net/confluence/display/SHIB2/NativeSPMetadataFilter20](https://image.slidesharecdn.com/canarie-20110531-canheit-110608121015-phpapp01/75/CANARIE-Eduroam-and-Shibboleth-Lessons-Areas-of-interest-20-2048.jpg)
![Enhancing Attribute ExchangesShared nothing today, but uses eduPerson schemaFinding that this may be paradox of choiceVery interesting space to explore, but keep in mind principles:Low friction to participate (ie, simplicity is good)Scalable and high degree of relevancy and utilityDon’t punish the end user or IdP owner.Interop across Canada and internationallyMany areas to exploreUse SHAC[1] technique for attributes?"urn:schac:dom.ain:Attribute:value”UseAustralian[2] approach for precise control and strong typing and vocabulary?Require full participation in various attribute sets (ie MUST populate all fields) but in different categories of SPs (category 1, 2,3 etc)?Hybrid??[1] http://www.terena.org/mail-archives/schac/msg00371.html[2] http://www.aaf.edu.au/technical/aaf-core-attributes/22](https://image.slidesharecdn.com/canarie-20110531-canheit-110608121015-phpapp01/75/CANARIE-Eduroam-and-Shibboleth-Lessons-Areas-of-interest-22-2048.jpg)
![My App Can’t Be Federated in CAF Because…I need to sign in Social identities (Google, OpenID)Reply: No problem, it can be doneAlready participating internationally with REFEDS & inCommon on Social Identity risk assessment and gateway designs[1]Certain gateways exist from uPenn & Sweden [2]Many unquantified risks at this time, but does workUser behind keyboard is unknownAttributes are self assertedNo knowledge of value of the account to the personThis is an active area of conversation.[1] https://spaces.internet2.edu/display/socialid/Using+SAML+and+Social+Identities--Guidelines+and+Considerations+for+Managers+and+Developers[2] https://tnc2011.terena.org/getfile/55825](https://image.slidesharecdn.com/canarie-20110531-canheit-110608121015-phpapp01/75/CANARIE-Eduroam-and-Shibboleth-Lessons-Areas-of-interest-25-2048.jpg)