BUS105 Needs Improvement (1) Satisfactory (2) Ex.docx
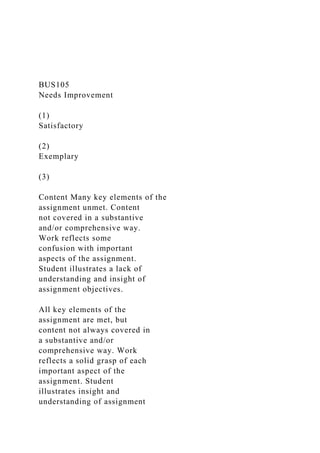
- 1. BUS105 Needs Improvement (1) Satisfactory (2) Exemplary (3) Content Many key elements of the assignment unmet. Content not covered in a substantive and/or comprehensive way. Work reflects some confusion with important aspects of the assignment. Student illustrates a lack of understanding and insight of assignment objectives. All key elements of the assignment are met, but content not always covered in a substantive and/or comprehensive way. Work reflects a solid grasp of each important aspect of the assignment. Student illustrates insight and understanding of assignment
- 2. objectives. All key elements of the assignment met. Content is covered in a substantive and comprehensive way with each important aspect of the assignment addressed. Student illustrates insight and understanding of assignment objectives. Organization Main points are unclear and many are not sufficiently supported. Ideas are not logically arranged. Construction of sentences and paragraphs reflects difficulty with organizing coherent thoughts. Main points are clearly stated, but not always supported. Ideas are logically arranged, but sentences and paragraphs are not well-constructed. Organization reflects coherent thought, but transitions are needed to help connect ideas. Main points are clearly stated and supported. Ideas are logically arranged. Sentences and paragraphs are well- constructed. Organization reflects coherent thought
- 3. with effective transitions used to connect ideas. Support (Support and Elaboration) Points are not supported with evidence. Student does not make an effort to anticipate the reader's concerns. Most points are supported with evidence (facts, statistics when applicable) and examples. Student makes an effort to anticipate the reader’s concerns by offering relevant explanations and clear support for the author’s position. Main points are supported with effective evidence (facts, statistics when applicable) and examples. Student anticipates the reader’s concerns by offering relevant explanations and clear support for the author’s position. Tone & Style (Professionalism)
- 4. Word choice is informal and is not directed towards appropriate audience. Tone and style are not appropriate for assignment. Font type and/or size are not appropriate for assignment. White space is not used effectively. Word choice is directed towards the appropriate audience, but some issues related to tone and style noted. Font type and size choices may not be appropriate for assignment. White space is used effectively. Word choice is directed towards the appropriate audience. Tone and style are appropriate for assignment. Professional font type and size for assignment purpose. Effective use of white space. Grammar/Mechanics Many errors noted in sentence structure and/or spelling. Rules of grammar, usage, and punctuation not followed. Documentation style not used or formatting contains several major
- 5. errors. Sentences are complete and spelling is correct. Minor grammar, usage, and/or punctuation errors noted. Appropriate documentation style used where applicable with some minor formatting errors. Sentences are complete and spelling is correct. Rules of grammar, usage, and punctuation followed. Appropriate documentation style used where applicable. Internet Usage Policy at Pyramid: A Short Report
- 6. September 20, 2013 Prepared for: Pyramid Design Team Prepared by: Student Name BUS105 Background Pyramid Design Team began seven years ago as a small design
- 7. firm with three employees. The original employees were the owner and two designers. With this core of three employees, each knew what was expected of the other, and official policies cut against the grain of the creative atmosphere that was being fostered. Therefore, aside from the founding document containing the mission of the company, there were no policies put in place. This worked fine, until recently. Within the last four years, Pyramid has hired 11 additional staff, including designers and programmers. The company has been implementing new policies regarding vacation time, holidays, and sexual harassment, for example, but there still exists no policy governing the use of the Internet at work. Now that the company consists of 14 employees, I propose the creation and adoption of an Internet policy that will provide employees with clear guidelines about its appropriate and sanctioned use at work.
- 8. Problem The inappropriate use of the Internet is threefold. First, the designers and developers are downloading beta versions of software from the Internet. Since this software is often in beta, there can be, and have been, numerous problems with these types of free downloads. Our IT manager has seen a huge increase in Trojan viruses penetrating our system and causing damage to our servers and other employees’ computers. He has spent countless hours trying to find and remove these viruses and has expended thousands of dollars in resources to call in technical specialists to eradicate the viruses. The intent of the designers and developers was simply to get the latest software that will allow them to create the best product. Unfortunately, that has not always been the case, and some of these downloads are causing serious IT threats to our systems.
- 9. The new Internet policy needs to ban this practice and clearly state that nothing can be downloaded from the Internet without the express consent of the IT manager and a supervisor. Second is the use of social media at work. The use of company computers by employees to view Facebook, other social media, and streaming services has increased 200% in the past 18 months! Some employees, for example, are logging-into Facebook when they arrive at work and leaving the page running as a tab in their web browser, checking it frequently throughout the day. This has decreased productivity. A study conducted by Nucleus Research and published by Computerworld found that “Companies that allow users to access Facebook in the workplace lose an average of 1.5% in total employee productivity, according to a new report from Nucleus Research, an IT research company. The survey of 237 employees
- 10. also showed that 77% of workers who have a Facebook account use it during work hours.” Facebook is, of course, the biggest offender, but the policy needs to ban all social media, such as Twitter, while at work. The third area of concern involves streaming video services, such as Netflix, Amazon Prime, and Hulu. Employees who eat lunch at their desk are using their computers to watch videos from a streaming video provider. The problem arises when the employee watching a video finds the content completely suitable, while a co-worker sitting nearby, or passing by his or her desk, finds the content inappropriate. As this is a subjective opinion, we can be opening ourselves up to a lawsuit for sexual harassment, for instance, if a video contained nudity in it and the passerby saw it and became threatened.
- 11. Although most employees are not falling into this category, it only takes one. Because of this, we need to ban streaming videos. Finally, there have been instances where pornography has been viewed on a company computer. I am sure we all can agree that banning the use of viewing or downloading any pornographic image using a company computer should be banned. Solution There needs to be a policy implemented where violations like these above can be dealt with immediately. Depending on the severity of the infraction, we can have a tiered system of punishment:
- 12. 1. First Infraction – verbal warning 2. Second Infraction – written warning 3. Third Infraction – dismissal from the company There are many forms an Internet usage policy can take, but I suggest we keep it simple. GFI, a company that provides IT solutions, provides a clear-cut policy for Internet usage that details what company computers should, and should not, be used for: • Company employees are expected to use the Internet responsibly and productively. Internet access is limited to job-related activities only and personal use is not permitted • Job-related activities include research and educational tasks
- 13. that may be found via the Internet that would help in an employee's role • All Internet data that is composed, transmitted and/or received by <company's> computer systems is considered to belong to <company> and is recognized as part of its official data. It is therefore subject to disclosure for legal reasons or to other appropriate third parties • The equipment, services and technology used to access the Internet are the property of <company> and the company reserves the right to monitor Internet traffic and monitor and access data that is composed, sent or received through its online
- 14. connections • Emails sent via the company email system should not contain content that is deemed to be offensive. This includes, though is not restricted to, the use of vulgar or harassing language/images • All sites and downloads may be monitored and/or blocked by <company> if they are deemed to be harmful and/or not productive to business • The installation of software such as instant messaging technology is strictly prohibited Unacceptable use of the Internet by employees includes, but is not limited to:
- 15. • Sending or posting discriminatory, harassing, or threatening messages or images on the Internet or via <company's> email service • Using computers to perpetrate any form of fraud, and/or software, film or music piracy • Stealing, using, or disclosing someone else's password without authorization • Downloading, copying or pirating software and electronic files that are copyrighted or without authorization • Sharing confidential material, trade secrets, or proprietary information outside of the organization • Hacking into unauthorized websites
- 16. • Sending or posting information that is defamatory to the company, its products/services, colleagues and/or customers • Introducing malicious software onto the company network and/or jeopardizing the security of the organization's electronic communications systems • Sending or posting chain letters, solicitations, or advertisements not related to business purposes or activities • Passing off personal views as representing those of the organization Obviously, not all points made here are necessary, but this provides the best overview of a policy that we can utilize to make our operations run more smoothly and
- 17. effectively. We can pick what we need and discard what does not apply. I suggest we begin work on creating this policy within the next week and have it ready to implement within one month. I am available at your convenience to discuss the creation of this policy. Works Cited "Sample Internet Usage Policy." GFI. GFI Software, n.d. Web. 20 Sept. 2013.
- 18. <http://www.gfi.com/pages/sample-internet-usage-policy>. "Study: Facebook Use Cuts Productivity at Work." Computerworld. Computerworld, Inc. 22 July 2009. Web. 20 Sept. 2013. <http://www.computerworld.com/s/article/ 9135795/Study_Facebook_use_cuts_productivity_at_work> The Benefits and Risks of Using Skype at Darcy’s:
- 19. A Short Report September 20, 2013 Prepared for: Darcy’s Department Store Prepared by: Student Name BUS105
- 20. 2 Background The East Coast buyers for Darcy’s Department Store are looking for an economical and efficient way to share information about the deals buyers are getting from various
- 21. suppliers and use real-time transmission of that information between one another to help save money. There are a number of tools to do this, but Skype has been mentioned as a leading contender. Skype claims to be an easy to use, online tool that allows users to connect with any other Skype user around the world for free. A user can make video and voice calls to other Skype users at no charge. Users can even share files among themselves, which provides a great asset during a business meeting. However, when there are group video calls, then Skype begins to charge a fee. Also, for buyers throughout the East Coast, this tool can be
- 22. useful if they need to talk with one another. However, for meetings that require more than two attendees, Skype is not a useful tool and is not intended to work that way for business. Benefits Among the most attractive benefits of Skype is that it is free and you can see the person you are talking with. To purchase a software license for 20 buyers that is compatible to what Skype can do will cost Darcy’s roughly $1,500 per month. There are no hidden charges with Skype. According to Skype’s web page, users get video and voice calls to other Skype users and “instant messaging and file sharing” all
- 23. at no charge. The video sharing feature of Skype will allow the buyers to see products in real time. For example, if two buyers are looking at similar merchandise from two different suppliers who are offering different pricing, then they can quickly Skype one another and compare the product to see if it is the same and to then get the best pricing for it. Two business writers for the Auburn Citizen in NY, state that there are business users “who can save time and money in scheduling and holding conferences or training sessions, demonstrate products or services for potential customers, and extend
- 24. customer service by showing customers how to get the most from your product” (Leon and Leon). Downsides Despite the benefits mentioned above, there are clear downsides to this product. I tested Skype over a one-week period by calling various Skype users throughout the East Coast and tried to simulate a conversation that a buyer might have. First, using Skype takes getting used to. During my five-day test, I never mastered the connection stage. This is when one Skype user “calls” another Skype user. Skype makes
- 25. 3 a distinctive sound that lets the user know it is making a call. However, once you connect to whom you are calling, the picture shows, but it takes about five seconds for that picture to catch up with the person sitting there. In essence, it is a still picture for five seconds. Second, once I was connected to the user, I quickly realized that what I was saying was not being transmitted in real-time. There could be up to a three second lag in what I said and the user hearing it. This created a number of challenges, but the biggest one
- 26. was this lag kept the other user and me talking over each other. I just assumed the user could not hear what I said, so I repeated myself. Of course, as soon as I spoke, then I heard the user’s response to my original message, and thus began us talking over one another. This was a persistent problem throughout my first two calls, but got better once I became more familiar with the technology. Third, the picture is grainy, like an old TV. In this world of high definition, the picture I was getting with Skype looked like a 1970s television set. I could see the person fine, but the lack of clarity was alarming. If buyers were trying to compare colors of a fabric,
- 27. for instance, that would be nearly impossible to do because of the degraded picture quality. Fourth, I experienced a number of connectivity issues throughout my test. I was only able to connect immediately on four of my 10 test calls. On the others, I thought the person picked up, but there was no one there, and I had to re- connect. This caused frustration and made me want to discard Skype each time it happened. Also during calls, it was not uncommon for the connection to be lost, and I would have to try and re- connect again. I am not sure why this occurs, but it happened on nearly 40% of my calls. Again, this caused a great deal of frustration.
- 28. Finally, there are concerns that the privacy of Skype users is being violated by Microsoft, “Anyone who uses Skype has consented to the company reading everything they write” (“Skype with Care). Recommendation The use of Skype really boils down to money. If we are trying to save money and need a readily available, free solution, then Skype is a contender. However, even though it is free, Skype poses a number of technology challenges that are outlined above. This alone makes this technology untenable for our company. At the swift pace we move,
- 29. little challenges like the one Skype poses lead me to not recommend the product. There are a number of other services we can use, including many instant messaging programs that provide similar services as Skype, but do it better. We can even use FaceTime, from Apple, that can be used on Macs, iPhones, iPads, and iPods, and most of our buyers seem to have at least one of these products. 4 In summary, although Skype is free, it does not meet the need we have to interconnect
- 30. buyers across the East Coast and allow them to quickly and efficiently conduct business. I do not recommend Skype for Darcy’s buyers. 5 Works Cited Leon, Norma, and Tony Leon. "Sky’s the limit for Skype video call uses." The Citizen. N.p., Aug. 2013. Web. 20 Sept. 2013. <http://auburnpub.com/lifestyles/sky-s-the- limit-for-skype-video-call-uses/article_5454fb55-8c85-5817-
- 31. 909f- 43a729f04992.html. >. "Skype with care – Microsoft is reading everything you write. ." The H Security. N.p., May 2013. Web. 20 Sept. 2013. <http://www.h- online.com/security/news/item/Skype-with-care- Microsoft-is-reading-everything-you-write-1862870.html>. "What is Skype?." Skype. N.p., n.d. Web. 20 Sept. 2013. <http://www.skype.com/en/what-is- skype/>. 1 Instructions for Graded Writing Assignment 3: Short Report
- 32. Readings: • Lesikar’s Chapter 11, pages 339-359 • Sample Short Report, pages 350-358 • Lesikar, Appendix B, pages 615-620 Instructions: For this final Graded Writing Assignment, you will compose a Short Report based on one of the scenarios outlined below. You must choose one of the scenarios listed below; papers submitted reflecting a scenario other than those listed below (even those listed in your text) will not be given credit or graded. Assignment Requirements: Write your findings as a well-organized Short Report containing the following key elements:
- 33. • A title page • Document headings to separate parts of the report • At least two sources with brief in-text citations as shown in sample Short Report (pages 350-358)1 • Interpretation of your findings in terms of their likely significance to you and your readers. Assignment Notes: • Create all pieces of the short report as one (1) document. • The Short Report should be 1,200-1,500 words in length. Remember to focus on content, not just writing to fill a word requirement. • You will upload your finished document to the appropriate
- 34. assignment in Business Communications. Instructions on how to upload are available in the Topic 12 assignment area. Scenarios: Option 1) The graphic design shop where you work as the account manager is doing well. Just last year, the owner hired three new designers and a receptionist, bringing the total number of employees to 14. But with growth comes certain headaches, and one of them is figuring out how to regulate employees’ Internet use. Currently, employees can download anything they want from the Internet and view any web site they wish. The owner’s IT person has alerted him to several problems. One is that the designers are
- 35. downloading any and all software that they think sounds “cool” —even software in beta 1 Please note that the sample shown in your book is a Mid- length Report and therefore contains some sections that you will not need for the Short Report. For instance, you will not need the letter of transmittal or the executive summary. 2 versions that still have a lot of kinks. As a result, their computers lock up or malfunction, and the IT person has to spend hours troubleshooting the problem to get it resolved. Two, there is concern over what Internet sites employees are
- 36. viewing, specifically those that are inappropriate for the workplace. Overall, the IT person is worried about security breaches resulting from these downloads, inappropriate web site visits, and other Internet activities. It’s time for a policy to be developed governing Internet-use, and your boss thinks you’re just the person to help write it. Your assignment is to study the current wisdom on workplace Internet policies and send your findings to your boss and the IT person as a short report, including a proposed Internet-use policy that might be implemented. Option 2) As a Senior Buyer at Darcy’s, a national department store, Sasha Warner manages the buyers in the eastern U.S. region. You’re currently working under her as a sale co-op student.
- 37. She drops by your office to chat one day and brings up a subject she’s been wondering about. “Do you know anything about Skype?” she asks. You nod, having used this online international phone service yourself. “I heard it’s totally free and really easy to use,” she continues, “so I’m thinking about recommending that all my buyers subscribe to it. Then maybe they could talk to each other and to international designers and merchandisers more easily. Is there any downside? Maybe security issues?” You’re not sure--but you offer to look into the matter for her. Do the necessary research, and, if you haven’t yet done so, try this service yourself and then write Sasha a report giving her the information she needs to
- 38. decide whether or not to pursue this idea further. She may want to share your report with other managers in the company, so be sure you give it your best effort. Option 3) You work for the owner of three local coffee and tea shops, one of which opened a few months ago. The newest one has already developed quite a nice, regular clientele, mostly those in or near the neighborhood who want an alternative to the big-coffee-chain experience, but your boss thinks its sales need a bump. She is considering holding an in-store promotion at the coffee shop – her first ever. Since she knows you’re an Internet whiz, she turns to you for help. “How do you run one of these events?” she wants to know. “How much do they cost? Are
- 39. they worth the effort and expense? What are my options? Do such promotions have lasting effects? How can I maximize the results?” You turn to the Internet and find a lot of great stuff about in- store promotions, so much, in fact, that you decide to present your findings to your boss in writing. Tell her what she needs and wants to know in a clear, well organized report. Having the information in writing will also be helpful if she wants to share it with other employees. Be sure she can go to your sources and read more if she wants to. Option 4) Many managers today are realizing that there really is something distinctive about “Gen Y,” or “Millennial,” employees (the children of the “baby boomers”--who were themselves
- 40. children of the World War II generation). Find a real client or invent a realistic company to use 3 as your client. Then review the literature on Gen Y employees and write your client a report in which you describe the distinctive traits of this segment of the workforce and recommend ways to recruit, manage, and retain them. Option 5) Your company does not offer flexible spending accounts (FSAs) for its employees. Your boss wonders if your company (you pick the name) should. Are FSAs a good idea for businesses and employees? Prepare a report for your boss in which you analyze the advantages
- 41. and disadvantages of FSAs so that she can decide whether to offer FSAs to your employees.