Embed presentation
Download to read offline

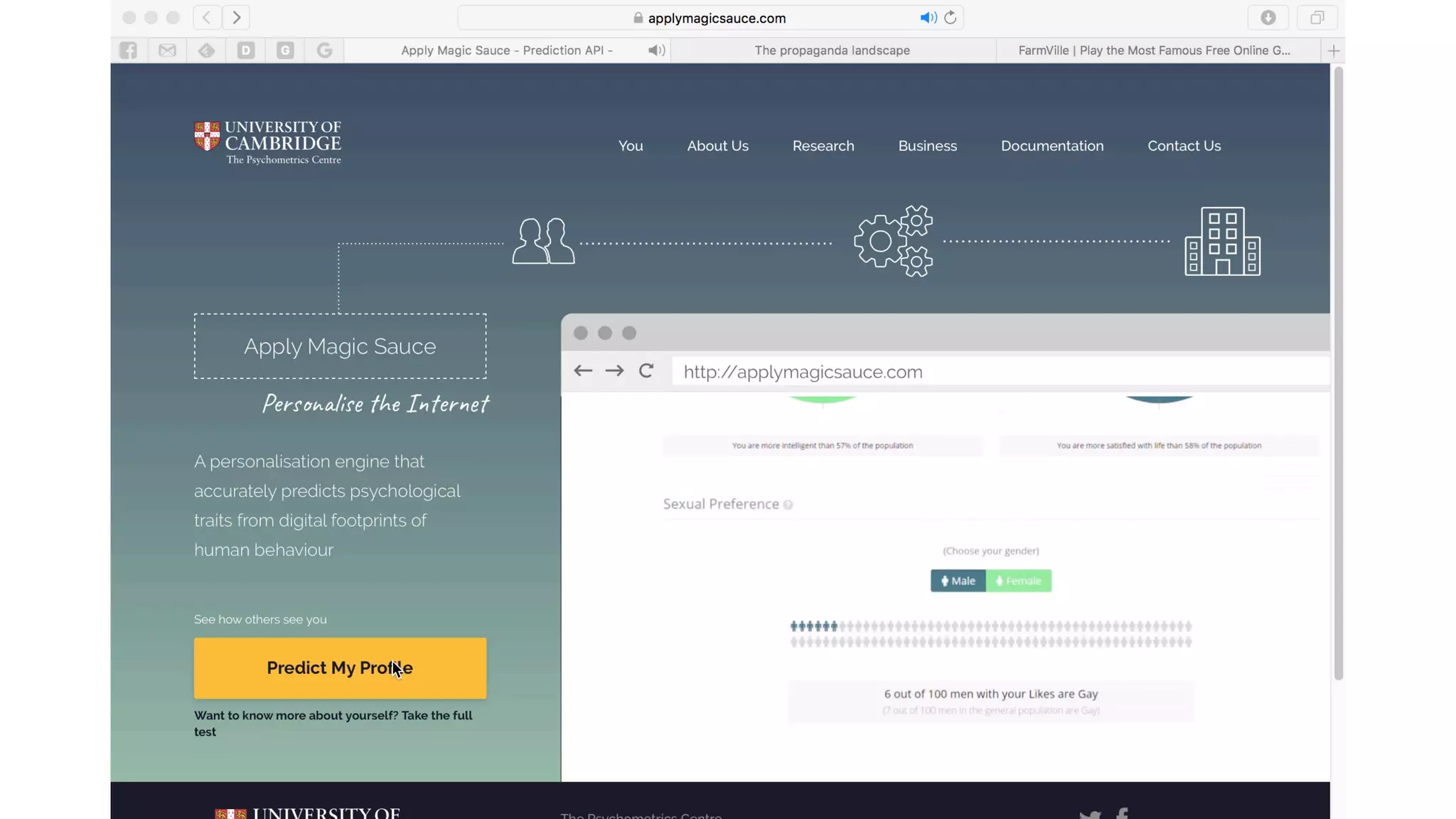




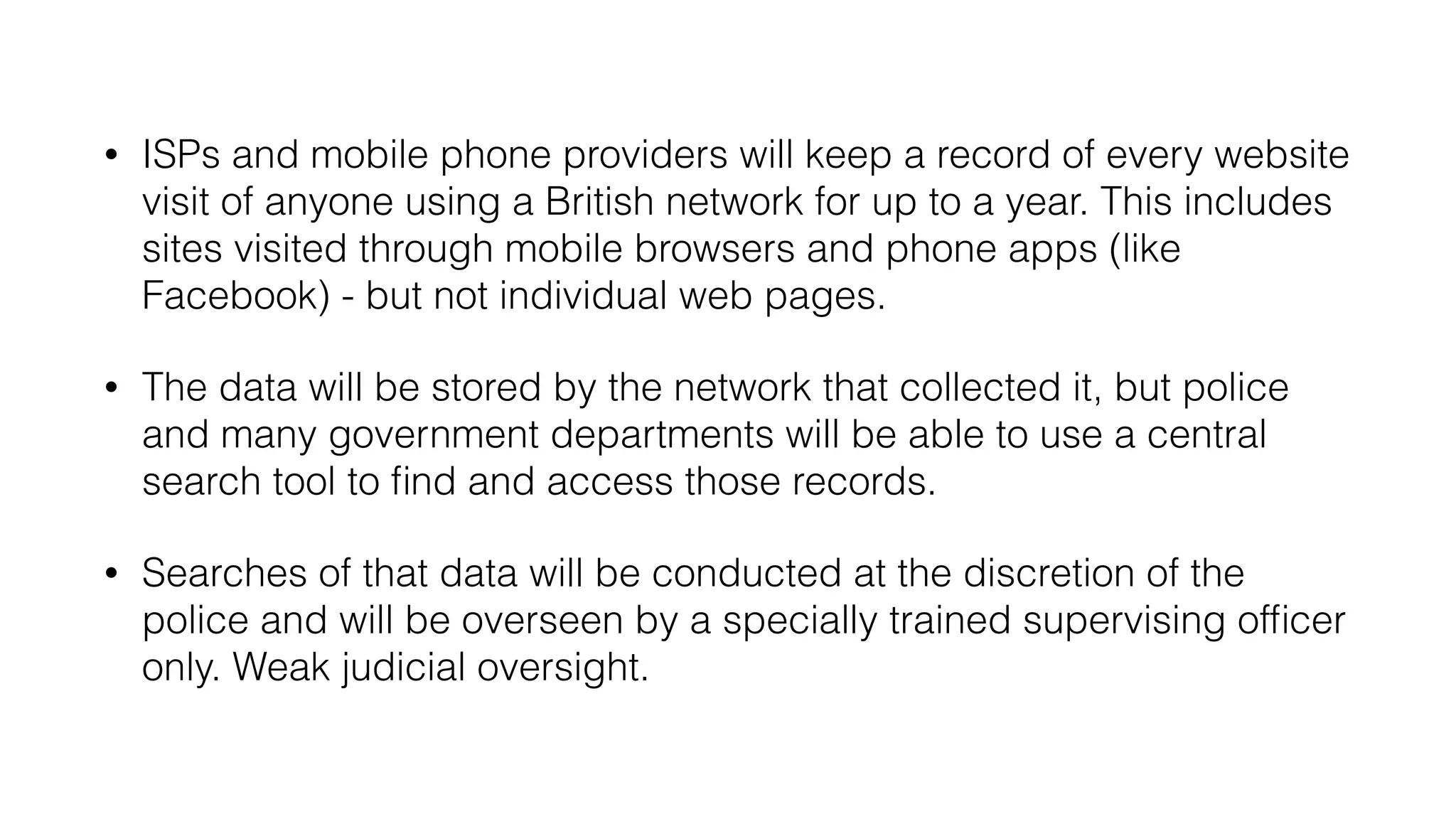
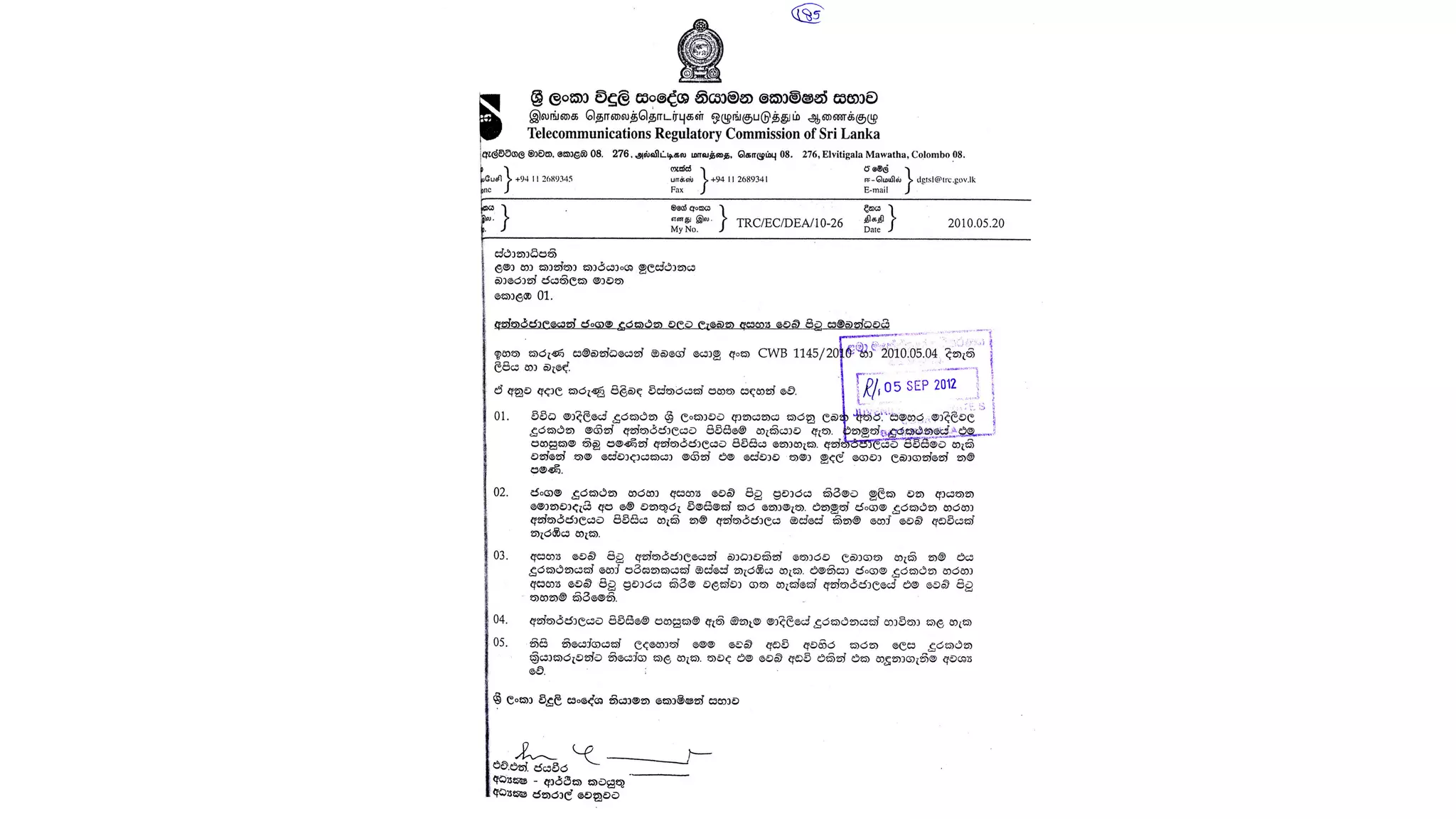





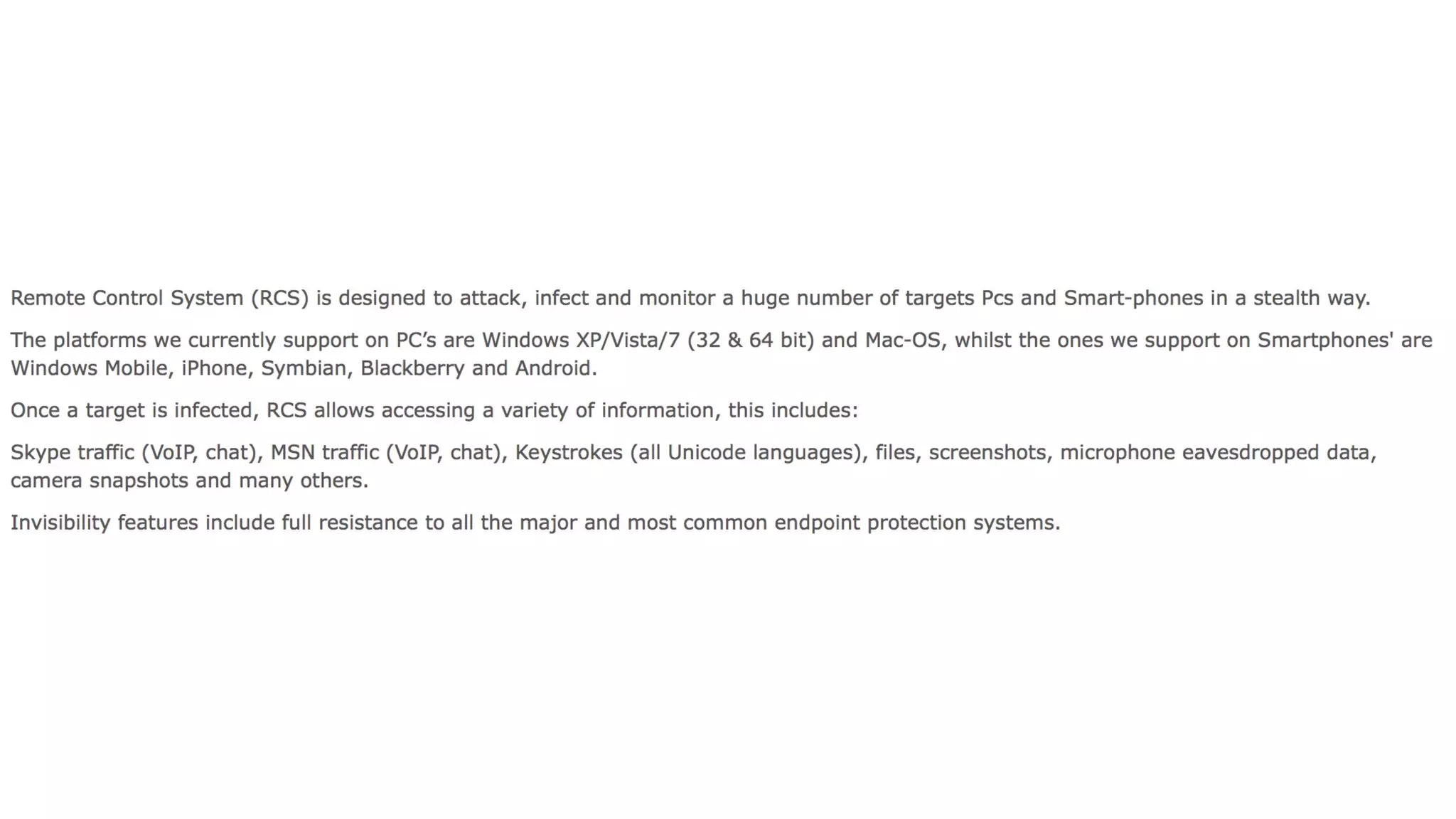








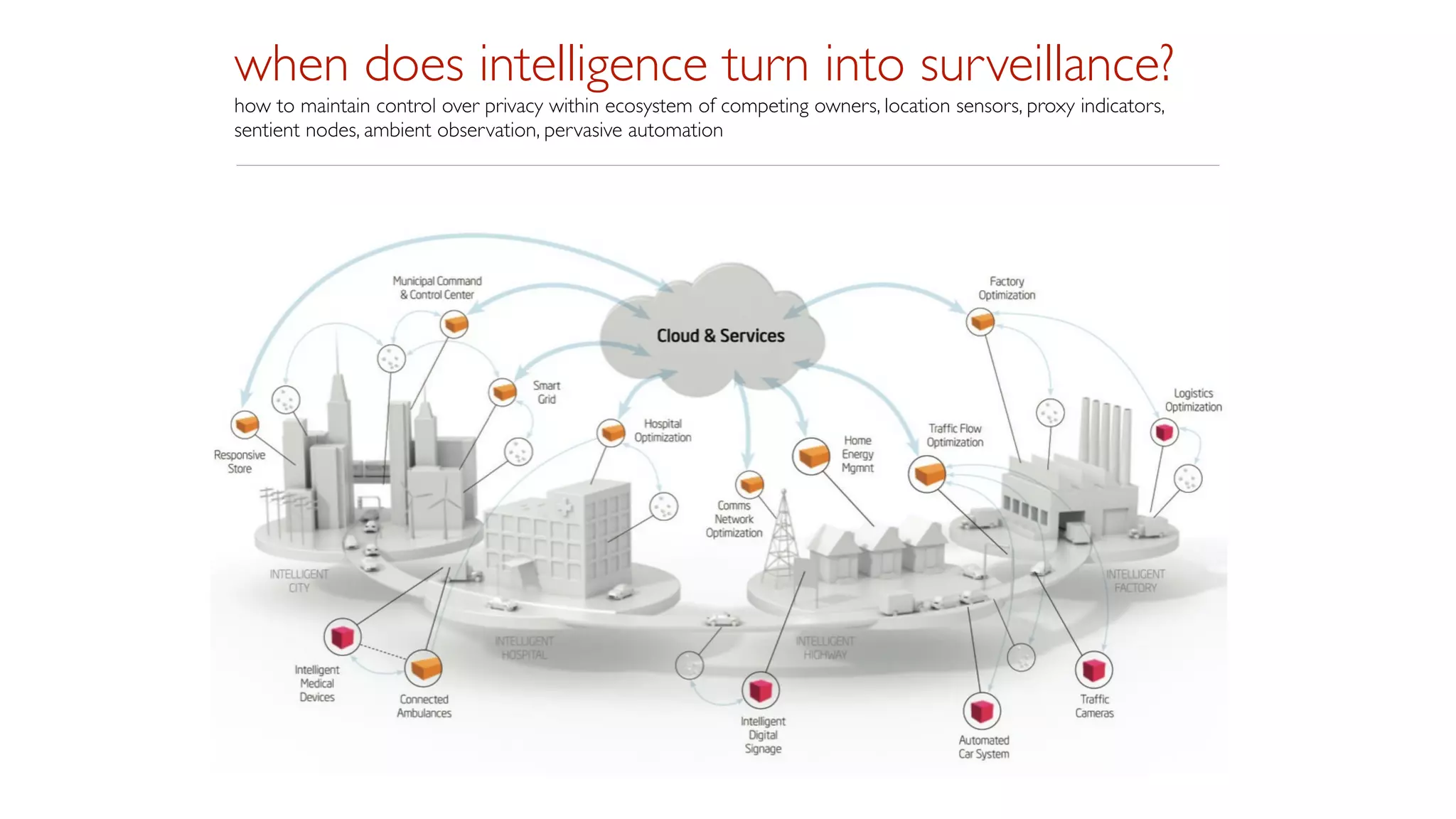




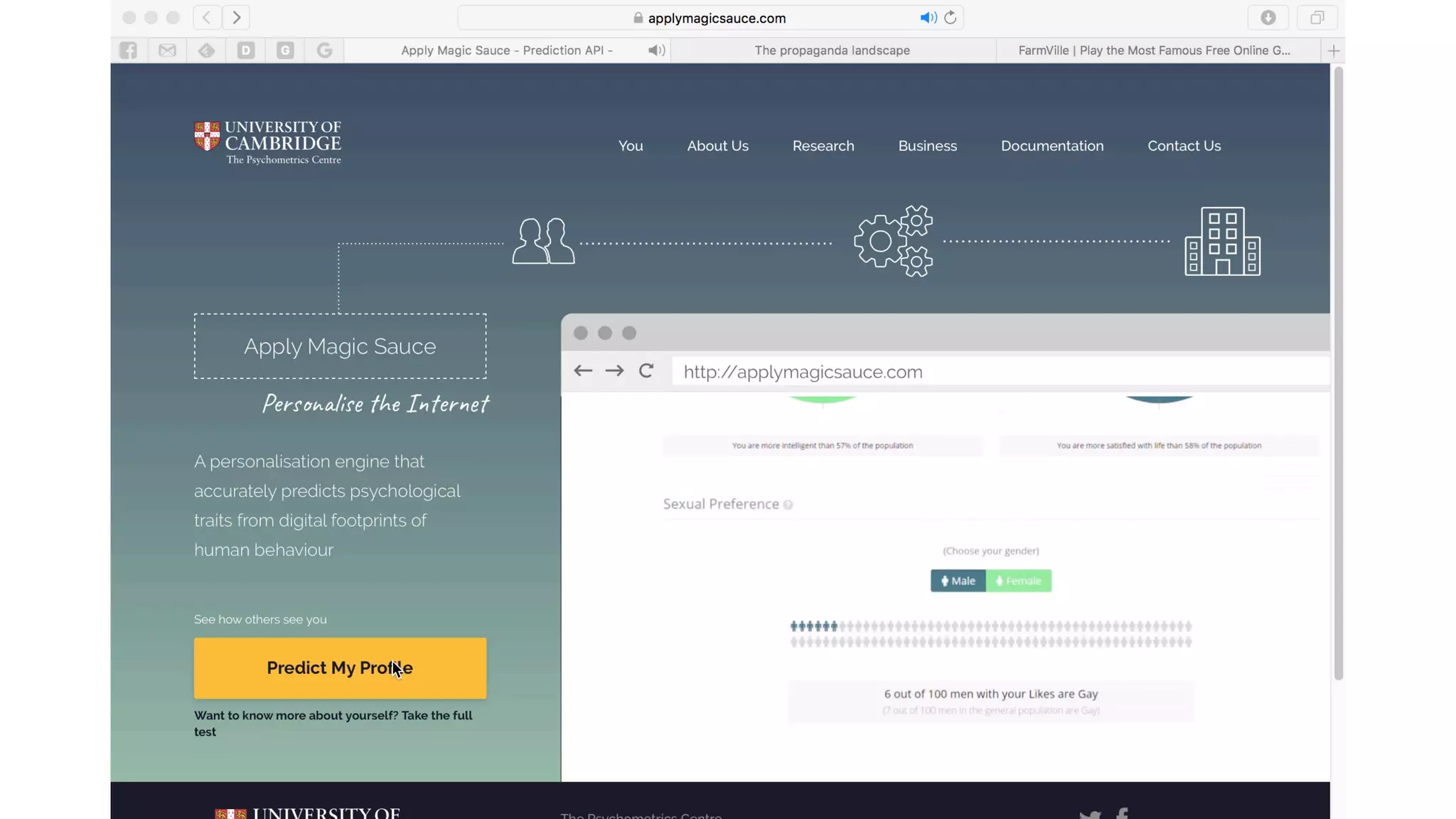
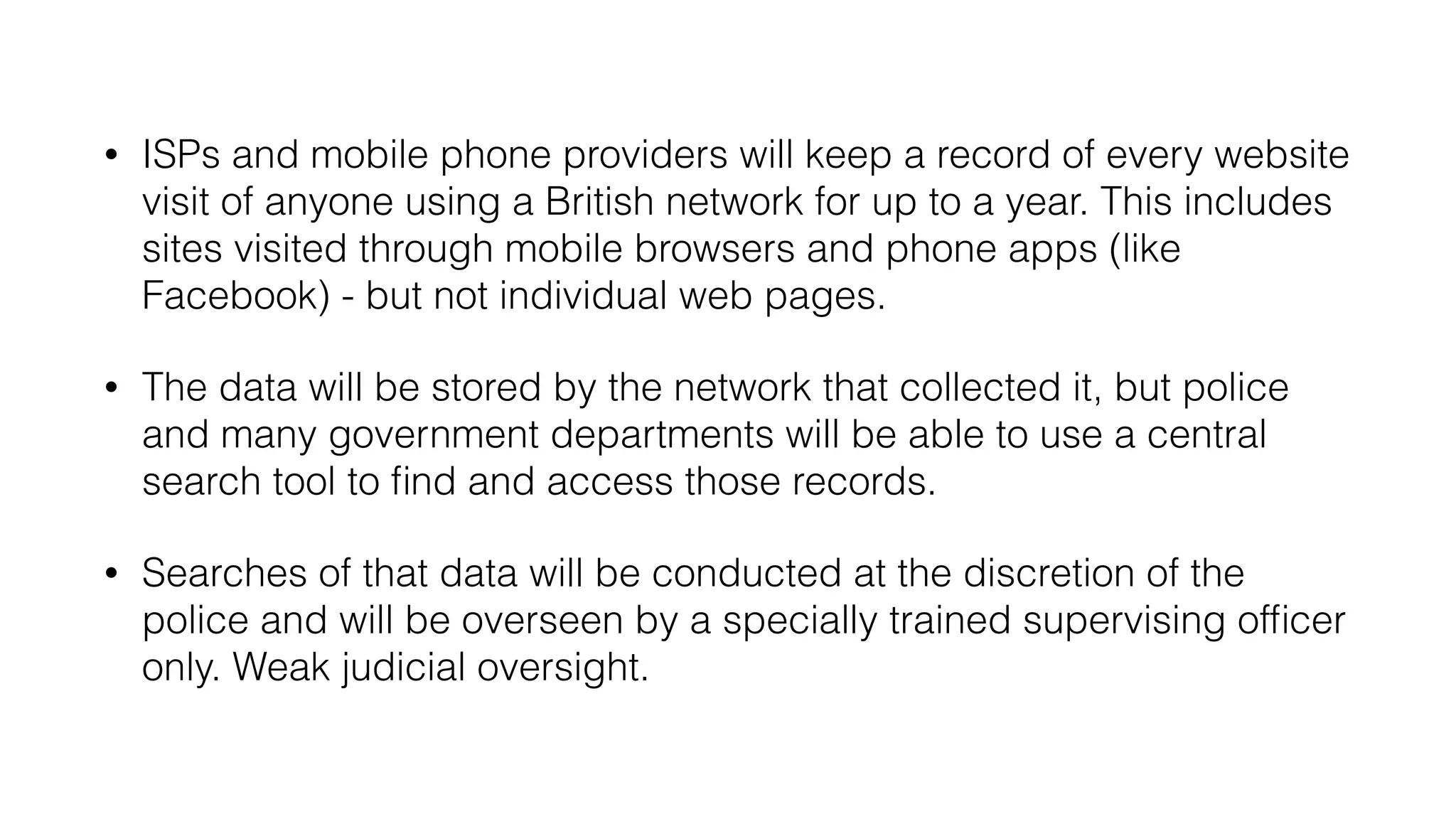
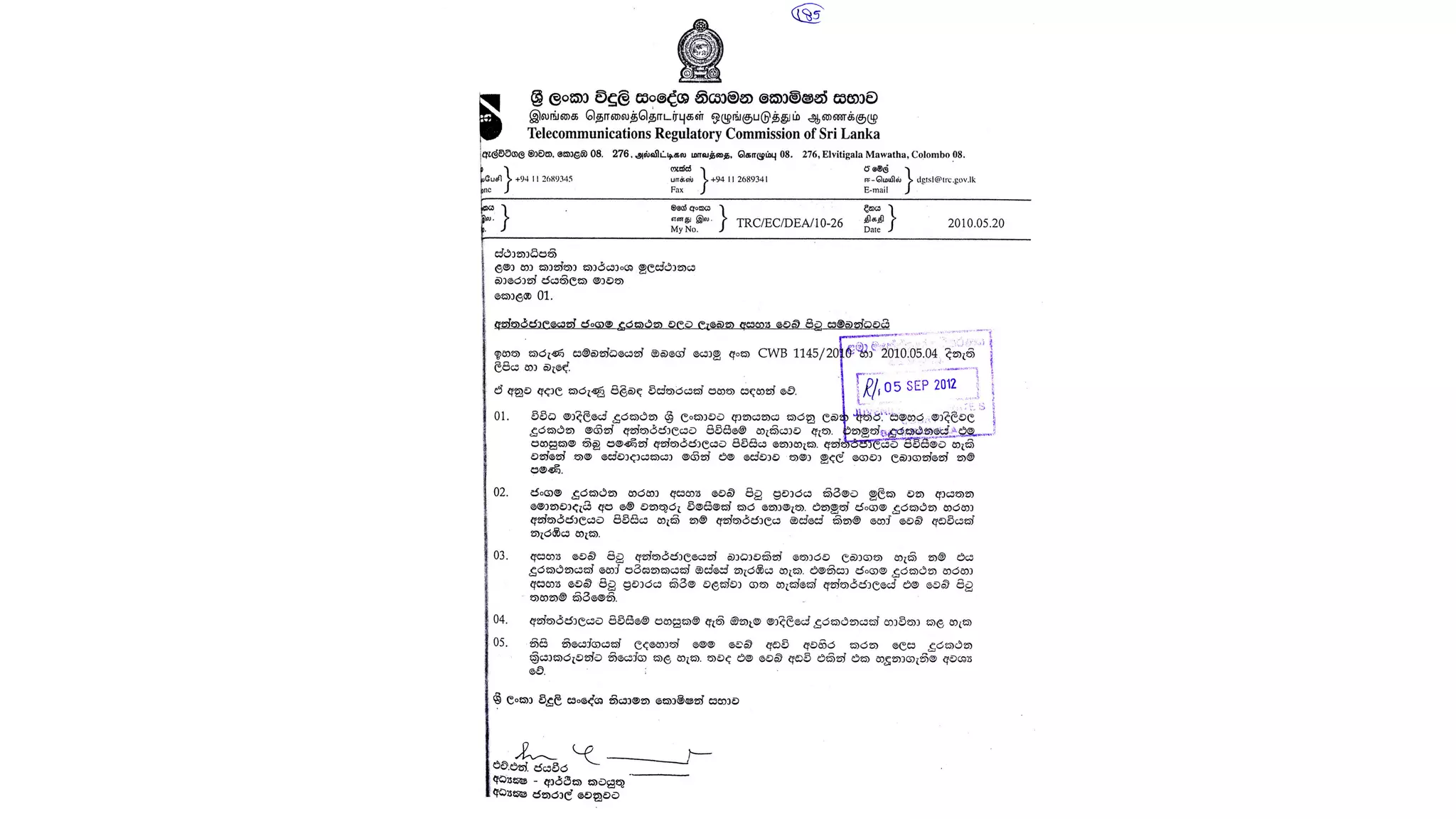
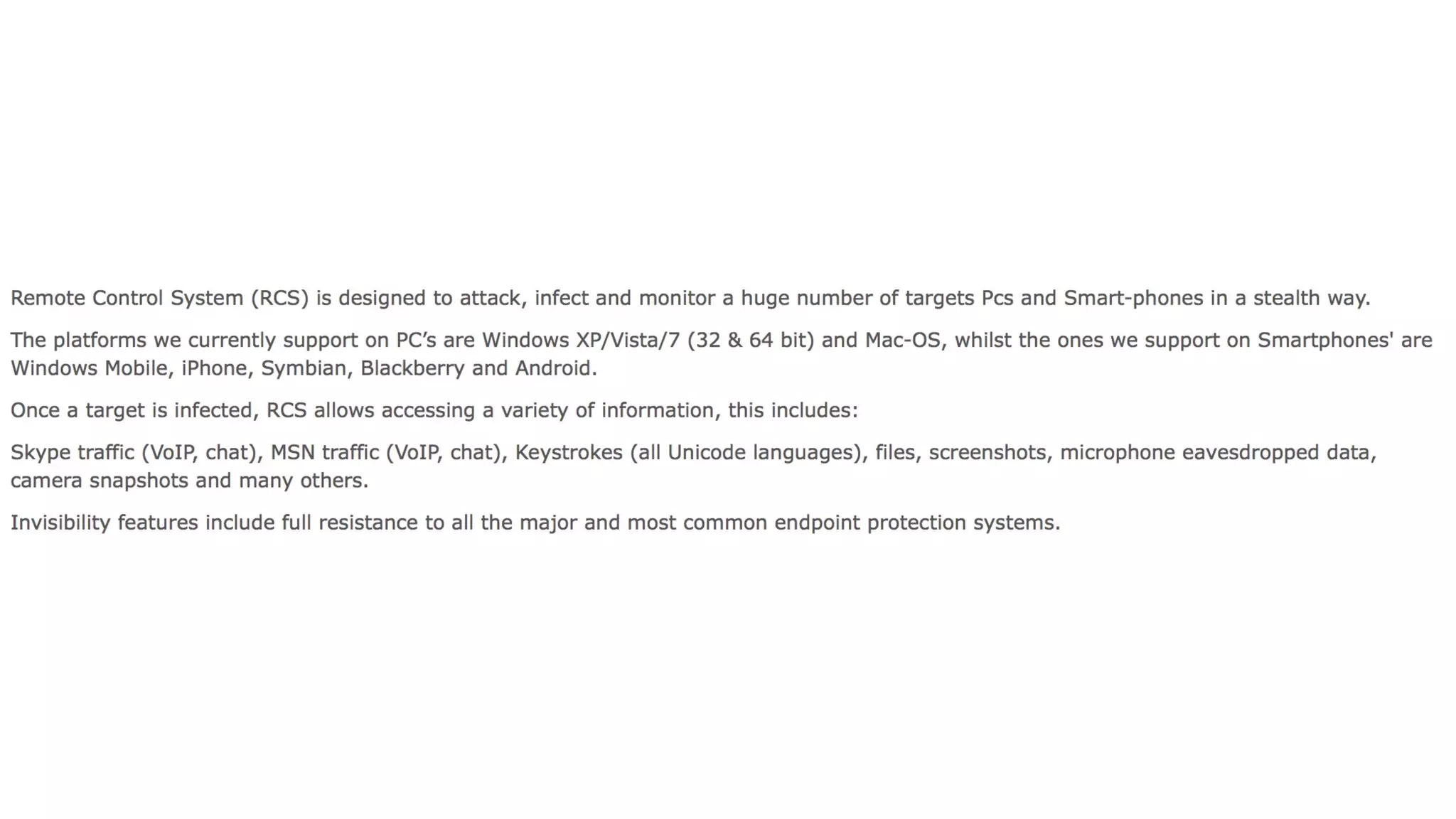
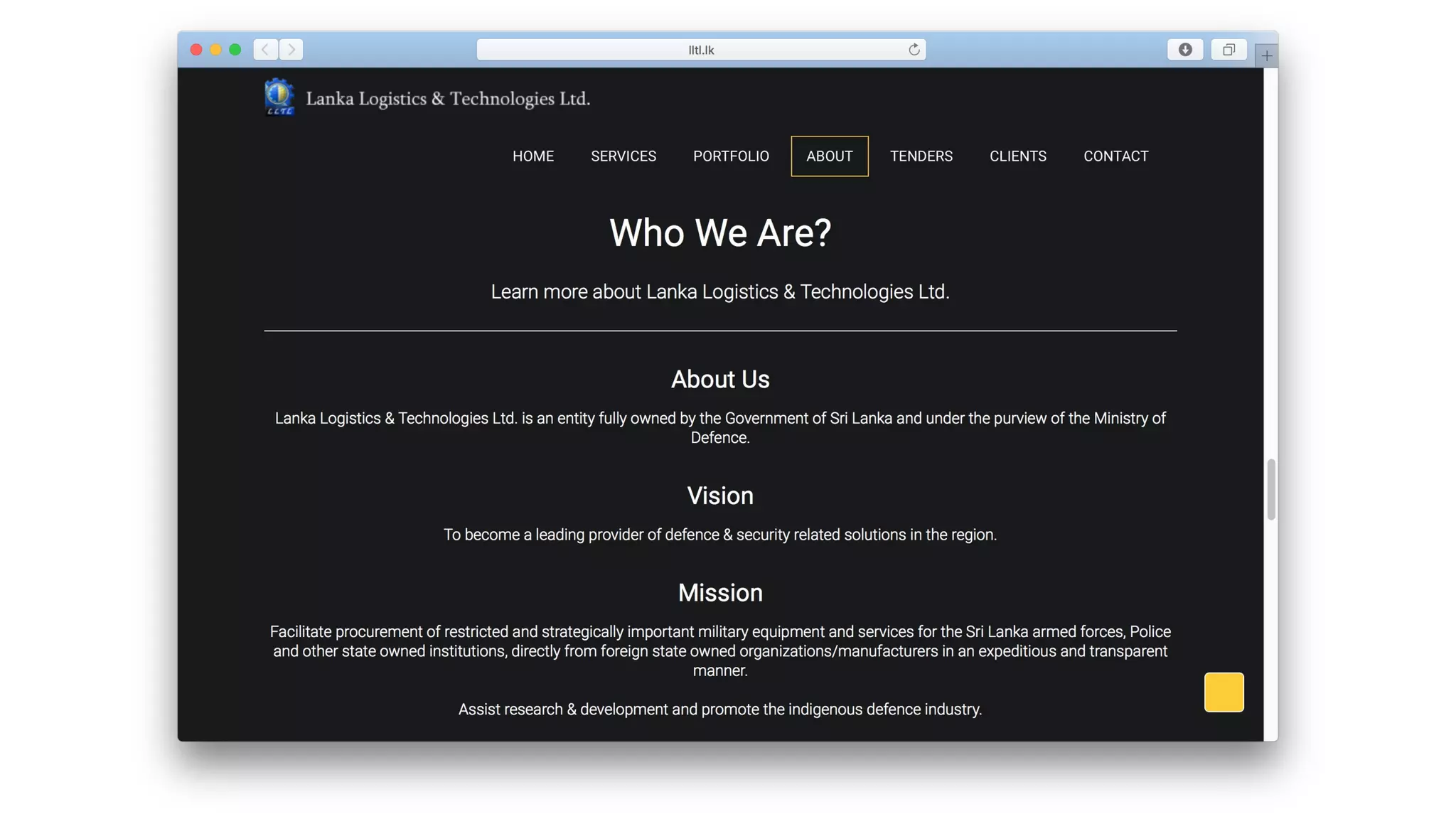
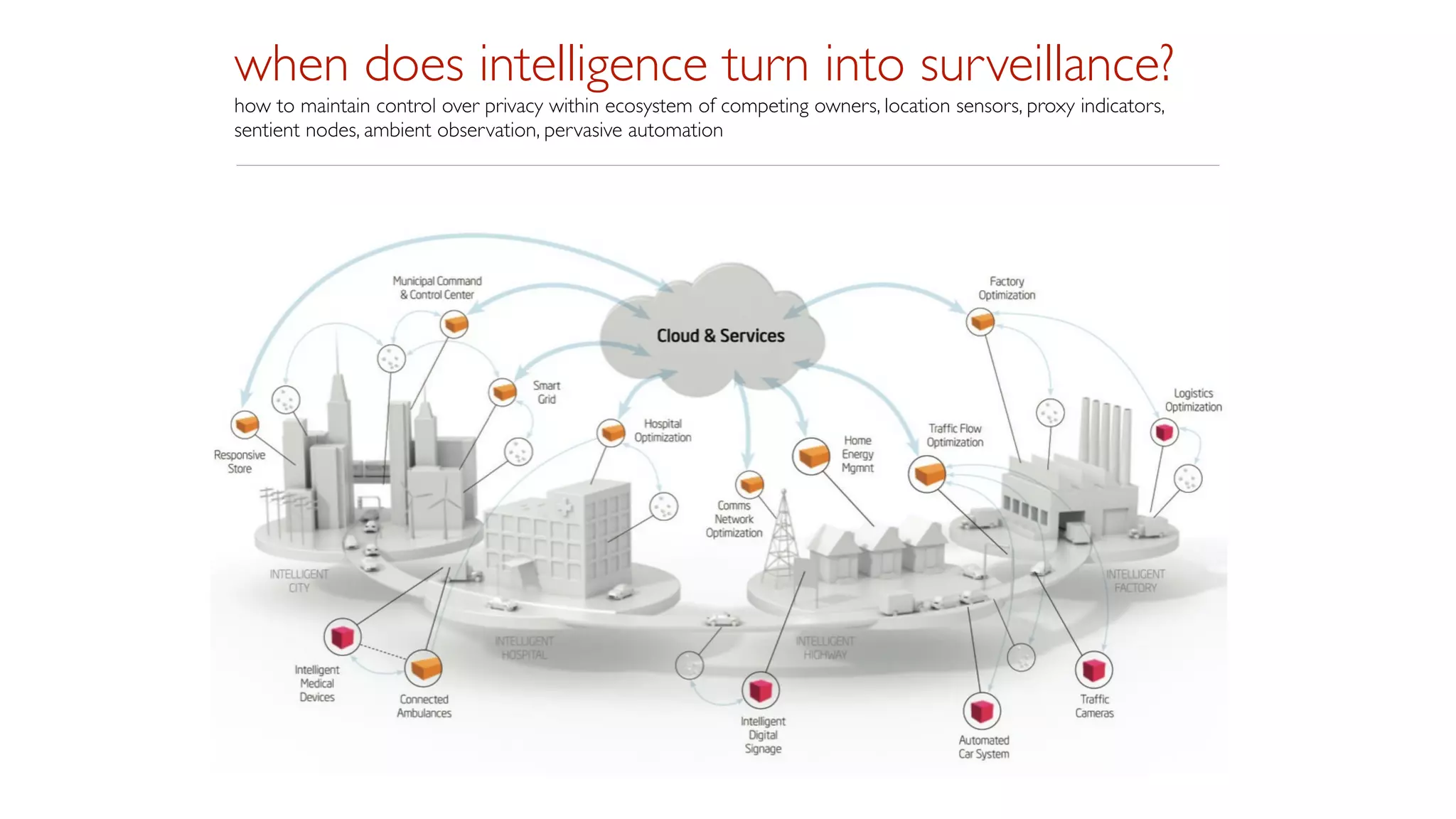
The document discusses issues around surveillance, privacy, and ethics in the digital age. It notes that personal data is increasingly being collected and stored by governments and companies without proper oversight or user consent. New laws allow intelligence agencies to access people's web browsing histories and communication data. Maintaining privacy has become difficult as technology advances and more entities seek to gather and leverage people's digital information for surveillance or other purposes. Overall it raises concerns about how surveillance has become normalized and privacy eroded in today's digital world.