Bigdata abstract bim earth corporation - david joshua plager, aia - cloud computing security architecture for building information modeling & management
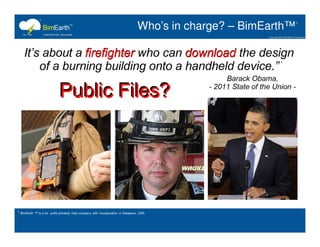
- 1. 1 Who’s in charge? – BimEarth™ 1 2 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA.
- 2. 1 Social Business HOT - BimIBM 1 2 2 “Social business is the next step in the overall evolution of business. As our global network of people becomes more instrumented, interconnected and intelligent, dramatic shifts are taking place. The ways in which people interact, relationships form, decisions are made, work is accomplished and goods are purchased are fundamentally changing.” 1 BimIBM is not a registered trademark. BimEarth Corporation thanks IBM for its publically accessible research and non-proprietary whitepapers in the areas of Business to Business integrations, Cloud Computing and Social Business innovation. 2 IBM is a registered trademark of IBM Corporation.
- 3. 1 BIM is for Everyone - BimIBM 1 2 2 “Location-based and social business networks are transforming the way people interact, form relationships, make decisions, accomplish work and purchase building goods and services.” “Globally instrumented, interconnected & intelligent networks are forming to deliver new products and services that geographically connect consumers and consumer groups within and across industries.” David “Joshua” Plager, AIA BimEarth 1 BimIBM is not a registered trademark. BimEarth Corporation thanks IBM for its publically accessible research and non-proprietary whitepapers in the areas of Business to Business integrations, Cloud Computing and Social Business innovation. 2 BIM is not a registered trademark. BimEarth™ believes BIM is for everyone.
- 4. 1 Management Information Base - BimIBM 1 2 2 “A management information base (MIB) is a virtual database used for managing the entities in a communications network. Most often associated with the Simple Network Management Protocol (SNMP), the term is also used more generically in contexts such as in OSI/ISO Network management model. While intended to refer to the complete collection of management information available on an entity, it is often used to refer to a particular subset, more correctly referred to as MIB-module.” 1 BimIBM is not a registered trademark. BimEarth Corporation thanks IBM for its publically accessible research and non-proprietary whitepapers in the areas of Business to Business integrations, Cloud Computing and Social Business innovation. 2 MIB is not a registered trademark. Definition provided by Wikipedia, the world’s free encyclopedia.
- 5. 1 Innovation – BimEarth™ 1 22 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA 2 2010 Gartner Hype Cycle Methodology & Report; contact: marcus.blosch@gartner.com.
- 6. 1 Innovation on Steroids – BimEarth™ 1 22 Geospatial Networks 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA 2 2010 Gartner Hype Cycle Methodology & Report; contact: marcus.blosch@gartner.com.
- 7. 1 Portal - BimClouds 1 2 1 BimClouds™ is a registered trademark & service mark of BimEarth Corporation, Delaware, United States of America
- 8. 1 Make it Public - BimShare 1 2 1 BimShare™ is a registered trademark of BimEarth Corporation, Delaware, United States of America
- 9. 1 Keep it Private - BimVault 1 2 1 BimVault ™ is a registered trademark of BimEarth Corporation, Delaware, United States of America
- 10. 1 Business to Business - BimFlow 1 1 1 1 1 BIMFlow™ by BimEarth™, the company's 2 flagship enterprise content collaboration offering, allows building professionals to collaborate on content with users both inside and outside their organization while providing IT with centralized security policy and administrative controls to manage the flow of work across the entire extended enterprise. 1 1 1 1 1 1 1 1 1 BimEarth™, BimClouds™, BimFlow™, BimHub™, BimWork™, BimForum are registered trademarks and Service Marks of BimEarth Corporation, Delaware, United States of America
- 11. 1 Project – BimFlow - BimHubs 1 2 1 BimHubs™ is a registered trademark of BimEarth Corporation, Delaware, United States of America BimEarth™’s BimClouds Browser™ overlays BimCloud™ service marks upon geographic (2D) and geospatial (3D) underlays to connect Users with (1) BimCloud™ security and its (3) sub- securities: BimShare™, BimVault™ and BimWork™. Within BimCloud™ BimWork™ securities, BimHubs™ securities are managed by Project Team Leaders & their Administrators. BimHubs is a premium BE Service. With BimHubs, project teams enjoy the world’s first business-social tool that marries together Digital Rights Management with integrated Applications, Forums & Repositories; Files may be launched Online, within a BimClouds Browser™ or separate Application Window on a User’s Desktop or other thin client device. Files may be exported out of network.
- 12. 1 Project – BimFlow - BimWork 1 2 1 BimWork™ is a registered trademark of BimEarth Corporation, Delaware, United States of America
- 13. 1 Project – BimFlow - BimForum 1 2 1 BimWork™ is a registered trademark of BimEarth Corporation, Delaware, United States of America
- 14. 1 1 AEC Phases & Instruments - BimHubs 2 2 3 1 BimHubs™ is a registered trademark of BimEarth Corporation, Delaware, United States of America. 2 BimPhase™ is a registered trademark of BimEarth Corporation, Delaware, United States of America. Secondary phases may be customized 3 BimJob™ is a registered trademark of BimEarth Corporation, Delaware, United States of America. All data must be associated by Users with (1) and only (1) BimJob™.
- 15. 1 1 Management & Authorizations - BimHubs 2 1 BimHubs™ is a registered trademark of BimEarth™ Corporation, Delaware, United States of America.
- 16. 1 Customer Applications – BimStacks™ 1 2 Services Not Offered OSI3 through OSI-6 Applications OSI-7 Applications 1 BimStacks™ is a registered trademark of BimEarth™ Corporation, Delaware, United States of America. BimEarth Corporation™ licenses BimTops™ to Apple and Microsoft Desktop Providers. BimTops™ are restricted to install only applications downloaded from BimStacks™. BimStacks™ contain only applications that restrict themselves to managing OSI-7 level securities. BimStacks contain current versions of all of the OSI-7 application offerings of Autodesk, Bently, Dassault, Google, McNeal & Associates, Microsoft, Nemetshcek & Trimble. BimStacks™ also house 3rd party mobile applications (not shown here) that meet BimEarth specifications and are certified by BimEarth™ Corporation.
- 17. 1 Launch within BimClouds - BimTops 1 2 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA. BimTops™ is a registered trademark of BimEarth™ Corporation. BimTops™ is a registered trademark of BimEarth™ Corporation, Delaware, United States of America. BimEarth Corporation™ licenses BimTops™ to Apple and Microsoft Desktop Providers. BimTops™ are restricted to install only applications downloaded from BimStacks™. BimStacks™ contain only applications that restrict themselves to managing OSI-7 level securities. BimStacks contain current versions of all of the OSI-7 application offerings of Autodesk, Bently, Dassault, Google, McNeal & Associates, Microsoft, Nemetshcek & Trimble.
- 18. 1 Or Launch with your OS - BimTops 1 2 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA. BimTops™ is a registered trademark of BimEarth™ Corporation. BimTops™ is a registered trademark of BimEarth™ Corporation, Delaware, United States of America. BimEarth Corporation™ licenses BimTops™ to Apple and Microsoft Desktop Providers. BimTops™ are restricted to install only applications downloaded from BimStacks™. BimStacks™ contain only applications that restrict themselves to managing OSI-7 level securities. BimStacks contain current versions of all of the OSI-7 application offerings of Autodesk, Bently, Dassault, Google, McNeal & Associates, Microsoft, Nemetshcek & Trimble.
- 19. 1 Print or Scan in 2D or 3D - BimCopy 1 2 2 dimensional 3 dimensional Low Volume 2 Large Format Color Hewlett- Packard Corporation 2 High Volume Large Format Greyscale Z Corporation Low Volume Small Format Single Material Zerox BimPrint (2D) Corporation BimPrint (3D) BimScan (2D) BimScan (3D) Low Volume, Small Format, Color Zerox Corporation Medium Volume Large Z Corporation Format Color or Greyscale 1 BimEarth ™ is a for profit privately held company with incorporation in Delaware, USA. BimCopy™, BimCopies™, BimPrint™, BimPrints™, BimScan™, BimScans™ & BimPay™ are registered trademarkes of BimEarth™ Corporation. 2 BimCopy™ is a Service BimEarth™ Corporation licenses to 3rd party printing houses
- 20. 1 2 Cloud Security Architecture – US NIST 2 1 BimEarth™ Corporation is a for profit privately held company with incorporation in Delaware, USA. 2 United States National Institute for Standards and Technology is a non profit government institute incorporated in the United States District of Columbia. US NIST employees and Authors, Peter Mell and Tim Grance, in October of 2009, published “The NIST Definition of Cloud Computing.” BimEarth™ Corporation designed it’s cloud security framework using this definition as a guide. Public, BimShare, BimVault and BimWork (sub-securities.) are terms and domains used by BimEarth™ Corporation to mean Public, Private and Project (sub-securities). .
- 21. 1 2 Cloud Security Architecture – BimClouds 2 1 BimEarth™ Corporation is a for profit privately held company with incorporation in Delaware, USA. The BimClouds™ Logo, Icon and Favicon (cloud & lightning bolt) are Trademarked and their use as Service Marks protected by US Laws. BimEarth™’s geographic (2D) and Geospatial (3D) underlays and Service Mark overlays to connect Users with a Network location 2 BimClouds™ are securities held by BimEarth™ Corporation. BimClouds™ is also the name of BimEarth™’s Browser & Web Applications through which these securities are accessed. Per US NIST Hybrid Cloud security definition, BimClouds™ (BimEarth™’s Hybrid Clouds with one per postal address)), contain sub-securities named Public, & Private . 3 BimEArth™ Corporation has chosen to same the 3rd sub-security “Project” in lieu of US NIST’s recommended name “Community”.
- 22. 1 Securities by Color – BimClouds 2 3 3 3 2 2 2 1 BimEarth™ Corporation is a for profit privately held company with incorporation in Delaware, USA. United States BimEarth™’s Logo & Service Mark are protected by US law. 2 BimEarth™’s BimClouds™ use primary colors to identify each BimCloud’s (3) sub-security environments. Red identifies Public data, Blue identifies Private data, and Yellow identifies Project (or Community) data. BimEarth™’s BimClouds use secondary colors to identify User Status. User faces and the logos of businesses, when provided, are outlined in these colors. Purple identifies Customer Administrators, Green identifies 3 Customer Employees., and Orange identifies Visitors.
