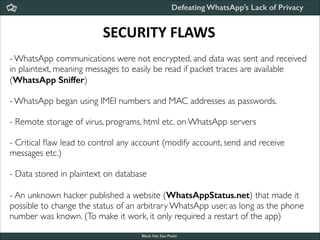
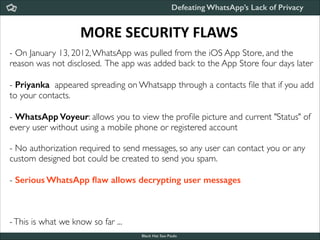
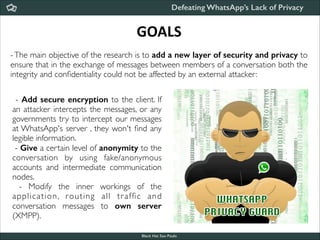
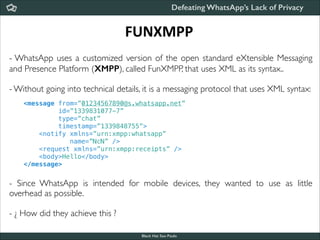
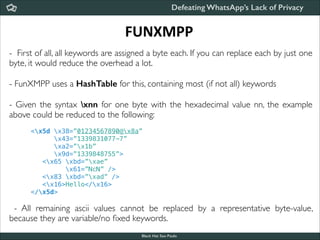
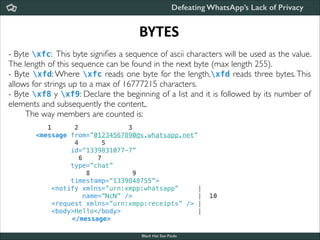
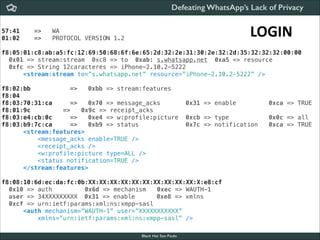
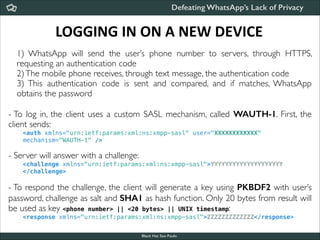
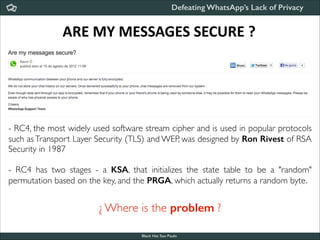
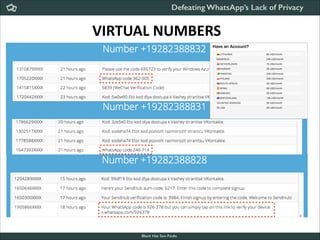
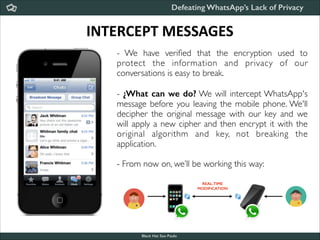
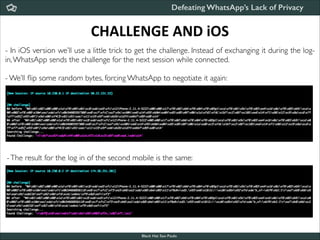
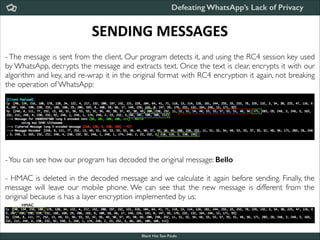
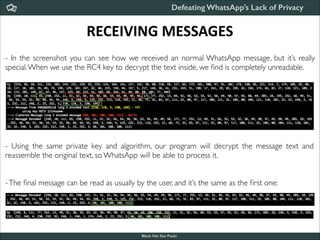
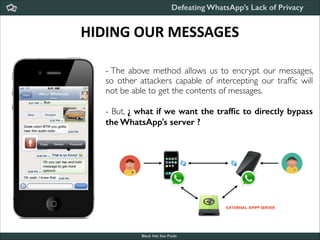
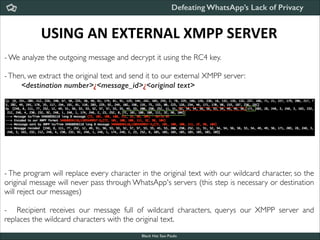
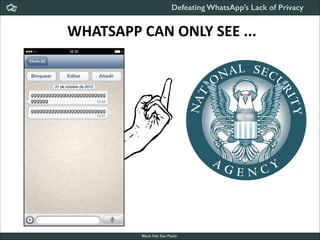
The document discusses security flaws in WhatsApp related to a lack of encryption of communications, metadata exposure, and discusses ways to add a new layer of security and privacy to WhatsApp messages by routing traffic through a custom server using encryption to protect the integrity and confidentiality of messages. It provides information on how WhatsApp's customized XMPP protocol works and how authentication is handled.