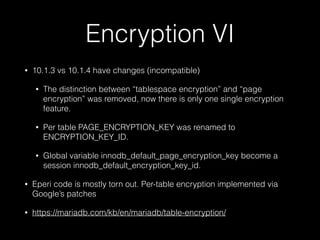
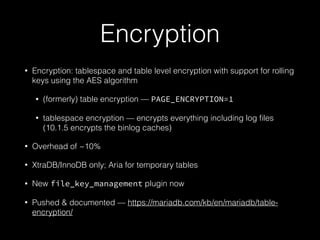
The document discusses essential security practices for using MariaDB and MySQL, highlighting improvements in encryption and authentication features in versions from 10.1 to 5.7. Key topics include user privileges management, SSL setup for secure connections, and password validation practices to enhance overall database security. It also covers installation considerations, auditing methods, and encryption mechanisms for data protection.
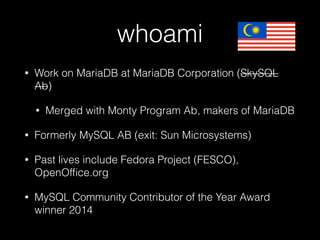
![Can you view privileges to
find a user with more access?
MariaDB [(none)]> SELECT host,user,password from mysql.user;
+--------------+-------------------+----------+
| host | user | password |
+--------------+-------------------+----------+
| localhost | root | |
| sirius | root | |
| 127.0.0.1 | root | |
| ::1 | root | |
| localhost | | |
| sirius | | |
+--------------+-------------------+----------+](https://image.slidesharecdn.com/betterencryptionsecuritywithmariadb10-151015214829-lva1-app6892/85/Better-encryption-security-with-MariaDB-10-1-MySQL-5-7-4-320.jpg)
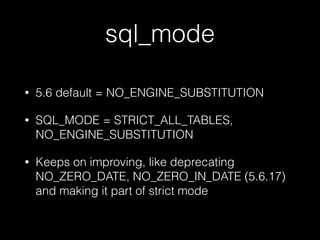

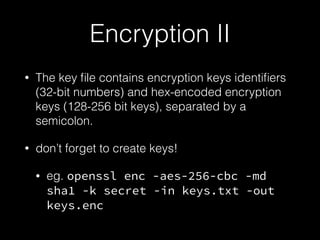
![my.cnf config
Configure [mysqld]
plugin-load-add=file_key_management.so
file-key-management
file-key-management-filename = /home/mdb/keys.enc
innodb-encrypt-tables
innodb-encrypt-log
innodb-encryption-threads=4
file_key_management_encryption_algorithm=aes_cbc
file_key_management_filename = /home/mdb/keys.enc
file_key_management_filekey = secret](https://image.slidesharecdn.com/betterencryptionsecuritywithmariadb10-151015214829-lva1-app6892/85/Better-encryption-security-with-MariaDB-10-1-MySQL-5-7-43-320.jpg)