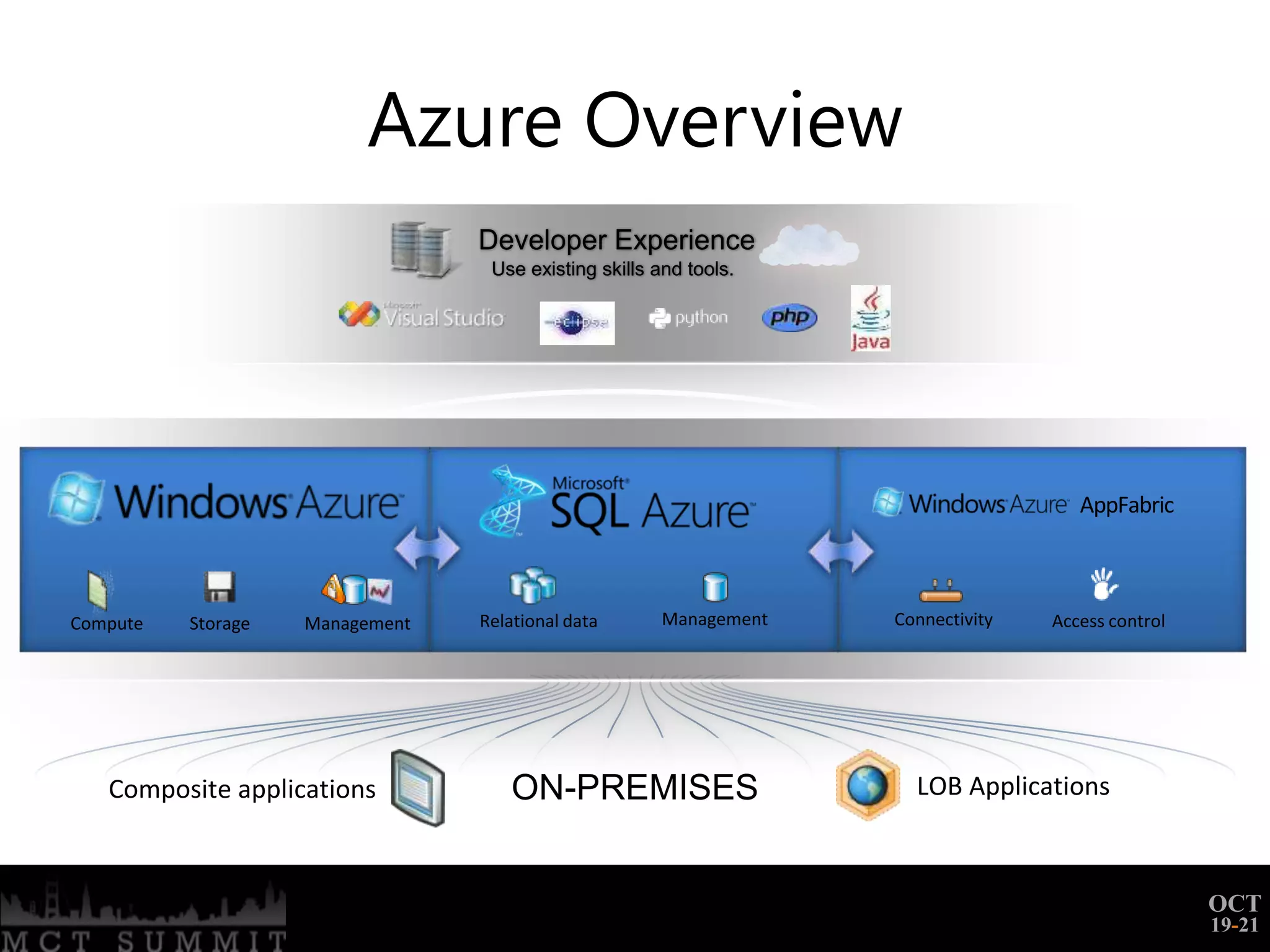
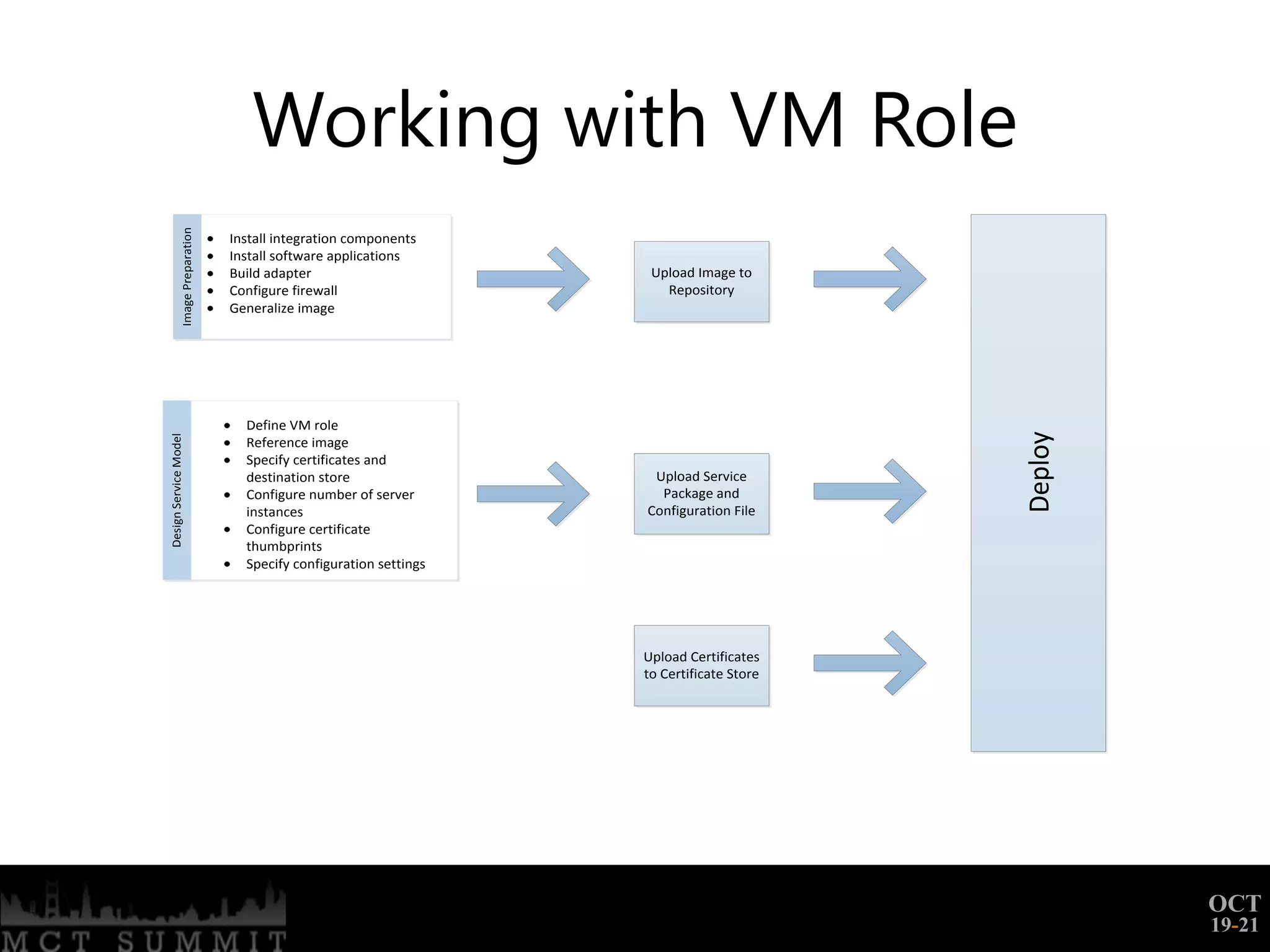
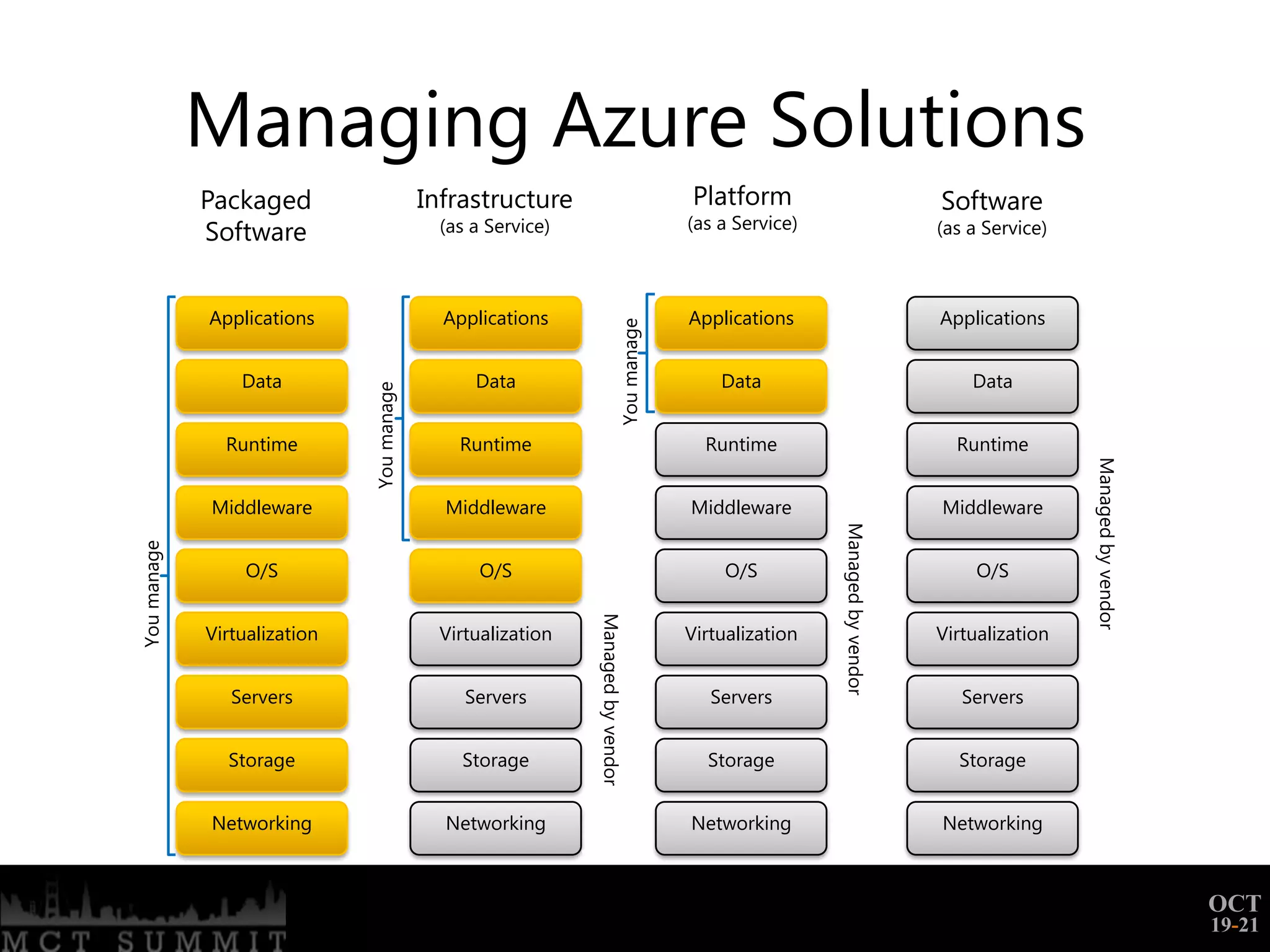
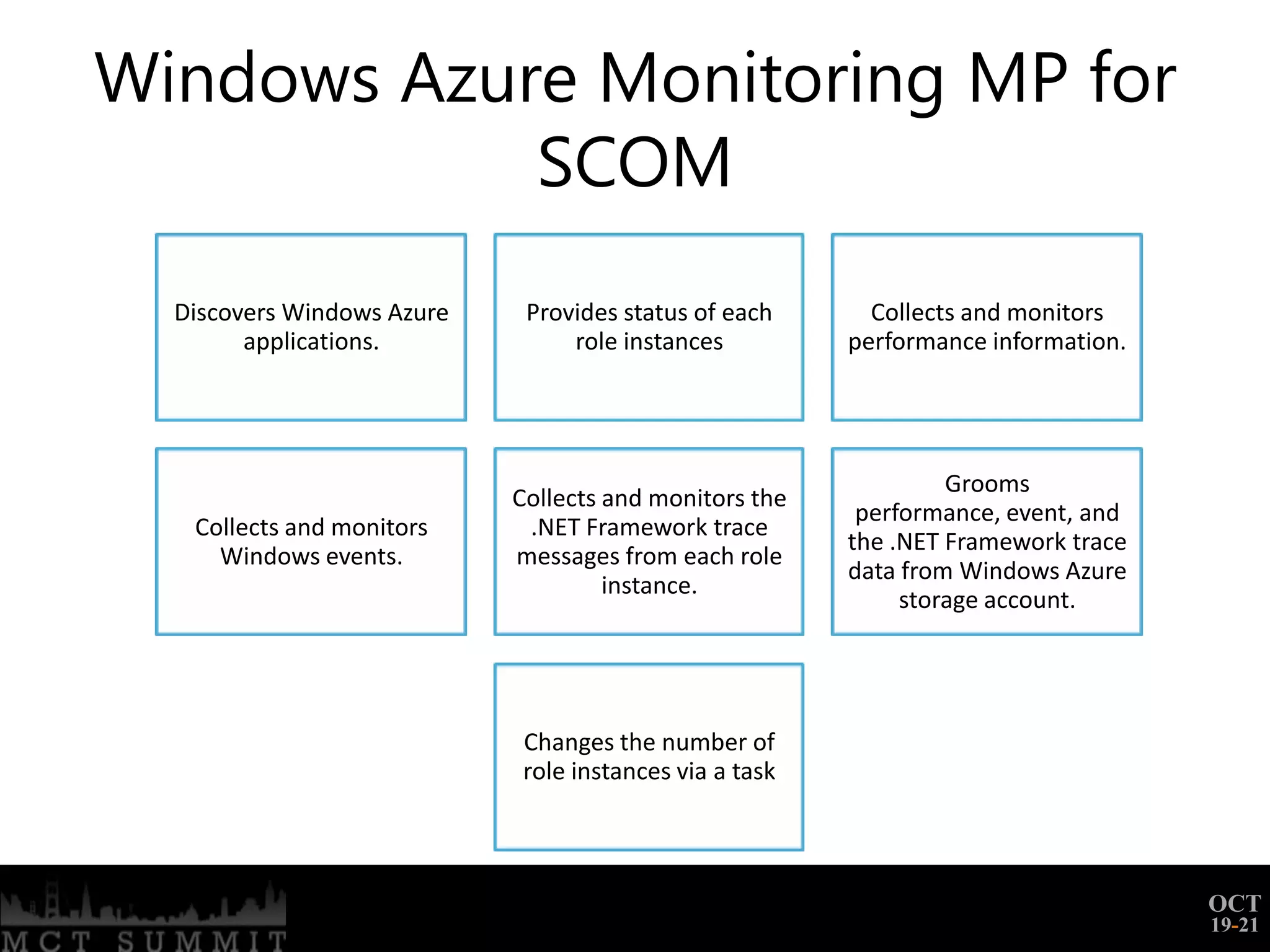
This document provides an agenda for a Windows Azure training session covering Azure Overview, Governance, Deploying Azure Solutions, Managing Azure Solutions, Monitoring Azure Solutions, and Extending to and from Azure. It includes demos and discusses topics such as deployment through the management portal and PowerShell, managing what components in Azure require administration, monitoring through diagnostics and System Center Operations Manager, and challenges of extending solutions beyond Azure.