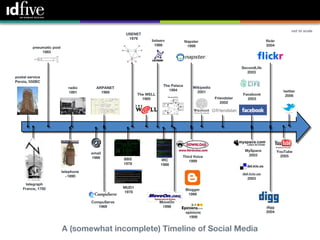
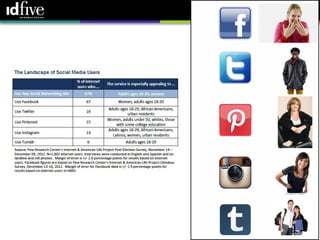
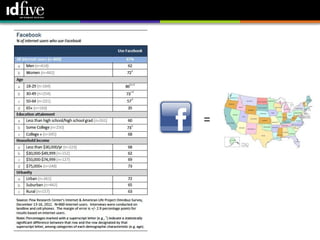
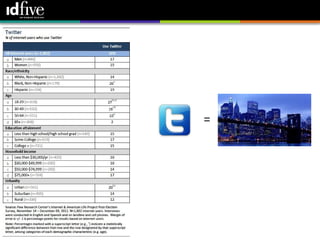
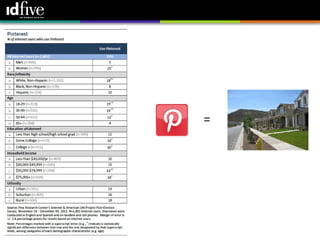
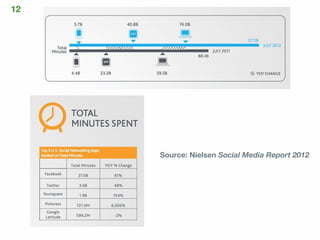
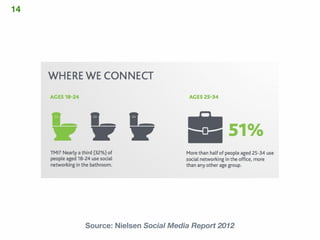
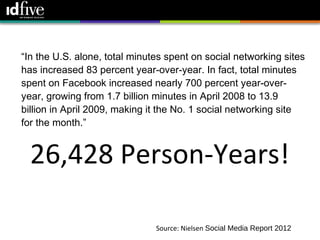
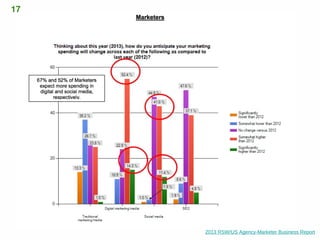
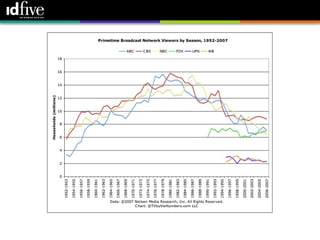
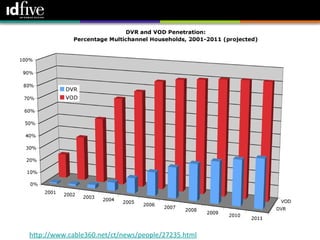
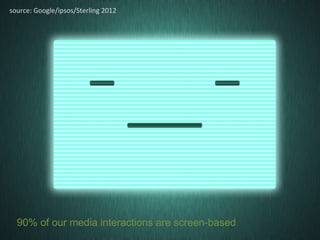
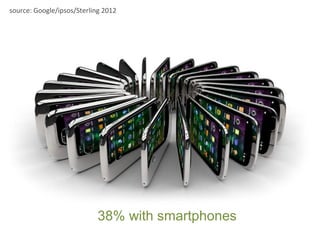
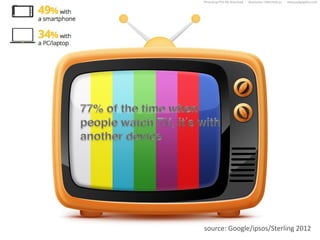
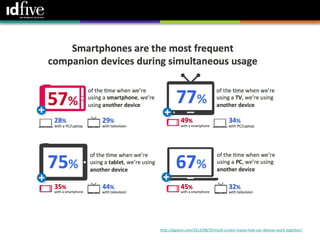
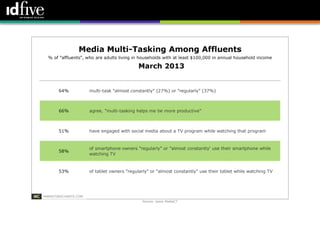
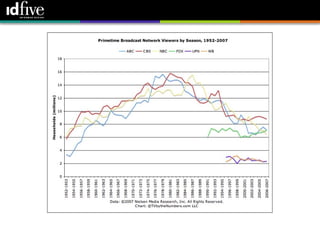
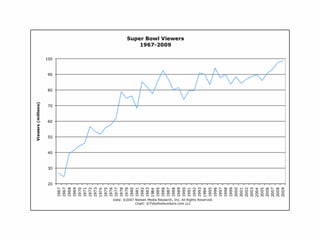
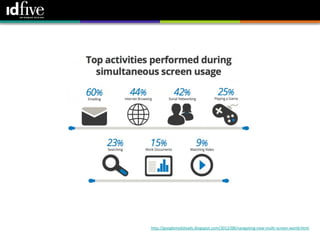
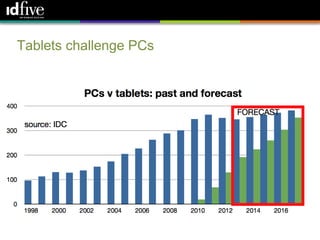
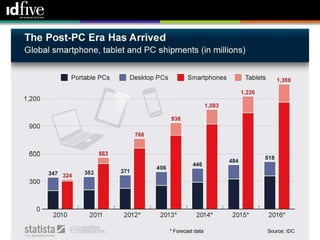
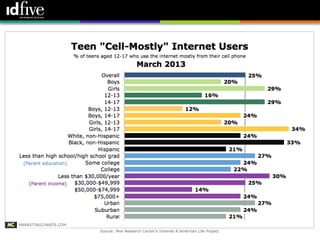
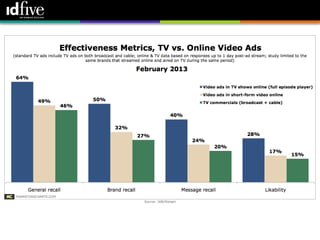
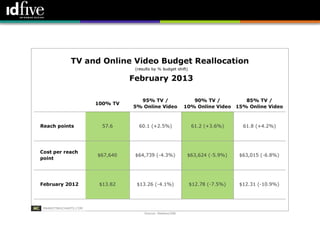
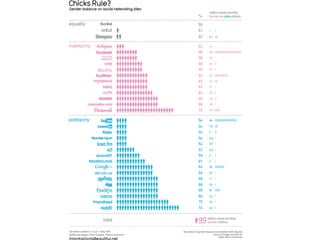
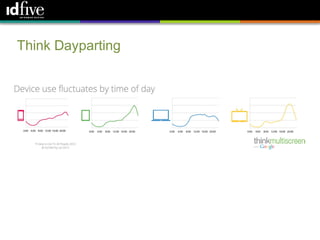
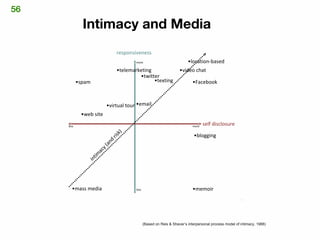
The document discusses the evolution and significance of social media, highlighting various platforms and their growth over time. It notes a substantial increase in user engagement, particularly on Facebook, and emphasizes the importance of understanding consumer behavior in a multi-screen environment. Additionally, it explores content creation and consumption, suggesting strategies for effective media interaction.