Embed presentation
Download to read offline
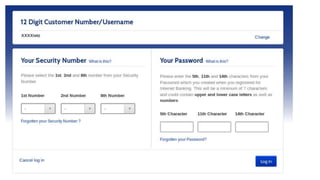
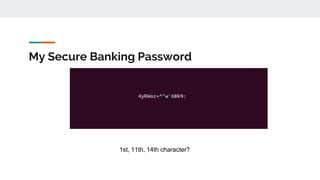
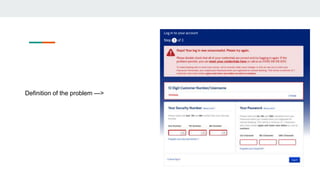
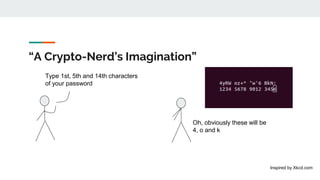
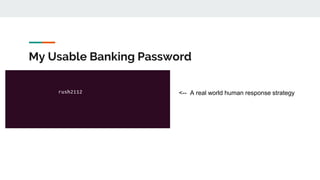
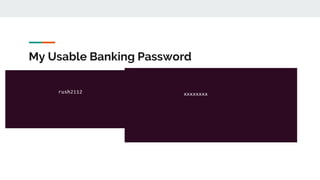
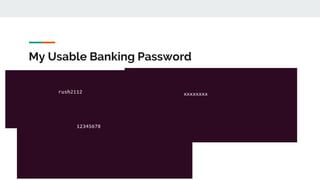
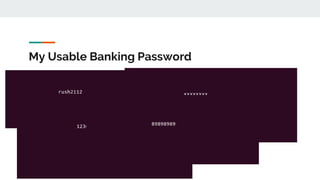
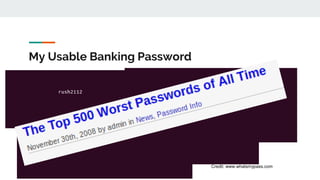


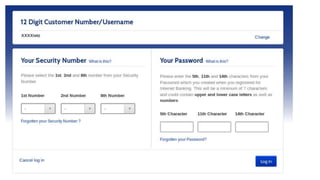
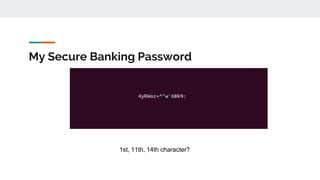
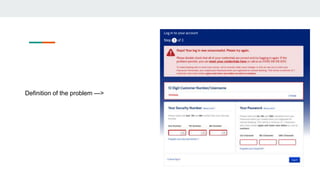
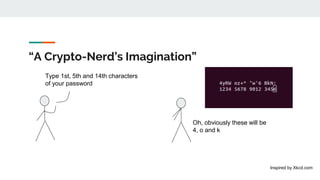
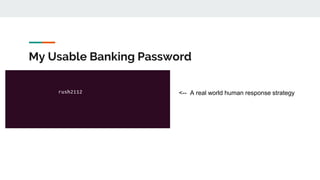
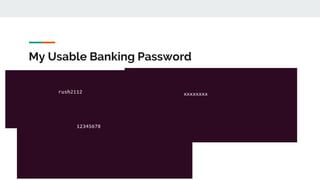
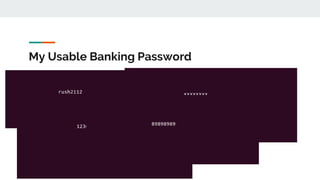
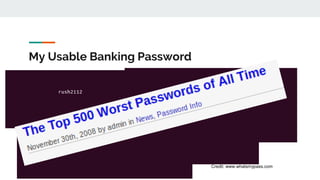
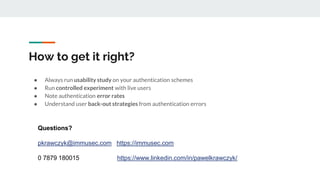
The document discusses issues surrounding password usability and security, criticizing existing practices like blocking password managers and limiting character entry. It suggests improvements such as using simple text fields and adopting more secure authentication methods like fingerprints and U2F. It emphasizes the importance of conducting usability studies and understanding user behavior related to authentication errors.