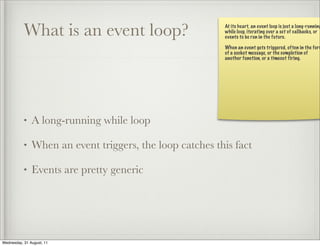
This document discusses asynchronous programming using Python. It begins with introductions and discusses some of the buzzwords around asynchronous programming like Node.js, Tornado, and event loops. It then provides a brief history of threading, multiprocessing, and asynchronous programming. It defines what an event loop is and discusses concepts like callbacks and deferreds. It notes that asynchronous code is generally harder to write and can be slower than synchronous code. However, asynchronous programming allows for greater scalability by avoiding threads and shared state.