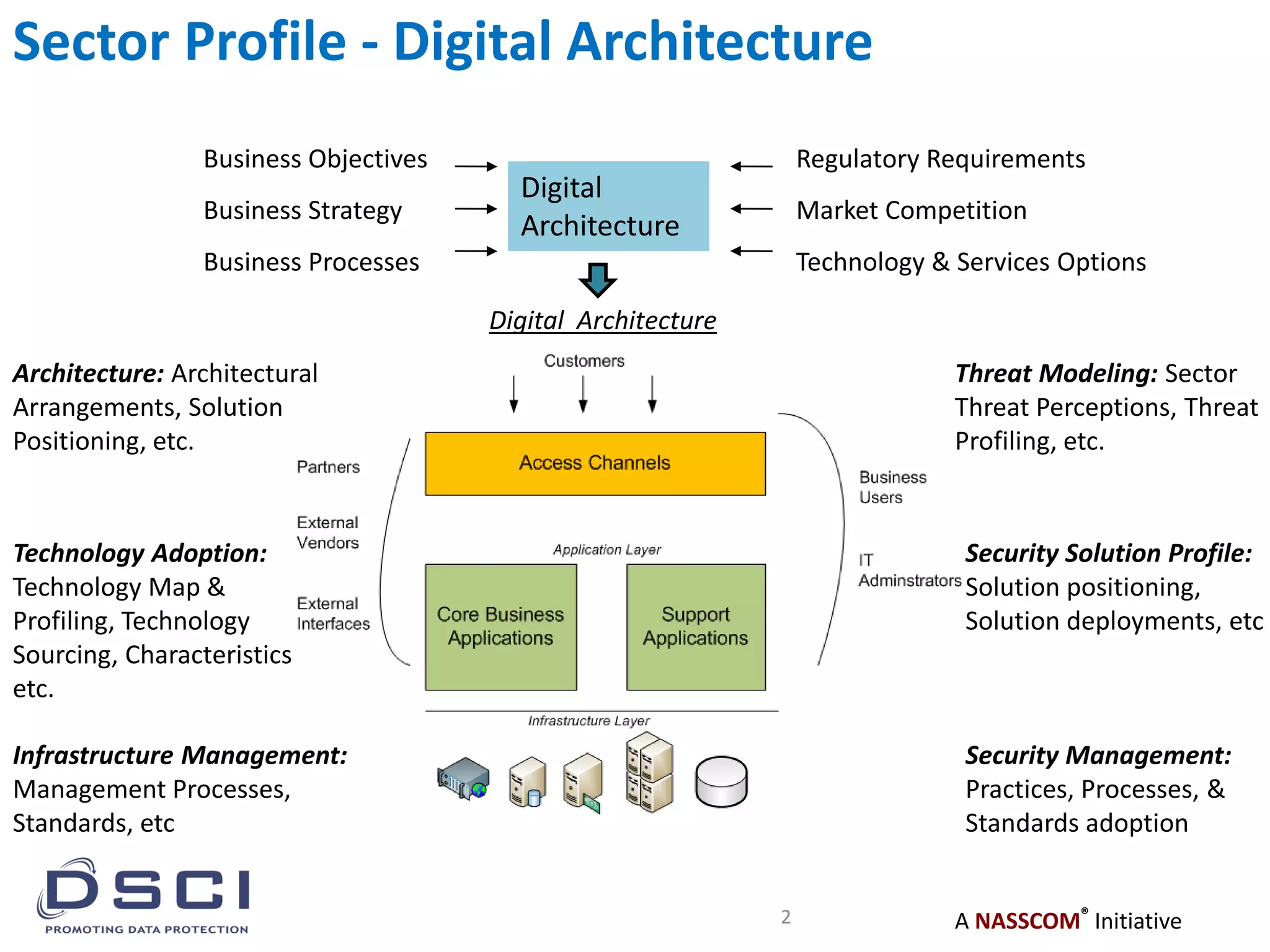
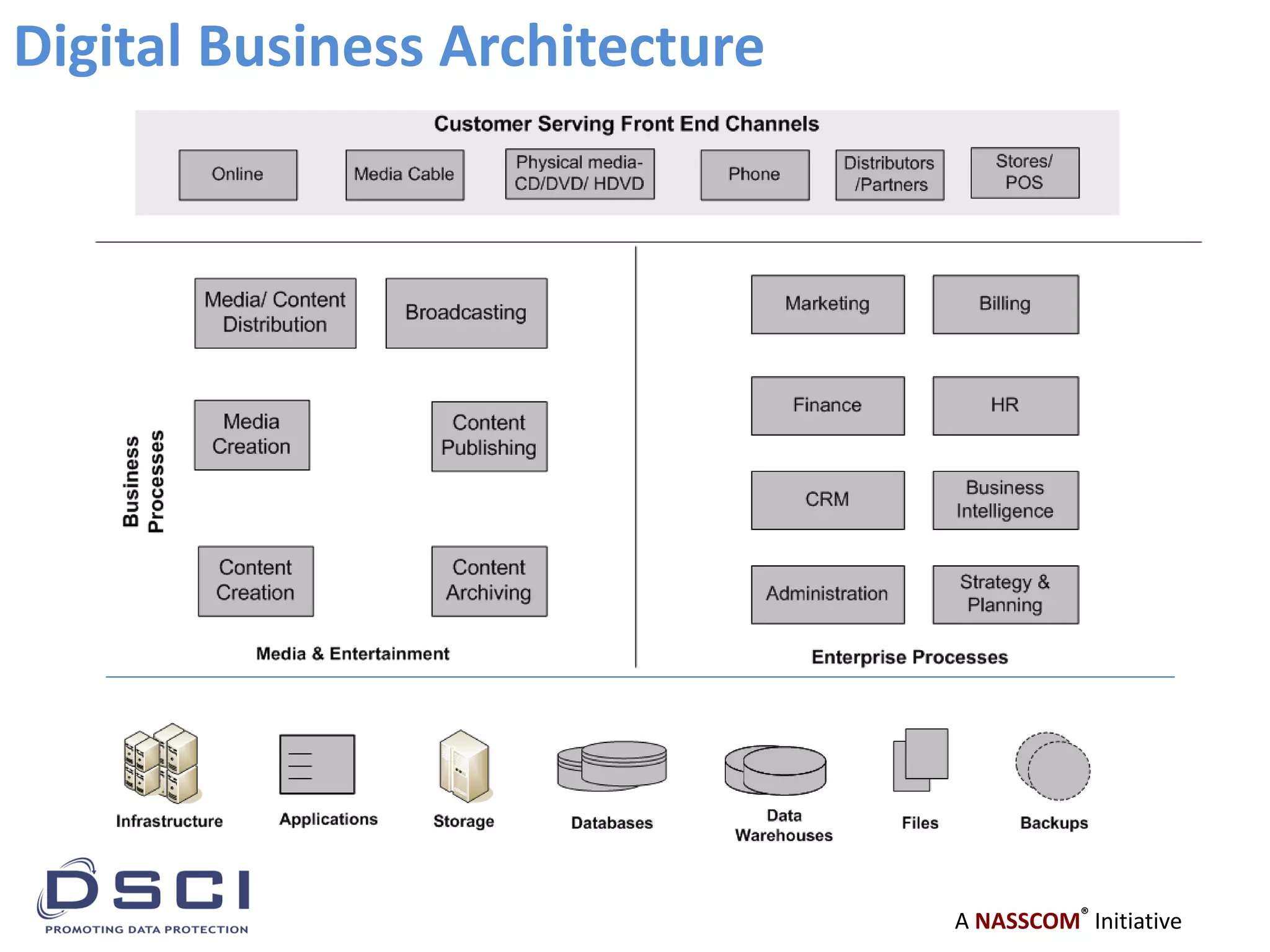
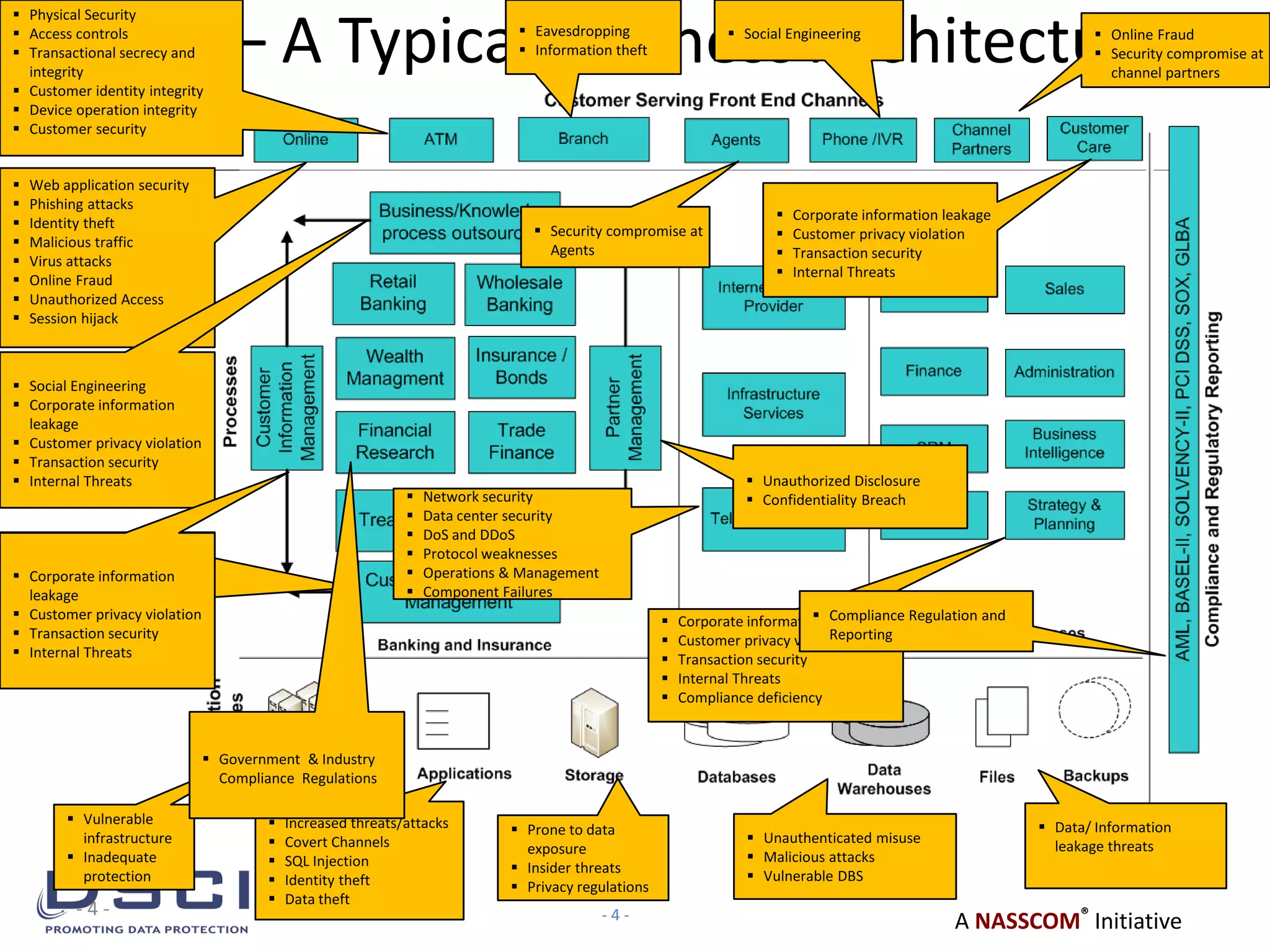
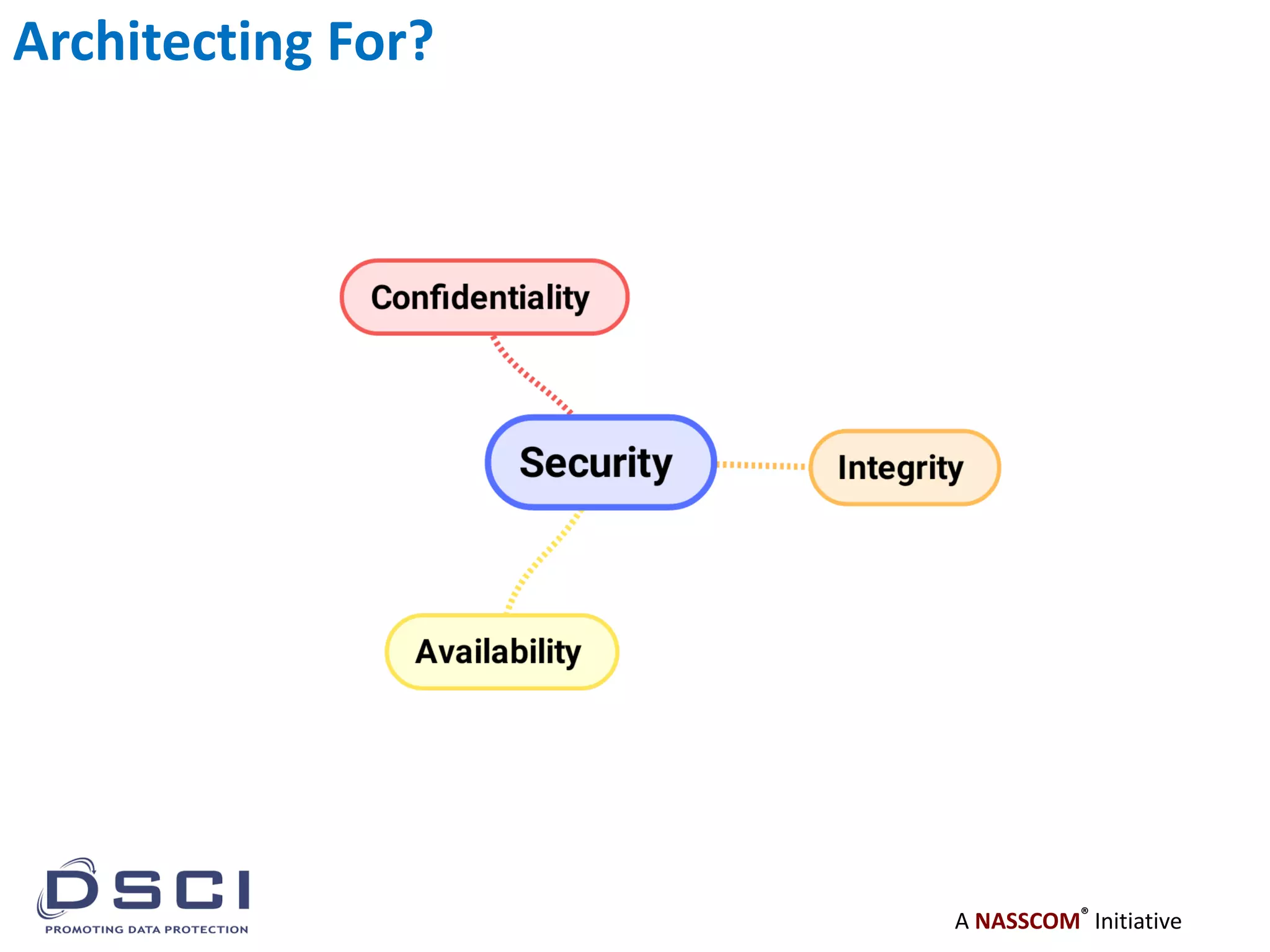
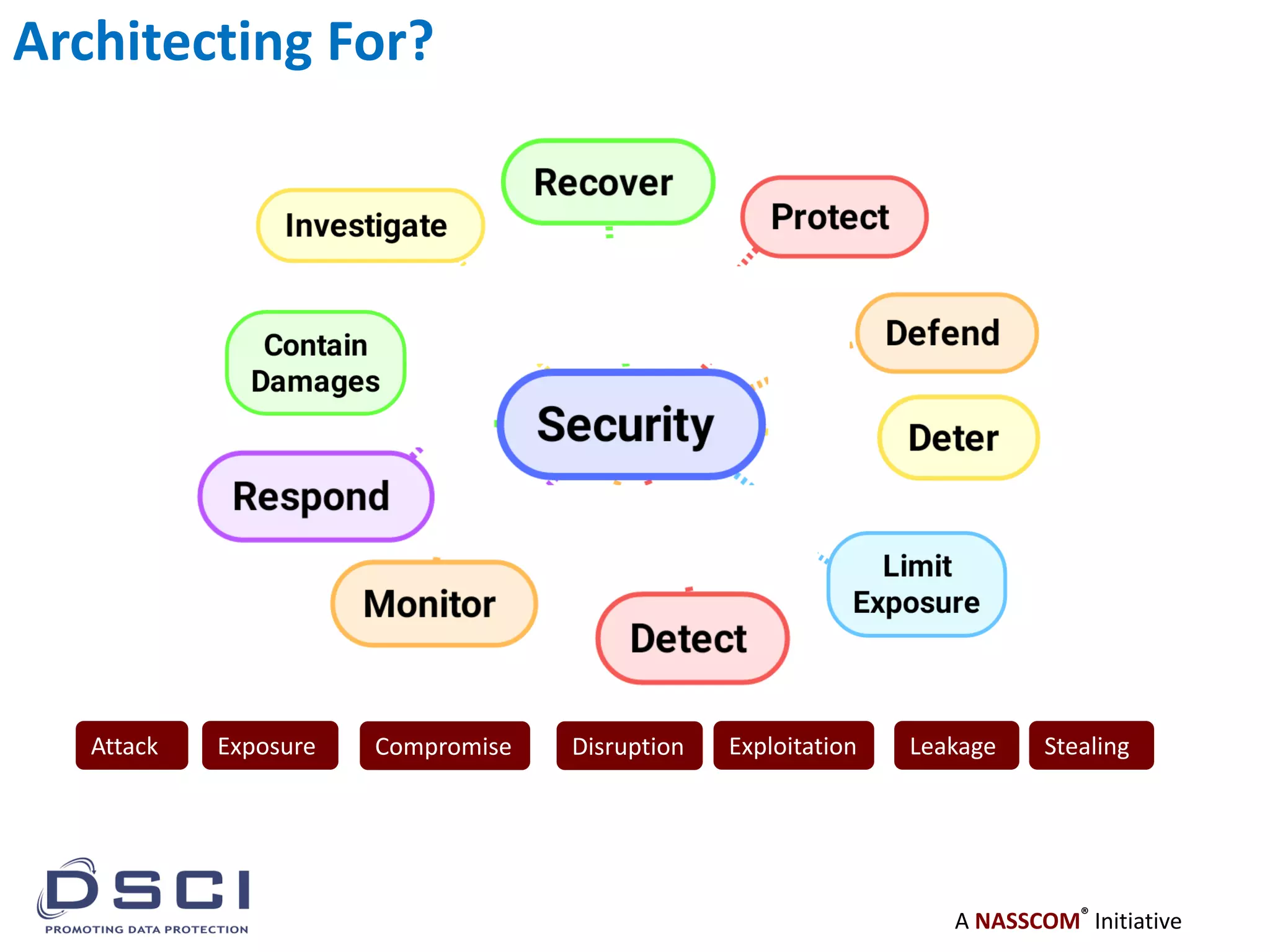
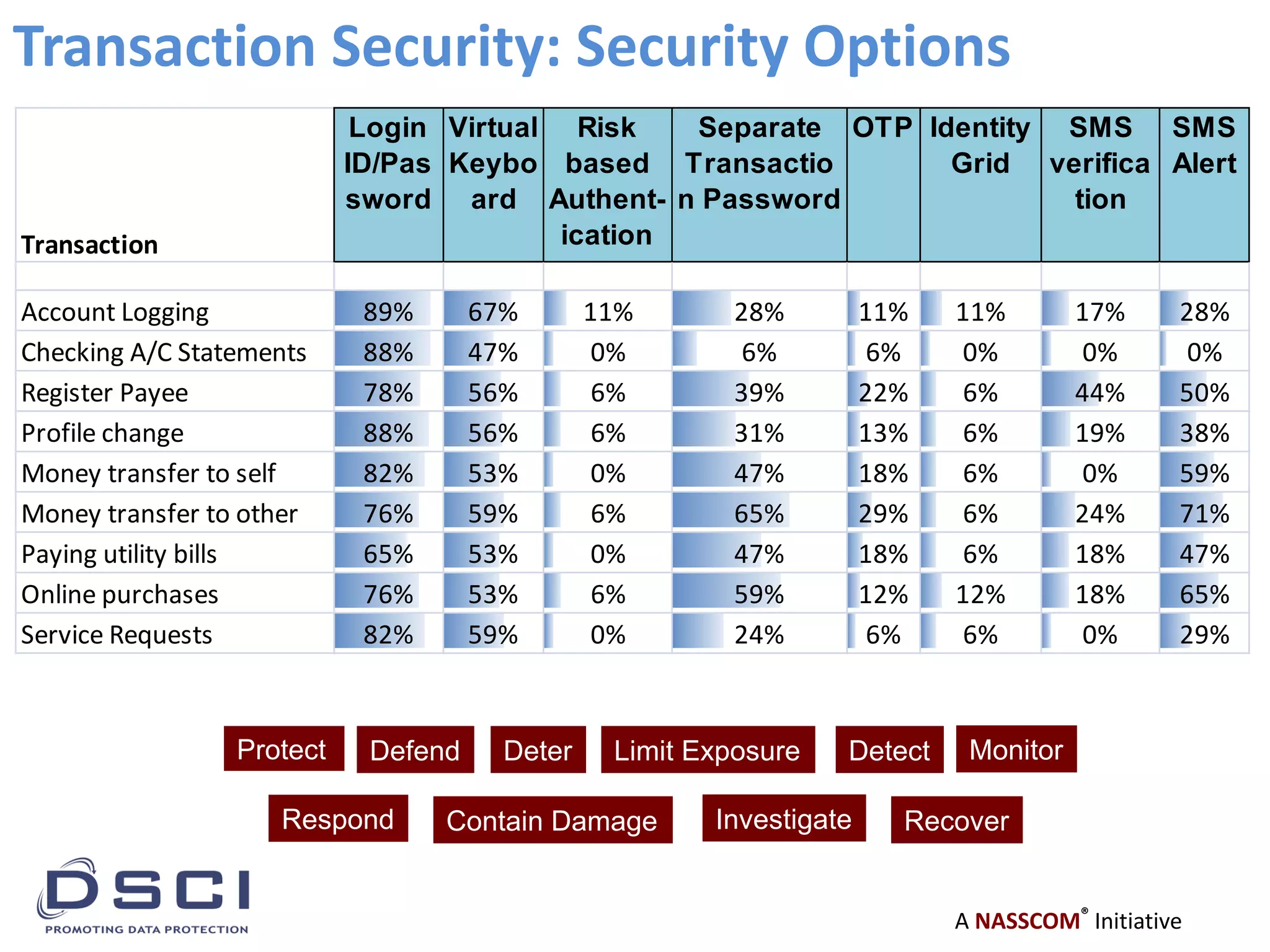
This document discusses transitioning from business architecture to security architecture. It provides an overview of key aspects of digital architecture like technology adoption, infrastructure management, threat modeling, and security solutions. It then discusses how a typical business architecture in the banking/finance sector (BFSI) can involve many threats across various areas. These threats need to be addressed through proper security architecture and controls. Finally, it analyzes security options for transactions and how they can help protect, defend, deter, limit exposure, detect issues, monitor activities, respond to incidents, contain damage, investigate problems, and aid recovery.