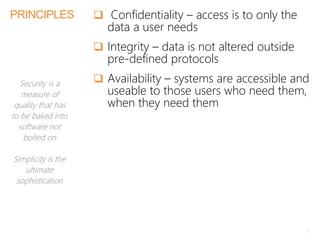
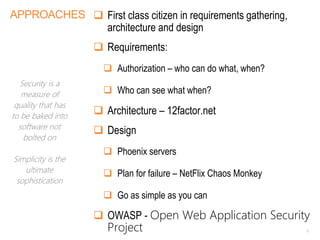
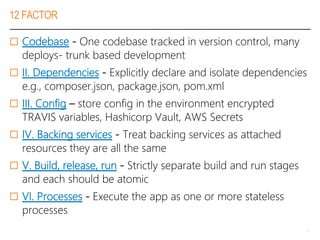
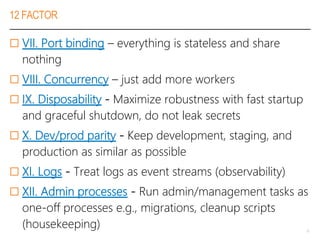
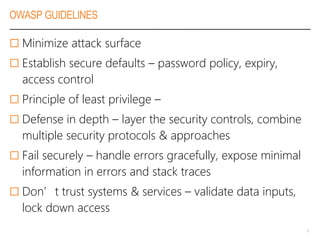
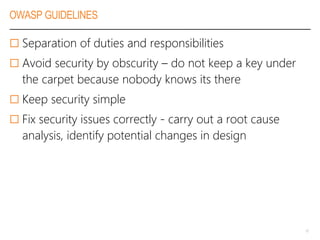
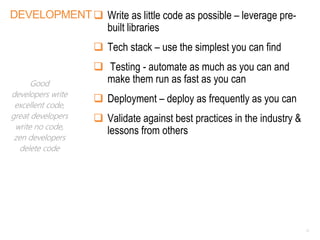
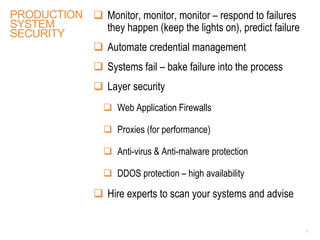
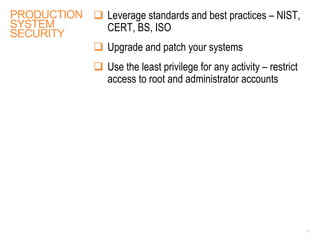
The document emphasizes the importance of integrating security into software development processes rather than treating it as an afterthought. It discusses principles such as confidentiality, integrity, and availability, alongside guidelines from OWASP for minimizing vulnerabilities. Ultimately, it highlights that security is a continuous responsibility requiring expertise and adherence to established best practices.