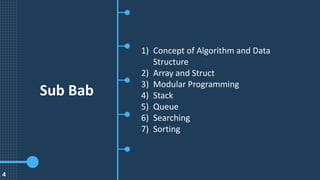
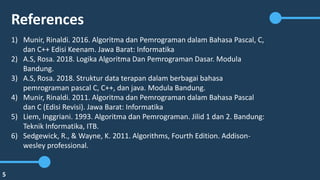
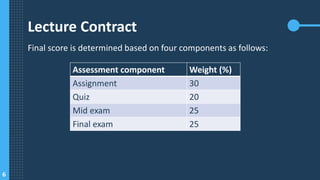
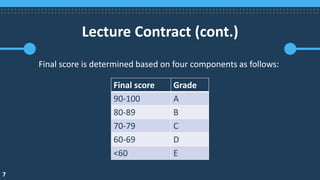
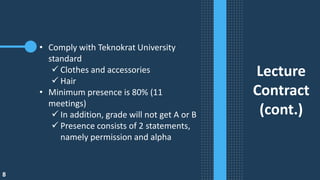
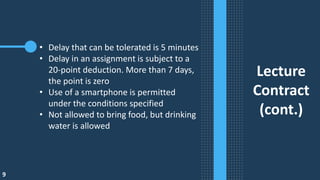
Dokumen ini membahas tentang algoritma dan struktur data yang mencakup konsep dasar, seperti array, struct, pemrograman modular, tumpukan (stack), antrian (queue), pencarian, dan pengurutan. Penilaian akhir berdasarkan komponen tugas, kuis, ujian tengah semester, dan ujian akhir dengan bobot tertentu, serta beberapa peraturan terkait kehadiran dan pengumpulan tugas. Referensi utama untuk studi ini berasal dari buku-buku tentang algoritma dan pemrograman dalam berbagai bahasa.