Algebra lab.module1.lesson5.posandneg
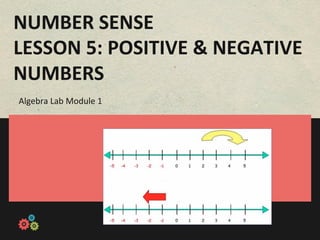
- 1. NUMBER SENSE LESSON 5: POSITIVE & NEGATIVE NUMBERS Algebra Lab Module 1
- 2. -‐-‐-‐-‐-‐-‐ -‐-‐-‐-‐-‐-‐ Launch You will review previous lessons in the module and begin to think about posi:ve and nega:ve integers. -‐-‐-‐-‐-‐-‐ -‐-‐-‐-‐-‐-‐ Morphology You will learn more about how to find the most meaningful parts of words. Investigation 3 -‐-‐-‐-‐-‐-‐ -‐-‐-‐-‐-‐-‐ You will watch two videos about positive and negative Investigation integers and how they are relevant in real life. In this ac:vity, you will get up out of your seat and embody -‐-‐-‐-‐-‐-‐ posi:ve and nega:ve numbers. By playing the role of Modeling -‐-‐-‐-‐-‐-‐ posi:ve or nega:ve, this game will teach you how posi:ve and nega:ve numbers affect each other. In this ac:vity, you will prac:ce adding and subtrac:ng posi:ve and nega:ve numbers. You will learn other -‐-‐-‐-‐-‐-‐ -‐-‐-‐-‐-‐-‐ Synthesis characteris:cs of posi:ve and nega:ve numbers through a true/false ac:vity. Lesson Activities 1 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers
- 3. Pos:ve and Nega:ve Number Synthesis You will reflect on whether or not it is valuable to manually add and subtract posi:ve and nega:ve numbers, even when you have a calculator within reach. You are ready to start the series of ac:vi:es on Posi:ve and Nega:ve Numbers… Small-scale Performance 2 Small-scale Performance 2 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 4. Descrip:on You will review the previous lessons and then begin to think about p osi:ve and nega:ve integers. Launch! 3 Launch!!! 5 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 5. Launch Review! Answer the following review questions in your Springnotes. 1. What place is the seven in? 245.678 2. Round this number to the nearest hundred. 32,990 3. Write this number in words. 5.006 Launch Review! 4 Launch!!! 5 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 6. Launch! 1. If you borrowed six dollars from Steve for some pizza, two dollars from Angelo for a soda, and three dollars from Michelle for a cookie, how much money will you owe in total? 2. Is there a math sign you can use to show that this is money owed, not money you actually have? Launch! 5 Launch!!! 5 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 7. Descrip:on This ac:vity will help you to iden:fy the most meaningful parts of words. This will deepen your understanding of a word and its related forms. Morphology Investigation 3 6 Launch!!! 5 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 8. READ, LOOK UP, DISCUSS 1. In your group, look at and read your 4. See if you can find other words that -‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐ words. Discuss what they might mean. contain some of the same morphemes. Think of everything you already know about the words. 5. Figure out the history of each morpheme. What language does it come from? Has it 2. Use the etymology, word-‐root always meant the same thing? What dic:onaries, and any other sources you other words have this morpheme? want in order to figure out the morphemes that make up this word. 6. Discuss how the morphemes word together to create the meaning of the 3. Figure out what each morpheme means. word. Can the morphemes help you remember how to spell the word? 7. Present one of your words to the class. Morphology Investigation 3: Steps 7 Note taking: Steps 9 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 9. How can knowing How are words word parts help us formed in to learn new different words? languages? How can it help What is a us to deepen our What are the word? understanding of different parts words we of a word? already knew? Metacognition 8 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers
- 10. Descrip:on You will connect principles of positive and negative integers to real life scenarios. Investigation 9 Investigation 11 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 11. WATCH & DESCRIBE 1. You will now watch two videos rela:ng to posi:ve and nega:ve integers. 2. When you are done, think of and describe at least one addi:onal example of where you see nega:ve numbers in your life. Click on the links below: Investigation: Steps 10 10 Algebra Lab Module 1 / LLesson 2: Rounding Nega:ve Numbers Algebra Lab Module 1 / esson 5: Posi:ve and
- 12. Descrip:on You will explore the effect nega:ve numbers have on problems, as well as how nega:ve numbers are represented in the real world. Modeling 11 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers
- 13. MOCK BATTLE -‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐ 1. You will be par:cipa:ng in the "Ba^le of posi:ve vs. nega:ve.” 2. Your teacher will first model the ac:vity and then you will work on the problems together as a whole class before branching off to do individual work. Modeling: Steps 12 Note taking: Steps 9 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 14. METACOGNITIVE QUESTION How does this ac:vity help you "visualize" combining posi:ve and nega:ve numbers? What did you no:ce about the meaning of the addi:on symbol and the subtrac:on symbol in the problems? Metacognition 13 Note taking: Metacognition 10 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 15. Descrip:on You will practice adding and subtracting positive and negative integers. Synthesis 14 Investigation 11 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers Algebra Lab Module 1 / Lesson 2: Rounding
- 16. PRACTICE a) Without using a calculator, b) Determine whether each statement is true or prac:ce simplifying the false and explain why. following: -‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐-‐ -‐9 + 4 = i. The sum of two posi:ve integers is always posi:ve. -‐5 + -‐3 = ii. The sum of two nega:ve integers is always posi:ve. -‐2 + 6 = iii. The sum of a nega:ve integer and a posi:ve integer is always nega:ve. -‐2 – 4 = iv. The sum of a nega:ve integer and a posi:ve integer is always 5 – 8 = posi:ve. 7 – 10 = Synthesis 15 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers
- 17. Did you think differently when you had to answer ques:ons in words, as opposed to just using numbers and math symbols? If so, how? Where did the pa^erns you found fit with the statements and where did they contradict them? + or -‐ Metacognition 16 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers
- 18. REFLECTION ON THE MATH Your teacher will give you a link to wall wisher for the following ques:ons. Be prepared to share out your thoughts. 1. Now that we have calculators readily accessible to us, explain why it is valuable to know how to manually add and subtract nega:ve and posi:ve integers? REFLECTION 17 Algebra Lab Module 1 / Lesson 5: Posi:ve and Nega:ve Numbers