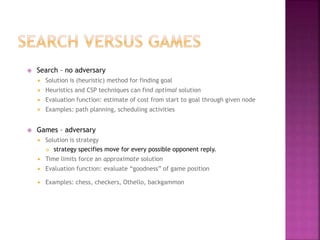
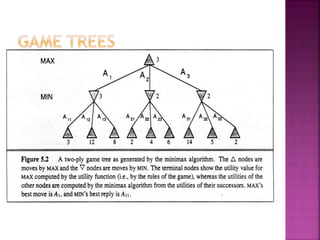
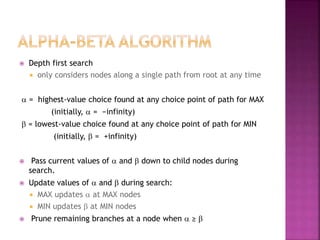
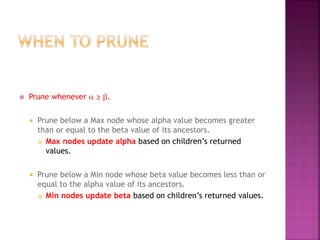
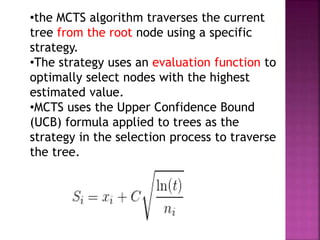
The document discusses game theory and algorithms for game playing in artificial intelligence, including minimax, alpha-beta pruning, and Monte Carlo tree search. Minimax is a decision-making algorithm that works by choosing the option that maximizes the minimum payoff. It assumes both players play optimally. Alpha-beta pruning improves on minimax by pruning branches that cannot affect the outcome. Monte Carlo tree search is a technique that builds a search tree using random simulations rather than exhaustive search.























































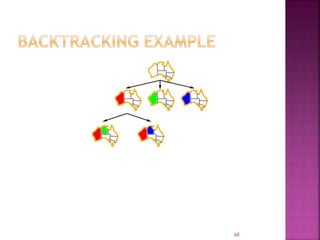






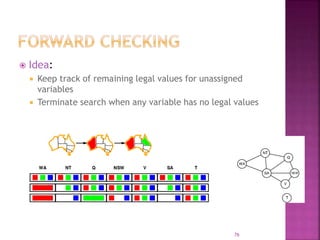





















![ Comment on Backtracking and look ahead
strategies (forward)in constraint
satisfaction problems. [6]
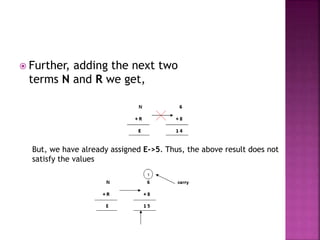
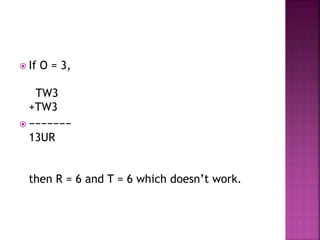
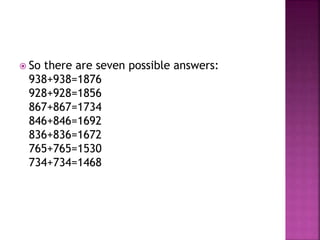
Apply crypt arithmetic to solve the problem
and represent the state search space to solve
,TWO+TWO=FOUR (OCT2019)](https://image.slidesharecdn.com/aiunit3-220919042900-55e42d22/85/AI_unit3-pptx-100-320.jpg)