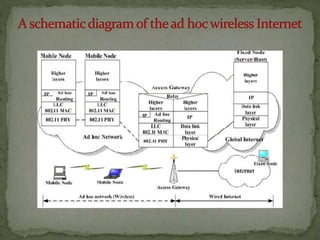
This document discusses ad hoc and wireless sensor networks. It describes several applications of ad hoc networks including military operations, collaborative work, emergency response, and wireless mesh networks. It also discusses wireless sensor networks and their use in fields like healthcare, environmental monitoring, and more. Finally, it outlines some of the major challenges in designing routing protocols for ad hoc networks such as mobility, bandwidth constraints, and resource limitations.