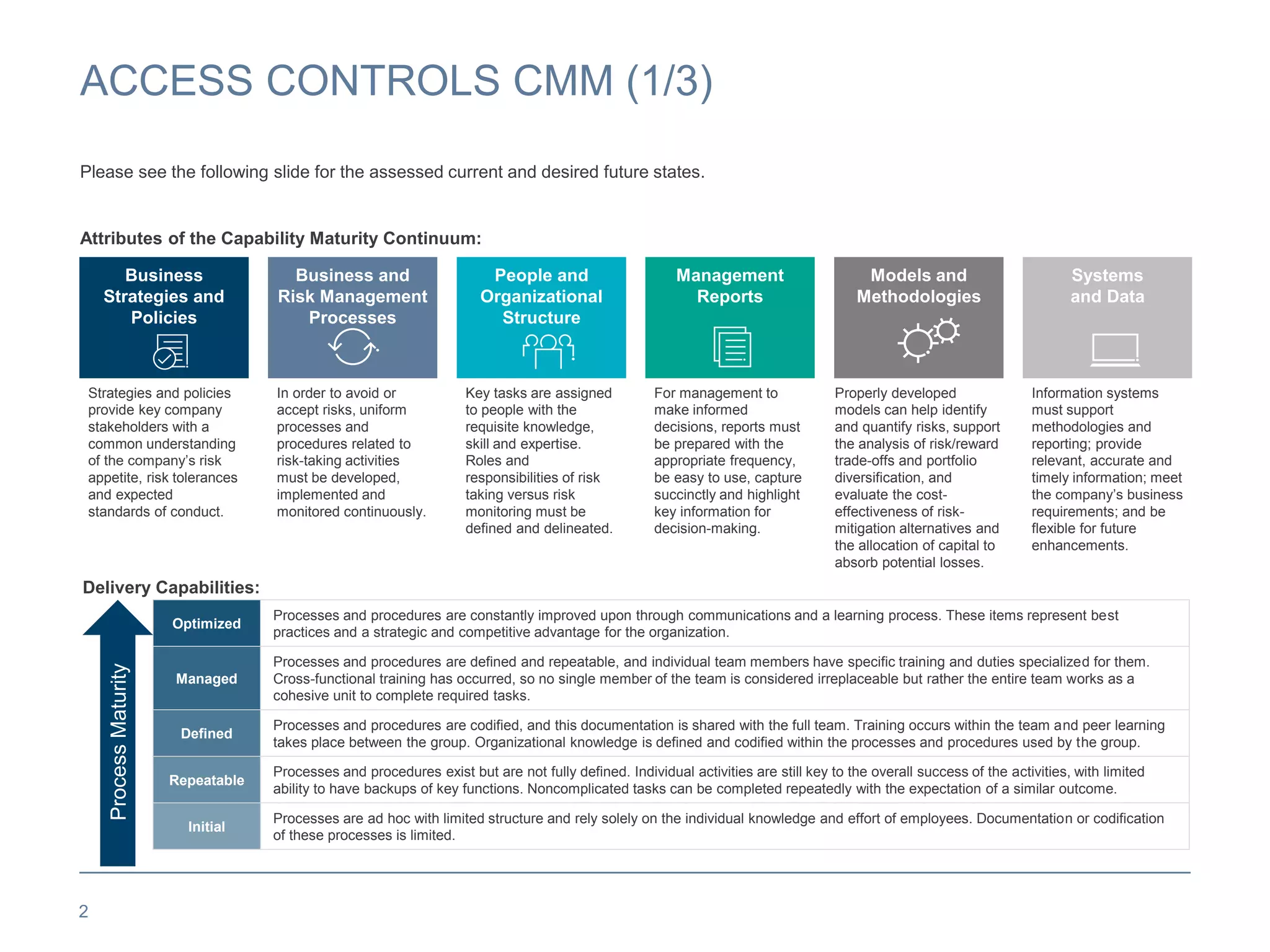
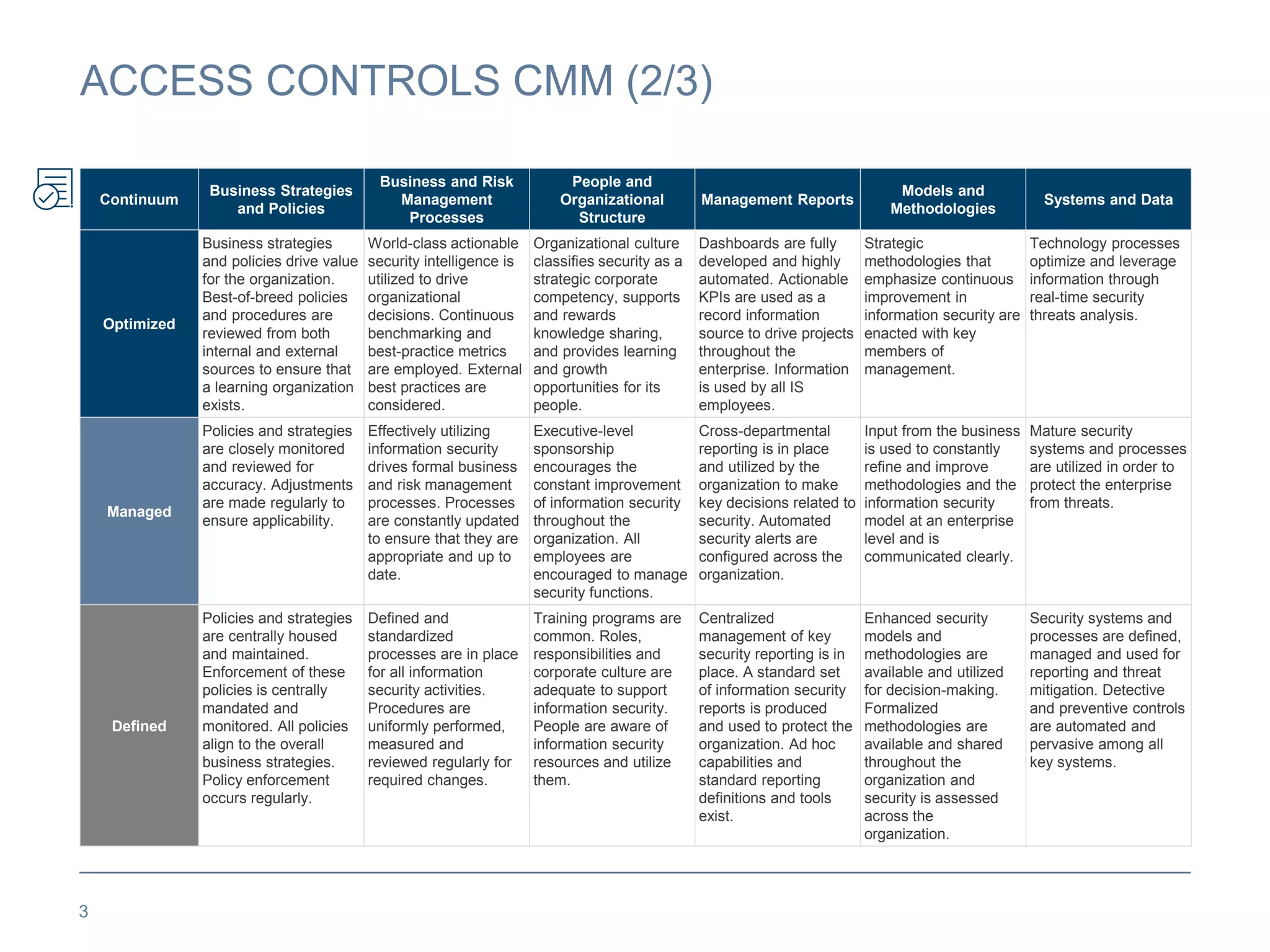
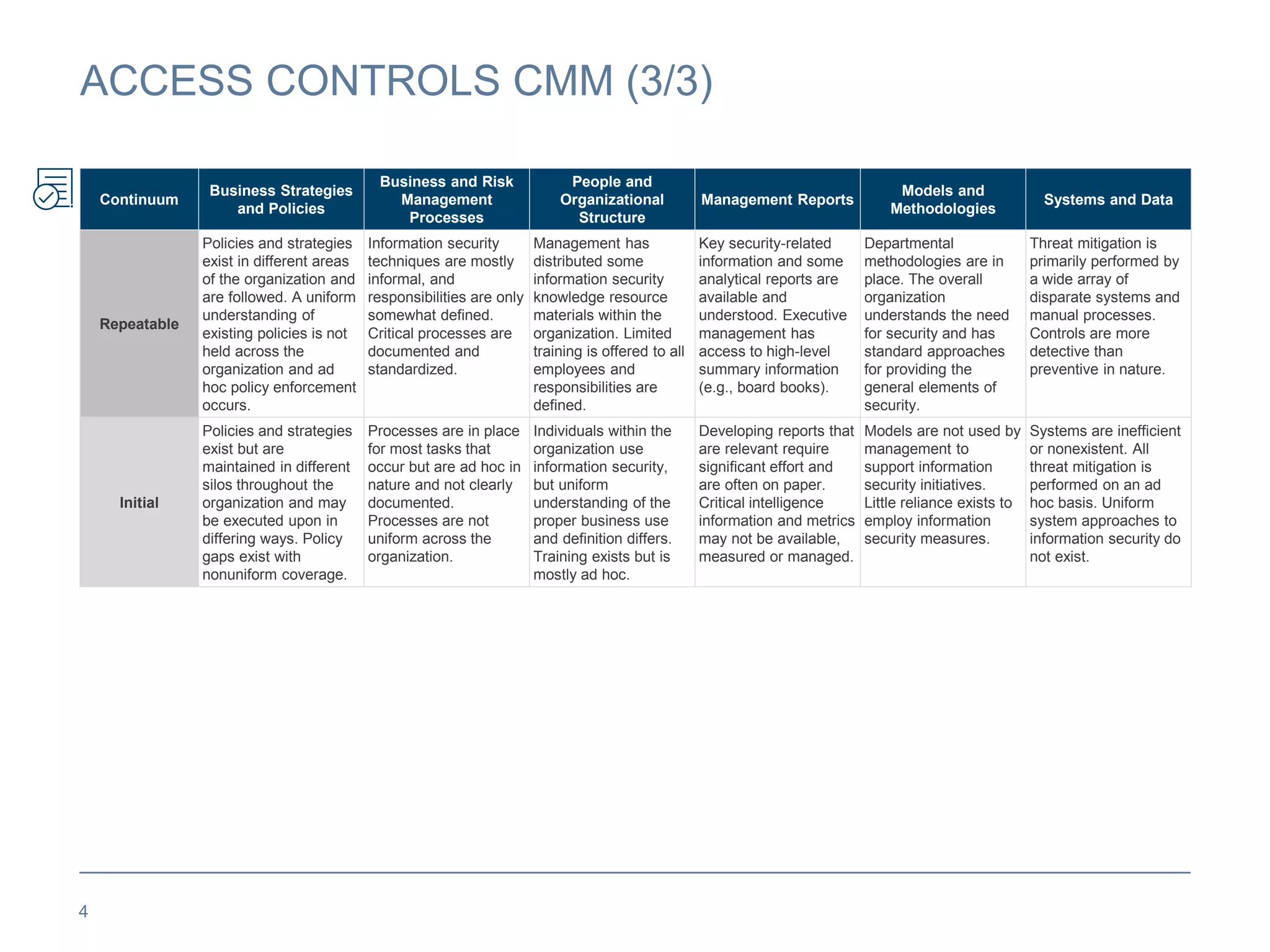
This document describes the Capability Maturity Model (CMM) for access controls. It outlines five levels of process maturity for key areas related to access controls: initial, repeatable, defined, managed, and optimized. For each level, it provides details on how business strategies and policies, business processes, organizational structure, management reports, methodologies, and systems/data would demonstrate that level of process maturity for access controls. The overall CMM aims to help organizations improve their access control processes by advancing through these defined levels of increasing maturity.