Embed presentation

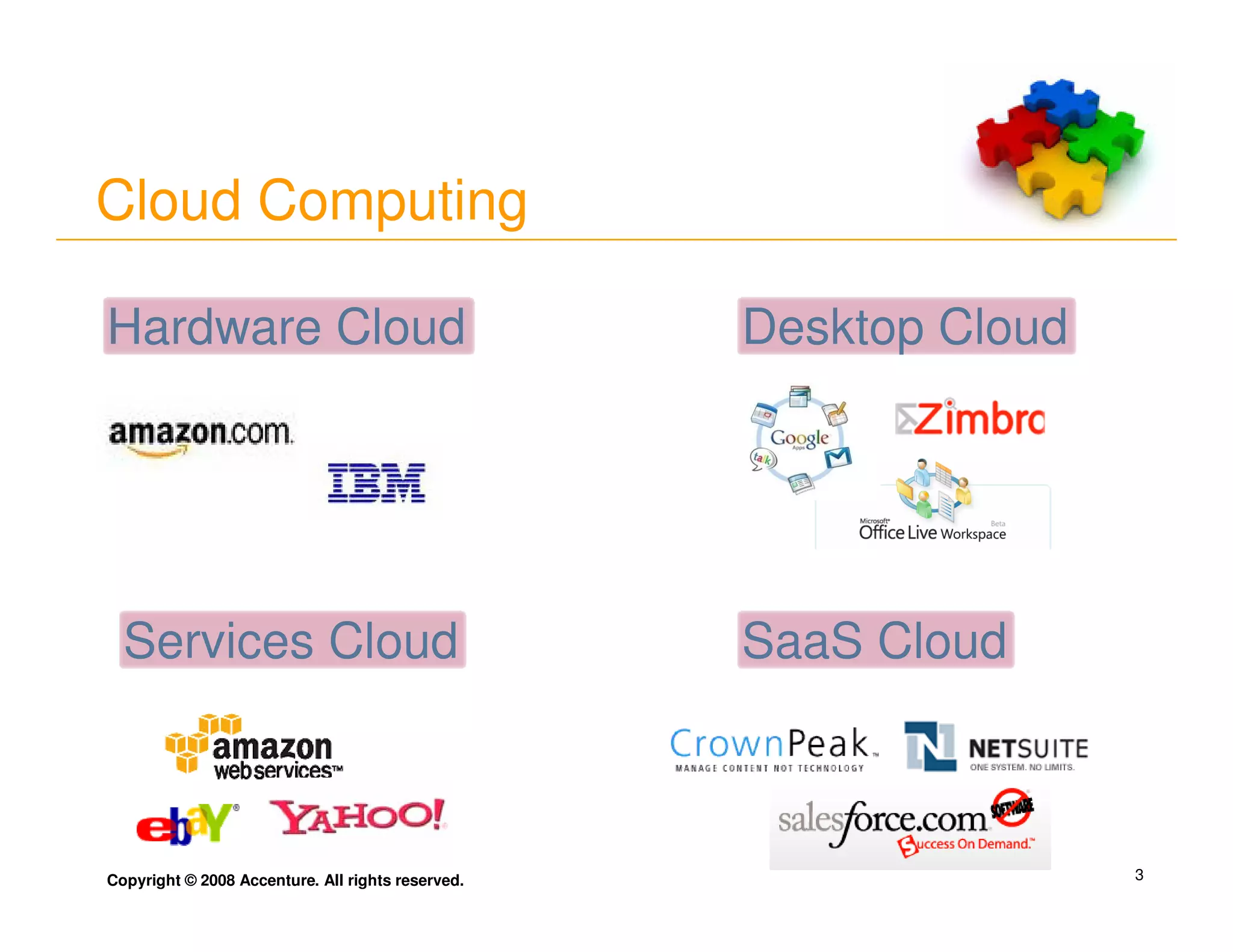
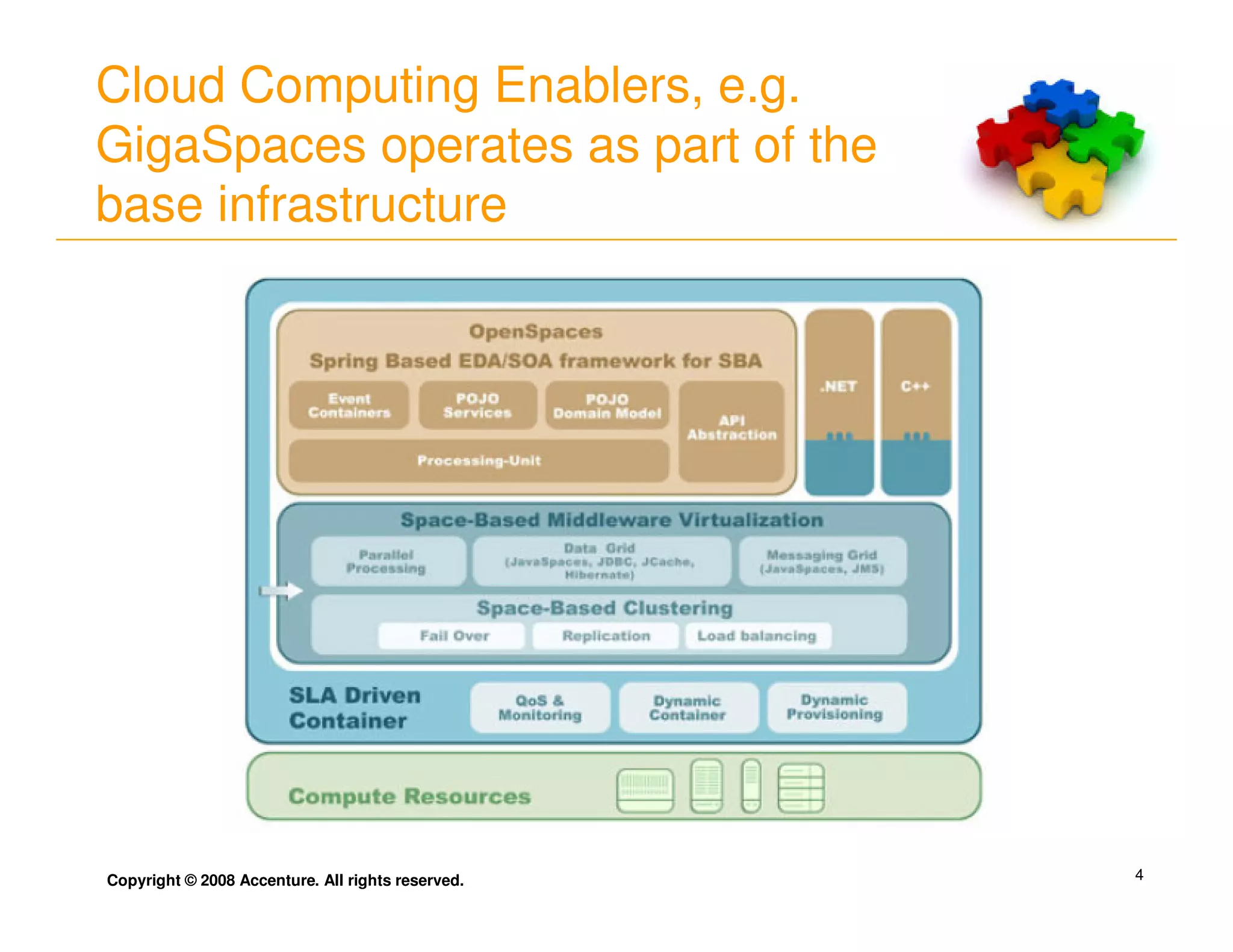
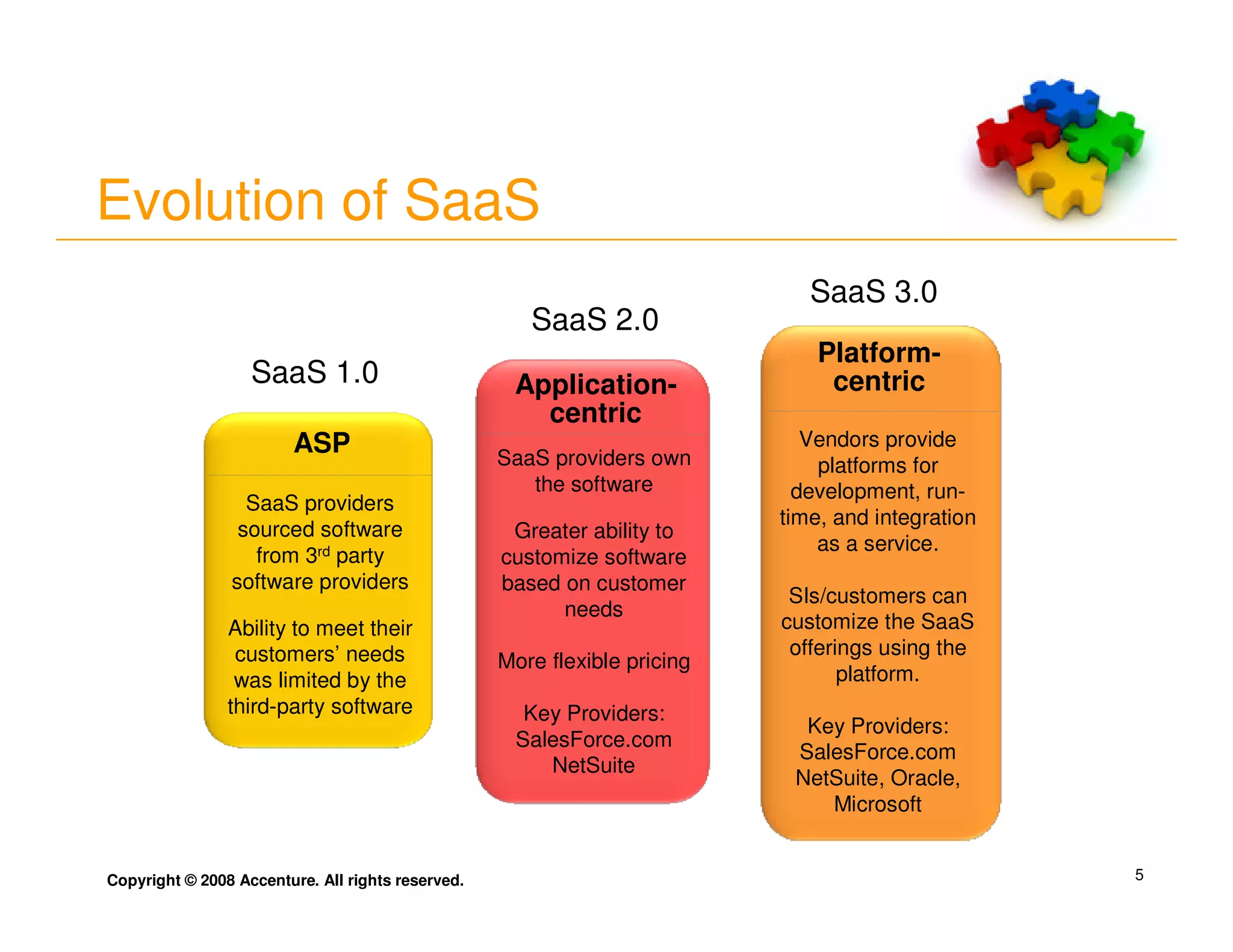
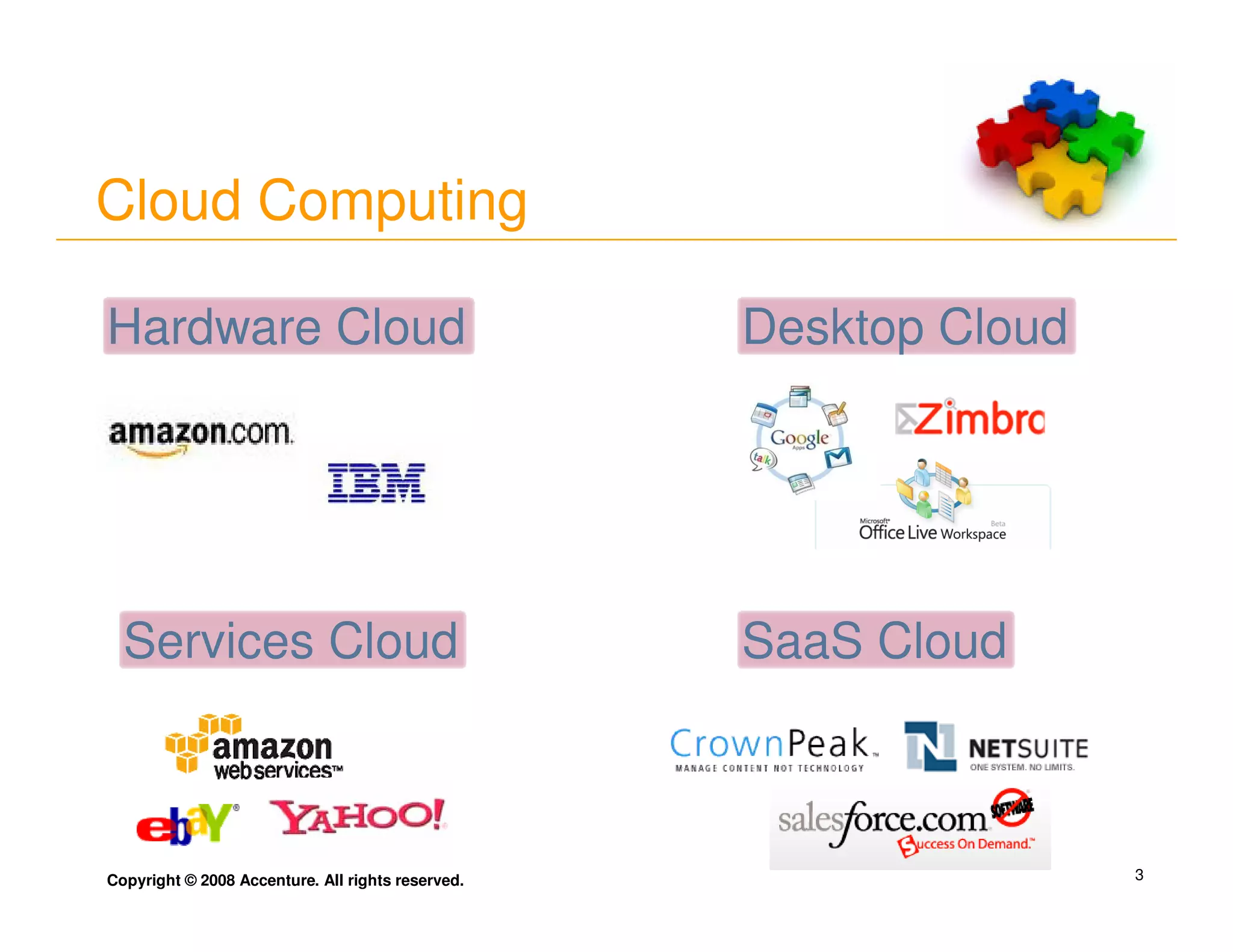
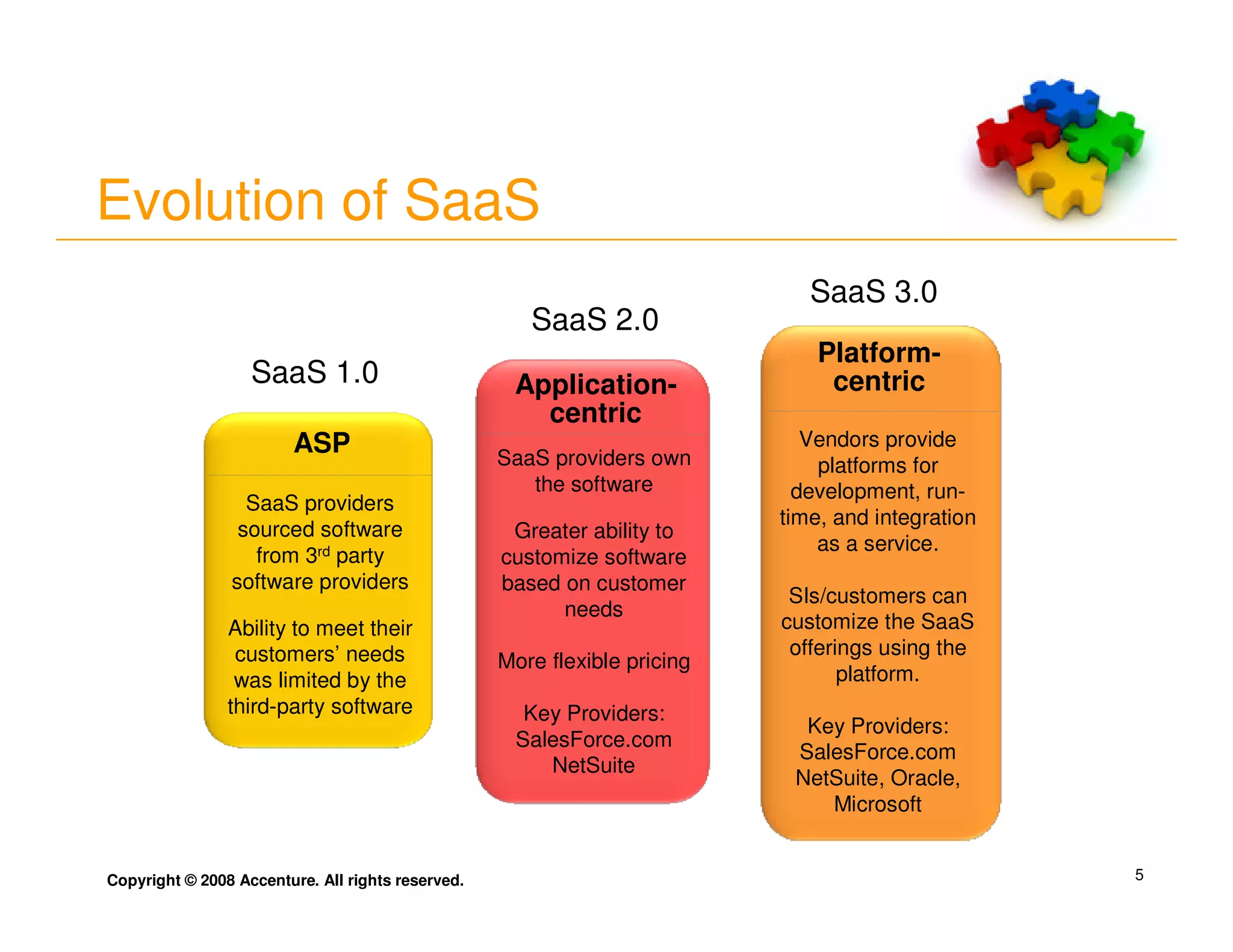
The document discusses cloud computing and its evolution. It identifies four types of cloud - hardware cloud, services cloud, desktop cloud and SaaS cloud. It describes the evolution of SaaS from SaaS 1.0 where providers sourced software from third parties to SaaS 3.0 which is platform-centric where vendors provide platforms for development, runtime and integration. It also discusses some implications of cloud computing around business case, data privacy/trust and integration. It includes a quote from Richard Stallman criticizing cloud computing as "hype" and a risk to losing control over data.