ACC Case Study
•
0 likes•134 views
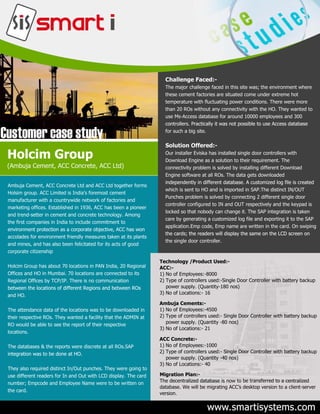
ACC – India’s no.1 cement company – Having more than 10,000 employees in 20 Regions with more than 75 locations are secured with more than 300 smart I Controllers...
Report
Share
Report
Share
Download to read offline
Recommended
2 b ppa con tic- 45566 luz elvira sarmiento

Este documento presenta un proyecto de aula para fortalecer las habilidades de suma en estudiantes de primer grado a través de actividades lúdicas y el uso de las TIC. El proyecto busca mejorar los procesos de adición para que los estudiantes puedan resolver problemas de su contexto de manera significativa. Se implementará una metodología que incluye guías didácticas, juegos matemáticos y el uso de herramientas digitales para hacer las matemáticas más entretenidas.
Mini Muthootu Case Study

Muthoottu Mini - Smart I Deployed Centralized Multi-location Time & Attendance solution for 650 branches of Mini Muthoottu and counting is on
Resume

Rajan Kumar is seeking a job where he can make active use of his knowledge and skills to achieve career targets through effective performance. He has an academic background that includes a high school certificate, senior secondary school certificate, and a bachelor's degree. His professional qualifications include a Diploma in Official Management. He has work experience as an IT Executive and MIS at a transportation company, and as an Accounts Executive at a teleshopping and marketing company. His skills include proficiency with various computer programs and accounting software.
Vijay resume

P. Vijayan is an Indian national seeking a job as an engineering assistant. He has over 12 years of experience in precision engineering and is currently studying Solidworks and Mastercam. Vijayan has held positions such as CNC machinist, EDM systems operations engineer, CNC setter/operator, and CNC operator. He has extensive experience programming and operating CNC machines, reading engineering drawings, and ensuring quality control. Vijayan is proficient in AutoCAD, Microsoft Office, Solidworks, and Mastercam. He holds a DME degree and has worked for companies in India and Malaysia.
Portafolio luz elvira sarmiento

El documento habla sobre trabajar con niños de 6 a 8 años en el Instituto Club Unión Sede E, que provienen de familias desplazadas con bajo nivel educativo. Los niños tienen dificultades con las sumas y problemas matemáticos, y falta de motivación para actividades educativas. El objetivo es diseñar estrategias lúdicas y usar recursos digitales para mejorar las habilidades matemáticas y la motivación de los estudiantes.
sap 6

Agriculture involves the active production of plants and animals in human-created ecosystems. It includes cultivating soil, growing and harvesting crops, and raising livestock. Agriculture developed independently in many places around the world starting around 14,500-12,000 years ago. Early domesticated crops include barley in the Middle East, millet in China, and squash in the Americas. Domesticated livestock developed during this same period, although dogs were domesticated earlier. Agriculture can be viewed as a farming system involving inputs like seeds, fertilizers, machinery and labor and outputs like crops, wool, dairy and poultry products.
Biometric Access and Attendance Terminal

BIOlite NG - Access and Attendance Terminal for Multilocation Attendance Management. Accurate monitoring of attendance, simultaneously at hundreds of outlet in the retail chain with the smart i multilocation attendance management software.
Recommended
2 b ppa con tic- 45566 luz elvira sarmiento

Este documento presenta un proyecto de aula para fortalecer las habilidades de suma en estudiantes de primer grado a través de actividades lúdicas y el uso de las TIC. El proyecto busca mejorar los procesos de adición para que los estudiantes puedan resolver problemas de su contexto de manera significativa. Se implementará una metodología que incluye guías didácticas, juegos matemáticos y el uso de herramientas digitales para hacer las matemáticas más entretenidas.
Mini Muthootu Case Study

Muthoottu Mini - Smart I Deployed Centralized Multi-location Time & Attendance solution for 650 branches of Mini Muthoottu and counting is on
Resume

Rajan Kumar is seeking a job where he can make active use of his knowledge and skills to achieve career targets through effective performance. He has an academic background that includes a high school certificate, senior secondary school certificate, and a bachelor's degree. His professional qualifications include a Diploma in Official Management. He has work experience as an IT Executive and MIS at a transportation company, and as an Accounts Executive at a teleshopping and marketing company. His skills include proficiency with various computer programs and accounting software.
Vijay resume

P. Vijayan is an Indian national seeking a job as an engineering assistant. He has over 12 years of experience in precision engineering and is currently studying Solidworks and Mastercam. Vijayan has held positions such as CNC machinist, EDM systems operations engineer, CNC setter/operator, and CNC operator. He has extensive experience programming and operating CNC machines, reading engineering drawings, and ensuring quality control. Vijayan is proficient in AutoCAD, Microsoft Office, Solidworks, and Mastercam. He holds a DME degree and has worked for companies in India and Malaysia.
Portafolio luz elvira sarmiento

El documento habla sobre trabajar con niños de 6 a 8 años en el Instituto Club Unión Sede E, que provienen de familias desplazadas con bajo nivel educativo. Los niños tienen dificultades con las sumas y problemas matemáticos, y falta de motivación para actividades educativas. El objetivo es diseñar estrategias lúdicas y usar recursos digitales para mejorar las habilidades matemáticas y la motivación de los estudiantes.
sap 6

Agriculture involves the active production of plants and animals in human-created ecosystems. It includes cultivating soil, growing and harvesting crops, and raising livestock. Agriculture developed independently in many places around the world starting around 14,500-12,000 years ago. Early domesticated crops include barley in the Middle East, millet in China, and squash in the Americas. Domesticated livestock developed during this same period, although dogs were domesticated earlier. Agriculture can be viewed as a farming system involving inputs like seeds, fertilizers, machinery and labor and outputs like crops, wool, dairy and poultry products.
Biometric Access and Attendance Terminal

BIOlite NG - Access and Attendance Terminal for Multilocation Attendance Management. Accurate monitoring of attendance, simultaneously at hundreds of outlet in the retail chain with the smart i multilocation attendance management software.
Slide show preview, rural values collaborative, for nmha

Private PowerPoint for discussion with New Mexico Hospital Association for a project to bring the Rural Values Collaborative to critical access hospitals in that state.
Training Mendapatkan Tubuh Ideal 30 hari di Rumah

Dokumen tersebut membahas tentang tipe tubuh manusia, cara membentuk badan ideal untuk setiap tipe tubuh, dan program latihan serta pola makan untuk meningkatkan berat badan dan massa otot.
Najam cv

Najmul Huda has over 15 years of experience in sales and marketing of commercial vehicles. He is currently a Senior Executive Sales at Juffali Industrial Products Company in Saudi Arabia. Previously he held sales roles at Al Habtoor Motors and Hinopak Motors in the UAE and Pakistan. He has a strong track record of achieving sales targets and developing new markets. Najmul Huda is seeking a challenging role to apply his experience and help companies grow their business.
Training Mendapatkan Tubuh Ideal 30 hari di Gym

GBPM Education Material
Join : http://grosirbajupriamurah.com/landing/ganteng
Marketing plan DryadShoppe

This document outlines the marketing plan for DryadShoppe, an e-commerce application for home decor products. It will source products locally from retailers in cities across India. The plan discusses DryadShoppe's offerings, objectives to increase customer satisfaction, promote local retailers digitally, and make quality products affordable. It analyzes the target demographics and competitors. The marketing strategy will involve segmentation, positioning, targeting, and an optimized marketing mix of product features, pricing, promotion, and place. Controls will ensure proper implementation of the plan.
CV AG - list of projects

The document outlines various solar projects undertaken related to solar irradiation analysis, solar PV feasibility studies and master plans, solar rooftop concepts, PV development feasibility studies, solar and hybrid option assessments, solar park advisory, PV plant development, PV project due diligence, and off-grid and mini-grid PV projects including hybrid systems. The projects span multiple countries and include analysis, feasibility studies, engineering support, and advisory services for installations ranging from hundreds of kW to multiple MW in size.
Dns rebinding

The document describes a DNS rebinding attack lab that aims to demonstrate how DNS rebinding works and help students gain experience using the technique. The lab simulates an IoT device (thermostat) behind a firewall that can be controlled via a web interface. To conduct the attack, the lab sets up a home network with the IoT device and an outside network with the attacker's servers. The attack circumvents the same-origin policy by getting the victim's browser to run the attacker's JavaScript, then using DNS rebinding to change the DNS mapping and redirect requests from the script to the IoT device, allowing temperature manipulation.
Basic Cisco ASA 5506-x Configuration (Firepower)

This document provides instructions for configuring basic network security on a Cisco ASA 5506-x firewall. It outlines requirements for separating networks into an Internet, user, and DMZ segment. It then provides steps to update the ASA software, configure interfaces and security levels, enable internet access via NAT and routing, allow web access to servers on the DMZ, optionally configure DHCP, and optionally redirect traffic to the FirePOWER module. It also includes steps for hardening the device by shutting down unused interfaces, enabling SSH access, and configuring time and logging.
Security plan

The document discusses security measures for a solicitor's company including physical security cameras and locks, cybersecurity such as firewalls, antivirus software, and regular updates, access controls like administrator rights and discretionary access control, and backups stored on the cloud. While current security is adequate, improvements could include an alarm system, more secure encryption for sensitive data, and prioritizing RAM to isolate privileged processes. The security plan implemented has improved safety significantly but physical security could be strengthened further.
“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...

“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2021/10/secure-hardware-architecture-for-embedded-vision-a-presentation-from-neurobinder/
Jonathan Cefalu, CEO and founder of NeuroBinder, presents the “Secure Hardware Architecture for Embedded Vision” tutorial at the May 2021 Embedded Vision Summit.
Security is a problem for every IoT system, but due to privacy concerns, security is particularly worrisome for embedded vision systems. In this talk, Cefalu covers how to design your embedded device so that the hardware architecture itself enforces strict guarantees about where visual data is able to flow.
In particular, Cefalu explores the idea of a “data diode” that uses hardware to enforce what parts of the system have access to video or images. This provides the highest level of protection against hacking or malware, as even if the device is completely hacked at the root level, the intruder will still be unable to access the visual data.Ip Phone Apps Training

- Avaya IP Phone Applications allow integrating business and internet applications directly onto phone displays for increased productivity and easy access to information.
- Custom applications can be built to connect phones to enterprise systems, displaying information like calendars, directories, stock prices and weather updates.
- Detailed instructions are provided for installing, configuring, maintaining and troubleshooting the Avaya IP Phone Applications software.
Microsoft 70-687 it exams dumps

http://www.it-exams.fr/70-687.htm Le certificat Microsoft 70-687 est l’un des certificats informatiques les plus recherchés dans le monde entier. L’acquisition du certificat Microsoft 70-687 peut vous servir de tremplin pour obtenir un poste informatique dans les moyennes ou les grandes entreprises. Selon une enquête, les entreprises informatiques universellement renommées préfèrent employer des candidats possédant un certificat professionnel. De plus, l’obtention du certificat Microsoft MCSA Windows 8 70-687 (TS:Configuring Windows 8) vous permettra de toucher un salaire beaucoup plus élevé. A l’aide de la dernière version de l’ouvrage de référence pour l’examen du certificat Microsoft MCSA Windows 8 70-687 (TS:Configuring Windows 8) fournie par www.it-exams.fr, vous pourrezy arriver sans difficulté !
Networking Concepts and Tools for the Cloud

This document discusses networking concepts and tools for cloud computing. It describes virtual local area networks, virtual private networks, and networking protocol layers. It explains how tools like OpenSSH, OpenVPN, and proxy servers can be used to set up different network topologies and solve connectivity problems for common cloud situations. Specific examples are provided for configuring firewalls and port forwarding on Linux systems. References are also included for further reading.
Security in the Real World - JavaOne 2013

Java was built from the ground up with security clearly in mind and is now the engine powering a huge number of business-critical systems. With this visibility and opportunity come attacks, and this session goes through the state of security in Java in 2013 and discusses some of the attack vectors. It presents a couple of real-world examples and also addresses the real-world challenges in getting security fixes out quickly. Finally, it touches on hardware cryptography. Come learn more about the reality of security today and take away a better awareness of exactly how Java helps protect you.
Andrew Hutton Hitachi presentation

This document outlines the layout of a 5 cabinet server room. Cabinet 1 contains core switching and SAN equipment. Cabinet 2 is for local patching and switching. Cabinet 3 contains phone and VOIP equipment. Cabinet 4 contains servers and a KVM over IP unit connected to the servers and SANs. Cabinet 5 contains additional local patching and switching equipment. Redundant UPS units provide power to the server room and environmental monitoring is in place.
IBM World of Watson 2016 - DB2 Analytics Accelerator on Cloud

IBM is introducing a new deployment option for the DB2 Analytics Accelerator on Cloud using dashDB as the acceleration engine. This provides customers with a hybrid cloud offering that gives the flexibility of running the Accelerator either on-premises or in the cloud. The Cloud deployment offers benefits like monthly pricing, hardware provisioning by IBM, and fast provisioning time. Initial focus areas include basic Accelerator functionality for offloading queries to the cloud, with a roadmap to continuously expand features and functionality.
Installation of pfSense on Soekris 6501

The document provides instructions for configuring a pfSense firewall to use a Clear Wireless 4G connection for primary internet access and failover to an existing office internet connection. It describes setting up the Clear Wireless WAN interface and a multi-WAN gateway group in pfSense. Traffic is configured to use the Clear Wireless gateway by default with failover to the office connection if the primary goes down. Initial tests of the Clear Wireless connection achieved speeds suitable for typical office use and zero packet loss. Configuring the Westell 6100 modem to bridge mode is also described to allow use of an external router.
Installation of pfSense on Soekris 6501

This document provides instructions for configuring a pfSense firewall to use multiple WAN connections for failover. It describes setting up a Clear Wireless 4G connection as the primary WAN and using the existing office connection as a backup. Specific steps include adding the WAN interfaces, creating a gateway group for failover, and configuring firewall rules to use the gateway group. Initial testing showed the Clear Wireless connection providing adequate speeds for typical office use while offloading over 6GB of data from the office connection in just 3 days.
Cloud Based Data Warehousing and Analytics

This document discusses Marriott International's journey to implementing a cloud-based data warehouse and analytics platform using IBM BigSQL on Softlayer cloud infrastructure. It describes the limitations of their existing on-premises system, challenges faced in migrating data and queries to the cloud, lessons learned, and next steps to further improve the platform. The system is now in production use by an initial group of users at Marriott.
Using a Zeno 3200

A user guide for setting up a stock Zeno 3200 data logger to work with wind speed, wind direction, and input voltages from an air monitor. Includes how to log in to Zeno 3200 with Hyperterminal and building the serial cable.
200-301-demo.pdf

And first-class of all, a threat to hone your competencies. It’s adequate if you experience in over your head. We all did sooner or later, this subsequent step is about pushing thru that worry and on the point of address something as hard because the 200-301. In case you get caught, reach out. In case you see others caught, assist them.
Cisco 200-301 Exam Dumps

How is this newsletter going to help you? Apart from providing you with a brief glimpse of the test’s topics and shape, we are able to additionally assist you discover efficient education substances. Cisco’s internet site is a extraordinary starting point, but you shouldn’t restriction your self to it. Despite the fact that you would possibly have by no means heard approximately them, you have to attempt exam dumps as they may grow to be your secret tool to get a passing rating in 2 hundred-301 assessment. But now, let’s start with the exam details.
More Related Content
Viewers also liked
Slide show preview, rural values collaborative, for nmha

Private PowerPoint for discussion with New Mexico Hospital Association for a project to bring the Rural Values Collaborative to critical access hospitals in that state.
Training Mendapatkan Tubuh Ideal 30 hari di Rumah

Dokumen tersebut membahas tentang tipe tubuh manusia, cara membentuk badan ideal untuk setiap tipe tubuh, dan program latihan serta pola makan untuk meningkatkan berat badan dan massa otot.
Najam cv

Najmul Huda has over 15 years of experience in sales and marketing of commercial vehicles. He is currently a Senior Executive Sales at Juffali Industrial Products Company in Saudi Arabia. Previously he held sales roles at Al Habtoor Motors and Hinopak Motors in the UAE and Pakistan. He has a strong track record of achieving sales targets and developing new markets. Najmul Huda is seeking a challenging role to apply his experience and help companies grow their business.
Training Mendapatkan Tubuh Ideal 30 hari di Gym

GBPM Education Material
Join : http://grosirbajupriamurah.com/landing/ganteng
Marketing plan DryadShoppe

This document outlines the marketing plan for DryadShoppe, an e-commerce application for home decor products. It will source products locally from retailers in cities across India. The plan discusses DryadShoppe's offerings, objectives to increase customer satisfaction, promote local retailers digitally, and make quality products affordable. It analyzes the target demographics and competitors. The marketing strategy will involve segmentation, positioning, targeting, and an optimized marketing mix of product features, pricing, promotion, and place. Controls will ensure proper implementation of the plan.
CV AG - list of projects

The document outlines various solar projects undertaken related to solar irradiation analysis, solar PV feasibility studies and master plans, solar rooftop concepts, PV development feasibility studies, solar and hybrid option assessments, solar park advisory, PV plant development, PV project due diligence, and off-grid and mini-grid PV projects including hybrid systems. The projects span multiple countries and include analysis, feasibility studies, engineering support, and advisory services for installations ranging from hundreds of kW to multiple MW in size.
Viewers also liked (6)
Slide show preview, rural values collaborative, for nmha

Slide show preview, rural values collaborative, for nmha
Similar to ACC Case Study
Dns rebinding

The document describes a DNS rebinding attack lab that aims to demonstrate how DNS rebinding works and help students gain experience using the technique. The lab simulates an IoT device (thermostat) behind a firewall that can be controlled via a web interface. To conduct the attack, the lab sets up a home network with the IoT device and an outside network with the attacker's servers. The attack circumvents the same-origin policy by getting the victim's browser to run the attacker's JavaScript, then using DNS rebinding to change the DNS mapping and redirect requests from the script to the IoT device, allowing temperature manipulation.
Basic Cisco ASA 5506-x Configuration (Firepower)

This document provides instructions for configuring basic network security on a Cisco ASA 5506-x firewall. It outlines requirements for separating networks into an Internet, user, and DMZ segment. It then provides steps to update the ASA software, configure interfaces and security levels, enable internet access via NAT and routing, allow web access to servers on the DMZ, optionally configure DHCP, and optionally redirect traffic to the FirePOWER module. It also includes steps for hardening the device by shutting down unused interfaces, enabling SSH access, and configuring time and logging.
Security plan

The document discusses security measures for a solicitor's company including physical security cameras and locks, cybersecurity such as firewalls, antivirus software, and regular updates, access controls like administrator rights and discretionary access control, and backups stored on the cloud. While current security is adequate, improvements could include an alarm system, more secure encryption for sensitive data, and prioritizing RAM to isolate privileged processes. The security plan implemented has improved safety significantly but physical security could be strengthened further.
“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...

“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2021/10/secure-hardware-architecture-for-embedded-vision-a-presentation-from-neurobinder/
Jonathan Cefalu, CEO and founder of NeuroBinder, presents the “Secure Hardware Architecture for Embedded Vision” tutorial at the May 2021 Embedded Vision Summit.
Security is a problem for every IoT system, but due to privacy concerns, security is particularly worrisome for embedded vision systems. In this talk, Cefalu covers how to design your embedded device so that the hardware architecture itself enforces strict guarantees about where visual data is able to flow.
In particular, Cefalu explores the idea of a “data diode” that uses hardware to enforce what parts of the system have access to video or images. This provides the highest level of protection against hacking or malware, as even if the device is completely hacked at the root level, the intruder will still be unable to access the visual data.Ip Phone Apps Training

- Avaya IP Phone Applications allow integrating business and internet applications directly onto phone displays for increased productivity and easy access to information.
- Custom applications can be built to connect phones to enterprise systems, displaying information like calendars, directories, stock prices and weather updates.
- Detailed instructions are provided for installing, configuring, maintaining and troubleshooting the Avaya IP Phone Applications software.
Microsoft 70-687 it exams dumps

http://www.it-exams.fr/70-687.htm Le certificat Microsoft 70-687 est l’un des certificats informatiques les plus recherchés dans le monde entier. L’acquisition du certificat Microsoft 70-687 peut vous servir de tremplin pour obtenir un poste informatique dans les moyennes ou les grandes entreprises. Selon une enquête, les entreprises informatiques universellement renommées préfèrent employer des candidats possédant un certificat professionnel. De plus, l’obtention du certificat Microsoft MCSA Windows 8 70-687 (TS:Configuring Windows 8) vous permettra de toucher un salaire beaucoup plus élevé. A l’aide de la dernière version de l’ouvrage de référence pour l’examen du certificat Microsoft MCSA Windows 8 70-687 (TS:Configuring Windows 8) fournie par www.it-exams.fr, vous pourrezy arriver sans difficulté !
Networking Concepts and Tools for the Cloud

This document discusses networking concepts and tools for cloud computing. It describes virtual local area networks, virtual private networks, and networking protocol layers. It explains how tools like OpenSSH, OpenVPN, and proxy servers can be used to set up different network topologies and solve connectivity problems for common cloud situations. Specific examples are provided for configuring firewalls and port forwarding on Linux systems. References are also included for further reading.
Security in the Real World - JavaOne 2013

Java was built from the ground up with security clearly in mind and is now the engine powering a huge number of business-critical systems. With this visibility and opportunity come attacks, and this session goes through the state of security in Java in 2013 and discusses some of the attack vectors. It presents a couple of real-world examples and also addresses the real-world challenges in getting security fixes out quickly. Finally, it touches on hardware cryptography. Come learn more about the reality of security today and take away a better awareness of exactly how Java helps protect you.
Andrew Hutton Hitachi presentation

This document outlines the layout of a 5 cabinet server room. Cabinet 1 contains core switching and SAN equipment. Cabinet 2 is for local patching and switching. Cabinet 3 contains phone and VOIP equipment. Cabinet 4 contains servers and a KVM over IP unit connected to the servers and SANs. Cabinet 5 contains additional local patching and switching equipment. Redundant UPS units provide power to the server room and environmental monitoring is in place.
IBM World of Watson 2016 - DB2 Analytics Accelerator on Cloud

IBM is introducing a new deployment option for the DB2 Analytics Accelerator on Cloud using dashDB as the acceleration engine. This provides customers with a hybrid cloud offering that gives the flexibility of running the Accelerator either on-premises or in the cloud. The Cloud deployment offers benefits like monthly pricing, hardware provisioning by IBM, and fast provisioning time. Initial focus areas include basic Accelerator functionality for offloading queries to the cloud, with a roadmap to continuously expand features and functionality.
Installation of pfSense on Soekris 6501

The document provides instructions for configuring a pfSense firewall to use a Clear Wireless 4G connection for primary internet access and failover to an existing office internet connection. It describes setting up the Clear Wireless WAN interface and a multi-WAN gateway group in pfSense. Traffic is configured to use the Clear Wireless gateway by default with failover to the office connection if the primary goes down. Initial tests of the Clear Wireless connection achieved speeds suitable for typical office use and zero packet loss. Configuring the Westell 6100 modem to bridge mode is also described to allow use of an external router.
Installation of pfSense on Soekris 6501

This document provides instructions for configuring a pfSense firewall to use multiple WAN connections for failover. It describes setting up a Clear Wireless 4G connection as the primary WAN and using the existing office connection as a backup. Specific steps include adding the WAN interfaces, creating a gateway group for failover, and configuring firewall rules to use the gateway group. Initial testing showed the Clear Wireless connection providing adequate speeds for typical office use while offloading over 6GB of data from the office connection in just 3 days.
Cloud Based Data Warehousing and Analytics

This document discusses Marriott International's journey to implementing a cloud-based data warehouse and analytics platform using IBM BigSQL on Softlayer cloud infrastructure. It describes the limitations of their existing on-premises system, challenges faced in migrating data and queries to the cloud, lessons learned, and next steps to further improve the platform. The system is now in production use by an initial group of users at Marriott.
Using a Zeno 3200

A user guide for setting up a stock Zeno 3200 data logger to work with wind speed, wind direction, and input voltages from an air monitor. Includes how to log in to Zeno 3200 with Hyperterminal and building the serial cable.
200-301-demo.pdf

And first-class of all, a threat to hone your competencies. It’s adequate if you experience in over your head. We all did sooner or later, this subsequent step is about pushing thru that worry and on the point of address something as hard because the 200-301. In case you get caught, reach out. In case you see others caught, assist them.
Cisco 200-301 Exam Dumps

How is this newsletter going to help you? Apart from providing you with a brief glimpse of the test’s topics and shape, we are able to additionally assist you discover efficient education substances. Cisco’s internet site is a extraordinary starting point, but you shouldn’t restriction your self to it. Despite the fact that you would possibly have by no means heard approximately them, you have to attempt exam dumps as they may grow to be your secret tool to get a passing rating in 2 hundred-301 assessment. But now, let’s start with the exam details.
Cisco 200-301 Exam Dumps

Do not permit yourself face your ccna two hundred-301 exam without proper guidance to remorse later when you fail in cisco licensed community associate real exam because many people had been there. Let assist you to your cisco two hundred-301 ccna real examination preparation. To help you put together on your cisco certified network partner (ccna) 200-301 exam.
I Didn't Know You Could Do That with zOS.pdf

1. The document discusses several new and updated features in recent z/OS releases: controlling GDGE maximum limits, using z/OS UNIX commands on MVS data sets, sending redacted dumps from z/OSMF Incident Log using Data Privacy for Diagnostics, installing individual products using z/OSMF portable software instances, viewing SNA application activity via the Function Registry, managing resource shortages with JES2's Emergency Subsystem, and a planned z/OS UUID capability.
2. The topics provide insights into system usage and improvements for problem diagnosis, software management, and urgent system tasks.
3. Users can benefit from these features to better understand their systems, install software easily, and respond to
Superior Cloud Economics with IBM Power Systems

IBM Power Systems is working to decrease costs, improve performance and use the open community to help competitive enterprises put data to work in the cloud.
resume

The document is a resume for Amid Kante that summarizes his qualifications and experience. It lists his technical skills including computer hardware and software, networking concepts, and various applications. It then outlines his work history in customer service roles for Whole Foods and AT&T, as well as his experience as an independent contractor performing various IT tasks. The resume concludes with his education history of an Associate's degree in Computer Science from City College of San Francisco and ongoing training in networking and cabling.
Similar to ACC Case Study (20)
“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...

“Secure Hardware Architecture for Embedded Vision,” a Presentation from Neuro...
IBM World of Watson 2016 - DB2 Analytics Accelerator on Cloud

IBM World of Watson 2016 - DB2 Analytics Accelerator on Cloud
More from smart-i Electronics Systems Pvt Ltd.
Nrl case study

NRL - A Public Sector undertaking Refinery in Golaghat, Assam is secured with Smart I's Integrated Access Control System (IACS)....
More case study

More – Aditya Birla Retail Ltd. - A leading retail store of Indian market is now highly secured and attendances of employees are fully automated with Smart I’s Multi door controllers...
God blessing case study

God Blessings - A Complete Automated Elevator System for Tallest Residential Tower in Pune..
Yamuna Expressway Case Study

Yamuna Expressway - All three toll plaza building of Yamuna Expressway is now highly secured by Smart I IP based 4 Door/4 Reader controllers with HID Reader....
smartXS NG:- 4 Door 8 Reader Access Control Panel

The faster and more efficient 4 Door 8 Reader Controller with a 32 bit processor and DIN Rail Mounting
smartXS NG plus

The document discusses ordering information for access control features. It provides details on how to purchase access control systems, including card readers, biometric scanners, and software. Customers can contact the sales team to get a quote and place an order for the products they need for their security needs.
smartCOMMANDCONTROL

This document outlines various licensing packages for an SCMD software product, including packages for 250, 500, 1000, and 5000 users, an unlimited user package, an extra company package for 1 additional company, and a mobile application package.
smartATTENDANCE

Desktop based time attendance software that is designed for small and medium organizations. It has a user friendly interface and provides comprehensive reports. The software offers various functions including device configuration, leave management, shift management, overtime calculation, and outdoor entry. It allows administrators to define attendance policies and rules. HR can manage different leave types and accruals. Shift patterns can be customized and workforce easily scheduled. The software also provides useful reports on attendance, overtime, and more.
smartACCESS

Desktop Based Access Management Software smartACCESS is a user friendly software designed for access control management in small, medium, and large organizations where security is highly important. It allows for device configuration, user enrollment, data downloading, and employee card activation/deactivation. The software provides comprehensive access management through access rules at various levels and useful reports for organizations. It also enables email and SMS notifications for certain events.
Solution for Retail Industry l Multilocation Attendance Monitoring - smart-i

Solution for Retail Industry l Multilocation Attendance Monitoring - smart-ismart-i Electronics Systems Pvt Ltd.
Attendance Solution with Multilocation Attendance monitoring SoftwareBIOlite NG plus

A state-of-the-art biometric Access & Attendance System, BIOlite NG plus looks deeper at the finger for its prints. Equipped with a globally acclaimed Multi Spectral sensor, it looks at both, the outer as well as the inner layers of the finger and therefore works effectively with almost every type of finger condition.
It is thus the most efficient, effective and reliable Biometric Attendance system for a wide range of industries such as those where the quality of the fingerprints is an issue such as oily, dry,wet, dirty, elderly, etc...
smartXS: 2 Door 2 Reader & 4 Door 4 Reader Access Control Panel

smartXS is compact and robust 'Access and Time Attendance' system. In current scenario where security requirements are becoming stringent, we provide different access control and Identification systems to meet modern security needs. The systems are reliable, robust, easy to install with minimum support.
More from smart-i Electronics Systems Pvt Ltd. (16)
Solution for Retail Industry l Multilocation Attendance Monitoring - smart-i

Solution for Retail Industry l Multilocation Attendance Monitoring - smart-i
smartXS: 2 Door 2 Reader & 4 Door 4 Reader Access Control Panel

smartXS: 2 Door 2 Reader & 4 Door 4 Reader Access Control Panel
Recently uploaded
Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...

On episode 272 of the Digital and Social Media Sports Podcast, Neil chatted with Brian Fitzsimmons, Director of Licensing and Business Development for Barstool Sports.
What follows is a collection of snippets from the podcast. To hear the full interview and more, check out the podcast on all podcast platforms and at www.dsmsports.net
Structural Design Process: Step-by-Step Guide for Buildings

The structural design process is explained: Follow our step-by-step guide to understand building design intricacies and ensure structural integrity. Learn how to build wonderful buildings with the help of our detailed information. Learn how to create structures with durability and reliability and also gain insights on ways of managing structures.
How to Implement a Real Estate CRM Software

To implement a CRM for real estate, set clear goals, choose a CRM with key real estate features, and customize it to your needs. Migrate your data, train your team, and use automation to save time. Monitor performance, ensure data security, and use the CRM to enhance marketing. Regularly check its effectiveness to improve your business.
2022 Vintage Roman Numerals Men Rings

Discover timeless style with the 2022 Vintage Roman Numerals Men's Ring. Crafted from premium stainless steel, this 6mm wide ring embodies elegance and durability. Perfect as a gift, it seamlessly blends classic Roman numeral detailing with modern sophistication, making it an ideal accessory for any occasion.
https://rb.gy/usj1a2
Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

CALL 8867766396 SATTA MATKA | DPBOSS | KALYAN MAIN BAZAR | FAST MATKA | DPBOSS GUESSING | TARA MATKA | KALYAN CHART | MATKA BOSS
Industrial Tech SW: Category Renewal and Creation

Every industrial revolution has created a new set of categories and a new set of players.
Multiple new technologies have emerged, but Samsara and C3.ai are only two companies which have gone public so far.
Manufacturing startups constitute the largest pipeline share of unicorns and IPO candidates in the SF Bay Area, and software startups dominate in Germany.
Understanding User Needs and Satisfying Them

https://www.productmanagementtoday.com/frs/26903918/understanding-user-needs-and-satisfying-them
We know we want to create products which our customers find to be valuable. Whether we label it as customer-centric or product-led depends on how long we've been doing product management. There are three challenges we face when doing this. The obvious challenge is figuring out what our users need; the non-obvious challenges are in creating a shared understanding of those needs and in sensing if what we're doing is meeting those needs.
In this webinar, we won't focus on the research methods for discovering user-needs. We will focus on synthesis of the needs we discover, communication and alignment tools, and how we operationalize addressing those needs.
Industry expert Scott Sehlhorst will:
• Introduce a taxonomy for user goals with real world examples
• Present the Onion Diagram, a tool for contextualizing task-level goals
• Illustrate how customer journey maps capture activity-level and task-level goals
• Demonstrate the best approach to selection and prioritization of user-goals to address
• Highlight the crucial benchmarks, observable changes, in ensuring fulfillment of customer needs
一比一原版新西兰奥塔哥大学毕业证(otago毕业证)如何办理

一模一样【微信:A575476】【新西兰奥塔哥大学毕业证(otago毕业证)成绩单Offer】【微信:A575476】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信:A575476】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信:A575476】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Explore the fascinating world of the Gemini Zodiac Sign. Discover the unique personality traits, key dates, and horoscope insights of Gemini individuals. Learn how their sociable, communicative nature and boundless curiosity make them the dynamic explorers of the zodiac. Dive into the duality of the Gemini sign and understand their intellectual and adventurous spirit.
2024-6-01-IMPACTSilver-Corp-Presentation.pdf

IMPACT Silver is a pure silver zinc producer with over $260 million in revenue since 2008 and a large 100% owned 210km Mexico land package - 2024 catalysts includes new 14% grade zinc Plomosas mine and 20,000m of fully funded exploration drilling.
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Schedule Unveiled
Income Tax exemption for Start up : Section 80 IAC

A presentation on the concept of Exemption of Profits of Start ups from Income Tax
How are Lilac French Bulldogs Beauty Charming the World and Capturing Hearts....

“After being the most listed dog breed in the United States for 31
years in a row, the Labrador Retriever has dropped to second place
in the American Kennel Club's annual survey of the country's most
popular canines. The French Bulldog is the new top dog in the
United States as of 2022. The stylish puppy has ascended the
rankings in rapid time despite having health concerns and limited
color choices.”
3 Simple Steps To Buy Verified Payoneer Account In 2024

Buy Verified Payoneer Account: Quick and Secure Way to Receive Payments
Buy Verified Payoneer Account With 100% secure documents, [ USA, UK, CA ]. Are you looking for a reliable and safe way to receive payments online? Then you need buy verified Payoneer account ! Payoneer is a global payment platform that allows businesses and individuals to send and receive money in over 200 countries.
If You Want To More Information just Contact Now:
Skype: SEOSMMEARTH
Telegram: @seosmmearth
Gmail: seosmmearth@gmail.com
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The Radar reflects input from APCO’s teams located around the world. It distils a host of interconnected events and trends into insights to inform operational and strategic decisions. Issues covered in this edition include:
-- June 2024 is National Volunteer Month --

Check out our June display of books on voluntary organisations
Authentically Social by Corey Perlman - EO Puerto Rico

Authentically Social by Corey Perlman - EO Puerto RicoCorey Perlman, Social Media Speaker and Consultant
Social media for business Recently uploaded (20)
Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...

Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...
Structural Design Process: Step-by-Step Guide for Buildings

Structural Design Process: Step-by-Step Guide for Buildings
Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...
Income Tax exemption for Start up : Section 80 IAC

Income Tax exemption for Start up : Section 80 IAC
How are Lilac French Bulldogs Beauty Charming the World and Capturing Hearts....

How are Lilac French Bulldogs Beauty Charming the World and Capturing Hearts....
3 Simple Steps To Buy Verified Payoneer Account In 2024

3 Simple Steps To Buy Verified Payoneer Account In 2024
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...
Authentically Social by Corey Perlman - EO Puerto Rico

Authentically Social by Corey Perlman - EO Puerto Rico
ACC Case Study
- 1. ChallengeFaced:- Themajorchallengefacedinthissitewas;theenvironmentwhere thesecementfactoriesaresituatedcomeunderextremehot temperaturewithfluctuatingpowerconditions.Thereweremore than20ROswithoutanyconnectivitywiththeHO.Theywantedto useMs-Accessdatabaseforaround10000employeesand300 controllers.PracticallyitwasnotpossibletouseAccessdatabasecontrollers.PracticallyitwasnotpossibletouseAccessdatabase forsuchabigsite. SolutionOffered:- OurinstallerEviskahasinstalledsingledoorcontrollerswith DownloadEngineasasolutiontotheirrequirement.The connectivityproblem issolvedbyinstallingdifferentDownload EnginesoftwareatallROs.Thedatagetsdownloaded independentlyindifferentdatabase.Acustomizedlogfileiscreatedindependentlyindifferentdatabase.Acustomizedlogfileiscreated whichissenttoHOandisimportedinSAP.ThedistinctIN/OUT Punchesproblem issolvedbyconnecting2differentsingledoor controllerconfiguredtoINandOUTrespectivelyandthekeypadis lockedsothatnobodycanchangeit.TheSAPintegrationistaken carebygeneratingacustomizedlogfileandexportingittotheSAP application.Empcode,Empnamearewritteninthecard.Onswiping thecards;thereaderswilldisplaythesameontheLCDscreenonthecards;thereaderswilldisplaythesameontheLCDscreenon thesingledoorcontroller. Technology/ProductUsed:- ACC:- 1)NoofEmployees:-8000 2)Typeofcontrollersused:-SingleDoorControllerwithbatterybackup powersupply.(Quantity-180nos) 3)NoofLocations:-16 AmbujaCements:- 1)NoofEmployees:-4500 2)Typeofcontrollersused:-SingleDoorControllerwithbatterybackup powersupply.(Quantity-80nos) 3)NoofLocations:-21 ACCConcrete:- 1)NoofEmployees:-1000 2)Typeofcontrollersused:-SingleDoorControllerwithbatterybackup powersupply.(Quantity-40nos) 3)NoofLocations:-40 MigrationPlan:- Thedecentralizeddatabaseisnowtobetransferredtoacentralized database.WewillbemigratingACC’sdesktopversiontoaclient-server version. Customercasestudy AmbujaCement,ACCConcreteLtdandACCLtdtogetherforms Holsim group.ACCLimitedisIndia’sforemostcement manufacturerwithacountrywidenetworkoffactoriesand marketingoffices.Establishedin1936,ACChasbeenapioneer andtrend-setterincementandconcretetechnology.Among thefirstcompaniesinIndiatoincludecommitmentto environmentprotectionasacorporateobjective,ACChaswonenvironmentprotectionasacorporateobjective,ACChaswon accoladesforenvironmentfriendlymeasurestakenatitsplants andmines,andhasalsobeenfelicitatedforitsactsofgood corporatecitizenship Holcim Grouphasabout70locationsinPANIndia,20Regional OfficesandHOinMumbai.70locationsareconnectedtoits RegionalOfficesbyTCP/IP.Thereisnocommunication betweenthelocationsofdifferentRegionsandbetweenROsbetweenthelocationsofdifferentRegionsandbetweenROs andHO. Theattendancedataofthelocationswastobedownloadedin theirrespectiveROs.TheywantedafacilitythattheADMINat ROwouldbeabletoseethereportoftheirrespective locations. Thedatabases&thereportswerediscreteatallROs.SAP integrationwastobedoneatHO.integrationwastobedoneatHO. TheyalsorequireddistinctIn/Outpunches.Theyweregoingto usedifferentreadersforInandOutwithLCDdisplay.Thecard number;EmpcodeandEmployeeNameweretobewrittenon thecard. Holcim Group (AmbujaCement,ACCConcrete,ACCLtd)
- 2. Flow Diagram of Holcim Group Architectureof Holcim setup
