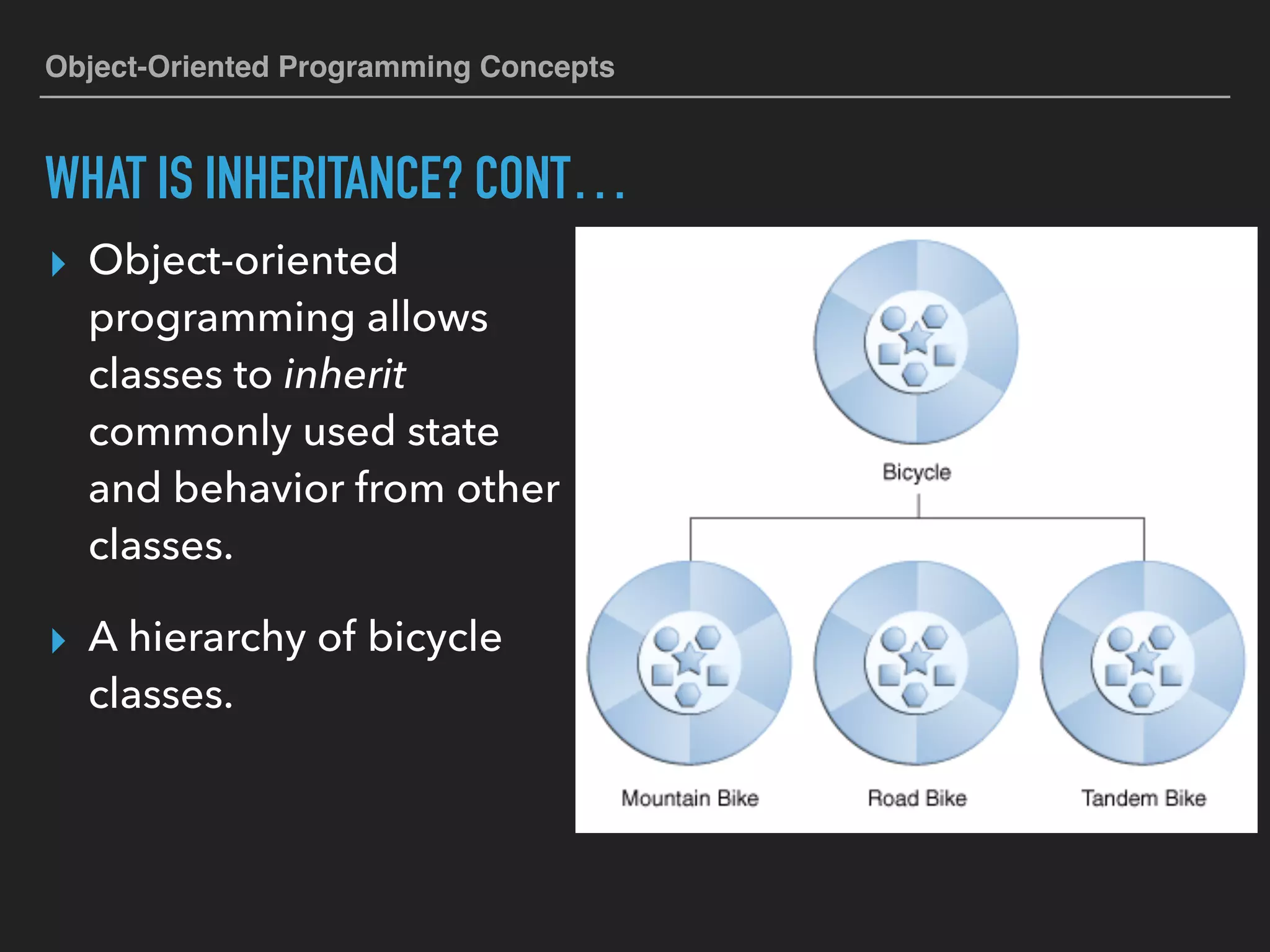
Inheritance in object-oriented programming allows classes to inherit common characteristics and behaviors from other classes, creating a hierarchy. For example, 'bicycle' serves as a superclass for 'mountainbike,' 'roadbike,' and 'tandembike,' allowing subclasses to focus on unique features. The syntax to create a subclass involves using the 'extends' keyword, ensuring that inherited properties and methods can be accessed while maintaining readability.