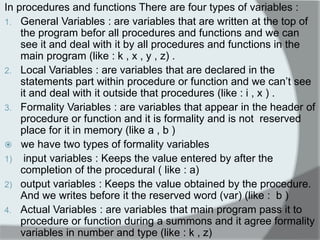
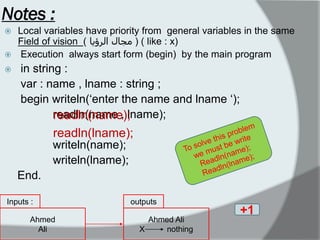
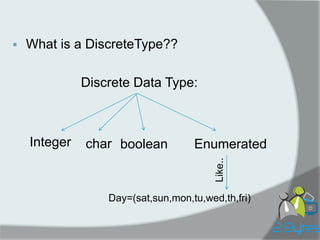
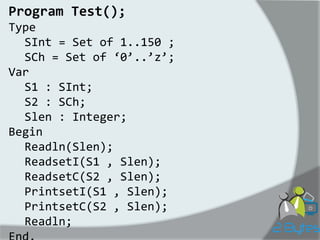
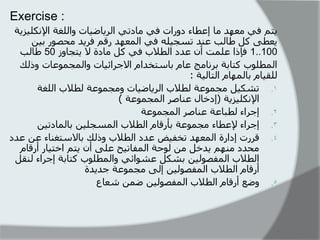
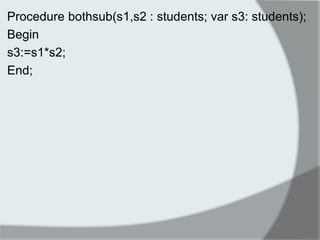
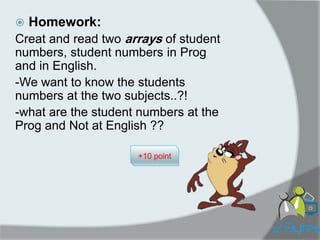
This document contains program code and notes about programming concepts like procedures, functions, variables, sets, and arrays. It discusses different types of variables, set operations, reading and printing sets, and provides examples of code for procedures to input and output sets. It also provides exercises asking the reader to write a program to manage student enrollment in math and English classes using sets and arrays.
![S1 := [ 55, 80, 99, 80, 600, 41, 44..55];
Isn‟t added
S1:
41 44..55 80 99](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-11-320.jpg)
![S1 :
S1 := [];](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-12-320.jpg)
![S2 := [200,20];
S2:
40..100
“NO Change”](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-13-320.jpg)
![S4 := [‘B’,’A’,’c’,’a’];
S4:
„a‟ „c‟](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-14-320.jpg)
![S4 := [I,k];
Var I,k:integer;
i:=1; k:=k+1;
+1
S4:
Compile Error !!](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-15-320.jpg)
![S1 := [I,j];
Var I,j:integer;
i:=1; j:=i*9;
+1
S1:
1,9](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-16-320.jpg)
![i, j : integer; i := 1; j := i-1; S1 := [i, j]; S1 := S1 + [i*2];
S1:
0,1,2
+1](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-17-320.jpg)
![Operation
•To put a value in it , we use [value] .
•The operations on Sets :
⋂ ⇔ *
⋃ ⇔ +
/ ⇔ -
⊆ ⇔ <=
⊇ ⇔ >=
∈ ⇔ in](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-19-320.jpg)
![Program SetsOperator; Var A0 : set of 1..15; A1 : set of 1..10; A2 : set of 5..15; i : integer; Begin A1 := [1..10]; A2 := [5..15]; A0 := A1*A2; {A0=[5..10]} A0 := A1+A2; {A0=[1..15]} A0 := A1-A2; {A0=[1..4]} A0 := A0-[1]; {A0=[2..4]}](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-20-320.jpg)
![A1 := [2,3];
A2 := [1,2,3,4,5];
if (A1 <= A2) then {or (A2 >= A1)}
writeln ('A1 is a subset of A2');
readln (i);
if (i in A1) then
writeln (i,' is in A1')
else
writeln (i,' is not in A1');
End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-21-320.jpg)
![True statement
A0, A1 : Set of 1..15; A : boolean; A0 := [1, 2]; A1 := [2, 4]; A0 := A0 – [77]; A := A1 >= A0; A := 1 in A0;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-22-320.jpg)
![Const Sets
Type
Digits = set of 0..9;
Const
HexD : set of '0'..'z‘ =
['0'..'9', 'A'..'F', 'a'..'f'];
ED : Digits = [0, 2, 4, 6, 8];
Var
d : Digits;
Begin
d := [8];
d := ED; {d=[0,2,4,6,8]}
ED:=ED+[9];
ED:=d;
End.
+1
Error .. Fateh 3eoonk !!](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-23-320.jpg)
![Enum Set
Type
Day = (sun,mon,….,sat);
Name=(koko,soso,fofo,fifi);
Var
days: Set of Day;
N:set of Name
Begin
Days:=[sun..sat];
N:=[KOKO,SOSO];
End.](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-24-320.jpg)

![Read Integer Sets
Procedure ReadsetI (var S:SInt; L:integer) ;
var
i, x : integer;
Begin
s:=[];
For i:=1 to L do
begin
Read(x);
S := S + [x];
end;
End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-27-320.jpg)
![Read Char Sets
Procedure ReadsetC (var S:SCh; L:integer) ; var i, x : Char; Begin s:=[]; For i:=1 to L do begin Read(x); S := S + [x]; end; End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-28-320.jpg)
![Print Integer Sets Using While Loop:
Procedure PrintsetI (S : SInt) ;
var
I : Integer;
Begin
I := 0;
While ( S <> []) do
If (I in S) then
begin
Writeln(I);
S := S – [I];
end;
I := I + 1;
End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-29-320.jpg)
![Print Integer Sets Using For Loop
Procedure PrintsetI (S : SI) ; var I : Integer; Begin For I:=1 to 32700 do Begin If (I in S) then Begin Writeln(I); S := S – [I]; End; If (S = []) then I := 32700; End; End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-30-320.jpg)
![Program prog2byte_team;
Uses wincrt;
Type students=set of 1..100;
numbers=array[1..50] of 1..100;
Var seng,smath : students;
Procedure inputset(var s : students; m:integer);
Var i,x: integer;
Begin
s:=[ ];
i:=0;
While (i<m) do
begin
writeln(„input students number „);
readln(x);
if (x in s) then
writeln(„ you input this number befor please enter
another number „)
else
begin
i:=i+1;
s:=s+[x];
end;
end;
End;
numbers of students](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-32-320.jpg)
![Procedure printset(s :students);
Var i:integer;
Begin
i:=1;
While (s<>[ ]) do
begin
if (i in s) then
begin
write(i:5);
s:=s-[ i ];
end;
i:=i+1;
end;
writeln;
End;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-33-320.jpg)
![Procedure deletestd(var s,n : students);
Var k,i,x ; integer;
Begin
n:= [ ];
Randomize;
i:=0;
Writeln(„enter the number you want to go throw out „);
Readln(x);
While (i<x) do
begin
k:= random(100) + 1;
if ( k in s ) then
begin
s:=s – [ k ];
seng:= seng – [ k ];
smath:=smath – [ k ];
i:=i+1;
n:=n + [ k ];
end;
end;
End;
بلاطنا حػىًجي
ان فًصىني يج ىًػح
انرقاطغ
:Randomize يقىو ترىنيذ
أرقاو ػشىائيح أػر اًدا ػهى
ساػح ان ظُاو
:Random(100)=0..99;
Random(100)+1=1..100](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-35-320.jpg)
![Procedure setinArray(s: students; var a: numbers ; var k: integer);
Var i : integer;
Begin
K:=0;
For i:=1 to 100 do
If (i in s) then
begin
k:=k+1;
a[k]:=i;
end;
End;
ي أجم اسرذػاء
انشؼاع في انثر اَيج
انرئيسي](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-36-320.jpg)
![Var nmath,neng,k,i :integer;
Aunaccepted : numbers;
Sunaccepted,sboth : students;
Begin
Writeln(„enter the number of math students „);
Readln(nmath);
Inputset(smath,nmath);
Writeln(„enter the number of English students „);
Readln(neng);
Inputset(seng,neng);
Bothsub(smath , seng , sboth);
Printset(sboth);
Deletestd(sboth,Sunaccepted);
Printset(Sunaccepted);
setinArray(Sunaccepted,Aunaccepted,k);
For i:=1 to k do
Writeln(Aunaccepted[i]:5);
Readln;
End.](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-37-320.jpg)



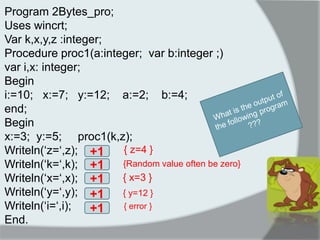
![Programme P-Matrix;
Const nMax=20; mMax=20;
Type Matrix=array[1..nmax,1..mmax] of real;
Var A,B,Add,mult :Matrix;
n1,n2 :1..nmax;
m1,m2 :1..mmax;
min: integer;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-42-320.jpg)
![Procedure ReadMat(Var: n:1..nmax;var m:1..mmax; var A:matrix);
Var i,j:integer;
begin
writeln(„enter the first Dimention of matrix< ‟ ,nmax);
Readln(n);
writeln(„enter the second Dimention of matrix< ‟ ,mmax);
Readln(m);
for i:=1 to n do
begin
for j:=1 to m do read(A[I,j]); {hint}
readln; {hint}
end;
end;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-43-320.jpg)
![Procedure WriteMat(Var: n:1..nmax;var m:1..mmax; var A:matrix);
Var i,j:integer;
begin
for i:=1 to n do
begin
for j:=1 to m do write(A[i,j],‟ ‟);
writeln;
end;
end;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-44-320.jpg)
![Function MinOfMatrix(n:1..nmax,m:1..mmax;A:matrix):real
Var i,j:integer; min:real;
begin
min:=A[1,1];
For i:=1 to n do
for j:=1 to m do
if (A[i,j]<min) then
min:=A[i,j];
MinOfMatrix:=min;
end;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-45-320.jpg)
![Procedure Add_Tow_Matrix(n1,n2:1..nmax; m1,m2:1..mmax; var n3:1..nmax; var m3:1..mmax; var c:Matrix);
Var i,j:integer;
begin
if(n1<>n2)or(m1<>m2) then
writeln(„the addition is impossible‟);
else
begin
n3:=n1; m3:=m1;
for i:=1 to n3 do
for j:=1 to m3 do
C[i.j]:=A[i,j]+B[i,j];
end;
end;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-46-320.jpg)
![Procedure Mult_Tow_Matrix(n1,n2:1..nmax; m1,m2:1..mmax; var n3:1..nmax; var m3:1..mmax; var c:Matrix);
Var i,j,k:integer;
begin
if(n1<>m2) then
writeln(„the multi is impossible‟);
else
begin
n3:=n2; m3:=m1; { A(m1,n1)*B(m2,n2)=C(m3,n3)}
for i:=1 to n3 do
for j:=1 to m3 do
begin
C[i,j]=0;
for k:=1 to m2
C[i.j]:= C[i.j] +A[i,k]*B[k,j];
end;
end;
end;](https://image.slidesharecdn.com/2bytesprog2course2014c1sets-141203172744-conversion-gate01/85/2Bytesprog2-course_2014_c1_sets-47-320.jpg)