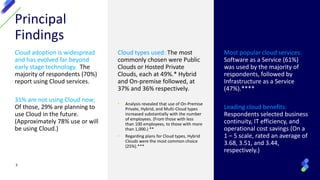
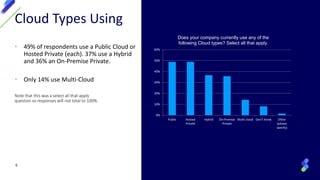
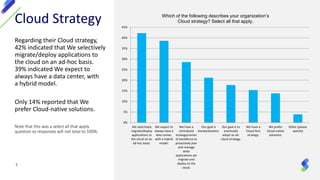
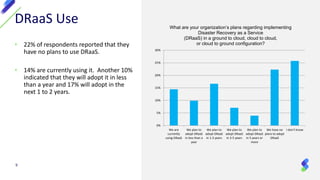
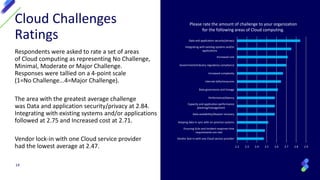
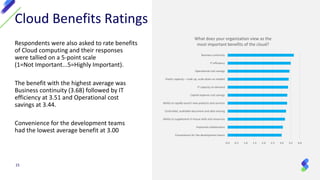
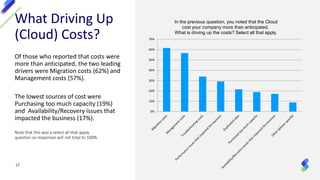
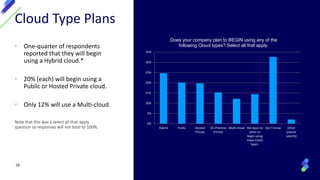
The survey found that cloud adoption is widespread, with 70% of respondents using cloud services. Public clouds and hosted private clouds were most commonly used (49% each). The top benefits cited were business continuity, IT efficiency, and cost savings. However, security/privacy was the top concern. While IT organizations had primary responsibility for cloud security and management, these were seen as ongoing challenges. Respondents indicated that cloud costs had exceeded expectations more often than not, driven mainly by migration and management costs. Looking ahead, hybrid cloud was the most common planned new deployment, indicating cloud strategies remain evolving.