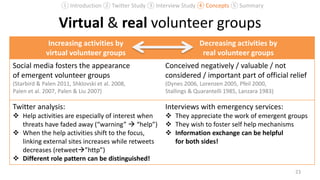
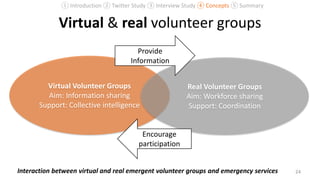
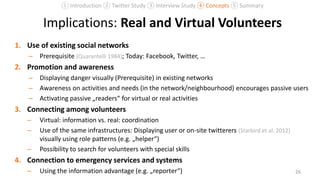
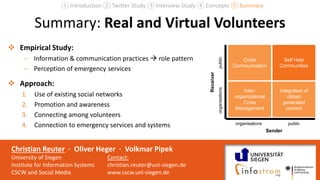
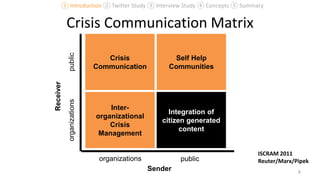
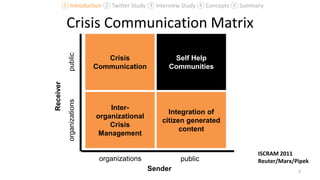
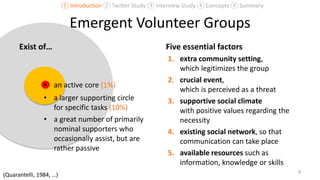
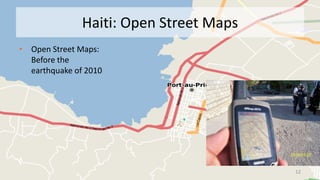
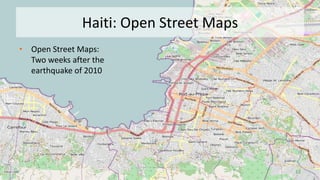
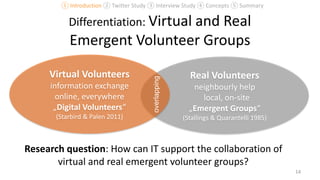
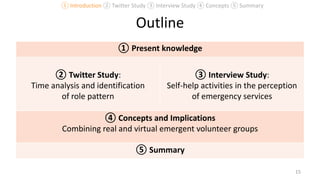
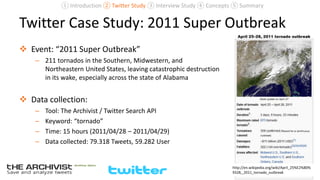
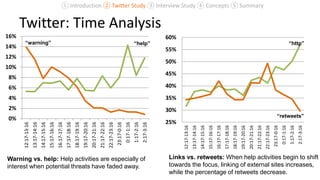
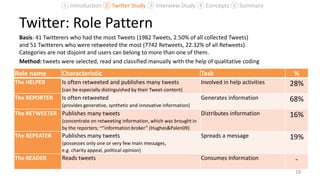
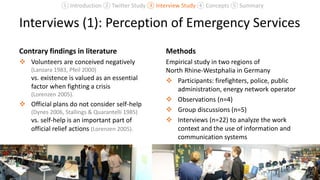
The document explores the integration of real and virtual volunteer groups in crisis management, focusing on how social media can support collaboration during emergencies. It discusses various studies, including a Twitter analysis during the 2011 Super Outbreak, highlighting the roles of volunteers and their effectiveness in crisis situations. The findings suggest that existing social networks and improved communication strategies can enhance the functionality of both volunteer types in supporting emergency services.






![Interviews (2): Perception of Emergency Services
Helpful: “Particularly during heavy rainfalls
self-help would be sometimes very helpful;
[…] Instead of calling us and writing down
that you have 2 cm water in the
basement.” (I05).
Information: “When somebody calls us,
who has seen something […], then we
certainly ask whether […] they have a gas
tank or whatever kind of heating system
they have.” (I07)
Legal basis: “Everything we do must have a
legal basis. […] A civil self-help group is not
a unit of the emergency service. After all,
we couldn’t utilize them, even if we wanted
to.” (I06) 21
Appearance: “The more you are in the
countryside, the more the citizens support
each other and the less they call the
state.” (I09)
Entitlement: „As you can see very clearly,
the entitlement has increased extremely
[...]. Since they call that the manhole cover
is located next ten centimeter.“ (I09)
Interest: „Our interest is to sensitize the
population that self-help mechanisms
develop” (I05).
① Introduction ② Twitter Study ③ Interview Study ④ Concepts ⑤ Summary](https://image.slidesharecdn.com/13-1600reuter-130702045852-phpapp02/85/Combining-Real-and-Virtual-Volunteers-through-Social-Media-21-320.jpg)