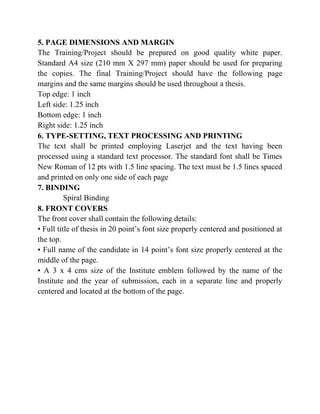
This document provides guidelines for students to follow when preparing their six-week industrial training report at Lovely Professional University in India. It outlines the required format and structure of the report, including formatting of preliminary pages, chapters, tables, figures, and references. Key requirements include having 5 chapters (Introduction, Company Profile, Training/Project Identification, Implementation Details, and Results and Discussion), a minimum of 10 references, and specific formatting for the cover page, table of contents, and other elements. The guidelines are intended to help students submit reports that are of the highest quality and follow a consistent structure.




![portrait style. Small size table and figures (less than half of writing area of a
page) should be incorporated within the text, while larger ones may be
presented in separate pages. Table and figures shall be numbered chapter –
wise. For example, the fourth figure in Chapter 5 will bear the number figure
5.4 or Fig.5.4. Table number and title will be placed above the table while the
figure number and caption will located below the figure and will be centered
left. Reference for Table and Figures reproduced from elsewhere shall be
cited in the last and separate line in the table and figure caption, e.g. [12].
Text in tables may be in font size of 10.
Table 4.6: Cell values and key sequence
Equations
All the equations should be typed in equation editor/LaTeX and should be
properly numbered.
For Example,
(Required no. of pages: 4-7 Pages)](https://image.slidesharecdn.com/115751guidelinesforpreparingtrainingreport2-130801135403-phpapp01/85/11575-1-guidelines-for-preparing-training-report-2-10-320.jpg)