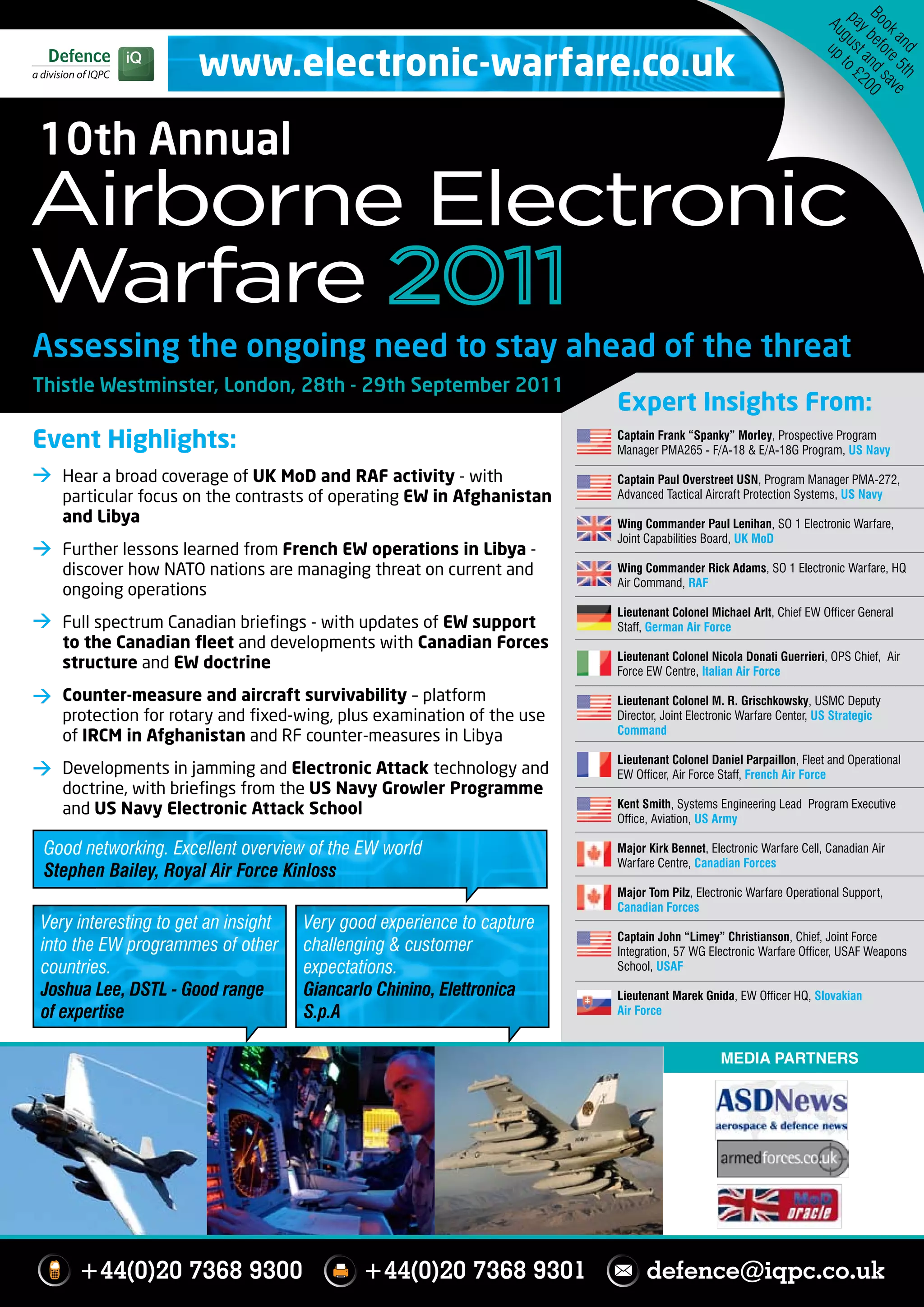
This document is a program for the 10th Annual Airborne Electronic Warfare conference taking place from September 28-29, 2011 in London. The conference will feature briefings from military experts from countries such as the UK, US, Canada, Germany, France and Italy on topics related to electronic warfare capabilities, operations, and technology developments. Presentations will provide insights into ongoing electronic warfare programs and lessons learned from recent operations in areas like Afghanistan and Libya. The event aims to give attendees an overview of the electronic warfare world and help assess needs to stay ahead of evolving threats.