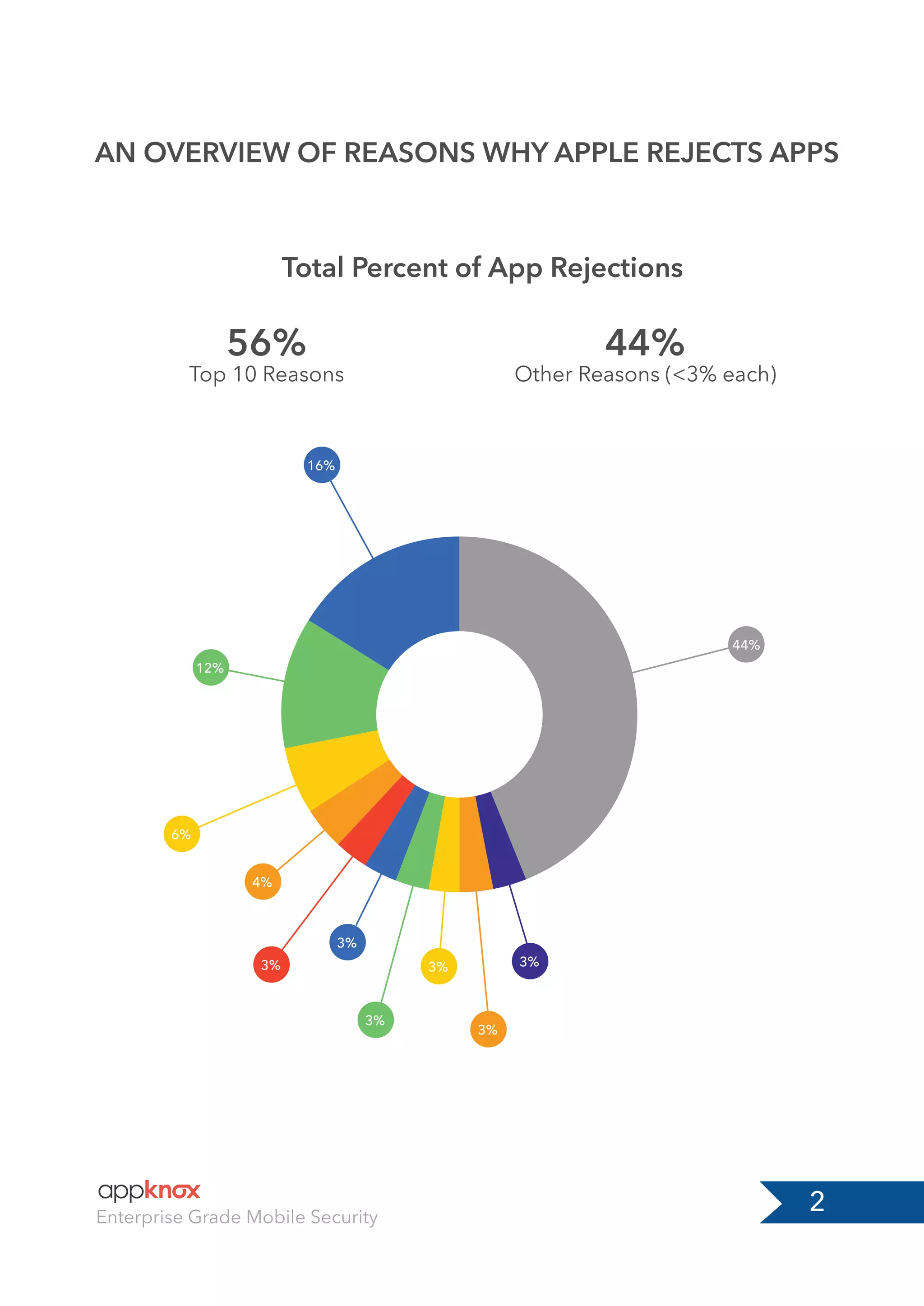
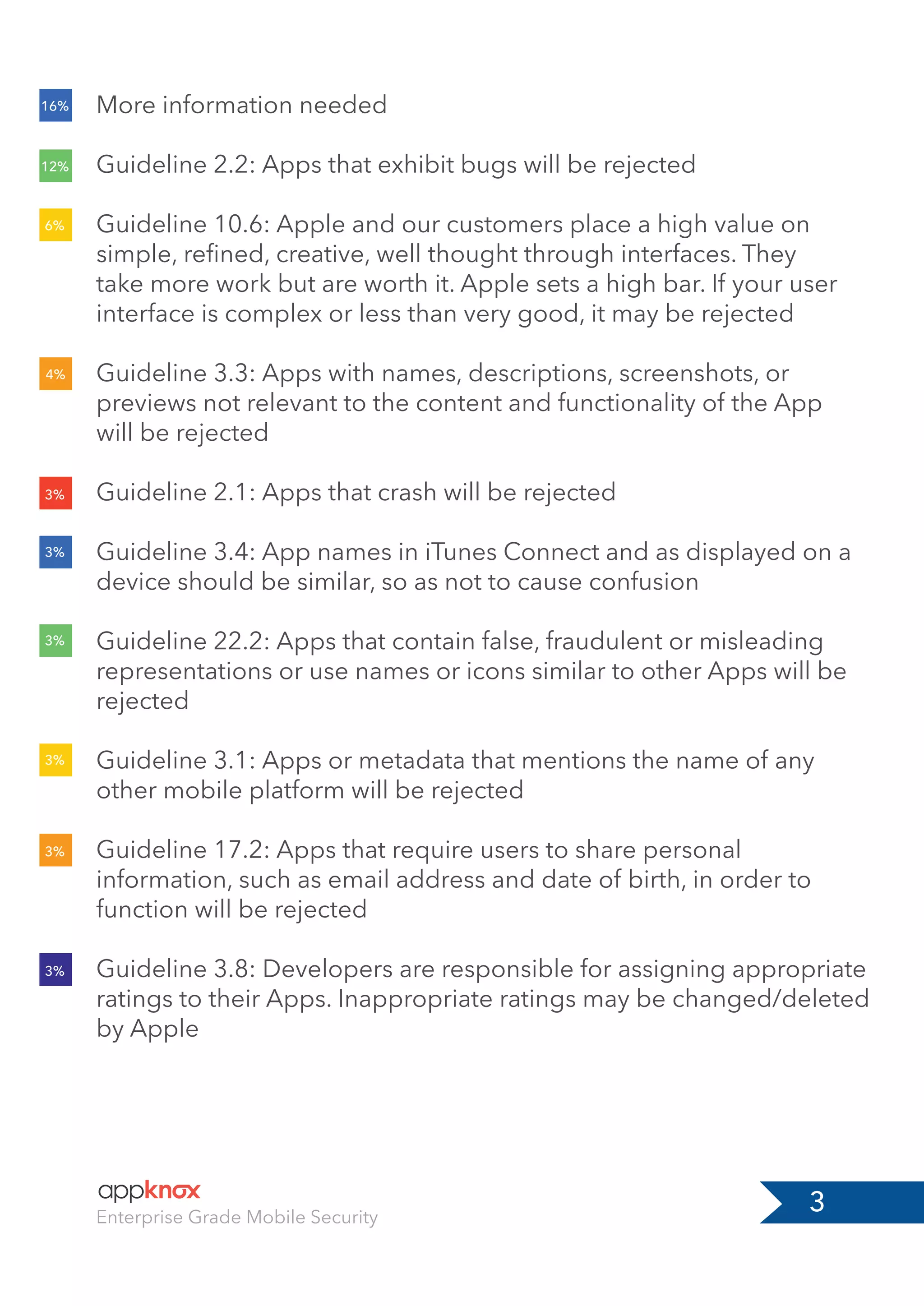
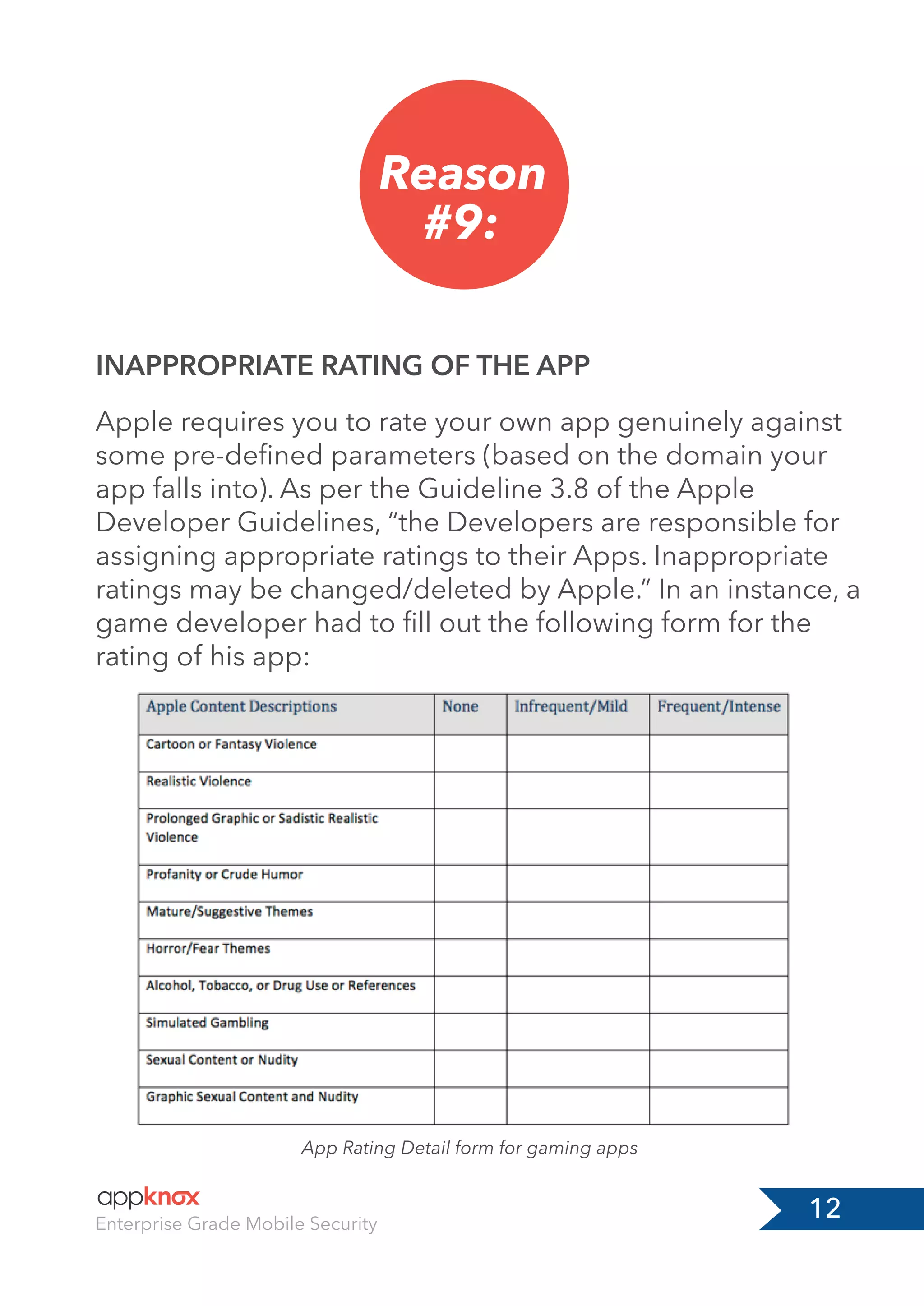
This document outlines the top ten reasons why Apple rejects apps from their App Store, including issues like insufficient information, bugs, substandard user interfaces, and violations of legal requirements. It highlights the importance of complying with Apple's guidelines for submission and offers solutions to avoid common pitfalls. Developers must ensure their apps meet quality standards, provide accurate information, and respect intellectual property rights to be successfully listed on the App Store.