contoh Shortcut dot batch
•Download as TXT, PDF•
0 likes•200 views
contoh shortcut format batch
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (7)
Similar to contoh Shortcut dot batch
Similar to contoh Shortcut dot batch (20)
Creating a keystroke logger in unix shell scripting

Creating a keystroke logger in unix shell scripting
Windows defender scheduled scan set up in windows 8

Windows defender scheduled scan set up in windows 8
Penetration Testing for Easy RM to MP3 Converter Application and Post Exploit

Penetration Testing for Easy RM to MP3 Converter Application and Post Exploit
How to remove password if you forgot windows 7 password apps for windows

How to remove password if you forgot windows 7 password apps for windows
Recently uploaded
Recently uploaded (20)
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
SQL Database Design For Developers at php[tek] 2024![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
SQL Database Design For Developers at php[tek] 2024
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Enhancing Worker Digital Experience: A Hands-on Workshop for Partners

Enhancing Worker Digital Experience: A Hands-on Workshop for Partners
contoh Shortcut dot batch
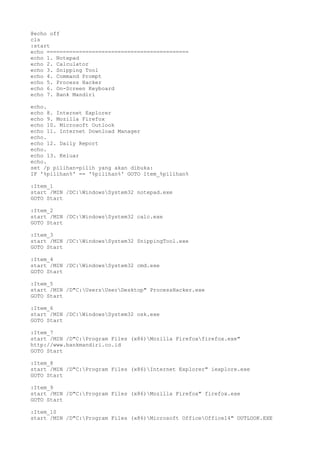
- 1. @echo off cls :start echo ============================================ echo 1. Notepad echo 2. Calculator echo 3. Snipping Tool echo 4. Command Prompt echo 5. Process Hacker echo 6. On-Screen Keyboard echo 7. Bank Mandiri echo. echo 8. Internet Explorer echo 9. Mozilla Firefox echo 10. Microsoft Outlook echo 11. Internet Download Manager echo. echo 12. Daily Report echo. echo 13. Keluar echo. set /p pilihan=pilih yang akan dibuka: IF '%pilihan%' == '%pilihan%' GOTO Item_%pilihan% :Item_1 start /MIN /DC:WindowsSystem32 notepad.exe GOTO Start :Item_2 start /MIN /DC:WindowsSystem32 calc.exe GOTO Start :Item_3 start /MIN /DC:WindowsSystem32 SnippingTool.exe GOTO Start :Item_4 start /MIN /DC:WindowsSystem32 cmd.exe GOTO Start :Item_5 start /MIN /D"C:UsersUserDesktop" ProcessHacker.exe GOTO Start :Item_6 start /MIN /DC:WindowsSystem32 osk.exe GOTO Start :Item_7 start /MIN /D"C:Program Files (x86)Mozilla Firefoxfirefox.exe" http://www.bankmandiri.co.id GOTO Start :Item_8 start /MIN /D"C:Program Files (x86)Internet Explorer" iexplore.exe GOTO Start :Item_9 start /MIN /D"C:Program Files (x86)Mozilla Firefox" firefox.exe GOTO Start :Item_10 start /MIN /D"C:Program Files (x86)Microsoft OfficeOffice14" OUTLOOK.EXE
- 2. GOTO Start :Item_11 start /MIN /D"C:Program Files (x86)Internet Download Manager" IDMan.exe GOTO Start :Item_12 D: cd Documents "Daily Report Mei (Maulana Kurniantoro).xlsx" GOTO Start :Item_13 exit
