More Related Content
Similar to LogRhythm E Phi Use Case
Similar to LogRhythm E Phi Use Case (20)
LogRhythm E Phi Use Case
- 1. USE CASE
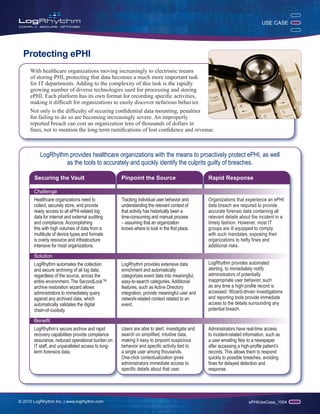
Protecting ePHI
With healthcare organizations moving increasingly to electronic means
of storing PHI, protecting that data becomes a much more important task
for IT departments. Adding to the complexity of this task is the rapidly
growing number of diverse technologies used for processing and storing
ePHI. Each platform has its own format for recording specific activities,
making it difficult for organizations to easily discover nefarious behavior.
Not only is the difficulty of securing confidential data mounting, penalties
for failing to do so are becoming increasingly severe. An improperly
reported breach can cost an organization tens of thousands of dollars in
fines, not to mention the long term ramifications of lost confidence and revenue.
LogRhythm provides healthcare organizations with the means to proactively protect ePHI, as well
as the tools to accurately and quickly identify the culprits guilty of breaches.
Securing the Vault Pinpoint the Source Rapid Response
Challenge
Healthcare organizations need to Tracking individual user behavior and Organizations that experience an ePHI
collect, securely store, and provide understanding the relevant context of data breach are required to provide
ready access to all ePHI-related log that activity has historically been a accurate forensic data containing all
data for internal and external auditing time-consuming and manual process relevant details about the incident in a
and compliance. Accomplishing – assuming that an organization timely fashion. However, most IT
this with high volumes of data from a knows where to look in the first place. groups are ill equipped to comply
multitude of device types and formats with such mandates, exposing their
is overly resource and infrastructure organizations to hefty fines and
intensive for most organizations. additional risks.
Solution
LogRhythm automates the collection LogRhythm provides extensive data LogRhythm provides automated
and secure archiving of all log data, enrichment and automatically alerting, to immediately notify
regardless of the source, across the categorizes event data into meaningful, administrators of potentially
entire environment. The SecondLook™ easy-to-search categories. Additional inappropriate user behavior, such
archive restoration wizard allows features, such as Active Directory as any time a high-profile record is
administrators to immediately query integration, provide meaningful user and accessed. Wizard-driven investigations
against any archived data, which network-related context related to an and reporting tools provide immediate
automatically validates the digital event. access to the details surrounding any
chain-of-custody. potential breach.
Benefit
LogRhythm’s secure archive and rapid Users are able to alert, investigate and Administrators have real-time access
recovery capabilities provide compliance search on simplified, intuitive data, to incident-related information, such as
assurance, reduced operational burden on making it easy to pinpoint suspicious a user emailing files to a newspaper
IT staff, and unparalleled access to long- behavior and specific activity tied to after accessing a high-profile patient’s
term forensics data. a single user among thousands. records. This allows them to respond
One-click contextualization gives quickly to possible breaches, avoiding
administrators immediate access to fines for delayed detection and
specific details about that user. response.
© 2010 LogRhythm Inc. | www.logrhythm.com ePHIUseCase_1004