1) As security threats become more advanced and complex, traditional security solutions are struggling to effectively detect insider threats and prevent breaches.
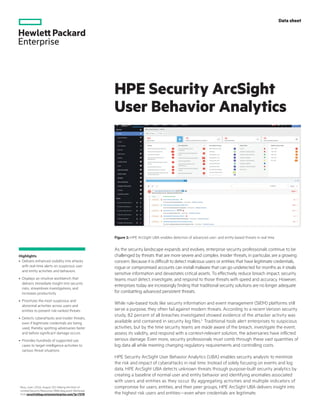
2) HPE Security ArcSight User Behavior Analytics (UBA) uses machine learning and behavioral analytics to detect anomalies and suspicious activities in real time, enabling faster identification and response to threats even from legitimate credentials.
3) By analyzing user and entity behaviors across peer groups and correlating activities with other threat indicators, HPE ArcSight UBA can prioritize the highest risk users and entities to help reduce the impact of cyberattacks.