Policy report barrat & associates ltd
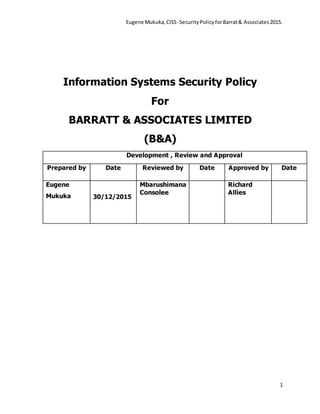
- 1. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 1 Information Systems Security Policy For BARRATT & ASSOCIATES LIMITED (B&A) Development , Review and Approval Prepared by Date Reviewed by Date Approved by Date Eugene Mukuka 30/12/2015 Mbarushimana Consolee Richard Allies
- 2. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 2 TABLE OF CONTENT INTRODUCTION 1.1 MALWARE AND VIRUS PROTECTION 1.1.1 Overview 1.1.2 Objective 1.1.2.1 How Viruses Can Infect Barrat & Associates Network 1.1.2.2 How Barrat & Associates IS Department should Fight Viruses 1.1.2.3 IS Responsibilities 1.1.2.4 Users’ Responsibility 1.2 CRYPTOGRAPHY PROCEDURE- NETWORK PARAMETER & REMOTE ACCESS SECURITY 1.2.1 Overview 1.2.2 Purpose 1.2.3 Procedure statements: 1.2.3.1 Data encryption for secure network transit 1.2.3.2 Required use of encryption Cryptography Policy 1.2.3.3 Required use of digital signatures 1.2.3.4 Cryptography implementation 1.3 REMOVABLE MEDIA PROCEDURE – USB AND OTHER PORTABLE DEVICES 1.3.1 Overview 1.3.2 Purpose 1.3.3 Scope 1.3.4 Procedure statements:
- 3. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 3 1.4 ACCESS RIGHTS PROCEDURE 1.4.1 Overview 1.4.2 Objective 1.4.3 Procedure Statements 2.1 PHYSICAL AND ENVIRONMENTAL SECURITY 2.1.1 Employee Responsibilities 3.1 DISASTER RECOVERY PROCEDURE 3.1.1 Roles and Responsibilities 3.1.2 Network Recovery Team 3.1.3 Server Recovery Team 3.2 Database Disaster Recovery 3.2.1 Web Application Disaster Recovery 3.2.2 Disaster Declaration 4.1 PASSWORD GUIDELINES PROCEDURE 4.1.1 Password Construction Guidelines 5.1 APPENDICES Appendix 1: Access Authorization Form Appendix 2 Risk Classification 6.1 REFFERENCES
- 4. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 4 INTRODUCTION The purpose of this Information Security is to protect the company information and its assets by ensuring the confidentiality, integrity and availability of information in order to mitigate business and legal risk, protecting corporate image and provide management with direction as well as support for Information Systems. 1.1 MALWARE AND VIRUS PROTECTION 1.1.1 Overview Availability, performance and security of the company’s system represent essential core assets to the daily operations of Barrat & Associates Limited (B & A). Viruses and other forms of malicious code represent a significant threat to the assets of the company. In order to combat this threat, a comprehensive company security policy must include antivirus provisions to detect, remove and protect against viral infections. Antiviral procedures should include identification of current and potential viral threats, computers and systems at risk of infection, files at risk of infection, infected computers and infected files. Infection patterns should be tracked and analyzed to identify chronic internal and external threats. Many virus infections threaten other computers sharing the infected computer's network. Infected computers must be cleared of viral infections immediately. Files that can be cleaned should have the viral code removed, thus returning them to pre-infected state. Files that cannot be cleaned must be quarantined until such time as they can be replaced with uninfected copies. If all efforts at removing viral infection fail, the computer's hard drive must be formatted and all software reinstalled using clean licensed copies. If an infected computer is deemed capable of infecting or affecting other computers or the network, the infected computer must be disconnected from the network until it is serviced by an IS representative or designee who will verify that the computer is virus-free. Antivirus activities must be centrally managed. New viruses represent a continual threat, requiring continual research to plan proactive measures against them. Users must be
- 5. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 5 educated about viral threats and the computing practices required protecting against infection. Whenever a new viral threat appears, the user community must be warned about the new threat. Up-to-date antivirus software must be distributed and its availability advertised to the B & A user community. Viruses can infect B & A Information systems by a wide variety of methods including email messages, the Internet and through accessing infecting files contained on USB drives, floppy disks, CDs and other portable devises used by B & A Users. Viruses can propagate very quickly as they are easily spread to other PCs connected to a computer network or the Internet. It is vitally important therefore that IS System connected to the network has anti-virus software installed and that this protective software is kept current. Viruses can also attack vulnerabilities in applications such as Microsoft Office and operating systems such as Windows and this software must also be made secure by the application of critical patches and updates as and when required. In order to combat viruses on the email gateway, servers and personal computing systems, Limited B & A has adopted a suite of system protection products. To prevent infection of B & A computer systems by computer viruses and other malicious code, this policy is intended to prevent major and widespread damage to user applications, files and hardware. 1.1.2 Objective: This procedure outlines how various viruses can infect B & A network, how B & A’s IS/IT department tries to prevent and or minimize infections and how B & A’s network users should respond to a virus if they suspect one has infected the network. 1.1.2.1 How Viruses Can Infect Barrat & Associates Network
- 6. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 6 There are actually three various types of computer viruses: true viruses, Trojan horses and worms. True viruses actually hide themselves, often as macros, within other files, such as spreadsheets or Word documents. When an infected file is opened from a computer connected to B & A’s network, the virus can spread throughout the network and may do damage to data resources. A Trojan horse is an actual program file that, once executed, doesn't spread but can damage the computer on which the file was run. A worm is also a program file that, when executed, can both spread throughout a network and do damage to the computer from which it was run. Viruses can enter B & A’s network in a variety of ways: i. E-mail: By far, most viruses are sent as e-mail attachments. These attachments could be working documents or spreadsheets, or they could be merely viruses disguised as pictures, jokes, etc. These attachments may have been knowingly sent by someone wanting to infect the organization's network or by someone who does not know the attachment contains a virus. However, once some viruses are opened, they automatically e-mail themselves and the sender may not know his or her computer is infected. ii. USB storage Disk, Diskette, CD, Zip disk, or other portable media: Viruses can also spread via various types of storage media. As with e-mail attachments, the virus could hide within a legitimate document or spreadsheet or simply be disguised as another type of file. iii. Software downloaded from the Internet: Downloading software via the Internet can also be a source of infection. As with other types of transmissions, the virus could hide within a legitimate document, spreadsheet, or other type of file. iv. Instant messaging attachments: Although less common than e-Mail attachments, more viruses are taking advantage of instant messaging software. These attachments work the same as e-mail viruses, but they are transmitted via instant messaging software.
- 7. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 7 1.1.2.2 How Barrat & Associates IS Department should Fight Viruses IS Department should fight viruses in the following ways: i. Firewall: B & A’s IS should deploy a firewall which should monitor all incoming traffic. A firewall is a system designed to prevent unauthorized access to or from a private network. Firewalls can be implemented in both hardware and software, or a combination of both. Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to the Internet, especially intranets. All messages entering or leaving the B & A network should pass through the firewall, which will examine each message and blocks those that do not meet the specified security criteria. ii. Scanning Internet traffic: All Internet traffic coming to and going from the network must pass through company servers and other network devices. Only specific types of network traffic are allowed beyond the organization’s exterior firewalls. For example, an e-mail message that originates outside of the network must pass through the antivirus protection firewall before it is allowed to enter the e-mail server. This device routes suspicious e-mail and attachments to an isolated storage device, defeating the purpose of a virus. Mail scanners are also installed on the e-mail server filtering suspicious virus mails and spam iii. Running server and workstation antivirus software: All vulnerable servers should run antivirus scanning software approved by the director of IT. This software should scan the file-sharing data stores, looking for suspicious code. Antivirus protection software should also be installed on all the organization workstations. This software scans all data written to or read from a workstation's hard drive. If it finds something suspicious, it isolates the dubious file on the computer and automatically notifies the help desk.
- 8. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 8 iv. Routinely updating virus definitions: Everyday, the anti-virus server scanning programs checks the antivirus program's control centre for updated virus definitions. These definition files allow the software to detect new viruses. If a new virus definition file is available, the virus scanning software is automatically updated and then the system administrator is informed. When end users turn on their computers located in the B & A network domain at the beginning of the workday, the workstation virus protection program checks with a B & A server on the network for updates. The workstation program will then download and install the update automatically, if one exists. The windows server also runs a utility called a SUS server (Software update service) which downloads all patches from the Microsoft site and installs them onto individual client PCs. Users must note that such online protection facilities may not be available during these times that a computer resource (e.g. laptop) is taken away from the B & A domain. Users are encouraged to make arrangements for offline solutions from the IS Helpdesk when intending to travel outside their normal station of duty. 1.1.2.3 IS Responsibilities The IS department shall: i. Install and maintain appropriate antivirus software on all computers. ii. Respond to all virus attacks, destroy any virus detected and document each incident. iii. Update software with new patches and definitions. iv. Play an advisory role. 1.1.2.4 Users’ Responsibility i. Employees shall not knowingly introduce a computer virus into the company computer systems. ii. Employees shall not load diskettes or attach USB storage disk systems with information of unknown origin to company computers.
- 9. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 9 iii. Incoming diskettes or USB storage disks shall be scanned for viruses before they are read. iv. Users must not prevent anti-virus updates being applied to their computer. v. Users must not disable the anti-virus software on their computers for any purpose without seeking the authority from the Director IT. vi. Users must allow regular updates to be applied to IS approved software installed on their computers and restart their systems at least once a week. Users who have permission to install their own software on their computers must ensure that this software is kept secure. 1.2 CRYPTOGRAPHY PROCEDURE- NETWORK PARAMETER & REMOTE ACCESS SECURITY 1.2.1 Overview This policy document sets out principles and expectations about when and how encryption of B & A digital information should (or should not) be used. 1.2.2 Purpose The purpose of this procedure is to protect the confidentiality and integrity of B & A’s information by applying appropriate levels of cryptographic controls through established processes and procedures. 1.2.3 Procedure statements: 1.2.3.1 Data encryption for secure network transit Provided no other restrictions apply, it is permitted for all B & A staffs to use computer systems which would normally and by default use encryption, in order to secure data in transit on a communications network.
- 10. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 10 Whenever possible and appropriate, encryption shall be used to support security of remote access connections to the B & A network and computing resources. 1.2.3.2 Required use of encryption Cryptography Policy Loss, theft, or unauthorized disclosure of certain information could be detrimental to B & A Ltd, staff or members. Such information includes that defined as personal data by the Data Protection and or classification. Where B & A is handling digital personal data that cannot be sufficiently secured by physical controls, the data must be encrypted. 1.2.3.3 Required use of digital signatures Significant B & A’s business information being communicated electronically should be authenticated by use of digital signatures; information received without a digital signature should not be relied upon. Staff involved must assess the level of risk and decide whether to require use of digital signatures or whether to use an alternative means to authenticate the communication. 1.2.3.4 Cryptography implementation All encryption products, standards and procedures used to protect sensitive B & A data must be ones which have been proven to work effectively. 1.3 REMOVABLE MEDIA PROCEDURE – USB AND OTHER PORTABLE DEVICES 1.3.1 Overview Removable media is a well-known source of malware infections and has been directly tied to the loss of sensitive information in B & A Ltd.
- 11. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 11 1.3.2 Purpose The purpose of this policy is to minimize the risk of loss or exposure of sensitive information maintained by B & A and to reduce the risk of acquiring malware infections on computers operated by the company. 1.3.3 Scope This policy covers all computers and servers operating in B & A Ltd. 1.3.4 Procedure statements: B & A Staff may only use removable media in their work computers. B & A removable media may not be connected to or used in computers that are not owned or leased by the company without explicit permission of the ICT security department. Sensitive information should be stored on removable media only when required in the performance of your assigned duties or when providing information required by other state or federal agencies. When sensitive information is stored on removable media, it must be encrypted in accordance with the B & A acceptable Encryption Policy. 1.4 ACCESS RIGHTS PROCEDURE 1.4.1 Overview Access rights to resources need to be controlled to prevent both intentional and accidental manipulation of data. Only users permitted to certain resources will be allowed access to them. This includes both logical and physical access. Access to resources should be done through the supervisors who will communicate with the Manager of IS/IT to ascertain if a user needs access to the requested resource. 1.4.2 Objective
- 12. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 12 The objective of this procedure is to establish the guidelines on how to request for access to a resource. 1.4.3 Procedure Statements i. Only IT staff shall enter sensitive areas like Server Rooms. Contractors, consultants and other third party staff can only enter such places with permission from Manager of IS/IT and must be accompanied by an IS staff member ii. All applications shall have an in built security to control access to application code and data. iii. Remote access to B & A network shall only be allowed if the data being sent out is encrypted and user authentication is done. iv. Administrative rights and access to computer operating system configuration will only be allowed to IS staff only who are authorized to carry out systems maintenance and administration. v. Access rights that have not been assigned to a user will be denied. vi. User rights can either be granted or revoked only by the IS department if a user violates the policy. vii. Access rights granted to users should be well documented in an access control document; this document shall be kept securely by the system owners. viii. All access rights records must be maintained by system owners who will carry out the updates as employees are transferred, change positions or fired and or retire. 2.1 PHYSICAL AND ENVIRONMENTAL SECURITY It is company policy to protect computer hardware, software, data and documentation from misuse, theft, unauthorized access and environmental hazards. The Computer Room housing sensitive and or critical processing facilities and communications equipment shall be protected from unauthorized entry by use of physical entry controls.
- 13. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 13 2.1.1 Employee Responsibilities The directives below apply to all employees: i. USB and disk storage units should be stored securely or out of sight when not in use. If they contain highly sensitive or confidential data, they must be locked up. ii. Storage units should be kept away from environmental hazards such as heat, direct sunlight and magnetic fields. iii. Critical computer equipment e.g., file servers, must be protected by an uninterruptible power supply (UPS). Other computer equipment should be protected by a surge suppressor. iv. Environmental hazards to hardware such as flood, smoke, liquids, high or low humidity and extreme heat or cold should be avoided near computer equipment and peripherals v. Since the IS Senior Manager is responsible for all equipment installations, disconnections, modifications and relocations, employees are not to perform these activities unilaterally. This does not apply to temporary moves of portable and or Laptop computers for which an initial connection has been set up by IS vi. Employees shall not take shared portable equipment such as laptop computers out of the plant without the informed consent of their department manager. Informed consent means that the manager knows what equipment is leaving, what data is on it and for what purpose it will be used. vii. Employees should exercise care to safeguard the valuable electronic equipment assigned to them. 3.1 DISASTER RECOVERY PROCEDURE 3.1.1 Roles and Responsibilities
- 14. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 14 The following teams should be developed and trained to respond to a contingency event affecting B & A’s information systems. The Director IS/IT is the sponsor of this plan and all staff involved view the DRP in the same light. 3.1.2 Network Recovery Team The function of the Network recovery team is to implement the network recovery plan. The Network recovery team must communicate all issues using a status report. This status report is critical in tracking the issues as well as providing input into the post - mortem process. 3.1.3 Server Recovery Team The function of the Server Recovery team is to implement the server recovery procedure. Critical to the success of this team is the correct classification of the problem. The Server recovery team will be responsible for the successful resolution of the server related issues. 3.2 Database Disaster Recovery Database Recovery, the following activities must be initiated: i. Initiate the Database DR Process. ii. If SQL Backup tapes are stored off-site organize the immediate retrieval. iii. After a successful restore, identify all transactions that were lost (if any) iv. Send status reports to the Control Team (10 minute intervals). v. Communicate status of the Databases to B & A Director IT. vi. Restore system to original (or as close) state. vii. Provide input to post-mortem process. 3.2.1 Web Application Disaster Recovery For Application Recovery, the following activities must be initiated: i. Restore Application Services.
- 15. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 15 ii. File Verification Tasks. iii. Application Validation and Synchronization Tasks. iv. Original or New site restoration. v. Concurrent processing. vi. Plan deactivation. 3.2.2 Disaster Declaration The disaster declaration procedures must incorporate escalation procedures and clearly define what type of outages will determine the procedures to be followed. It must define who has the authority and responsibility to declare a disaster. Once a disaster is declared, the disaster recovery procedures will immediately govern the recovery process. In an emergency, B & A’s top priority is to preserve the health and safety of its staff before proceeding with the activation of the DRP.A disaster will be declared when the computer environment will have a major impact on data integrity. 4.1 PASSWORD GUIDELINES PROCEDURE 4.1.1 Password Construction Guidelines Passwords are used to access B & A systems. Poor, weak passwords are easily cracked and put the entire system at risk. Therefore, strong passwords are required. Try to create a password that is also easy to remember. Below are some guidelines on how to create a password:- i. Passwords should contain at least 8 characters
- 16. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 16 ii. Passwords should contain at least uppercase letters (e.g. N) or lowercase letters (e.g.) or a combination of both. iii. Passwords should contain at least alpha numerical characters (e.g. 5) iv. Passwords should contain at least special characters (e.g. $, *, &) v. Passwords should not be based on users’ personal information or that of his or her friends, family members, or pets. Personal information includes logon I.D., name, birthday, address, phone number, or any permutations thereof vi. Passwords should not be words that can be found in a standard dictionary (English or foreign) or are publicly known slang or jargon vii. Passwords should not be trivial, predictable or obvious viii. Passwords should not be based on publicly known fictional characters from books, films and so on ix. Passwords should not be based on the company's name or geographic location. 5.1 APPENDICES Appendix 1: Access Authorization Form I understand that: The permissions, profiles, privileges, accesses and other entrustments granted to me as a result of my association with (Name of Application)………………………………………………………… are based on the need to accomplish my assigned responsibility and authority. I also acknowledge that I will be the sole user of the password issued to me and will ensure that this password is kept secure at all times.
- 17. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 17 I am responsible for my adherence to the B & A’s policies and procedures identified by the IS/IT Department Accordingly, I agree to comply with the security requirements of B & A Limited. I acknowledge these understandings and agreements by my signature below. Name: ……………………………………………Department: ………………………………… Application(s): …………………………………………………………………. Signature: ………………………………………… Date: ……………………. I, ……………………………………………………..authorize the request for access to the mentioned application(s) by the person described above. Signature: ……………………………………….. Date: …………………………………. IS/IT OFFICE USE Name: ……………………………………………………………………………………………. I, a member of the IT department duly authorized to assign users access, have generated a new username and password for the applicant. Signature: ……………………………………………….. Date: ……………………… Appendix 2 Risk Classification Risk Classifications Risk Level Risk Description High The loss of confidentiality, integrity, or availability could be expected to have a severe or catastrophic adverse effect on B&A operations, its Assets or on its employees. Moderate The loss of confidentiality, integrity, or availability could be expected to have a serious adverse effect on B&A operations, its Assets or on its employees.
- 18. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 18 Risk Level Risk Description Low The loss of confidentiality, integrity, or availability could be expected to have a limited adverse effect on B&A operations, its Assets or on its employees. 6.1 REFFERENCES 1. Information Security Policies- SANS Institute, implementation of information security policies, http://www.sans.org/security-resources/policies, accessed throughout the development of this policy. 2. Laban, M., Krnjet in, S., & Niko lic, B. (2007). Risk management and risk assessment in the enterprise. Symposiumabout Occupational Safety and Health, Novi Sad, pp. 44-57 3. Boran, S., (2003).IT security cook book. Boran Consulting.
- 19. Eugene Mukuka,CISS -SecurityPolicyforBarrat& Associates2015. 19 4. Bristol University; Information Security Policy Documents; http://www.bristol.ac.uk/infosec/policies/docs. accessed on 23rd , 24th & 26th December 2016. 5. Risk Management. (2006). Implementation principles and Inventories for Risk Manage9ment/Risk Assess-ment methods and tools. Conducted by the Technical Department of ENISA Section Risk Manage-ment, June 2006. 6. Carl Claunch, (2015). Managing risk after support for windows Server 2003 end, ComputerWeekly.com http://www.computerweekly.com/feature/Managing-risk-after-support-for-Windows-Server- 2003-ends accessed on 9/11/2015 7. Braid, Matthew -Collecting ElectronicEvidence After a System Compromise, AusCERT,2001: 8. How to write information Security Policy, by Jennifer Bayuk; CSO June 16, 2009 8:00 AM PT Information Security Policy Development for compliance: ISO/IEC 27001, NIST SP 800-53, HIPAA Standard, PCI DSS V2.0,and AUP V5.0 9. P. Prasad; A Dynamically Reconfigurable Intrusion Detection System, Master of Science (MSc) Thesis, University of North Carolina State, 2003.
