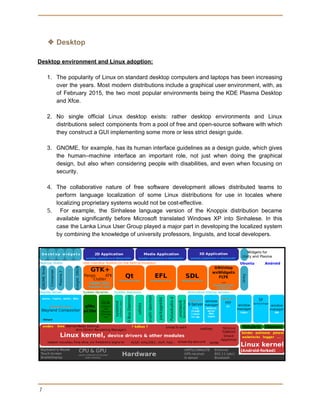
The document provides an overview of Linux as a family of free and open-source operating systems, detailing its architecture, hardware support, and various components such as memory and process management. It highlights Linux's prevalence in servers, supercomputers, and embedded systems, emphasizing its licensing under the GNU General Public License and the collaborative nature of its development. Additionally, the document discusses key concepts in security, space management, and the increasing popularity of Linux distributions in desktop use.