11 palo alto user-id concepts
•
0 likes•837 views
https://www.facebook.com/MostafaElLathyIT mostafa.it@hotmail.com https://www.youtube.com/channel/UCAEiVvBP3DbIKUcoZBcaHvQ
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
9 palo alto virtual routers concept (routing on palo alto)

9 palo alto virtual routers concept (routing on palo alto)
Palo Alto Networks y la tecnología de Next Generation Firewall

Palo Alto Networks y la tecnología de Next Generation Firewall
End to End Security With Palo Alto Networks (Onur Kasap, engineer Palo Alto N...

End to End Security With Palo Alto Networks (Onur Kasap, engineer Palo Alto N...
Similar to 11 palo alto user-id concepts
Similar to 11 palo alto user-id concepts (20)
Deploying Next Generation Firewalling with ASA - CX

Deploying Next Generation Firewalling with ASA - CX
Material best practices in network security using ethical hacking

Material best practices in network security using ethical hacking
Cortana Analytics Workshop: Cortana Analytics -- Security, Privacy & Compliance

Cortana Analytics Workshop: Cortana Analytics -- Security, Privacy & Compliance
Bright talk mapping the right aut solution for you 2014 final (1)

Bright talk mapping the right aut solution for you 2014 final (1)
Latest Developments in Cloud Security Standards and Privacy

Latest Developments in Cloud Security Standards and Privacy
Ladies Be Architects: Integration Study Group: Security & State Management

Ladies Be Architects: Integration Study Group: Security & State Management
Endpoint Agent Part 3: LAN, Wireless, Gateways and Proxies

Endpoint Agent Part 3: LAN, Wireless, Gateways and Proxies
Cloud Security Standards: What to Expect and What to Negotiate V2.0

Cloud Security Standards: What to Expect and What to Negotiate V2.0
Technology Overview - Validation & ID Protection (VIP)

Technology Overview - Validation & ID Protection (VIP)
Recently uploaded
Recently uploaded (20)
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Spring Boot vs Quarkus the ultimate battle - DevoxxUK

Spring Boot vs Quarkus the ultimate battle - DevoxxUK
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...

Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
CNIC Information System with Pakdata Cf In Pakistan

CNIC Information System with Pakdata Cf In Pakistan
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
11 palo alto user-id concepts
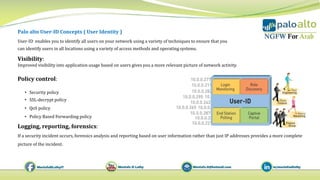
- 1. Palo alto User-ID Concepts ( User Identity ) User‐ID enables you to identify all users on your network using a variety of techniques to ensure that you can identify users in all locations using a variety of access methods and operating systems. Visibility: Improved visibility into application usage based on users gives you a more relevant picture of network activity. Policy control: • Security policy • SSL-decrypt policy • QoS policy • Policy Based Forwarding policy Logging, reporting, forensics: If a security incident occurs, forensics analysis and reporting based on user information rather than just IP addresses provides a more complete picture of the incident.
- 2. 1. ( Group mapping ) User-to-Group mapping: This process learns group names then the users that are members of the groups. It allows the firewall to write policy and create reports based on Groups rather than individual users. 2. ( User mapping ) User-to-IP mapping: This process associated a user name with a specific IP. Palo alto User Identification (User-ID) process.
- 3. 1-Palo alto Group Mapping 1. Create an LDAP server profile that defines how the firewall connects and authenticates to your directory server. The firewall supports a variety of directory servers • Microsoft Active Directory (AD) • Novell eDirectory • Sun ONE Directory Server • Other LDAPs 2. Specify Groups based on LDAP filters • You can limit which groups will be available in policy rules • You can specify groups that already exist in your directory service • Define custom groups based on LDAP filters
- 4. Single Active Directory Domain abc.local Multi Active Directory Domain in Forest abc.local Alex.abc.local • Domain = Logical • Domain Controller = Server it contain Active Directory & LDAP • Active Directory = Service installed on server to be Domain Controller Designing User To Group Mapping
- 5. 2-Palo alto User Mapping Methods 1. Server Monitoring ( Active Directory) • PAN‐OS Integrated User‐ID Agentless • Install User-ID Agent software on Domain or member server. 1. GlobalProtect Software (VPN Client) 2. Authentication Policy and Captive Portal (Web Portal ) 3. Client Probing (WMI and / or NetBIOS) 4. Port Mapping (Terminal Services Agent ) 5. Syslog 6. X‐Forwarded‐For (XFF) Headers 7. XML API
- 6. 2-Palo alto User Mapping Methods
- 7. Server Monitoring ( Active Directory) • PAN‐OS Integrated User‐ID Agentless • Install User-ID Agent software on Domain or member server Which Agent Should I Use? PAN‐OS Integrated User‐ID Agentless • If you have small to medium deployment with 10 or less Domain controllers or Exchange servers • If you wish to share PAN-OS sourced mappings from AD, Captive portal or Global Protect with other PA devices (max 255 devices) User-ID Agent Software (Windows) • If you have medium to large deployment with more than 10 domain controllers • If you have multi-domain setup with large number of servers to monitor Note: Can have a combination of the two in a deployment
- 8. User-ID Agent Overview • Agent major version should match PAN-OS major version (i.e. 8.0 agent for PAN-OS 8.0 devices) • Agent does NOT need to be installed on AD server or Domain controller, it just needs to be install on any machine that is a member of the domain. • Need service account user with special permeation NOT required to be Domain Admin. • For Win2008/2012, “Event Log Reader” ,“Server Operator” and “DCOM Users” group • In addition, add the service account to “Log on as a Service” Enable User-ID on trusted zones • By only enabling User-ID on internal and trusted zones, there is no exposure of these services to the Internet, which helps to keep this service protected from any potential attacks. • User-ID should never be enabled on an untrusted zone.
- 9. Domain Controller Reading Security Logs The User-ID Agent will connect to each Domain Controller and Exchange server in its configured list and will monitor the security log. • Windows 2008,2012 corresponding events are: • 4624 (Account Log On Success) • 4768 (Authentication Ticket Granted) • 4769 (Service Ticket Granted) • 4770 (Ticket Granted Renewed)
- 10. Domain Controller Reading Security Logs The User-ID Agent will connect to each Domain Controller and Exchange server in its configured list and will monitor the security log. • Windows 2008,2012 corresponding events are: • 4624 (Account Log On Success) • 4768 (Authentication Ticket Granted) • 4769 (Service Ticket Granted) • 4770 (Ticket Granted Renewed)
- 11. Agent and Firewall Communication The firewall has specific, non‐configurable timers for its communication to the agent. • 2 seconds: Get list of new IP / user mapping from agent. This is a delta of new mapping only. • 2 seconds: Send list of Unknown IP addresses that were encountered in traffic to the agent. • 5 seconds: Get agent status. This is a heartbeat uses to determine the status of each configured agent. • 10 minutes: Get group membership changes from agent. This is just the delta of changes since the last check. • 1 hour: Get full list of IP / user mappings from agent.
