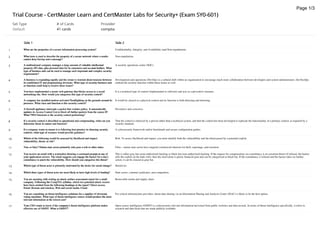
Trial Course - CertMaster Learn and CertMaster Labs for Security+ (Exam SY0-601).pdf
- 1. Set Type # of Cards Provider Default 41 cards comptia Side 1 Side 2 1 What are the properties of a secure information processing system? Confidentiality, Integrity, and Availability (and Non-repudiation). 2 What term is used to describe the property of a secure network where a sender cannot deny having sent a message? Non-repudiation. 3 A multinational company manages a large amount of valuable intellectual property (IP) data, plus personal data for its customers and account holders. What type of business unit can be used to manage such important and complex security requirements? A security operations center (SOC). 4 A business is expanding rapidly and the owner is worried about tensions between its established IT and programming divisions. What type of security business unit or function could help to resolve these issues? Development and operations (DevOps) is a cultural shift within an organization to encourage much more collaboration between developers and system administrators. DevSecOps embeds the security function within these teams as well. 5 You have implemented a secure web gateway that blocks access to a social networking site. How would you categorize this type of security control? It is a technical type of control (implemented in software) and acts as a preventive measure. 6 A company has installed motion-activated floodlighting on the grounds around its premises. What class and function is this security control? It would be classed as a physical control and its function is both detecting and deterring. 7 A firewall appliance intercepts a packet that violates policy. It automatically updates its Access Control List to block all further packets from the source IP. What TWO functions is the security control performing? Preventive and corrective. 8 If a security control is described as operational and compensating, what can you determine about its nature and function? That the control is enforced by a person rather than a technical system, and that the control has been developed to replicate the functionality of a primary control, as required by a security standard. 9 If a company wants to ensure it is following best practice in choosing security controls, what type of resource would provide guidance? A cybersecurity framework and/or benchmark and secure configuration guides. 10 Which of the following would be assessed by likelihood and impact: vulnerability, threat, or risk? Risk. To assess likelihood and impact, you must identify both the vulnerability and the threat posed by a potential exploit. 11 True or false? Nation state actors primarily only pose a risk to other states. False—nation state actors have targeted commercial interests for theft, espionage, and extortion. 12 You receive an email with a screenshot showing a command prompt at one of your application servers. The email suggests you engage the hacker for a day's consultancy to patch the vulnerability. How should you categorize this threat? This is either gray hat (semi-authorized) hacking or black hat (non-authorized) hacking. If the request for compensation via consultancy is an extortion threat (if refused, the hacker sells the exploit on the dark web), then the motivation is purely financial gain and can be categorized as black hat. If the consultancy is refused and the hacker takes no further action, it can be classed as gray hat. 13 Which type of threat actor is primarily motivated by the desire for social change? Hacktivist. 14 Which three types of threat actor are most likely to have high levels of funding? State actors, criminal syndicates, and competitors. 15 You are assisting with writing an attack surface assessment report for a small company. Following the CompTIA syllabus, which two potential attack vectors have been omitted from the following headings in the report? Direct access, Email, Remote and wireless, Web and social media, Cloud. Removable media and supply chain. 16 You are consulting on threat intelligence solutions for a supplier of electronic voting machines. What type of threat intelligence source would produce the most relevant information at the lowest cost? For critical infrastructure providers, threat data sharing via an Information Sharing and Analysis Center (ISAC) is likely to be the best option. 17 Your CEO wants to know if the company's threat intelligence platform makes effective use of OSINT. What is OSINT? Open-source intelligence (OSINT) is cybersecurity-relevant information harvested from public websites and data records. In terms of threat intelligence specifically, it refers to research and data feeds that are made publicly available. Trial Course - CertMaster Learn and CertMaster Labs for Security+ (Exam SY0-601) Page 1/3
- 2. 18 You are assessing whether to join AIS. What is AIS and what protocol should your SIEM support in order to connect to AIS servers? Automated Indicator Sharing (AIS) is a service offered by the Department of Homeland Security (DHS) for participating in threat intelligence sharing. AIS uses the Trusted Automated eXchange of Indicator Information (TAXII) protocol as a means of transmitting CTI data between servers and clients. 19 You suspect that a rogue host is acting as the default gateway for a subnet in a spoofing attack. What command line tool(s) can you use from a Windows client PC in the same subnet to check the interface properties of the default gateway? Use ipconfig to check the IP addresses of the default gateway and the DHCP server. Use arp to check the MAC addresses associated with those IP addresses and investigate possible spoofing. You could also use the route command to verify the properties of the default route. 20 You suspect the rogue host is modifying traffic before forwarding it, with the side effect of increasing network latency. Which tool could you use to measure latency on traffic routed from this subnet? From a Windows host, the pathping tool can be used to measure latency along a route. 21 What type of tool could you use to fingerprint the host acting as the default gateway? This requires a tool that performs fingerprinting—service and version detection—by examining responses to network probes and comparing them to known responses from common platforms. Nmap is very widely used for this task, or you could use hping or Netcat. 22 You are investigating a Linux server that is the source of suspicious network traffic. At a terminal on the server, which tool could you use to check which process is using a given TCP port? You can use the netstat command to do this. 23 What is a zone transfer and which reconnaissance tools can be used to test whether a server will allow one? A zone transfer is where a domain name server (DNS) allows a client to request all the name records for a domain. nslookup (Windows) and dig (principally Linux) can be used to test whether this query is allowed. You could also mention the dnsenum tool, which will check for zone transfers along with other enumeration tests on DNS infrastructure. 24 What type of organizational security assessment is performed using Nessus? Nessus is an automated network vulnerability scanner that checks for software vulnerabilities and missing patches. 25 You are developing new detection rules for a network security scanner. Which tool will be of use in testing whether the rules match a malicious traffic sample successfully? The tcpreplay tool can be used to stream captured traffic from a file to a monitored network interface. 26 What security posture assessment could a pen tester make using Netcat? Whether it is possible to open a network connection to a remote host over a given port. 27 You are recommending that a business owner invest in patch management controls for PCs and laptops. What is the main risk from weak patch management procedures on such devices? Vulnerabilities in the OS and applications software such as web browsers and document readers or in PC and adapter firmware can allow threat actors to run malware and gain a foothold on the network. 28 You are advising a business owner on security for a PC running Windows XP. The PC runs process management software that the owner cannot run on Windows 10. What are the risks arising from this, and how can they be mitigated? Windows XP is a legacy platform that is no longer receiving security updates. This means that patch management cannot be used to reduce risks from software vulnerabilities. The workstation should be isolated from other systems to reduce the risk of compromise. 29 As a security solutions provider, you are compiling a checklist for your customers to assess potential weak configuration vulnerabilities, based on the CompTIA Security+ syllabus. From the headings you have added so far, which is missing and what vulnerability does it relate to? Default settings, Unsecured root accounts, Open ports and services, Unsecure protocols, Weak encryption, Errors. Open permissions refers to misconfigured access rights for data folders, network file shares, and cloud storage. 30 You are advising a customer on backup and disaster recovery solutions. The customer is confused between data breaches and data loss and whether the backup solution will protect against both. What explanation can you give? Backup solutions mitigate risks from data loss, where files or information is deleted, corrupted, or otherwise destroyed. Backup does not mitigate risks from data breach, where confidential or private data is stolen (exfiltrated) and made public or sold for criminal profit. Mitigating risks of data breach requires effective secure processing, authorization, and authentication security controls. 31 A system integrator is offering a turnkey solution for customer contact data storage and engagement analytics using several cloud services. Does this solution present any supply chain risks beyond those of the system integrator's consulting company? Yes, the system integrator is proposing the use of multiple vendors (the cloud service providers), with potentially complex issues for collecting, storing, and sharing customer personal data across these vendors. Each company in the supply chain should be assessed for risk and compliance with cybersecurity and privacy standards. 32 You have received an urgent threat advisory and need to configure a network vulnerability scan to check for the presence of a related CVE on your network. What configuration check should you make in the vulnerability scanning software before running the scan? Verify that the vulnerability feed/plug-in/test has been updated with the specific CVE that you need to test for. 33 You have configured a network vulnerability scanner for an engineering company. When running a scan, multiple sensors within an embedded systems network became unresponsive, causing a production shutdown. What alternative method of vulnerability scanning should be used for the embedded systems network? A fully non-intrusive solution should be adopted, such as sniffing traffic using a network tap or mirror port. Using the network traffic to detect vulnerabilities rather than actively probing each device will not cause system stability issues (though there is greater risk of false positive and false negative results). 34 A vulnerability scan reports that a CVE associated with CentOS Linux is present on a host, but you have established that the host is not running CentOS. What type of scanning error event is this? False positive. Page 2/3
- 3. 35 A small company that you provide security consulting support to has resisted investing in an event management and threat intelligence platform. The CEO has become concerned about an APT risk known to target supply chains within the company's industry sector and wants you to scan their systems for any sign that they have been targeted already. What are the additional challenges of meeting this request, given the lack of investment? Collecting network traffic and log data from multiple sources and then analyzing it manually will require many hours of analyst time. The use of threat feeds and intelligence fusion to automate parts of this analysis effort would enable a much swifter response. 36 What term relates to assessment techniques that avoid alerting threat actors? This can be referred to as maneuver. 37 A website owner wants to evaluate whether the site security mitigates risks from criminal syndicates, assuming no risk of insider threat. What type of penetration testing engagement will most closely simulate this adversary capability and resources? A threat actor has no privileged information about the website configuration or security controls. This is simulated in a black box (or blind) pen test engagement. 38 You are agreeing a proposal to run a series of team-based exercises to test security controls under different scenarios. You propose using purple team testing, but the contracting company is only familiar with the concept of red and blue teams. What is the advantage of running a purple team exercise? In a red versus blue team, there is no contact between the teams, and no opportunity to collaborate on improving security controls. In a purple team exercise, there is regular contact and knowledge sharing between the teams throughout the progression of the exercise. 39 Why should an Internet service provider (ISP) be informed before pen testing on a hosted website takes place? ISPs monitor their networks for suspicious traffic and may block the test attempts. The pen test may also involve equipment owned and operated by the ISP. 40 What tools are used for OSINT? Open-source intelligence is a reconnaissance activity to gather information about the target from any public source. The basic tool is web searches/queries plus sites that scan/scrape/monitor vulnerabilities in Internet-facing services and devices. There are also specialist OSINT tools, such as theHarvester, that aggregate data from queries for different resources. 41 In the context of penetration testing, what is persistence? Persistence refers to the tester's ability to reconnect to the compromised host and use it as a remote access tool (RAT) or backdoor. Page 3/3