CS8601-QB.pdf
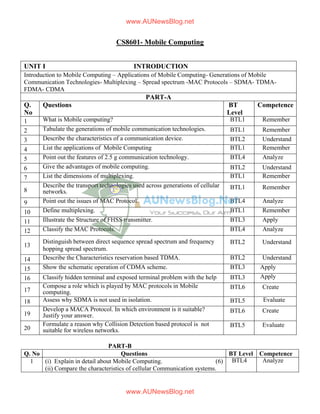
- 1. CS8601- Mobile Computing UNIT I INTRODUCTION Introduction to Mobile Computing – Applications of Mobile Computing- Generations of Mobile Communication Technologies- Multiplexing – Spread spectrum -MAC Protocols – SDMA- TDMA- FDMA- CDMA PART-A Q. No Questions BT Level Competence 1 What is Mobile computing? BTL1 Remember 2 Tabulate the generations of mobile communication technologies. BTL1 Remember 3 Describe the characteristics of a communication device. BTL2 Understand 4 List the applications of Mobile Computing BTL1 Remember 5 Point out the features of 2.5 g communication technology. BTL4 Analyze 6 Give the advantages of mobile computing. BTL2 Understand 7 List the dimensions of multiplexing. BTL1 Remember 8 Describe the transport technologies used across generations of cellular networks. BTL1 Remember 9 Point out the issues of MAC Protocol. BTL4 Analyze 10 Define multiplexing. BTL1 Remember 11 Illustrate the Structure of FHSS transmitter. BTL3 Apply 12 Classify the MAC Protocols. BTL4 Analyze 13 Distinguish between direct sequence spread spectrum and frequency hopping spread spectrum. BTL2 Understand 14 Describe the Characteristics reservation based TDMA. BTL2 Understand 15 Show the schematic operation of CDMA scheme. BTL3 Apply 16 Classify hidden terminal and exposed terminal problem with the help ofa diagram. BTL3 Apply 17 Compose a role which is played by MAC protocols in Mobile computing. BTL6 Create 18 Assess why SDMA is not used in isolation. BTL5 Evaluate 19 Develop a MACA Protocol. In which environment is it suitable? Justify your answer. BTL6 Create 20 Formulate a reason why Collision Detection based protocol is not suitable for wireless networks. BTL5 Evaluate PART-B Q. No Questions BT Level Competence 1 (i) Explain in detail about Mobile Computing. (6) (ii) Compare the characteristics of cellular Communication systems. BTL4 Analyze www.AUNewsBlog.net www.AUNewsBlog.net
- 2. (7) 2 Summarize the applications of Mobile computing. (13) BTL2 Understand 3 (i) Explain the features of different generations of cellular technologies. (7) (ii) Analyze the properties required for MAC Protocols. (6) BTL4 Analyze 4 Demonstrate the working principle of (i) FDMA scheme. (7) (ii) SDMA scheme. (6) BTL3 Apply 5 Explain in detail about the multiplexing schemes for communication systems. (13) BTL1 Remember 6 (i) Examine the operation of spreading and dispreading of spread spectrum. (5) (ii) Describe the Direct spread spectrum in detail. (8) BTL1 Remember 7 Compare and contrast SDMA,TDMA,FDMA and CDMA schemes. (13) BTL4 Analyze 8 Illustrate the transmitter and receiver and explain the working principle of FHSS. (13) BTL3 Apply 9 Generalize the role of various codes used in CDMA and explain the working of CDMA scheme. (13) BTL6 Create 10 Describe the operations of the following technologies (i) Fixed TDM. (4) (ii) Classical ALOHA. (4) (iii)Slotted ALOHA. (5) BTL1 Remember 11 Explain the different categories of MAC protocols in detail. (13) BTL2 Understand 12 Discuss: (i) Hidden terminal and Exposed terminal problem. (7) (ii) Far and Near Terminal problem. (6) BLT-2 Understand 13 (i)Describe the role of MAC protocol. In which layer of OSI model the MAC protocols operated? (7) (ii) Identify the role of CSMA /CA in wireless network. (6) BTL1 Remember 14 Summarize the Carrier Sense Multiple Access Protocols. (13) BTL5 Evaluate PART-C Q. No Questions BT Level Competence 1 Generalize the roles and application environments of mobile computing. (15) BTL -6 Create 2 What do you understand by 2.5G? Mention few characteristics of this technology. Analyze how it differs from 2G and 3G. (15) BTL-4 Analyze 3 Do you agree with the following statement: “In CSMA/CD protocol, when two nodes transmit on a shared medium, a collision can occur only when two nodes start transmitting exactly at the same instant?” Explain your answer. (15) BTL 5 Evaluate 4 What is MACA protocol? In which environment is it suitable? Briefly expain its working. Compose a solution to solve the hidden and BTL6 Create www.AUNewsBlog.net www.AUNewsBlog.net
- 3. exposed terminal problem using MACA protocol. (15) UNIT II MOBILE TELECOMMUNICATION SYSTEM Introduction to Cellular Systems – GSM – Services & Architecture – Protocols – Connection Establishment – Frequency Allocation – Routing – Mobility Management – Security – GPRS- UMTS – Architecture – Handover – Security PART-A Q. No Questions BT Level Competence 1. Define GSM. BTL1 Remember 2. Tabulate the services of GSM? BTL1 Remember 3. Show the connection establishment in GSM. BTL3 Apply 4. List the functions of mobility management. BTL 1 Remember 5. Classify the major functions in RSS. BTL 4 Analyze 6. Pointout the import features of GSM security. BTL 4 Analyze 7. Discuss about BTS. BTL 2 Understand 8. Classify the functions of HLR and VLR. BTL3 Apply 9. List the possible handover scenarios in GSM. BTL 1 Remember 10. Give the protocol architecture for signaling in GSM. BTL 2 Understand 11. What is SGSN? List the functions. BTL 1 Remember 12. Discuss about the services provided by GPRS. BTL 2 Understand 13. Analyze the purpose of UTRAN in UMTS. BTL 4 Analyze 14. Explain in what ways is GPRS better than GSM? BTL 5 Evaluate 15. Define UMTS. What are the elements of UMTS? BTL1 Remember 16. Generalize the tasks of radio network controller. BTL 6 Create 17. Assess the functions of core network in UMTS. BTL 5 Evaluate 18. Show the different classes of UMTS handover scenarios. BTL 3 Apply 19. Differentiate between a GSM network and UMTS network. BTL2 Understand 20. Develop UMTS network with its interfaces. BTL 6 Create PART-B Q. No Questions BT Level Competence 1. Describe the GSM architecture in detail. (13) BTL 1 Remember 2. Classify various categories of GSM services in detail. (13) BTL 4 Analyze 3. (i)What are the functions of authentication and encryption in GSM? (7) (ii)How a GSM network provides security to the customers? (6) BTL 3 Apply 4. (i) Demonstrate protocolarchitectureofGSMindetail. (10) BTL 3 Apply www.AUNewsBlog.net www.AUNewsBlog.net
- 4. (ii) Examine how the MS is located and addressed in GSM. (3) 5. (i)Generalize the role of Handover in GSM. (3) (ii) Develop the solutions for effective handover. (10) BTL 6 Create 6. Describe in detail about (i) Connection Establishment in GSM. (7) (ii) Signaling in GSM. (6) BTL 1 Remember 7. (i)Explain GPRS transmission plane protocol reference model. (7) (ii) Explain GPRS services. (6) BTL 5 Evaluate 8. (i) Discuss UMTS system architecture in detail. (7) (ii) Describe the functions of HLR and VLR in call routing and roaming. (6) BTL 2 Understand 9. Describe the GPRS architecture in detail. (13) BTL 1 Remember 10. Discuss about the UTRAN interface of UMTS in detail . (13) BTL 2 Understand 11. (i)Explain the core network of UMTS architecture. (8) (ii)Explain the radio network controller in detail. (5) BTL 1 Remember 12. Summarize the handover procedures in UMTS networks. (13) BTL 2 Understand 13. (i) Why UMTS technology is superior to GPRS technology? Justify your answer. (8) (ii)Analyze the advantages and limitations of GPRS. (5) BTL 4 Analyze 14. Explain the similarities and dissimilarities between a GSM network and UMTS networks. (13) BTL 4 Analyze PART-C Q. No Questions BT Level Competence 1. Which types of different services does GSM offer? Give some examples and reasons why these services can be separated? (15) BTL5 Evaluate 2. Give reasons for handover in GSM and the problems associated with it. What are the typical steps for handover? What types of handover can occur? Which resources are to be allocated during data transmission? (15) BTL6 Create 3. Analyze the interfaces and signaling used in GSM Network and UMTS network. (15) BTL4 Analyze 4. How does UMTS implement asymmetrical communication and different data rates? Explain OVSF code in UMTS. (15) BTL5 Evaluate UNIT III MOBILE NETWORK LAYER Mobile IP – DHCP – AdHoc– Proactive protocol-DSDV, Reactive Routing Protocols – DSR, AODV , Hybrid routing –ZRP, Multicast Routing- ODMRP, Vehicular Ad Hoc networks ( VANET) –MANET Vs VANET – Security. www.AUNewsBlog.net www.AUNewsBlog.net
- 5. PART-A Q. No Questions BT Level Competence 1 Define Mobile IP? Name its Functional entities. BTL-1 Remember 2 What is meant by DHCP? Why does an IP conflict occurs? BTL-1 Remember 3 Express the role of Subnet Mask , Router address ,DNS address in DHCP. BTL 2 Understand 4 Assess the term ‘Ad-Hoc Network’ in a wireless Communication. BTL5 Evaluate 5 Give the role of agent solicitation message. When it is used? BTL 2 Understand 6 Define COA. BTL1 Remember 7 Differentiate between Proactive and Reactive Routing Protocols. BTL 2 Understand 8 Identify the roles of DSR protocol. BTL 1 Remember 9 Classify different types of MANET Routing Protocols. BTL3 Apply 10 Discuss the three steps used in DSDV for the reconfiguration of path used for ongoing data transfer. BTL 2 Understand 11 Give the advantages of routing in wireless networks. BTL 2 Understand 12 Analyze the strategies used in Inter zone routing and Intra zone routing. BTL 4 Analyze 13 List the disadvantages of DSDV. BTL 1 Remember 14 Classify Multicast Routing Protocols. BTL 4 Analyze 15 How to Create a Network Multicasting? BTL 6 Create 16 Discriminate between Unicasting and Multicasting. BTL 5 Evaluate 17 Show the basic operation of ODMRP using diagram. BTL 3 Apply 18 Pointout the differences between MANET and VANET. BTL 4 Analyze 19 Generalize the threats in VANET. BTL 6 Create 20 Define VANET. BTL 1 Remember PART-B Q. No Questions BT Level Competence 1 (i) Explain the use of a Mobile Node and corresponding node. (7) BTL 5 Evaluate www.AUNewsBlog.net www.AUNewsBlog.net
- 6. (ii) Explain the services that are provided by the Home Agent. (6) 2 Describe Route optimization in detail. (13) BTL 1 Remember 3 (i) Discover the requirements of Mobile IP. (7) (ii) Show how Tunelling and encapsulation play a crucial role in packet delivery through routing. (6) BTL 3 Apply 4 Demonstrate the operation of DHCP with a neat diagram and explain its protocol architecture. (13) BTL 3 Apply 5 (i) Generalize the working mechanism of Agent discovery. (7) (ii) Explain the registration of the packets during its delivery from source to destination. (6) BTL6 Create 6 (i) Discuss the problems the dynamic topology causes in the design of routing protocol. (7) (ii) In what way the Dynamic Source Routing provides a possible path for packet transmission to the destination. (6) BTL 1 Remember 7 Classify the encapsulation types used in Mobile IP. (13) BTL 4 Analyze 8 (i) Describe with a diagram and an example the use of Ad-Hoc networks. (7) (ii) Describe why the traditional packet routing protocol for wired network cannot be used straightaway in a MANET. (6) BTL 2 Understand 9 Describe at least three applications of Mobile Ad-Hoc Networks.(13) BTL 1 Remember 10 Discuss about the similarities and differences between MANET and VANET. (13) BTL 2 Understand 11 (i) Explain in detail about the architecture of VANET. (7) (ii) Explain the design issues in MANET protocols. (6) BTL 1 Remember 12 Summarize the characteristics and the creation of a basic Ad-hoc networks. (13) BTL 2 Understand 13 (i) Explain the multicast protocols for MANET in detail. (7) (ii) Analyze features of multicast routing protocols for MANET. (6) BTL 4 Analyze 14 Explain in detail about the security issues in VANET. (13) BTL 4 Analyze PART-C Q. No Questions BT Level Competence 1 Give the factors that make mobile ad hoc networks more vulnerable to security attacks compared to the traditional networks. Also explain major types of security attacks that are possible in a mobile ad hoc network. Compose a solution to overcome from these types of attacks. (15) BTL 6 Create 2 i) Explain the discovery of care of address in the context of movement of a mobile to a foreign network. (8) ii) What do you mean by encapsulation and decapsulation in the context of mobile IP? Explain why they are needed? BTL5 Evaluate www.AUNewsBlog.net www.AUNewsBlog.net
- 7. (7) 3 What is meant by size and node density of a MANET? Explain these two terms and discuss how these two parameters impact the design of a MANET. (13) BTL 4 Analyze 4 Analyze the working of DSR and DSDV in detail. (13) BTL 4 Analyze UNIT IV MOBILE TRANSPORT AND APPLICATION LAYER Mobile TCP– WAP – Architecture – WDP – WTLS – WTP –WSP – WAE – WTA Architecture – WML PART-A Q. No Questions BT Level Competence 1 Define the TCP issues in Mobile IP networks. BTL1 Remember 2 Illustrate Mobile TCP with a diagram. BTL3 Apply 3 Summarize the advantages and disadvantages of Mobile IP. BTL5 Evaluate 4 Examine the use of snoop protocol in TCP. BTL3 Apply 5 What is meant by I-TCP? BTL1 Remember 6 Classify different types of TCP Approaches used in Mobile Networks. BTL4 Analyze 7 How will you develop a WAP for Mobile Networks? BTL6 Create 8 Give the different layers of WAP. BTL5 Evaluate 9 Analyze WAP using a Client – Server diagram. BTL4 Analyze 10 Express the different applications of WAP. BTL2 Understand 11 Distinguish between WDP and WTLS. BTL2 Understand 12 List the functions of WTLS. BTL1 Remember 13 Differentiate between WTP and WTA. BTL4 Analyze 14 List the classes of WTP Transactions. BTL1 Remember 15 Design the connection mode and connectionless mode of WSP Protocols. BTL6 Create 16 Interpret how synchronization markup language is used to connect a node in internet. BTL2 Understand 17 Tabulate the different layers used in WAP. BTL1 Remember 18 Identify the logical model of WAE Mobile Computing. BTL1 Remember 19 Interpret the operation of WTA in Mobile Computing with diagram. BTL2 Understand www.AUNewsBlog.net www.AUNewsBlog.net
- 8. 20 Show the use of WML in Mobile Computing. BTL3 Apply PART-B Q. No Questions BT Level Competence 1 (i) Discuss in detail about Mobile TCP. (7) (ii) Summarize the TCP approaches used in Mobile Networks.(6) BTL2 Understand 2 (i) Illustrate the use of WAP in Mobile networks. (7) (ii) Show the architecture of WAP and its working. (6) BTL3 Apply 3 Demonstrate the WAP Communication Protocols and its components. (13) BTL3 Apply 4 (i) What is the role of WDP in Mobile Networks. (7) (ii) How WDP enables transparent communication in the delivery of packets. (6) BTL6 Create 5 (i) Evaluate the role of WTLS in providing privacy, data integrity and authentication. (7) (ii) Evaluate with the help of a diagram of how WTLS helps in establishing a secure session. (6) BTL5 Evaluate 6 Describe in detail WTLS class 0, class 1, class 2 initiator and responder used in WTLS. (13) BTL 2 Understand 7 (i) Draw the architecture of WSP Session establishment, Suspension, resume, termination. (7) (ii) Explain in detail WSP as connectionless session service. (6) BTL 1 Remember 8 Explain in detail with a diagram the use of Wireless Application environment. (13) BTL 1 Remember 9 (i) Point out the use of WAE application models. (7) (ii) Explain in detail WTA Logical Architecture. (6) BTL 4 Analyze 10 Define short notes on : (i) WTA voice message. (9) (ii) Classes of libraries in WTA. (4) BTL 1 Remember 11 Describe in detail about the use of WML. (13) BTL 1 Remember 12 (i) Express the basic features of WML. (7) (ii) Summarize the role of WML in mobile computing. (6) BTL 2 Understand 13 Classify and explain in detail about the different layers of Wireless Application Protocol. (13) BTL 4 Analyze www.AUNewsBlog.net www.AUNewsBlog.net
- 9. 14 Analyze the role of i-mode in mobile computing with a diagram. (13) BTL 4 Analyze PART-C Q. No Questions BT Level Competence 1 Generalize the M-TCP approach of extending TCP to work efficiently in mobile network. How does M-TCP maintain end to end semantics? (15) BTL6 Create 2 What role does initiator and responder play in the transport layer of WTLS? Explain in detail. (15) BTL5 Evaluate 3 Classify wireless application protocol in different layers. (15) BTL4 Analyze 4 What role does WTA play in Mobile computing? How it is useful in terms of long distance communication. (15) BTL5 Evaluate UNIT V MOBILE PLATFORMS AND APPLICATIONS Mobile Device Operating Systems – Special Constrains & Requirements – Commercial Mobile Operating Systems – Software Development Kit: iOS, Android, BlackBerry, Windows Phone – MCommerce – Structure – Pros & Cons – Mobile PaymentSystem – Security Issues. PART-A Q. No Questions BTLevel Competence 1. What is microkernel operating system? BTL1 Remember 2. Give four examples of Mobile OS. BTL2 Understand 3. Differentiate the operating system for mobile phone and the operating system for desktop. BTL2 Understand 4. Show the advantages of mobile operating system. BTL3 Apply 5. Define POS. BTL1 Remember 6. Assess the special constraints and requirements of Mobile OS. BTL5 Evaluate 7. What is M-commerce? BTL1 Remember 8. Assess the pros and cons of E-Commerce BTL5 Evaluate 9. Express micropayment in M-Commerce. BTL2 Understand 10. What are the different payment systems available in M-Commerce? BTL1 Remember 11. Examine why microkernel is preferred for developing a mobile OS. BTL3 Apply 12. List the different versions of Android. BTL1 Remember 13. Pointout the drawbacks of Symbian os. BTL4 Analyze 14. Analyze the features of windows iPhone. BTL4 Analyze 15. Describe UIQ interface. BTL3 Apply 16. Develop android software stack with neat diagram. BTL6 Create 17. Describe the features of Blackberry operating system. BTL2 Understand 18. Differentiate E-commerce and M- commerce BTL4 Analyze www.AUNewsBlog.net www.AUNewsBlog.net
- 10. 19. Compose the solutions for security issues in mobile OS. BTL6 Create 20. Differentiate mobile OS with Traditional OS. BTL 1 Remember PART-B Q. No Questions BT Level Competence 1. Explain the special constraints and requirements of mobile OS.(13) BTL5 Evaluate 2. i) Discuss about the evolution and the features of Windows mobile OS (6) ii) Give the structure of Android software stack and explain. (7) BTL2 Understand 3. Compare and contrast the various mobile OS. (13) BTL4 Analyze 4. Summarize the various applications of M-Commerce. (13) BTL2 Understand 5 (i) List and explain the components of mobile operating system.(7) (ii) Write short notes on Android SDK. (6) BTL1 Remember 6. (i)Illustrate mobile device OS with a suitable example. (8) (ii)Explain the flexibilities that a user would be required to take with a single tasking operating system is used in the mobile device. (5) BTL3 Apply 7. i)Illustrate the architecture of Andriod operating system. (7) ii)Examine the evolution of Windows OS for mobile. (6) BTL3 Apply 8. Write detailed notes on E-Commerce. (13) BTL1 Remember 9. a) What do you understand by M-commerce? Explain the advantages and disadvantages of M-commerce. (5) b) Identify the situation where micropayments are essential and how it can be achieved. (8) BTL1 Remember 10. Generalize the functions of (i)B2B Commerce. (8) (ii) B2C commerce. (5) BTL6 Create 11. (i)Identify the properties of mobile payment system. (8) (ii) Describe about mobile payment solutions. (5) BTL1 Remember 12. Explain the different mobile payment schemes in detail. (13) BTL2 Understand 13. (i)What do you understand by the security issues in mobile payment system? (5) (ii)Analyze the mobile payment security solutions in detail. (8) BTL 4 Analyze 14. Explain the ways by which m-payments are settled along with any two applications. (13) BTL 4 Analyze PART-C Q. No Questions BT Level Competence www.AUNewsBlog.net www.AUNewsBlog.net
- 11. 1. Assess the special features that an operating system for mobile device needs to support compared to the features provided by a traditional operating system. (15) BTL5 Evaluate 2. i)Explain the principle functions of the operating system of a mobile device. ( 8 ) ii)Analyze how an example application can be implemented on mobile device and the specific operating system service that it make use of. (7) BTL 4 Analyze 3. What do you understand by the mobile payment system? Briefly explain an application where mobile payment may be useful. Explain the different payment systems that are available. (15) BTL 5 Evaluate 4. Integrate an application where E- commerce is used. Explain the different types of e- commerce involved in the application with the participants. (15) BTL 6 Create www.AUNewsBlog.net www.AUNewsBlog.net