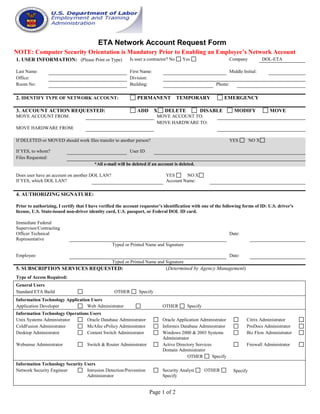
ETA Network Account Request Form Summary
- 1. Page 1 of 2 ETA Network Account Request Form NOTE: Computer Security Orientation is Mandatory Prior to Enabling an Employee’s Network Account 1. USER INFORMATION: (Please Print or Type) Is user a contractor? No Yes Company DOL-ETA Last Name: First Name: Middle Initial: Office: Division: Room No: Building: Phone: 2. IDENTIFY TYPE OF NETWORK ACCOUNT: PERMANENT TEMPORARY EMERGENCY 3. ACCOUNT ACTION REQUESTED: ADD X DELETE DISABLE MODIFY MOVE MOVE ACCOUNT FROM: MOVE ACCOUNT TO: MOVE HARDWARE FROM: MOVE HARDWARE TO: If DELETED or MOVED should work files transfer to another person? YES NO X If YES, to whom? User ID Files Requested: *All e-mail will be deleted if an account is deleted. Does user have an account on another DOL LAN? YES NO X If YES, which DOL LAN? Account Name: 4. AUTHORIZING SIGNATURE: Prior to authorizing, I certify that I have verified the account requestor’s identification with one of the following forms of ID: U.S. driver's license, U.S. State-issued non-driver identity card, U.S. passport, or Federal DOL ID card. Immediate Federal Supervisor/Contracting Officer Technical Representative Date: Typed or Printed Name and Signature Employee: Date: Typed or Printed Name and Signature 5. SUBSCRIPTION SERVICES REQUESTED: (Determined by Agency Management) Type of Access Required: General Users Standard ETA Build OTHER Specify Information Technology Application Users Application Developer Web Administrator OTHER Specify Information Technology Operations Users Unix Systems Administrator Oracle Database Administrator Oracle Application Administrator Citrix Administrator ColdFusion Administrator McAfee ePolicy Administrator Informix Database Administrator ProDocs Administrator Desktop Administrator Content Switch Administrator Windows 2000 & 2003 Systems Administrator Biz Flow Administrator Websense Administrator Switch & Router Administrator Active Directory Services Domain Administrator Firewall Administrator OTHER Specify Information Technology Security Users Network Security Engineer Intrusion Detection/Prevention Administrator Security Analyst OTHER Specify Specify
- 2. Page 2 of 2 Applications Required: E-Mail Mail Distribution Group Memberships Required (specify) Specify application CITRIX (Remote Access) Complete the section below ONLY if there is a need for the individual to work remotely and he/she meets the following criteria: (Check all that applies) Are you using government furnished equipment Yes No Note: For those who check No to this question, personally owned equipment is being used. PERMANENT TEMPORARY Perform essential roles in an “actual” Continuity of Operations Plan (COOP) or pandemic emergency Participate in COOP or pandemic practice exercises Require 24-hour access to network services or for address administrative priorities (e.g., Office of Foreign Labor Certification Certifying Official) Need to work remotely on a temporary basis in response to disaster relief efforts or other high priority activities Work under a formal Flexiplace Agreement Federal Project Officer engaged in scheduled monitoring activities Please complete the questions below. This information will be used tor reset your account in the event you lose your token or have forgotten your PIN. Security Questions 1 What is your favorite color? Security Questions 2 What is your favorite hobby? 6. COMPLETION INFORMATION: A. Has the User completed the Computer Security Orientation? B. Has the User been instructed where to obtain the following information technology security documents: • ETA Computer Security Handbook (CSH), Chapter 101, Information Technology Policy Manual; • ETA CSH, Chapter 204, Information Technology User Procedures; • ETA CSH, Chapter 30l, Volume 1, IT Personnel Security Procedures; and • Operational Procedures Handbook, Access Authorization Procedures? YES NO YES NO Date: Date: C. Has the user read and accepted the following security documents: • Rules of Behavior for Mobile Users and Teleworkers? • Rules of Behavior for System Administrators of Mobile Users and Teleworkers (if a System Administrator of Citrix)? YES NO YES NO Date: Date: User ID: Hardware Assigned: RSA Token Token Type Assigned: Permanent Temporary COMMENTS: Token Processed By: Printed name and signature Date Completed: Account Processed By: Printed name and signature Date Completed: Revised 05/21/2009