Unit 1
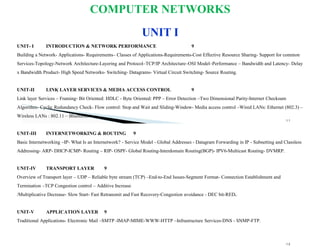
- 1. COMPUTER NETWORKS UNIT I 1.1 1.2 UNIT- I INTRODUCTION & NETWORK PERFORMANCE 9 Building a Network- Applications- Requirements– Classes of Applications-Requirements-Cost Effective Resource Sharing- Support for common Services-Topology-Network Architecture-Layering and Protocol–TCP/IP Architecture–OSI Model–Performance – Bandwidth and Latency- Delay x Bandwidth Product- High Speed Networks- Switching- Datagrams- Virtual Circuit Switching- Source Routing. UNIT-II LINK LAYER SERVICES & MEDIA ACCESS CONTROL 9 Link layer Services – Framing- Bit Oriented: HDLC - Byte Oriented: PPP – Error Detection –Two Dimensional Parity-Internet Checksum Algorithm- Cyclic Redundancy Check- Flow control: Stop and Wait and Sliding-Window- Media access control –Wired LANs: Ethernet (802.3) – Wireless LANs : 802.11 – Bluetooth. UNIT-III INTERNETWORKING & ROUTING 9 Basic Internetworking –IP- What Is an Internetwork? - Service Model - Global Addresses - Datagram Forwarding in IP - Subnetting and Classless Addressing- ARP- DHCP-ICMP- Routing – RIP- OSPF- Global Routing-Interdomain Routing(BGP)- IPV6-Multicast Routing- DVMRP. UNIT-IV TRANSPORT LAYER 9 Overview of Transport layer – UDP – Reliable byte stream (TCP) –End-to-End Issues-Segment Format- Connection Establishment and Termination –TCP Congestion control – Additive Increase /Multiplicative Decrease- Slow Start- Fast Retransmit and Fast Recovery-Congestion avoidance - DEC bit-RED. UNIT-V APPLICATION LAYER 9 Traditional Applications- Electronic Mail –SMTP -IMAP-MIME-WWW-HTTP –Infrastructure Services-DNS - SNMP-FTP.
- 2. TEXT BOOKS Larry L. Peterson, Bruce S. Davie, “Computer Networks: A Systems Approach”, Fifth Edition,Morgan Kaufmann Publishers, 2011. Behrouz A. Forouzan, “Data communication and Networking”, Fourth Edition, Tata McGraw – Hill, 2011. REFERENCES William Stallings, Data and Computer Communications,TenthEdition,PearsonEducation,2013. Nader. F. Mir, “Computer and Communication Networks”, Pearson Prentice Hall Publishers, 2010. DATA COMMUNICATIONS: 1. Telecommunication means communication at a distance 2. Data refers to information presented in whatever form is agreed upon by the parties creating and using the data. 3. Data communications are the exchange of data between two devices via some form of transmission medium such as a wire cable.
- 3. Figure 1.1 Components of a data communication system 1.5 Components of data communication: Message: The information (data) to be communicated. Popular : text, numbers, pictures, audio, and video. □Sender: The sender is the device that sends the data message. ◦ It can be a computer, workstation, telephone handset, video camera, etc. □Receiver: The receiver is the device that receives the message. ◦ It can be a computer, workstation, telephone handset, television, etc. □Transmission medium: The physical path by which a message travels from sender to receiver. ◦ Some examples : twisted-pair wire, coaxial cable, fiber-optic cable, and radio waves. □Protocol: A protocol is a set of rules that govern data communications. ◦ It represents an agreement between the communicating devices. Dept of CSE, VEC 1.6
- 6. Data Flow: □ Communication between two devices can be ◦ Simplex ◦ Half-duplex ◦ Full-duplex 1.9 Dept of CSE, VEC Figure 1.2 Data flow (simplex, half-duplex, and full-duplex) 1.1 0 Dept of CSE, VEC
- 7. Simplex mode: The communication is unidirectional, as on a one-way street. □ Only one of the two devices on a link can transmit; the other can only receive □Examples : Keyboards and traditional monitors □The keyboard can only introduce input; The monitor can only accept output. □The simplex mode can use the entire capacity of the channel to send data in one direction. 1.1 1 Dept of CSE, VEC Half-duplex mode: □Each station can both transmit and receive, but not at the same time □When one device is sending, the other can only receive, and vice versa □The entire capacity of a channel is taken over by whichever of the two devices is transmitting at the time □Examples : Walkie-talkies and radios 1.1 2 Dept of CSE, VEC
- 8. Full duplex mode: □ Both stations can transmit and receive simultaneously □ It is like a two-way street with traffic flowing in both directions at the same time. □ The link capacity can be shared in two ways: ◦ Either the link must contain two physically separate transmission paths, one for sending and the other for receiving ◦ Or the capacity of the channel is divided between signals traveling in both directions. □ Example: The telephone network ◦ When two people are communicating by a telephone line, both can talk and listen at the same time. 1.1 3 Dept of CSE, VEC 14 Effectiveness of Data Communications □ Depends on 3 fundamental characteristics: ◦ Delivery : ● The system must deliver data to the correct destination ● Data must be received by the intended device or user and only by that device or user ◦ Accuracy: ● The system must deliver the data accurately. ● Data that have been altered in transmission and left uncorrected are unusable ◦ Timeliness: ● The system must deliver data in a timely manner ● Data delivered. late are useless ● Delivering the data in the same order that they are produced and without significant delay (real time transmission)
- 9. 1-2 NETWORKS A network •A set of nodes (often referred to as devices) connected by communication links. •A node can be a computer, printer, or any other device capable of sending and/or receiving data generated by the devices in the network. •A link can be a cable, air, optical fiber, or any medium which can transport a signal carrying information. Topics : ▪ Network Criteria ▪ Physical Structures ▪ Categories ofDN ept e oft Cw SE,o VE r Cks 1.1 5 Network Criteria □ Performance ◦ Depends on Network Elements ◦ Measured in terms of Delay and Throughput □ Reliability ◦ Failure rate of network components ◦ Measured in terms of availability/robustness □ Security ◦ Data protection against corruption/loss of data due to: ● Errors Dept of CSE, VEC 6 1.1
- 10. Performance □ Performance can be measured by the following metrics: ◦ Transit time: Amount of time required for a message to travel from one device to another ◦ Response time: The elapsed time between an inquiry and a response □ The performance of a network depends on the factors such as: ◦ number of users ◦ type of transmission medium ◦ capabilities of the connected hardware ◦ efficiency of the software. 17 Dept of CSE, VEC Performance Contd., □Performance is often evaluated by two networking metrics: ◦ Throughput ◦ Delay. □We often need more throughput and less delay. □Two criteria are often contradictory. □If we try to send more data to the network, we may increase throughput □But we increase the delay because of traffic congestion in the network Dept of CSE, VEC 18
- 11. Reliability □ Network reliability is measured by ◦ the frequency of failure, ◦ the time it takes a link to recover from a failure ◦ the network's robustness in a catastrophe. 19 Dept of CSE, VEC Security □Network security issues include ◦ protecting data from unauthorized access ◦ protecting data from damage and development ◦ implementing policies and procedures for recovery from breaches and data losses Dept of CSE, VEC 20
- 12. Physical Structures □ Type of Connection ◦ Point to Point - single transmitter and receiver ◦ Multipoint - multiple recipients of single transmission □ Physical Topology ◦ Connection of devices ◦ Type of transmission – ● Unicast, ● Mulitcast, ● Broadcast 1.2 1 Dept of CSE, VEC Figure 1.3 Types of connections: point-to-point and multipoint Dept of CSE, VEC 2 1.2
- 13. Point-to-point: □ A point-to-point connection provides a dedicated link between two devices □ The entire capacity of the link is reserved for transmission between those two devices □ Most point-to-point connections use an actual length of wire or cable to connect the two ends, but other options, such as microwave or satellite links, are also possible □ Example : change television channels by infrared remote control, between the remote control and the television's control system. 23 Dept of CSE, VEC Multipoint : □ A multipoint also called multidrop connection □ More than two specific devices share a single link □ The capacity of the channel is shared, either spatially or temporally □ If several devices can use the link simultaneously, it is a spatially shared connection □ If users must take turns, it is a timeshared connection. Dept of CSE, VEC 24
- 14. Physical Topology □ The geometric representation of the relationship of all the links and linking devices (nodes) to one another □ Two or more devices connect to a link; Two or more links form a topology 25 Dept of CSE, VEC Figure 1.4 Categories of topology 1.2 Dept of CSE, VEC 6
- 15. Figure 1.5 A fully connected mesh topology (five devices) 1.2 7 Dept of CSE, VEC Mesh Topology Dept of CSE, VEC 28 □ In a mesh topology, every device has a dedicated point-to-point link to every other device. □ The term dedicated means that the link carries traffic only between the two devices it connects □ To find the number of physical links in a fully connected mesh network with n nodes, we first consider that each node must be connected to every other node. □ So we need n(n - 1) physical links. □ However, if each physical link allows communication in both directions (duplex mode), we can divide the number of links by 2 □ In other words, we can say that in a mesh topology, we need n(n-1)/2 duplex mode links
- 16. Advantages of mesh topology □ Dedicated links guarantees that each connection can carry its own data load, thus eliminating the traffic problems that can occur when links must be shared by multiple devices □ Mesh topology is robust. If one link becomes unusable, it does not incapacitate the entire system □ Privacy or security – as message travels along a dedicated line, only the intended recipient sees it □ Point-to-point links make fault identification and fault isolation easy 29 Dept of CSE, VEC Disadvantages of mesh topology Dept of CSE, VEC 30 □ Every device must be connected to every other device so installation and reconnection are difficult □ The sheer bulk of the wiring can be greater than the available space (in walls, ceilings, or floors) can accommodate □ The hardware required to connect each link (I/O ports and cable) can be prohibitively expensive □ For these reasons a mesh topology is usually implemented in a limited fashion, for example, as a backbone connecting the main computers of a hybrid network that can include several other topologies □ Example: Connection of telephone regional offices in which each regional office needs to be connected to every other regional office.
- 17. Figure 1.6 A star topology connecting four stations 1.3 1 Dept of CSE, VEC Star Topology □ Each device has a dedicated point-to-point link only to a central controller, usually called a hub. □ The devices are not directly linked to one another. □ Unlike a mesh topology, a star topology does not allow direct traffic between devices. □ The controller acts as an exchange: ◦ If one device wants to send data to another, ● it sends the data to the controller, ● which then relays the data to the other connected device Dept of CSE, VEC 32
- 18. Advantages of star topology □ Less expensive than a mesh topology: each device needs only one link and one I/O port to connect it to any number of others. □ Far less cabling needs to be housed, only one connection: between that device and the hub □ Robustness: If one link fails, only that link is affected. All other links remain active. This factor also lends itself to easy fault identification and isolation 33 Dept of CSE, VEC Disadvantages of star topology □Dependency of the whole topology on one single point, the hub. If the hub goes down, the whole system is dead □Although a star requires far less cable than a mesh, each node must be linked to a central hub. For this reason, often more cabling is required in a star than in some other topologies (such as ring or bus). Example: □The star topologyis used in local-area networks (LANs) Dept of CSE, VEC 34
- 19. Figure 1.7 A bus topology connecting three stations 1.3 5 Dept of CSE, VEC Bus Topology □It follows a multipoint connection □One long cable acts as a backbone to link all the devices in a network □Nodes are connected to the bus cable by drop lines and taps. □A drop line is a connection running between the device and the main cable. □A tap is a connector that either splices into the main cable or punctures the sheathing of a cable to create a contact with the metallic core. Dept of CSE, VEC 36
- 20. □ Ease of installation □ Bus uses less cabling than mesh or star topologies, as backbone cable can be laid along the most efficient path, then connected to the nodes by drop lines of various lengths Advantages of bus topology 37 Dept of CSE, VEC Disadvantages of bus topology □ Difficult reconnection and fault isolation □Signal reflection at the taps can cause degradation in quality. This can be controlled by limiting the number and spacing of devices connected to a given length of cable □A fault or break in the bus cable stops all transmission, even between devices on the same side of the problem Example: □ Ethernet LANs can use a bus topology Dept of CSE, VEC 38
- 21. Figure 1.8 A ring topology connecting six stations 1.3 9 Dept of CSE, VEC Ring Topology Dept of CSE, VEC 40 □ In a ring topology, each device has a dedicated point-to-point connection with only the two devices on either side of it. □ A signal is passed in one direction along the ring, until it reaches its destination from device to device. □ Each device in the ring incorporates a repeater. □ When a device receives a signal intended for another device, its repeater regenerates the bits and passes them along
- 22. Advantages of Ring Topology □ Easy to install and reconfigure: Each device is linked to only its immediate neighbor. To add or delete a device requires changing only two connections □ Fault isolation is simplified: In a ring, a signal is circulating at all times. If one device does not receive a signal within a specified period, it can issue an alarm. The alarm alerts the network operator to the problem and its location. 41 Dept of CSE, VEC Disadvantages of Ring Topology □ Unidirectional traffic: In a simple ring, a break in the ring (such as a disabled station) can disable the entire network. □This weakness can be solved by using a dual ring or a switch capable of closing off the break. Example: □Ring topology was prevalent when IBM introduced its local-area network Token Ring. Today, the need for higher-speed LANs has made this topology less popular. Dept of CSE, VEC 42
- 23. Figure 1.9 A hybrid topology: a star backbone with three bus networks 1.4 3 Dept of CSE, VEC Hybrid Topology Dept of CSE, VEC 44 □ A network can be hybrid. Example: □ a main star topologywith each several stations in a bus topology branch connecting
- 24. Categories of Networks □ Local Area Networks (LANs) ◦ Short distances ◦ Designed to provide local interconnectivity □ Wide Area Networks (WANs) ◦ Long distances ◦ Provide connectivity over large areas □ Metropolitan Area Networks (MANs) ◦ Provide connectivity over areas such as a city, a campus 1.4 5 Dept of CSE, VEC Local Area Network (LAN) □A local area network (LAN) is usually privately owned and links the devices in a single office, building, or campus □Depending on the needs of an organization and the type of technology used, a LAN can be as simple as two PCs and a printer in someone's home office; or it can extend throughout a company and include audio and video peripherals. □Currently, LAN size is limited to a few kilometers. Dept of CSE, VEC 46
- 25. Figure 1.10 An isolated LAN connecting 12 computers to a hub in a closet 1.4 7 Dept of CSE, VEC □ LANs are designed to allow resources to be shared between personal computers or workstations. □ The resources to be shared can include hardware (e.g., a printer), software (e.g., an application program), or data. □ A common example of a LAN, found in many business environments, links a workgroup of task-related computers, for example, engineering workstations or accounting PCs. □ One of the computers may be given a large capacity disk drive and may become a server to clients. □ Software can be stored on this central server and used as needed by the whole group. Dept of CSE, VEC 48 Local Area Network (LAN)
- 26. □ In addition to size, LANs are distinguished from other types of networks by their transmission media and topology. □ In general, a given LAN will use only one type of transmission medium. □ The most common LAN topologies are bus, ring, and star. □ Early LANs had data rates in the 4 to 16 megabits per second (Mbps) range. □ Today, however, speeds are normally 100 or 1000 Mbps. □ Wireless LANs are the newest evolution in LAN technology. Local Area Network (LAN) 49 Dept of CSE, VEC Metropolitan Area Network □A metropolitan area network (MAN) is a network with a size between a LAN and a WAN. □It normally covers the area inside a town or a city. □It is designed for customers who need a high-speed connectivity, normally to the Internet, and have endpoints spread over a city or part of city. □A good example of a MAN is the part of the telephone company network that can provide a high-speed DSL line to the customer. □ Another example is the cable TV network that originally was designed for cable TV, but today can also be used for high-speed data connection to the Internet Dept of CSE, VEC 50
- 27. 51 MAN Designed to extend over an entire city – May be a single network such as cable television network – may be a means of connecting a number of LANS into a larger network Metropolitan Area Network (MAN) hom e cable headend cable distribution network (simplified) A Cable TV Network is an example of a MAN Typically 500 to 5,000 homes 52
- 28. 53 Cable Network Architecture: Overview hom e cable headend cable distribution network (simplified) Cable Network Architecture: Overview hom e cable headend cable distribution network server(s 54
- 29. □ A wide area network (WAN) provides long-distance transmission of data, image, audio, and video information over large geographic areas that may comprise a country, a continent, or even the whole world. □ A WAN can be as complex as the backbones that connect the Internet (Switched WAN) or as simple as a dial-up line that connects a home computer to the Internet (a point-to-point WAN ) □ The switched WAN connects the end systems, which usually comprise a router (internetworking connecting device) that connects to another LAN or WAN. □ The point-to-point WAN is normally a line leased from a telephone or cable TV provider that connects a home computer or a small LAN to an Internet service provider (lSP). □ This type of WAN is often used to provide Internet access. Wide Area Network (WAN) 55 Dept of CSE, VEC WAN Provides long distance transmission of data, voice, image and video information over large geographic areas – a country/continent/world 56
- 30. Figure 1.11 WANs: a switched WAN and a point-to-point WAN 1.5 7 Dept of CSE, VEC Figure 1.12 A heterogeneous network made of four WANs and two LANs 1.5 8 Dept of CSE, VEC
- 31. □ An early example of a switched WAN is X.25, a network designed to provide connectivity between end users □ A good example of a switched WAN is the Asynchronous network with Transfer Mode (ATM) network, which is a fixed-size data unit packets called cells □ Another example of WANs is the wireless WAN Wide Area Network (WAN) 59 Dept of CSE, VEC nners and Uses of Computer Networks □Communicating using email, video, instant messaging and other methods □Sharing devices such as printers, sca photocopiers □Sharing files □Sharing software and operating programs on remote systems □Allowing network users to easily access and maintain information 1.6 8 Dept of CSE, VEC
- 32. Applications (1) end systems (hosts): run application programs e.g. Web, email at “edge of network” client/server model client host requests, receives service from always-on server e.g. Web browser/server; email client/server Client/server model is applicable in an intranet. 61 Client/server model is applicable in an intranet 62 Applications (2) □ Peer-Peer model: ◦ No fixed clients or servers ◦ Each host can act as both client & server □ Examples: Napster, Gnutella, KaZaA
- 33. 63 Applications (3) □ WWW □ Instant Messaging (Internet chat, text messaging on cellular phones) □ Peer-to-Peer □ Internet Phone □ Video-on-demand □ Distributed Games □ Remote Login (Telnet) □ File Transfer 1-4 PROTOCOLS A protocol is •synonymous with rule. •It consists of a set of rules that govern data communications. •It determines •what is communicated, •how it is communicated and •when it is communicated. •The key elements of a protocol are syntax, semantics and timing 1.6 4 Dept of CSE, VEC
- 34. Elements of a Protocol □ Syntax ◦ Structure or format of the data ◦ Indicates how to read the bits - field delineation □ Semantics ◦ Interprets the meaning of the bits ◦ Knows which fields define what action □ Timing ◦ When data should be sent and what ◦ Speed at which data should be sent or speed at which it is being received. 1.6 5 Dept of CSE, VEC Protocols and Standards □Standards ◦ Essential in creating and maintaining an open and competitive market for equipment manufacturers and in guaranteeing national and international interoperability of data and telecommunications technology and processes ◦ De facto: Standards that have not been approved by an organised body but have been adopted as standards through widespread use ◦ De jure: legislated by an officially recognised body 66
- 35. 67 Protocols and Standards □ Standards Organisations ◦ International organisation for Standardisation (ISO) ◦ International Telecommunication Union –Telecommunication Standards Sector (ITU-T) ◦ American National Standards Institute (ANSI) ◦ Institute of Electrical and Electronics Engineers (IEEE) ◦ Electronic Industries Assoctiation (EIA) Protocols and Standards □ Regulatory Agencies ◦ Federal Communication Commission (FCC) □ Internet Standards ◦ Internet Draft ◦ Request for Comment (RFC) 68
- 36. Protocol Layering □ In data communication and networking, a protocol defines the rules that both the sender and receiver and all intermediate devices need to follow to be able to communicate effectively. □ When communication is simple, we may need only one simple protocol □ When the communication is complex, we may need to divide the task between different layers, in which case we need a protocol at each layer or protocol layering. 69 Dept of CSE, VEC □ In the first scenario, communication is so simple that it can occur in only one layer. Assume Maria and Ann are neighbors with a lot of common ideas. Communication between Maria and Ann takes place in one layer, face to face, in the same language Dept of CSE, VEC 70 Protocol Layering A single-layer protocol
- 37. □ In the second scenario, we assume that Ann is offered a higher-level position in her company, but needs to move to another branch located in a city very far from Maria. □ The two friends still want to continue their communication and exchange ideas because they have come up with an innovative project to start a new business when they both retire. □ They decide to continue their conversation using regular mail through the post office. However, they do not want their ideas to be revealed by other people if the letters are intercepted. They agree on an encryption/decryption technique. Protocol Layering 71 Dept of CSE, VEC Protocol Layering Dept of CSE, VEC 72 A three-layer protocol
- 38. □ Protocol layering enables us to divide a complex task into several smaller and simpler tasks □ One of the advantages of protocol layering is that it allows us to separate the services from the implementation □ A layer needs to be able to receive a set of services from the lower layer and to give the services to the upper layer □ Protocol layering in the Internet, is that communication does not always use only two end systems □ There are intermediate systems that need only some layers, but not all layers □ If we did not use protocol layering, we would have to make each intermediate system as complex as the end systems, which makes the whole system more expensive Protocol Layering 73 Dept of CSE, VEC Principles of Protocol Layering First Principle □The first principle dictates that if we want bidirectional communication, we need to make each layer so that it is able to perform two opposite tasks, one in each direction Second Principle □The second principle that we need to follow in protocol layering is that the two objects under each layer at both sites should be identical Dept of CSE, VEC 74
- 39. Logical Connections □Layer-to-layer communication □Logical (imaginary) connection at each layer through which they can send the object created from that layer Principles of Protocol Layering 75 Dept of CSE, VEC 76 Overview