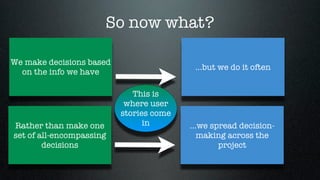
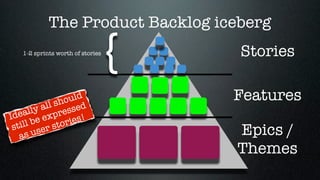
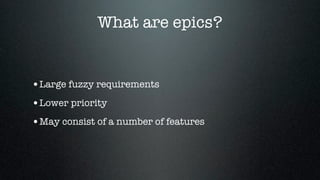
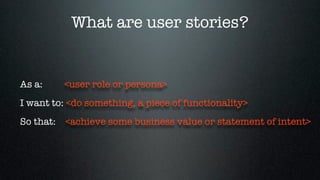
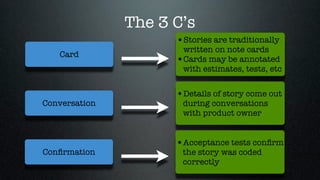
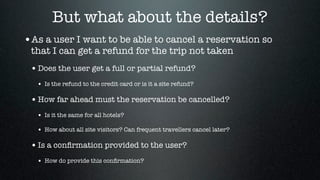
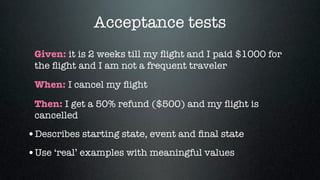
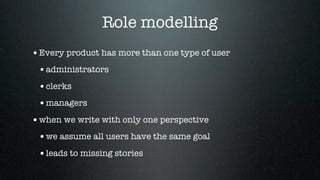
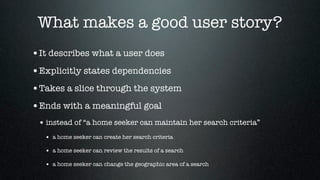
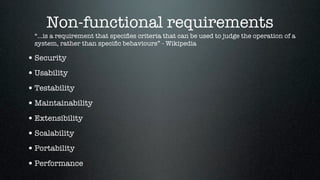
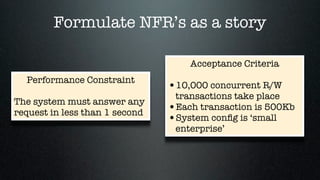
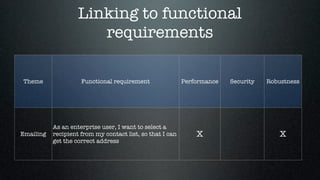
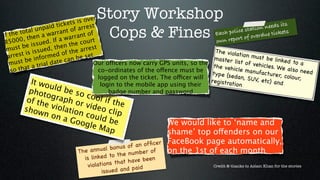
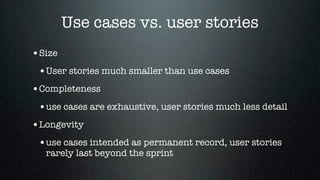
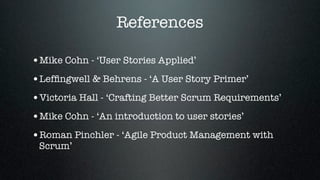
The document presents guidelines for writing effective user stories in Agile development. It emphasizes the importance of understanding user roles, ensuring stories are independent, negotiable, valuable, estimable, small, and testable (INVEST). Additionally, it outlines techniques for engaging users in story writing, the significance of acceptance criteria, and best practices for prioritizing and decomposing stories.