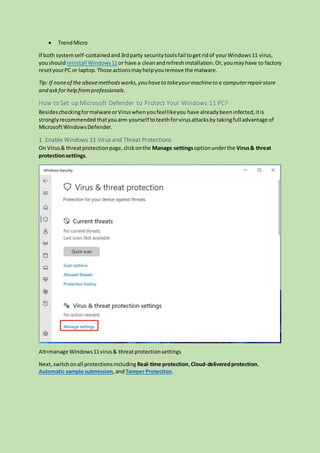
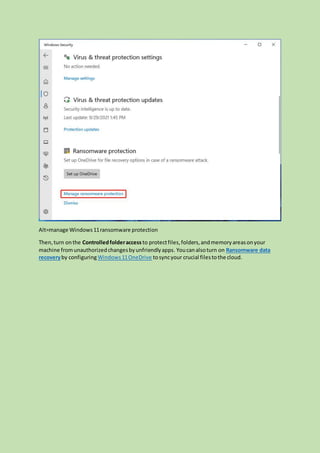
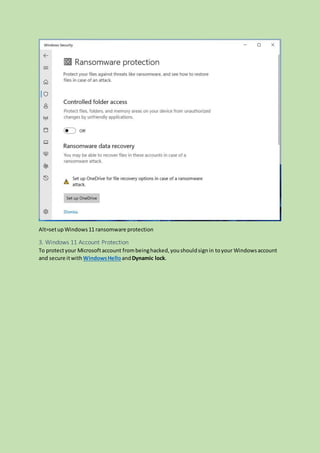
The document provides a comprehensive guide on dealing with viruses and malware in Windows 11, covering definitions, detection, removal, and prevention methods. It highlights the rise of Windows 11-specific malware and the importance of using security measures like Microsoft Defender and third-party antivirus tools. The document also outlines steps for virus detection and removal, as well as tips for maintaining system security.