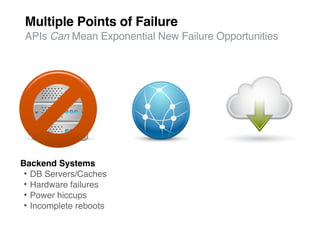
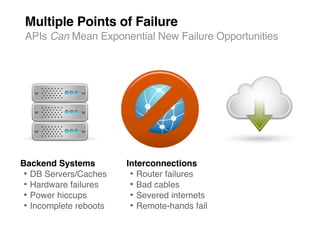
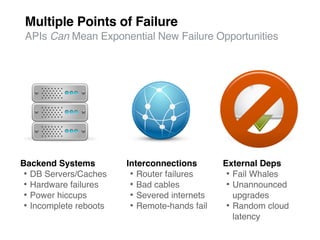
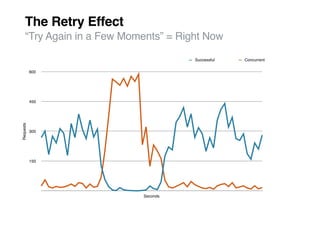
The document discusses best practices for API usage and management, emphasizing the importance of testing, versioning, and embracing standards to minimize failure opportunities. It provides five key tips: thorough testing, planning for future versions, embracing standards, continuous monitoring, and handling failures gracefully. Additionally, it suggests utilizing API management services for effective monitoring and support.