What does a trust framework operator do?
•
0 likes•135 views
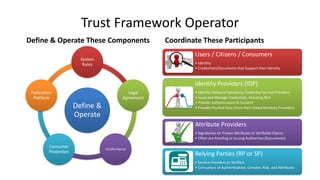
What are the categories of operations and responsibilities of a Trust Framework Operator to administer a trust framework. Would you want to get into the business? Is it a business?
Report
Share
Report
Share
Download to read offline
Recommended
SAG RTA: Most Important Choice of Investors and Mutual Fund Houses

SAG provides top-class RTA services including access to entire RTA application forms, affordable fees, and a unique dashboard for individuals and professionals. They have expert backend support, timely updates, and links with national depositories. Choosing SAG offers benefits like recommended articles on capital raising tools, allotment of shares, and opening a demat account.
ogil_trader_for_underwriting_factsheet_06-15-web[1]![ogil_trader_for_underwriting_factsheet_06-15-web[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![ogil_trader_for_underwriting_factsheet_06-15-web[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Trader for Underwriting is an insurance placing and policy administration system that provides a robust workflow framework alongside configurable options. It offers both B2B and B2C distribution through an extranet, intranet, or portal. Key features include obtaining quotes, transacting new business and renewals, an optional broker extranet, and an advanced rating engine. Benefits include full policy administration through predefined workflows, cloud-based scalability, Solvency II compliance, multilingual and multicurrency support, audit capabilities, and reporting and document production.
UC in the cloud

1. The document proposes a unified communications service built as a cloud-ready web application to address customers' friction points.
2. Key friction points for customers include proprietary devices, difficult incremental rollouts, adding users to sessions, and federation issues.
3. The proposal is for a UC service delivered via browser as a client that can accept dynamic downloads from an application server, addressing all identified friction points.
Solicitation Tool, Reverse Auction Service

The Solicitation Tool, Reverse Auction Service & QA/QC Auditing application is an integrated solution to improve operational efficiencies while achieving measurable cost savings.
WSO2Con USA 2017: Multi-tenanted, Role-based Identity & Access Management sol...

The goal of West’s project is to provide a centralized identity and access management solution within West’s Interactive Services division that can be leveraged by the customer facing portal and several other web applications developed within the company. Apart from the several out-of-the-box features that West benefited from, WSO2 Identity Server had to be extended for certain other requirements. This session will go into the details of these extensions as it relates to multi-tenancy, role-based permissions and access control by product, as well as tenant subscription and entitlements.
Resilient Network Systems - Trust Network Overview Slides - July 2014

Slides on Resilient Network Systems' Trust Network platform for display on our homepage and distribution to interested users.
Managing outsource IT contracts - Fundamentals

- What is a contract?
- Understand the concepts of outsourcing relationships
- To explain some of the different contract types involved in outsourcing
- Typical reasons for outsourcing
- Contracting parties
- Key aspects to clarify when outsourcing
- Commercial aspects
- General principles
- Checklist
Carrie Peter

Digital Retail Africa 2023 hosted by IT News Africa - Carrie Peter speaks on Balancing User Experience and Security Compliance at Scale at the Digital Retail Africa 2023 conference. #retailtech #ecommerce #customerexperience #onlineshopping #securitycompliance
Recommended
SAG RTA: Most Important Choice of Investors and Mutual Fund Houses

SAG provides top-class RTA services including access to entire RTA application forms, affordable fees, and a unique dashboard for individuals and professionals. They have expert backend support, timely updates, and links with national depositories. Choosing SAG offers benefits like recommended articles on capital raising tools, allotment of shares, and opening a demat account.
ogil_trader_for_underwriting_factsheet_06-15-web[1]![ogil_trader_for_underwriting_factsheet_06-15-web[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![ogil_trader_for_underwriting_factsheet_06-15-web[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Trader for Underwriting is an insurance placing and policy administration system that provides a robust workflow framework alongside configurable options. It offers both B2B and B2C distribution through an extranet, intranet, or portal. Key features include obtaining quotes, transacting new business and renewals, an optional broker extranet, and an advanced rating engine. Benefits include full policy administration through predefined workflows, cloud-based scalability, Solvency II compliance, multilingual and multicurrency support, audit capabilities, and reporting and document production.
UC in the cloud

1. The document proposes a unified communications service built as a cloud-ready web application to address customers' friction points.
2. Key friction points for customers include proprietary devices, difficult incremental rollouts, adding users to sessions, and federation issues.
3. The proposal is for a UC service delivered via browser as a client that can accept dynamic downloads from an application server, addressing all identified friction points.
Solicitation Tool, Reverse Auction Service

The Solicitation Tool, Reverse Auction Service & QA/QC Auditing application is an integrated solution to improve operational efficiencies while achieving measurable cost savings.
WSO2Con USA 2017: Multi-tenanted, Role-based Identity & Access Management sol...

The goal of West’s project is to provide a centralized identity and access management solution within West’s Interactive Services division that can be leveraged by the customer facing portal and several other web applications developed within the company. Apart from the several out-of-the-box features that West benefited from, WSO2 Identity Server had to be extended for certain other requirements. This session will go into the details of these extensions as it relates to multi-tenancy, role-based permissions and access control by product, as well as tenant subscription and entitlements.
Resilient Network Systems - Trust Network Overview Slides - July 2014

Slides on Resilient Network Systems' Trust Network platform for display on our homepage and distribution to interested users.
Managing outsource IT contracts - Fundamentals

- What is a contract?
- Understand the concepts of outsourcing relationships
- To explain some of the different contract types involved in outsourcing
- Typical reasons for outsourcing
- Contracting parties
- Key aspects to clarify when outsourcing
- Commercial aspects
- General principles
- Checklist
Carrie Peter

Digital Retail Africa 2023 hosted by IT News Africa - Carrie Peter speaks on Balancing User Experience and Security Compliance at Scale at the Digital Retail Africa 2023 conference. #retailtech #ecommerce #customerexperience #onlineshopping #securitycompliance
Most Comprehensive, Updated and Scalable Compliance Management Software Solut...

Most Comprehensive, Updated and Scalable Compliance Management Software Solut...Lawrbit Lextech India Private Limited
Lawrbit Enterprise Compliance Management Software Solution
Lawrbit helps businesses to manage regulatory compliance risks proactively through its comprehensive Regulatory Intelligence for 70+ countries covering 1000+ regulatory bodies and 3500+ laws globally.
Our Regulatory Intelligence is created, managed and updated by 100+ Tier 1 & 2 law firms globally. It provides a centralised framework and an integrated approach to manage an extensive range of compliance requirements, enabling businesses to efficiently manage cross geography, functional and industry mandates; allowing users to know and manage global regulatory compliance confidently with the most comprehensive and authentic legal intelligence – in a single solution.unit 1 Federated Identity Management_4.pptx

This document discusses federated identity management. It defines identity as who or what a person or thing is. Federated identity allows for portable identity across different domains through agreements and standards. Key requirements for identity federation include authentication, identity management, trust between domains, identity and attribute mapping, and attribute exchange. Popular protocols for federated identity include OpenID, SAML, and WS-Trust/WS-Federation. The document provides examples of how WSO2 Identity Server can be used to implement different federation patterns like token exchange and resource STS. It also discusses how a SaaS application could use trusted identity providers for user authentication and attribute sharing while mapping identity provider roles to application roles.
Elevate 2019: Financial Professional Slides

This document provides an overview of ethics standards and rules for CPAs, including those from the AICPA and other standard-setting bodies. It discusses the AICPA Code of Professional Conduct, which establishes principles like integrity, objectivity and independence. The Code also contains rules for members in public practice and business regarding issues like conflicts of interest, confidentiality, acts discreditable to the profession, and independence. Additional topics covered include statements on tax services, IRS Circular 230, continuing education requirements, and responding to client errors or omissions.
Provider Authentication for Health Information Exchange

Provider Authentication for Health Information Exchange Presentation to Privacy & Security Tiger Team
Total compliance | Statutory Compliance - Alphabricks Technologies

Total compliance, Statutory Compliance provides unified solutions for all your compliance needs across organization. It allows organization to define and track compliance's and provides visibility and transparency into compliance readiness.
Presentation

Single Sign On (SSO) allows a user to authenticate once and gain access to multiple related systems without re-authenticating. SSO uses protocols like SAML and OAuth to issue authentication tokens after initial login. SAML is an XML-based standard that transfers user identity and attribute data between an identity provider and service provider using assertions. Metadata ensures secure transactions by allowing providers to look up authentication endpoints and validate digital signatures. The SSO workflow involves a user authenticating with an identity provider, which issues a token for the user to access a service provider. Major SSO providers include Microsoft, IBM, Red Hat, and ForgeRock.
TrustedAgent FedRAMP Security Authorization

TrustedAgent GRC streamlines the complexity of obtaining security authorization from FedRAMP for cloud IaaS, PaaS, and SaaS services and applications. From tracking evidence and key control implementation to create key deliverables like security plans and managing continuous monitoring for ongoing compliance. TrustedAgent significantly reduces the amount of work to be done manually including managing vulnerabilities from ongoing compliance. Download and contact us to learn more how TrustedAgent GRC can create opportunities for your cloud offerings in the Federal Government.
Co p

This document discusses enterprise identity and access management. It covers foundational concepts like identity, authentication, authorization and accounting. It also discusses managing identity operations, including provisioning, privileged access management and synchronization. Managing identity in the extended enterprise through identity federation and identity as a service is also covered. The document concludes with considerations around identity management compliance and operations.
eSignatures: The lynchpin for Digitisation

Carrie Peter from Impression Signatures delivered a keynote on eSignatures: The lynchpin for Digitisation at Digital Finance Africa 2023.
Chapter 5 - Identity Management

This document discusses key concepts in identity and access management including:
- Objects, subjects, access control, identification, authentication, and authorization are the core components.
- Identification provides uniqueness, authentication provides validity, and authorization provides access control.
- Multi-factor authentication using something you know, have, and are is most secure.
- Directories, like LDAP, centrally manage digital identities and attributes to streamline access management.
Co p

This document discusses managing enterprise identity and access in 2013. It covers the changing landscape of identity and access management with business workflows extending beyond company infrastructure. It also discusses foundational concepts of enterprise identity including identification, authentication, authorization, and accounting. It covers managing identity operations, the extended enterprise through identity federation and identity as a service, as well as compliance and operations considerations.
Charging Up Your Subscription Commerce With a 360 View (Subscribed13)

Learn how to improve customer service and increase efficiencies across your organization by using Salesforce to provide a 360 degree of your customers. In addition, hear how you can collect revenues faster and improve customer retention by using a self-service module for onboarding, renewals, invoicing and payments, changing subscription terms, and setting up auto-pay.
Overview.ppt

InCommon provides federated identity management for higher education institutions and their partners. It establishes a common trust framework that allows institutions to leverage their identity databases and single sign-on systems. This allows users to access multiple online resources with one set of credentials. Through standards like SAML and Shibboleth, InCommon handles authentication while services make authorization decisions based on shared attributes. Over 250 institutions and millions of users participate in InCommon's federation for convenient and secure access to a growing number of academic and commercial resources.
Can Blockchain Enable Identity Management?

Blockchain continues to gain traction in the market place as a compelling solution for making identity and access management (IAM) more cost effective by harnessing the power of distributed members in order to “crowdsource” identity services. This session will review an attempt to prove this hypothesis through a proof-of-concept (POC) built for a not-for-profit healthcare consortium.
Learning Objectives:
1: Learn what blockchain is and how it can help solve problems within IAM.
2: Understand the intended end-state and key players in the blockchain identity ecosystem.
3: Learn about the key elements and lessons learned from this POC.
(Source: RSA Conference USA 2018)
Carrie Peter 

The document discusses the use of eSignatures to digitize processes that were traditionally paper-based. It notes that eSignatures allow single interactions to enable multiple digital processes and maximize value. It also outlines relevant legislation around eSignatures and prescriptions in South Africa. Compliance with various acts is required regarding consent, agreements, identity verification and securely storing records for mandated periods. The consequences of non-compliance, like data breaches and fines, are also mentioned. Overall the document promotes eSignatures as a way to improve processes, reduce costs and prevent fraud.
LexComply - Compliance Software India

Drive compliance culture to ensure 100% adherence & lower risks with LexComply Legal Compliance Management solution in India, having integrated technology & updated legal library to identify, Allocate, Report & monitor compliance across group companies, locations, departments, & 3rd parties.
Functional model (2)

A proposed functional model for the NSTIC (National Strategy for Trusted Identities in Cyberspace) Identity Ecosystem.
LexComply - Regulatory compliance and Risk Management Software

Ensure 100% Compliance coverage through LexComply Compliance Management Software & Legal library - Identify, Allocate, Know, Report & Monitor Compliance across group companies, departments and 3rd parties Visit :- https://lexcomply.com
Blockchain and the investment industry stack

Provides initial reflections on the potential of blockchain to transform the end-to-end retail investments industry
unit4.pptx

ASTHETIC In computing, identity management (IdM) describes the management of individual principals, their authentication, authorization, and privileges within or across system and enterprise boundaries with the goal of increasing security and productivity while decreasing cost, downtime and repetitive tasks.
The terms "Identity Management" and "Identity and Access Management" are used interchangeably in the area of Identity access management, while identity management its
Ready to Unlock the Power of Blockchain!

Imagine a world where data flows freely, yet remains secure. A world where trust is built into the fabric of every transaction. This is the promise of blockchain, a revolutionary technology poised to reshape our digital landscape.
Toptal Tech is at the forefront of this innovation, connecting you with the brightest minds in blockchain development. Together, we can unlock the potential of this transformative technology, building a future of transparency, security, and endless possibilities.
存档可查的(USC毕业证)南加利福尼亚大学毕业证成绩单制做办理

精仿办理南加利福尼亚大学毕业证成绩单(【微信176555708】)毕业证学历认证OFFER专卖国外文凭学历学位证书办理澳洲文凭|澳洲毕业证,澳洲学历认证,澳洲成绩单【微信176555708】 澳洲offer,教育部学历认证及使馆认证永久可查 ,国外毕业证|国外学历认证,国外学历文凭证书 USC毕业证,USC毕业证,USC毕业证,USC毕业证,USC毕业证,USC毕业证【微信176555708】,USC毕业证,专业为留学生办理毕业证、成绩单、使馆留学回国人员证明、教育部学历学位认证、录取通知书、Offer、(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
学历顾问:微信:176555708
More Related Content
Similar to What does a trust framework operator do?
Most Comprehensive, Updated and Scalable Compliance Management Software Solut...

Most Comprehensive, Updated and Scalable Compliance Management Software Solut...Lawrbit Lextech India Private Limited
Lawrbit Enterprise Compliance Management Software Solution
Lawrbit helps businesses to manage regulatory compliance risks proactively through its comprehensive Regulatory Intelligence for 70+ countries covering 1000+ regulatory bodies and 3500+ laws globally.
Our Regulatory Intelligence is created, managed and updated by 100+ Tier 1 & 2 law firms globally. It provides a centralised framework and an integrated approach to manage an extensive range of compliance requirements, enabling businesses to efficiently manage cross geography, functional and industry mandates; allowing users to know and manage global regulatory compliance confidently with the most comprehensive and authentic legal intelligence – in a single solution.unit 1 Federated Identity Management_4.pptx

This document discusses federated identity management. It defines identity as who or what a person or thing is. Federated identity allows for portable identity across different domains through agreements and standards. Key requirements for identity federation include authentication, identity management, trust between domains, identity and attribute mapping, and attribute exchange. Popular protocols for federated identity include OpenID, SAML, and WS-Trust/WS-Federation. The document provides examples of how WSO2 Identity Server can be used to implement different federation patterns like token exchange and resource STS. It also discusses how a SaaS application could use trusted identity providers for user authentication and attribute sharing while mapping identity provider roles to application roles.
Elevate 2019: Financial Professional Slides

This document provides an overview of ethics standards and rules for CPAs, including those from the AICPA and other standard-setting bodies. It discusses the AICPA Code of Professional Conduct, which establishes principles like integrity, objectivity and independence. The Code also contains rules for members in public practice and business regarding issues like conflicts of interest, confidentiality, acts discreditable to the profession, and independence. Additional topics covered include statements on tax services, IRS Circular 230, continuing education requirements, and responding to client errors or omissions.
Provider Authentication for Health Information Exchange

Provider Authentication for Health Information Exchange Presentation to Privacy & Security Tiger Team
Total compliance | Statutory Compliance - Alphabricks Technologies

Total compliance, Statutory Compliance provides unified solutions for all your compliance needs across organization. It allows organization to define and track compliance's and provides visibility and transparency into compliance readiness.
Presentation

Single Sign On (SSO) allows a user to authenticate once and gain access to multiple related systems without re-authenticating. SSO uses protocols like SAML and OAuth to issue authentication tokens after initial login. SAML is an XML-based standard that transfers user identity and attribute data between an identity provider and service provider using assertions. Metadata ensures secure transactions by allowing providers to look up authentication endpoints and validate digital signatures. The SSO workflow involves a user authenticating with an identity provider, which issues a token for the user to access a service provider. Major SSO providers include Microsoft, IBM, Red Hat, and ForgeRock.
TrustedAgent FedRAMP Security Authorization

TrustedAgent GRC streamlines the complexity of obtaining security authorization from FedRAMP for cloud IaaS, PaaS, and SaaS services and applications. From tracking evidence and key control implementation to create key deliverables like security plans and managing continuous monitoring for ongoing compliance. TrustedAgent significantly reduces the amount of work to be done manually including managing vulnerabilities from ongoing compliance. Download and contact us to learn more how TrustedAgent GRC can create opportunities for your cloud offerings in the Federal Government.
Co p

This document discusses enterprise identity and access management. It covers foundational concepts like identity, authentication, authorization and accounting. It also discusses managing identity operations, including provisioning, privileged access management and synchronization. Managing identity in the extended enterprise through identity federation and identity as a service is also covered. The document concludes with considerations around identity management compliance and operations.
eSignatures: The lynchpin for Digitisation

Carrie Peter from Impression Signatures delivered a keynote on eSignatures: The lynchpin for Digitisation at Digital Finance Africa 2023.
Chapter 5 - Identity Management

This document discusses key concepts in identity and access management including:
- Objects, subjects, access control, identification, authentication, and authorization are the core components.
- Identification provides uniqueness, authentication provides validity, and authorization provides access control.
- Multi-factor authentication using something you know, have, and are is most secure.
- Directories, like LDAP, centrally manage digital identities and attributes to streamline access management.
Co p

This document discusses managing enterprise identity and access in 2013. It covers the changing landscape of identity and access management with business workflows extending beyond company infrastructure. It also discusses foundational concepts of enterprise identity including identification, authentication, authorization, and accounting. It covers managing identity operations, the extended enterprise through identity federation and identity as a service, as well as compliance and operations considerations.
Charging Up Your Subscription Commerce With a 360 View (Subscribed13)

Learn how to improve customer service and increase efficiencies across your organization by using Salesforce to provide a 360 degree of your customers. In addition, hear how you can collect revenues faster and improve customer retention by using a self-service module for onboarding, renewals, invoicing and payments, changing subscription terms, and setting up auto-pay.
Overview.ppt

InCommon provides federated identity management for higher education institutions and their partners. It establishes a common trust framework that allows institutions to leverage their identity databases and single sign-on systems. This allows users to access multiple online resources with one set of credentials. Through standards like SAML and Shibboleth, InCommon handles authentication while services make authorization decisions based on shared attributes. Over 250 institutions and millions of users participate in InCommon's federation for convenient and secure access to a growing number of academic and commercial resources.
Can Blockchain Enable Identity Management?

Blockchain continues to gain traction in the market place as a compelling solution for making identity and access management (IAM) more cost effective by harnessing the power of distributed members in order to “crowdsource” identity services. This session will review an attempt to prove this hypothesis through a proof-of-concept (POC) built for a not-for-profit healthcare consortium.
Learning Objectives:
1: Learn what blockchain is and how it can help solve problems within IAM.
2: Understand the intended end-state and key players in the blockchain identity ecosystem.
3: Learn about the key elements and lessons learned from this POC.
(Source: RSA Conference USA 2018)
Carrie Peter 

The document discusses the use of eSignatures to digitize processes that were traditionally paper-based. It notes that eSignatures allow single interactions to enable multiple digital processes and maximize value. It also outlines relevant legislation around eSignatures and prescriptions in South Africa. Compliance with various acts is required regarding consent, agreements, identity verification and securely storing records for mandated periods. The consequences of non-compliance, like data breaches and fines, are also mentioned. Overall the document promotes eSignatures as a way to improve processes, reduce costs and prevent fraud.
LexComply - Compliance Software India

Drive compliance culture to ensure 100% adherence & lower risks with LexComply Legal Compliance Management solution in India, having integrated technology & updated legal library to identify, Allocate, Report & monitor compliance across group companies, locations, departments, & 3rd parties.
Functional model (2)

A proposed functional model for the NSTIC (National Strategy for Trusted Identities in Cyberspace) Identity Ecosystem.
LexComply - Regulatory compliance and Risk Management Software

Ensure 100% Compliance coverage through LexComply Compliance Management Software & Legal library - Identify, Allocate, Know, Report & Monitor Compliance across group companies, departments and 3rd parties Visit :- https://lexcomply.com
Blockchain and the investment industry stack

Provides initial reflections on the potential of blockchain to transform the end-to-end retail investments industry
unit4.pptx

ASTHETIC In computing, identity management (IdM) describes the management of individual principals, their authentication, authorization, and privileges within or across system and enterprise boundaries with the goal of increasing security and productivity while decreasing cost, downtime and repetitive tasks.
The terms "Identity Management" and "Identity and Access Management" are used interchangeably in the area of Identity access management, while identity management its
Similar to What does a trust framework operator do? (20)
Most Comprehensive, Updated and Scalable Compliance Management Software Solut...

Most Comprehensive, Updated and Scalable Compliance Management Software Solut...
Provider Authentication for Health Information Exchange

Provider Authentication for Health Information Exchange
Total compliance | Statutory Compliance - Alphabricks Technologies

Total compliance | Statutory Compliance - Alphabricks Technologies
Charging Up Your Subscription Commerce With a 360 View (Subscribed13)

Charging Up Your Subscription Commerce With a 360 View (Subscribed13)
LexComply - Regulatory compliance and Risk Management Software

LexComply - Regulatory compliance and Risk Management Software
Recently uploaded
Ready to Unlock the Power of Blockchain!

Imagine a world where data flows freely, yet remains secure. A world where trust is built into the fabric of every transaction. This is the promise of blockchain, a revolutionary technology poised to reshape our digital landscape.
Toptal Tech is at the forefront of this innovation, connecting you with the brightest minds in blockchain development. Together, we can unlock the potential of this transformative technology, building a future of transparency, security, and endless possibilities.
存档可查的(USC毕业证)南加利福尼亚大学毕业证成绩单制做办理

精仿办理南加利福尼亚大学毕业证成绩单(【微信176555708】)毕业证学历认证OFFER专卖国外文凭学历学位证书办理澳洲文凭|澳洲毕业证,澳洲学历认证,澳洲成绩单【微信176555708】 澳洲offer,教育部学历认证及使馆认证永久可查 ,国外毕业证|国外学历认证,国外学历文凭证书 USC毕业证,USC毕业证,USC毕业证,USC毕业证,USC毕业证,USC毕业证【微信176555708】,USC毕业证,专业为留学生办理毕业证、成绩单、使馆留学回国人员证明、教育部学历学位认证、录取通知书、Offer、(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
学历顾问:微信:176555708
办理毕业证(UPenn毕业证)宾夕法尼亚大学毕业证成绩单快速办理

官方原版办理宾夕法尼亚大学毕业证【微信176555708】学历认证怎么做:原版仿制宾夕法尼亚大学电子版成绩单毕业证认证【宾夕法尼亚大学毕业证成绩单】、宾夕法尼亚大学文凭证书成绩单复刻offer录取通知书、购买UPenn圣力嘉学院本科毕业证、【宾夕法尼亚大学毕业证办理UPenn毕业证书哪里买】、宾夕法尼亚大学 Offer在线办理UPenn Offer宾夕法尼亚大学Bachloer Degree。(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
学历顾问:微信:176555708
一比一原版(SLU毕业证)圣路易斯大学毕业证成绩单专业办理

SLU毕业证原版定制【微信:176555708】【圣路易斯大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
成绩单ps(UST毕业证)圣托马斯大学毕业证成绩单快速办理

一比一原版制作UST毕业证【微信176555708】圣托马斯大学毕业证书原版↑制作圣托马斯大学学历认证文凭办理圣托马斯大学留信网认证,留学回国办理毕业证成绩单文凭学历认证【微信176555708】专业为海外学子办理毕业证成绩单、文凭制作,学历仿制,回国人员证明、做文凭,研究生、本科、硕士学历认证、留信认证、结业证、学位证书样本、美国教育部认证百分百真实存档可查】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
学历顾问:微信:176555708
Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...

This article delves into how the Internet of Things in manufacturing is reshaping the industry, its benefits, challenges, and future prospects.
可查真实(Monash毕业证)西澳大学毕业证成绩单退学买

办理假西澳大学毕业证【微信176555708】购买,办理Monash成绩单,Monash毕业证制作【微信176555708】【西澳大学毕业证】,Monash毕业证购买,Monash学位证,西澳大学学位证【Monash成绩单制作】【Monash毕业证文凭 Monash本科 澳洲学历认证原版制作【diploma certificate degree transcript 】【留信网认证,本科,硕士,海归,博士,排名,成绩单】代办国外(海外)澳洲、韩国、加拿大、新西兰等各大学毕业证。 ?我们对海外大学及学院的毕业证成绩单所使用的材料,尺寸大小,防伪结构(包括:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。 文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)都有原版本文凭对照。#一整套西澳大学文凭证件办理#—包含西澳大学西澳大学毕业证成绩单学历认证|使馆认证|归国人员证明|教育部认证|留信网认证永远存档教育部学历学位认证查询办理国外文凭国外学历学位认证#我们提供全套办理服务。
一整套留学文凭证件服务:
一:西澳大学西澳大学毕业证成绩单毕业证 #成绩单等全套材料从防伪到印刷水印底纹到钢印烫金
二:真实使馆认证(留学人员回国证明)使馆存档
三:真实教育部认证教育部存档教育部留服网站永久可查
四:留信认证留学生信息网站永久可查
国外毕业证学位证成绩单办理方法:
1客户提供办理西澳大学西澳大学毕业证成绩单信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
教育部文凭学历认证认证的用途:
如果您计划在国内发展那么办理国内教育部认证是必不可少的。事业性用人单位如银行国企公务员在您应聘时都会需要您提供这个认证。其他私营 #外企企业无需提供!办理教育部认证所需资料众多且烦琐所有材料您都必须提供原件我们凭借丰富的经验帮您快速整合材料让您少走弯路。
实体公司专业为您服务如有需要请联系我: 微信176555708
重新申请毕业证书(RMIT毕业证)皇家墨尔本理工大学毕业证成绩单精仿办理

不能毕业办理【RMIT毕业证【微信176555708】皇家墨尔本理工大学文凭学历】【微信176555708】【皇家墨尔本理工大学文凭学历证书】【皇家墨尔本理工大学毕业证书与成绩单样本图片】毕业证书补办 Fake Degree做学费单【毕业证明信-推荐信】成绩单,录取通知书,Offer,在读证明,雅思托福成绩单,真实大使馆教育部认证,回国人员证明,留信网认证。网上存档永久可查!全套服务:皇家墨尔本理工大学皇家墨尔本理工大学本科学位证成绩单真实回国人员证明 #真实教育部认证。让您回国发展信心十足#铸就十年品质!信誉!实体公司!可以视频看办公环境样板如需办理真实可查可以先到公司面谈勿轻信小中介黑作坊!
可以提供皇家墨尔本理工大学钢印 #水印 #烫金 #激光防伪 #凹凸版 #最新版的毕业证 #百分之百让您绝对满意
印刷DHL快递毕业证 #成绩单7个工作日真实大使馆教育部认证1个月。为了达到高水准高效率
请您先以qq或微信的方式对我们的服务进行了解后如果有皇家墨尔本理工大学皇家墨尔本理工大学本科学位证成绩单帮助再进行电话咨询。
国外毕业证学位证成绩单如何办理:
1客户提供办理信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作皇家墨尔本理工大学毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
Gen Z and the marketplaces - let's translate their needs

The product workshop focused on exploring the requirements of Generation Z in relation to marketplace dynamics. We delved into their specific needs, examined the specifics in their shopping preferences, and analyzed their preferred methods for accessing information and making purchases within a marketplace. Through the study of real-life cases , we tried to gain valuable insights into enhancing the marketplace experience for Generation Z.
The workshop was held on the DMA Conference in Vienna June 2024.
留学学历(UoA毕业证)奥克兰大学毕业证成绩单官方原版办理

制做办理奥克兰大学学历证书<176555708微信>【毕业证明信-推荐信做学费单>【微信176555708】【制作UoA毕业证文凭认证奥克兰大学毕业证成绩单购买】【UoA毕业证书】{奥克兰大学文凭购买}】成绩单,录取通知书,Offer,在读证明,雅思托福成绩单,真实大使馆教育部认证,回国人员证明,>【制作UoA毕业证文凭认证奥克兰大学毕业证成绩单购买】【UoA毕业证书】{奥克兰大学文凭购买}留信网认证。
奥克兰大学学历证书<微信176555708(一对一服务包括毕业院长签字,专业课程,学位类型,专业或教育领域,以及毕业日期.不要忽视这些细节.这两份文件同样重要!毕业证成绩单文凭留信网学历认证!)[留学文凭学历认证(留信认证使馆认证)奥克兰大学毕业证成绩单毕业证证书大学Offer请假条成绩单语言证书国际回国人员证明高仿教育部认证申请学校等一切高仿或者真实可查认证服务。
多年留学服务公司,拥有海外样板无数能完美1:1还原海外各国大学degreeDiplomaTranscripts等毕业材料。海外大学毕业材料都有哪些工艺呢?工艺难度主要由:烫金.钢印.底纹.水印.防伪光标.热敏防伪等等组成。而且我们每天都在更新海外文凭的样板以求所有同学都能享受到完美的品质服务。
国外毕业证学位证成绩单办理方法:
1客户提供办理奥克兰大学奥克兰大学硕士毕业证成绩单信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)
— — — — 我们是挂科和未毕业同学们的福音我们是实体公司精益求精的工艺! — — — -
一真实留信认证的作用(私企外企荣誉的见证):
1:该专业认证可证明留学生真实留学身份同时对留学生所学专业等级给予评定。
2:国家专业人才认证中心颁发入库证书这个入网证书并且可以归档到地方。
3:凡是获得留信网入网的信息将会逐步更新到个人身份内将在公安部网内查询个人身份证信息后同步读取人才网入库信息。
4:个人职称评审加20分个人信誉贷款加10分。
5:在国家人才网主办的全国网络招聘大会中纳入资料供国家500强等高端企业选择人才。
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
国外证书(Lincoln毕业证)新西兰林肯大学毕业证成绩单不能毕业办理

退学办理新西兰林肯大学毕业证【微信176555708】学历认证怎么做:原版仿制新西兰林肯大学电子版成绩单毕业证认证【新西兰林肯大学毕业证成绩单】、新西兰林肯大学文凭证书成绩单复刻offer录取通知书、购买Lincoln圣力嘉学院本科毕业证、【新西兰林肯大学毕业证办理Lincoln毕业证书哪里买】、新西兰林肯大学 Offer在线办理Lincoln Offer新西兰林肯大学Bachloer Degree。1客户提供办理信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:微信176555708我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
7完成交易删除客户资料
高精端提供以下服务:
一:新西兰林肯大学新西兰林肯大学毕业证文凭证书全套材料从防伪到印刷水印底纹到钢印烫金
二:真实使馆认证(留学人员回国证明)使馆存档
三:真实教育部认证教育部存档教育部留服网站可查
四:留信认证留学生信息网站可查
五:与学校颁发的相关证件1:1纸质尺寸制定(定期向各大院校毕业生购买最新版本毕,业证成绩单保证您拿到的是鲁昂大学内部最新版本毕业证成绩单微信176555708)
A.为什么留学生需要操作留信认证?
留信认证全称全国留学生信息服务网认证,隶属于北京中科院。①留信认证门槛条件更低,费用更美丽,并且包过,完单周期短,效率高②留信认证虽然不能去国企,但是一般的公司都没有问题,因为国内很多公司连基本的留学生学历认证都不了解。这对于留学生来说,这就比自己光拿一个证书更有说服力,因为留学学历可以在留信网站上进行查询!
B.为什么我们提供的毕业证成绩单具有使用价值?
查询留服认证是国内鉴别留学生海外学历的唯一途径但认证只是个体行为不是所有留学生都操作所以没有办理认证的留学生的学历在国内也是查询不到的他们也仅仅只有一张文凭。所以这时候我们提供的和学校颁发的一模一样的毕业证成绩单就有了使用价值。
制作毕业证书(ANU毕业证)莫纳什大学毕业证成绩单官方原版办理

在线办理莫纳什大学毕业证【微信:176555708】(ANU毕业证书)成绩单学位证【微信:176555708】,留信认证(真实可查,永久存档)纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。#一整套莫纳什大学文凭证件办理#—包含莫纳什大学莫纳什大学毕业证文凭证书学历认证|使馆认证|归国人员证明|教育部认证|留信网认证永远存档教育部学历学位认证查询办理国外文凭国外学历学位认证#我们提供全套办理服务。
一整套留学文凭证件服务:
一:莫纳什大学莫纳什大学毕业证文凭证书毕业证 #成绩单等全套材料从防伪到印刷水印底纹到钢印烫金
二:真实使馆认证(留学人员回国证明)使馆存档
三:真实教育部认证教育部存档教育部留服网站永久可查
四:留信认证留学生信息网站永久可查
国外毕业证学位证成绩单办理方法:
1客户提供办理莫纳什大学莫纳什大学毕业证文凭证书信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
教育部文凭学历认证认证的用途:
如果您计划在国内发展那么办理国内教育部认证是必不可少的。事业性用人单位如银行国企公务员在您应聘时都会需要您提供这个认证。其他私营 #外企企业无需提供!办理教育部认证所需资料众多且烦琐所有材料您都必须提供原件我们凭借丰富的经验帮您快速整合材料让您少走弯路。
实体公司专业为您服务如有需要请联系我: 微信176555708
不能毕业如何获得(USYD毕业证)悉尼大学毕业证成绩单一比一原版制作

挂科购买☀【悉尼大学毕业证购买】【微信176555708】【USYD毕业证模板办理】加拿大文凭、本科、硕士、研究生学历都可以做,二、业务范围:
★、全套服务:毕业证、成绩单、化学专业毕业证书伪造【悉尼大学大学毕业证】微信176555708【USYD学位证书购买】◆◆◆◆◆ — — — 归国服务中心 — — -◆◆◆◆◆
【主营项目】
一.毕业证、成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
国外毕业证、学位证、成绩单办理流程:
1、客户提供办理信息:姓名、生日、专业、学位、毕业时间等(如信息不确定可以咨询顾问:【微信176555708】我们有专业老师帮你查询);
2、开始安排制作毕业证、成绩单电子图;
3、毕业证、成绩单电子版做好以后发送给您确认;
4、毕业证、成绩单电子版您确认信息无误之后安排制作成品;
5、成品做好拍照或者视频给您确认;
6、快递给客户(国内顺丰,国外DHL、UPS等快读邮寄)。
专业服务,请勿犹豫联系我!本公司是留学创业和海归创业者们的桥梁。一次办理,终生受用,一步到位,高效服务。详情请在线咨询办理,欢迎有诚意办理的客户咨询!洽谈。
◆招聘代理:本公司诚聘英国、加拿大、澳洲、新西兰、加拿大、法国、德国、新加坡各地代理人员,如果你有业余时间,有兴趣就请联系我们咨询【微信176555708】
没文凭怎么找工作。让您回国发展信心十足!
★、真实教育部学历学位认证;(一对一专业服务,可全程监控跟踪进度)
★、真实使馆认证,可以通过大使馆查询确认;(即教育部留服认证,不成功不收费)
★、毕业证、成绩单等材料,从防伪到印刷、水印到钢印烫金,高精仿度都是跟学校原版100%相同的;(敬请放心使用)
★、可以提供钢印、水印、烫金、激光防伪、凹凸版、最新版的毕业证、百分之百让您绝对满意、
★、印刷,DHL快递毕业证、成绩单7个工作日,真实大使馆教育部认证1个月。为了达到高水准高效率。
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

Ellisha Heppner, Grant Management Lead, presented an update on APNIC Foundation to the PNG DNS Forum held from 6 to 10 May, 2024 in Port Moresby, Papua New Guinea.
一比一原版(LBS毕业证)伦敦商学院毕业证成绩单专业办理

LBS毕业证原版定制【微信:176555708】【伦敦商学院毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Search Result Showing My Post is Now Buried

Search results burying my post that used to rank before Google's March 2024 algorithm update.
Understanding User Behavior with Google Analytics.pdf

Unlocking the full potential of Google Analytics is crucial for understanding and optimizing your website’s performance. This guide dives deep into the essential aspects of Google Analytics, from analyzing traffic sources to understanding user demographics and tracking user engagement.
Traffic Sources Analysis:
Discover where your website traffic originates. By examining the Acquisition section, you can identify whether visitors come from organic search, paid campaigns, direct visits, social media, or referral links. This knowledge helps in refining marketing strategies and optimizing resource allocation.
User Demographics Insights:
Gain a comprehensive view of your audience by exploring demographic data in the Audience section. Understand age, gender, and interests to tailor your marketing strategies effectively. Leverage this information to create personalized content and improve user engagement and conversion rates.
Tracking User Engagement:
Learn how to measure user interaction with your site through key metrics like bounce rate, average session duration, and pages per session. Enhance user experience by analyzing engagement metrics and implementing strategies to keep visitors engaged.
Conversion Rate Optimization:
Understand the importance of conversion rates and how to track them using Google Analytics. Set up Goals, analyze conversion funnels, segment your audience, and employ A/B testing to optimize your website for higher conversions. Utilize ecommerce tracking and multi-channel funnels for a detailed view of your sales performance and marketing channel contributions.
Custom Reports and Dashboards:
Create custom reports and dashboards to visualize and interpret data relevant to your business goals. Use advanced filters, segments, and visualization options to gain deeper insights. Incorporate custom dimensions and metrics for tailored data analysis. Integrate external data sources to enrich your analytics and make well-informed decisions.
This guide is designed to help you harness the power of Google Analytics for making data-driven decisions that enhance website performance and achieve your digital marketing objectives. Whether you are looking to improve SEO, refine your social media strategy, or boost conversion rates, understanding and utilizing Google Analytics is essential for your success.
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Brad Spiegel Macon GA’s journey exemplifies the profound impact that one individual can have on their community. Through his unwavering dedication to digital inclusion, he’s not only bridging the gap in Macon but also setting an example for others to follow.
Recently uploaded (20)
Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...

Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...
Gen Z and the marketplaces - let's translate their needs

Gen Z and the marketplaces - let's translate their needs
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024
Understanding User Behavior with Google Analytics.pdf

Understanding User Behavior with Google Analytics.pdf
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx
What does a trust framework operator do?
- 1. Trust Framework Operator Define & Operate These Components Define & Operate System Rules Legal Agreement Conformance Consumer Protection Federation Platform Coordinate These Participants Users / Citizens / Consumers • Identity • Credentials/Documents that Support their Identity Identity Providers (IDP) • Identity Network Operators, Credential Service Providers • Issue and Manage Credentials, including Risk • Provide Authentication & Consent • Provide Proofed Data (from their linked Attribute Providers) Attribute Providers • Signatories on Proven Attributes or Verifiable Claims • Often are Proofing or Issuing Authorities (Documents) Relying Parties (RP or SP) • Service Providers or Verifiers • Consumers of Authentication, Consent, Risk, and Attributes
- 2. Define the System Rules • Roles & Participants • Policy Library • Liability Handling • Conformance Assessment • Trust Marks • Shared Signals • Procedures • Change Notification • Breech Notification • User-Managed Identity • Informed Consent • User Ability to Fix • Selective Disclosure • Redress & Revocation • Trust Levels • Proofing • Attribute Accuracy • Authentication • Credential Mgt • Standards Identity Privacy ControlsNotification
- 3. Author Multilateral Agreements • Establishes the Federation • One legal agreement for each Role within the Federation – Adhere to System Rules – Protect Consumers as Defined • An Entity can play multiple roles within the Federation – Sign multiple agreements • Agree to Assessment Process for ConformanceRole = User, Identity Provider, Attribute Provider, Relying Party
- 4. Assess Conformance to System Rules • Audit and Enforce System Rules – Federation Operator Assesses? – Third Party Assessors? • Revocation and Suspension • Standards Adherence • Maintain Consumer Protection • Establish & Award Trust Marks
- 5. Protect the Consumer – Fuzzy Requirement • Abide by Law and Legislation within Region of Operation • Built into every aspect of System Rules • Redress and Notification Processes • Consumer-Managed Orientation • Consumer Right to Revoke • Promote Federation Brand • Build Consumer Promoters
- 6. Operate the Federation Platform • Discovery Services – RPs & Users discover IDPs and APs – White & Black List Services • Interoperability Functionality – Open ID Connect, Self-Sovereign • Federation Web Site – Consumer Information Site • Redress Mechanisms – Participant Services Site • Onboarding & Service Integration • Mediation • Billing and Reporting
