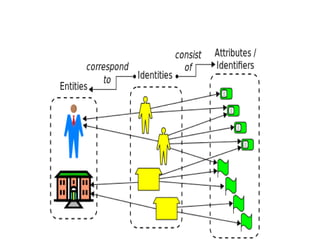
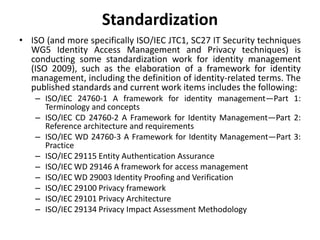
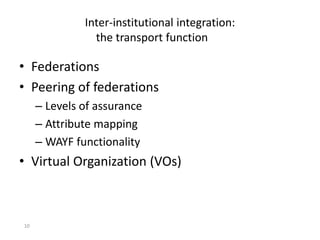
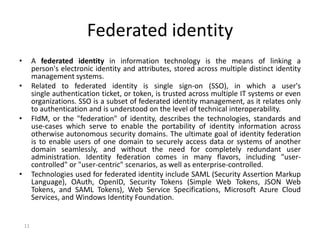
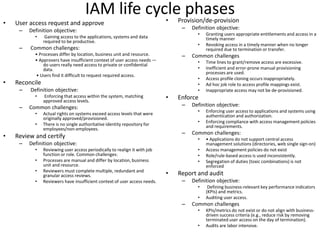
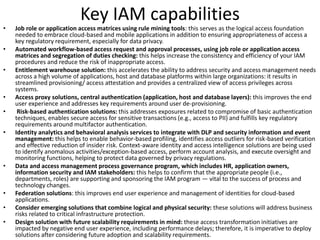
Identity and Access Management (IAM) focuses on controlling user identities, their authentication, authorization, and access privileges across systems to enhance security and efficiency. Key functions include user identity creation, management, access management, and the integration of modern technologies like cloud computing and federated identity solutions. IAM is evolving with standards and practices to ensure seamless user access and management of identities within increasingly complex digital environments.