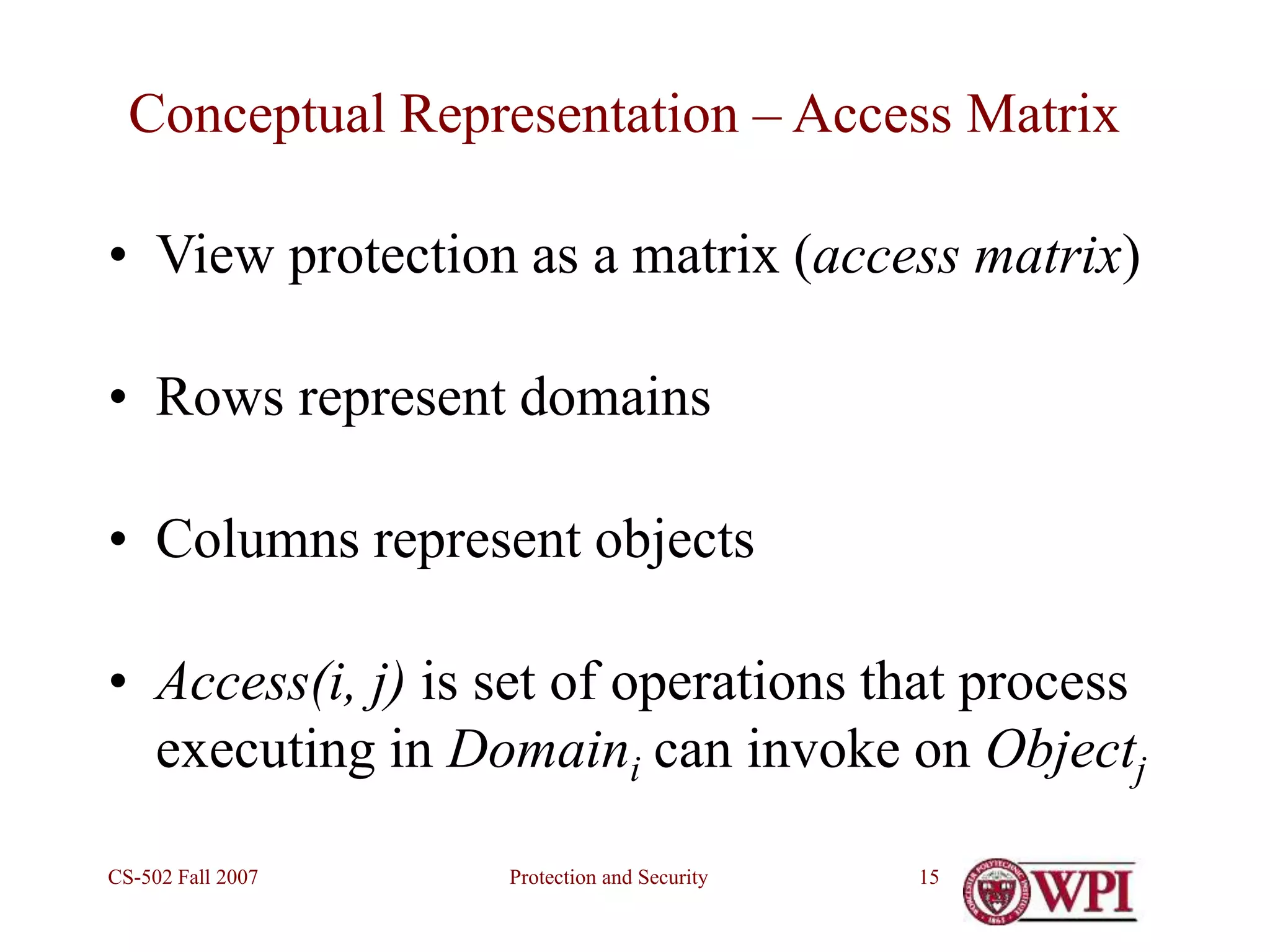
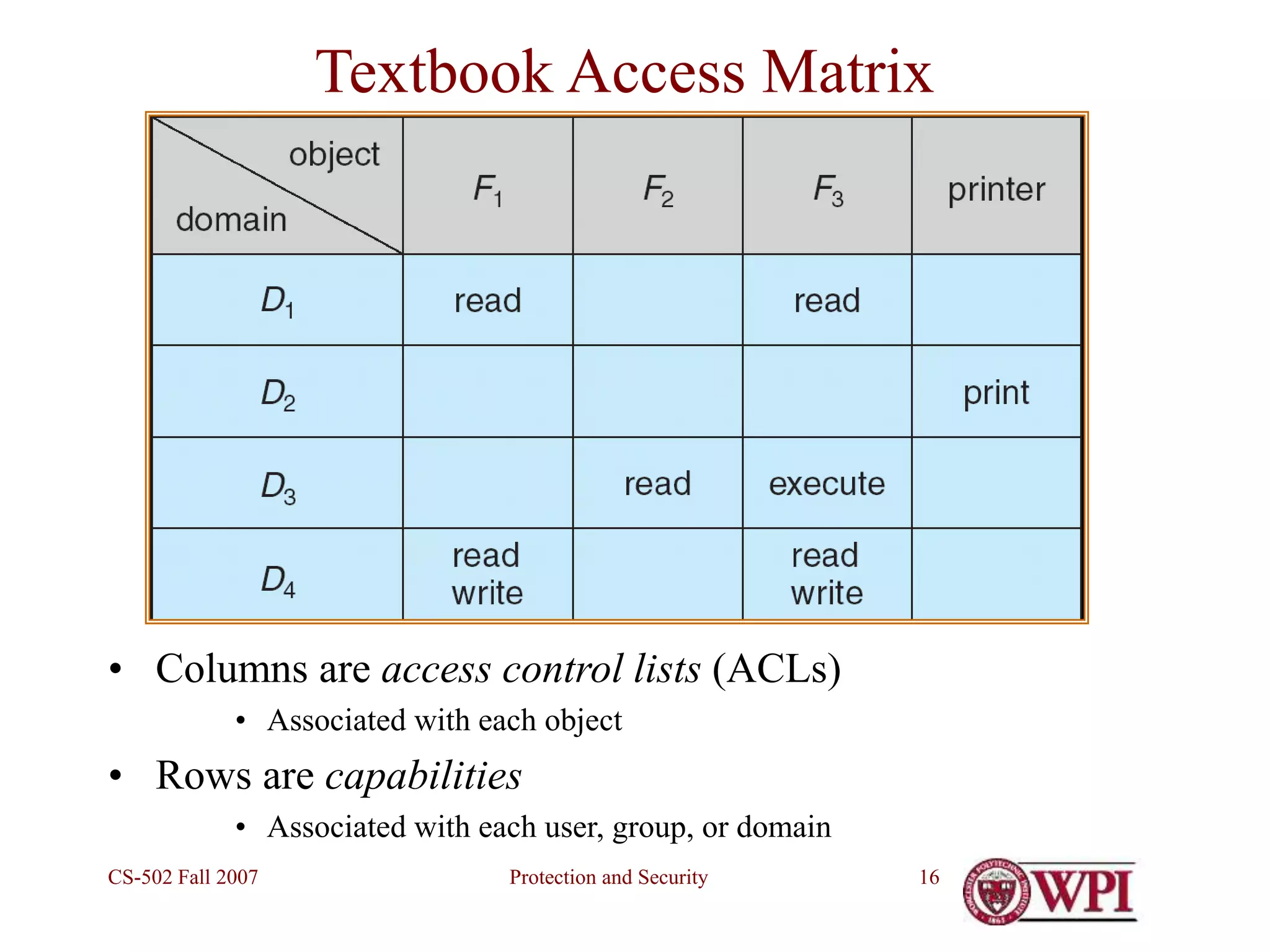
This document discusses protection and security in operating systems. It begins by defining protection as mechanisms within the OS to control access to programs and resources, while security refers to issues external to the OS like authentication. The document then outlines topics on protection mechanisms and security issues. It discusses the first computer virus as an example of how a program can reproduce itself and propagate in a way that is hard to detect. Finally, it covers goals of protection like least privilege and separating policy from mechanism in OS design.
![Protection and Security
CS-502 Fall 2007 6
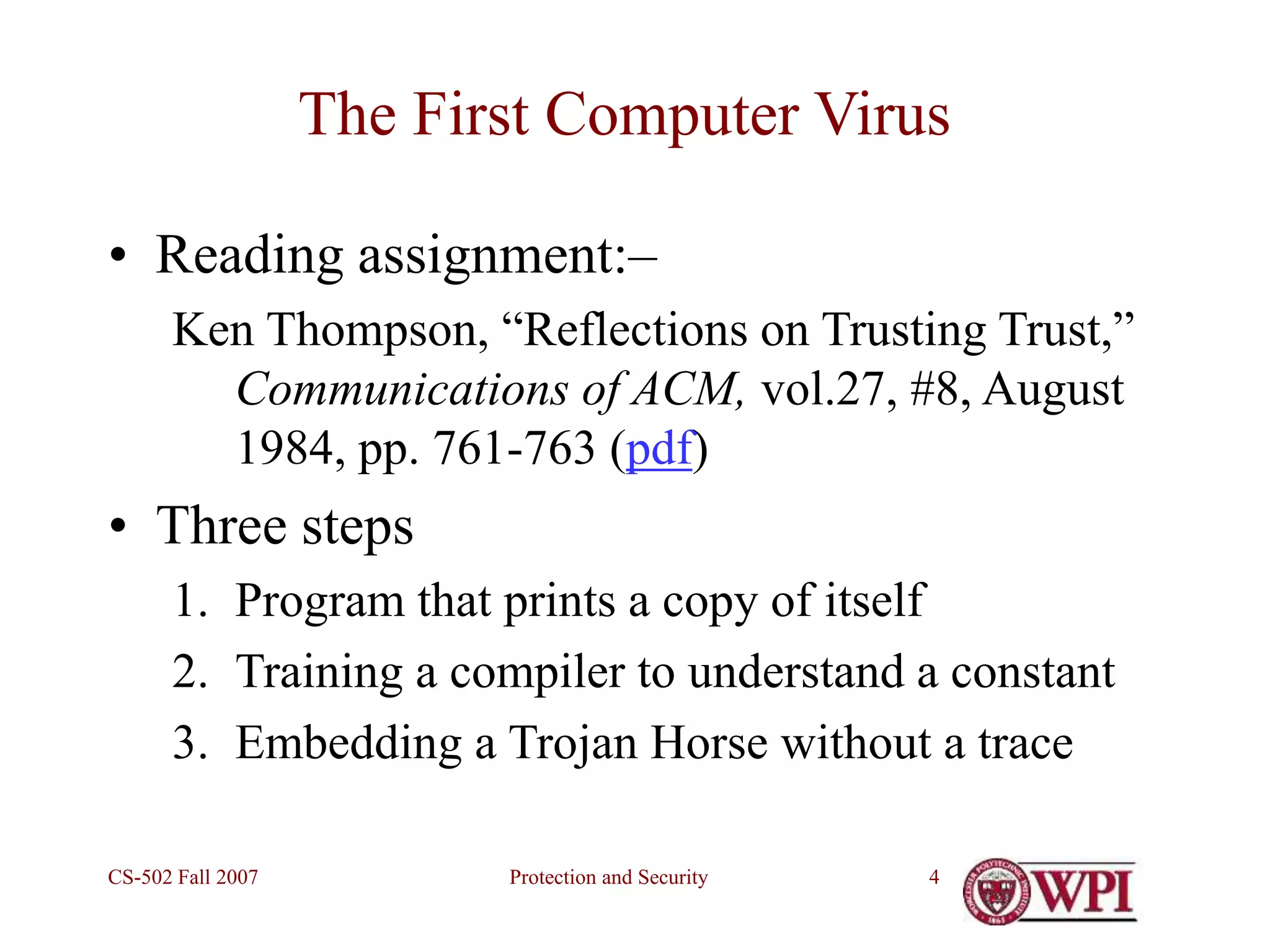
Step 2 – Teaching constant values to compiler
/* reading string constants */
if (s[i++] == '')
if (s[i] == 'n') insert ('n');
elseif (s[i] == 'v') insert ('v');
elseif …
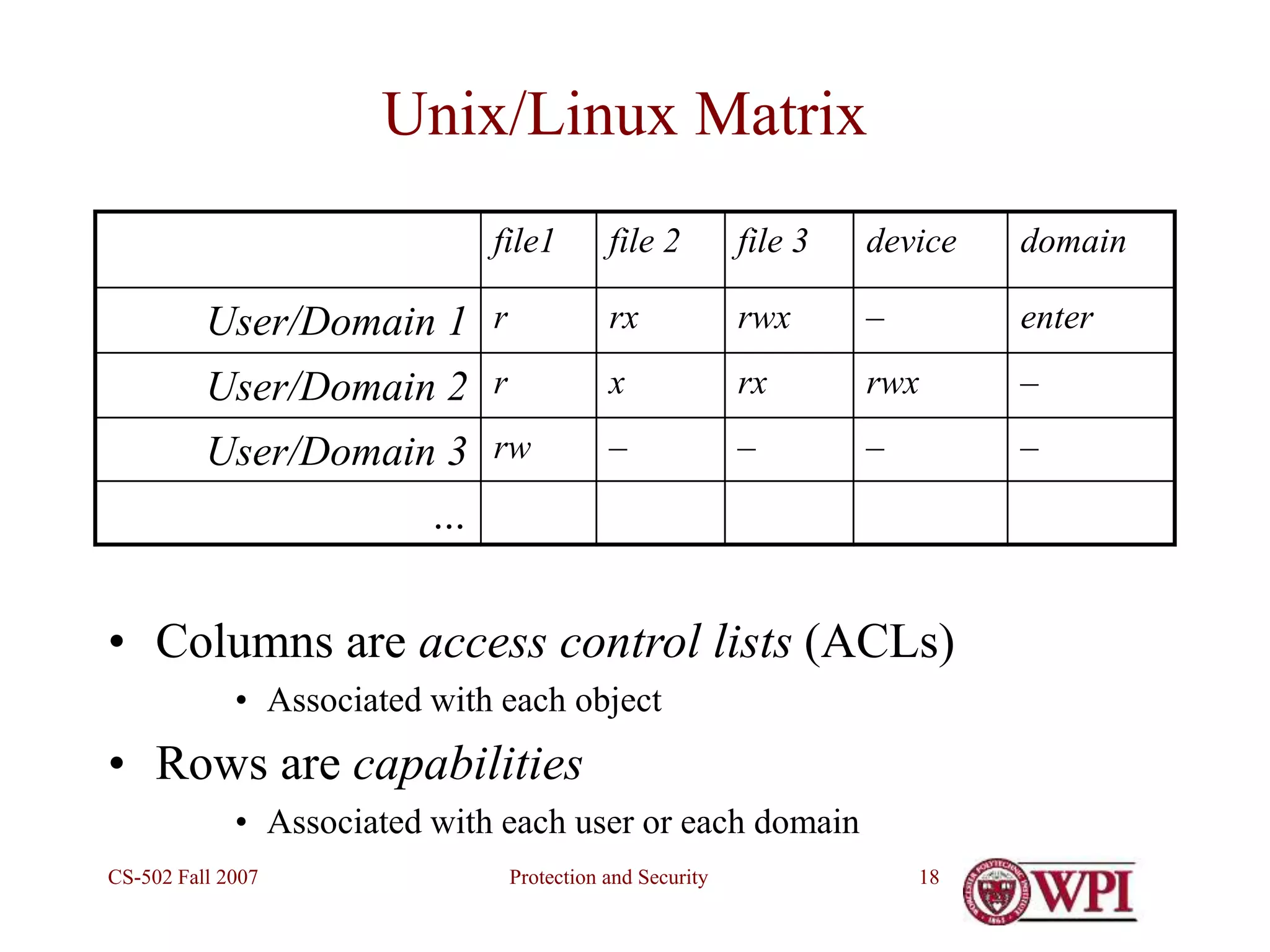
• Question: How does compiler know what integer
values to insert for 'n‘, 'v‘, etc.?](https://image.slidesharecdn.com/week13protectionandsecurity-230418061921-8c4530aa/75/Week-13-Protection-and-Security-ppt-6-2048.jpg)
![Protection and Security
CS-502 Fall 2007 7
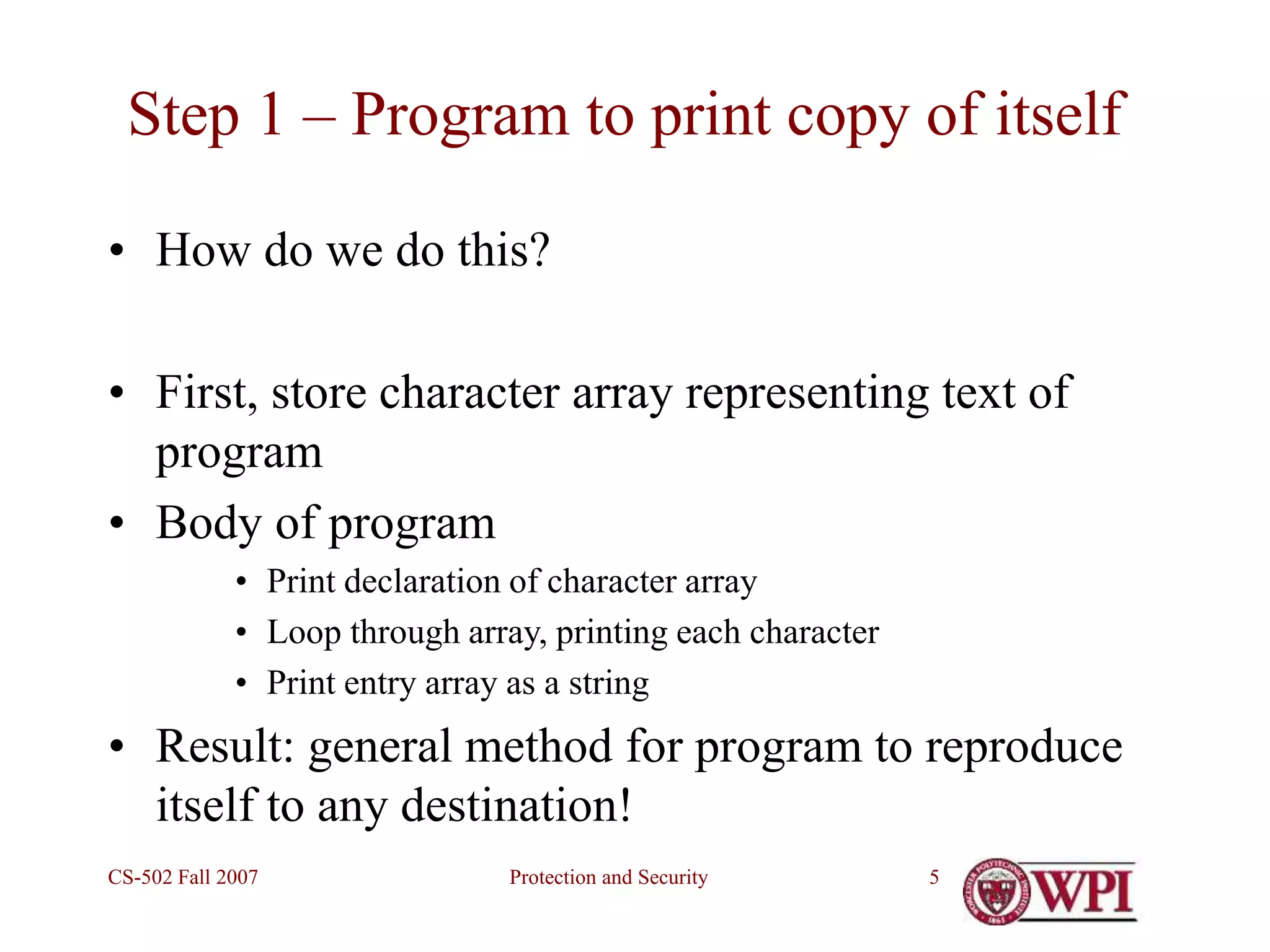
Step 2 (continued)
• Answer: In the first compiler for this machine
type, insert the actual character code
• i.e., 11 (decimal) for ‘v’, etc.
/* reading string constants */
if (s[i++] == '')
if (s[i] == 'n') insert ('n');
elseif (s[i] == 'v') insert (11);
elseif …
• Next: Use the first compiler to compile itself!](https://image.slidesharecdn.com/week13protectionandsecurity-230418061921-8c4530aa/75/Week-13-Protection-and-Security-ppt-7-2048.jpg)