Website hacking, Start basic website hacking, Beginner website hacking practicals, Sql injection, Cross Site Scripting (xss), Denial of Services(ddos), Finding Admin Panel of Websites
•Download as PPSX, PDF•
2 likes•170 views
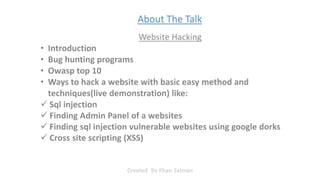
The document discusses various hacking techniques, including using Google dorks to find cross-site scripting vulnerabilities, performing SQL injection attacks to access accounts, finding and exploiting admin panels, conducting cross-site scripting attacks, and launching denial of service attacks. It also mentions bug hunting, the OWASP top 10 security risks, and some of the biggest DDoS attacks of the past decade.
Report
Share
Report
Share
Recommended
Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx

Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptxnull - The Open Security Community
More Related Content
Recently uploaded
Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx

Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptxnull - The Open Security Community
Recently uploaded (20)
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Unlocking the Potential of the Cloud for IBM Power Systems

Unlocking the Potential of the Cloud for IBM Power Systems
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...

"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...
Human Factors of XR: Using Human Factors to Design XR Systems

Human Factors of XR: Using Human Factors to Design XR Systems
"Federated learning: out of reach no matter how close",Oleksandr Lapshyn

"Federated learning: out of reach no matter how close",Oleksandr Lapshyn
New from BookNet Canada for 2024: BNC BiblioShare - Tech Forum 2024

New from BookNet Canada for 2024: BNC BiblioShare - Tech Forum 2024
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx

Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx
Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...

Automating Business Process via MuleSoft Composer | Bangalore MuleSoft Meetup...
Unleash Your Potential - Namagunga Girls Coding Club

Unleash Your Potential - Namagunga Girls Coding Club
Featured
More than Just Lines on a Map: Best Practices for U.S Bike Routes

More than Just Lines on a Map: Best Practices for U.S Bike RoutesProject for Public Spaces & National Center for Biking and Walking
Featured (20)
AI Trends in Creative Operations 2024 by Artwork Flow.pdf

AI Trends in Creative Operations 2024 by Artwork Flow.pdf
Content Methodology: A Best Practices Report (Webinar)

Content Methodology: A Best Practices Report (Webinar)
How to Prepare For a Successful Job Search for 2024

How to Prepare For a Successful Job Search for 2024
Social Media Marketing Trends 2024 // The Global Indie Insights

Social Media Marketing Trends 2024 // The Global Indie Insights
Trends In Paid Search: Navigating The Digital Landscape In 2024

Trends In Paid Search: Navigating The Digital Landscape In 2024
5 Public speaking tips from TED - Visualized summary

5 Public speaking tips from TED - Visualized summary
Google's Just Not That Into You: Understanding Core Updates & Search Intent

Google's Just Not That Into You: Understanding Core Updates & Search Intent
The six step guide to practical project management

The six step guide to practical project management
Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...

Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...
Unlocking the Power of ChatGPT and AI in Testing - A Real-World Look, present...

Unlocking the Power of ChatGPT and AI in Testing - A Real-World Look, present...
More than Just Lines on a Map: Best Practices for U.S Bike Routes

More than Just Lines on a Map: Best Practices for U.S Bike Routes
Website hacking, Start basic website hacking, Beginner website hacking practicals, Sql injection, Cross Site Scripting (xss), Denial of Services(ddos), Finding Admin Panel of Websites
- 1. Created By Khan Salman About The Talk
- 2. Finding (XSS) vulnerable website using google dorks Denial of Service Attack. Created By Khan Salman
- 3. Website? Created By Khan Salman
- 4. Created By Khan Salman Introduction:
- 5. Created By Khan Salman Hacking a website:
- 6. At first time mostly what comes in mind? Created By Khan Salman
- 7. Created By Khan Salman Bug Hunting
- 8. Created By Khan Salman OWASP
- 9. Owasp top 10 Created By Khan Salman
- 10. Created By Khan Salman The Simple SQL Injection Hack
- 11. Created By Khan Salman
- 12. Sql injection demonstration Created By Khan Salman
- 13. We can get access to the account Created By Khan Salman
- 14. Created By Khan Salman
- 15. Created By Khan Salman
- 16. Created By Khan Salman Finding admin panel of websites:
- 17. Created By Khan Salman
- 18. Created By Khan Salman
- 19. Created By Khan Salman Cross site scripting (XSS):
- 20. Created By Khan Salman
- 21. Created By Khan Salman
- 22. Created By Khan Salman
- 23. Created By Khan Salman Denial of service ( DOS attack )
- 24. Created By Khan Salman
- 25. Created By Khan Salman Some of the famous attacks: Reference: https://www.abusix.com/blog/5-biggest-ddos-attacks-of-the-past-decade
- 26. Created By Khan Salman Summary