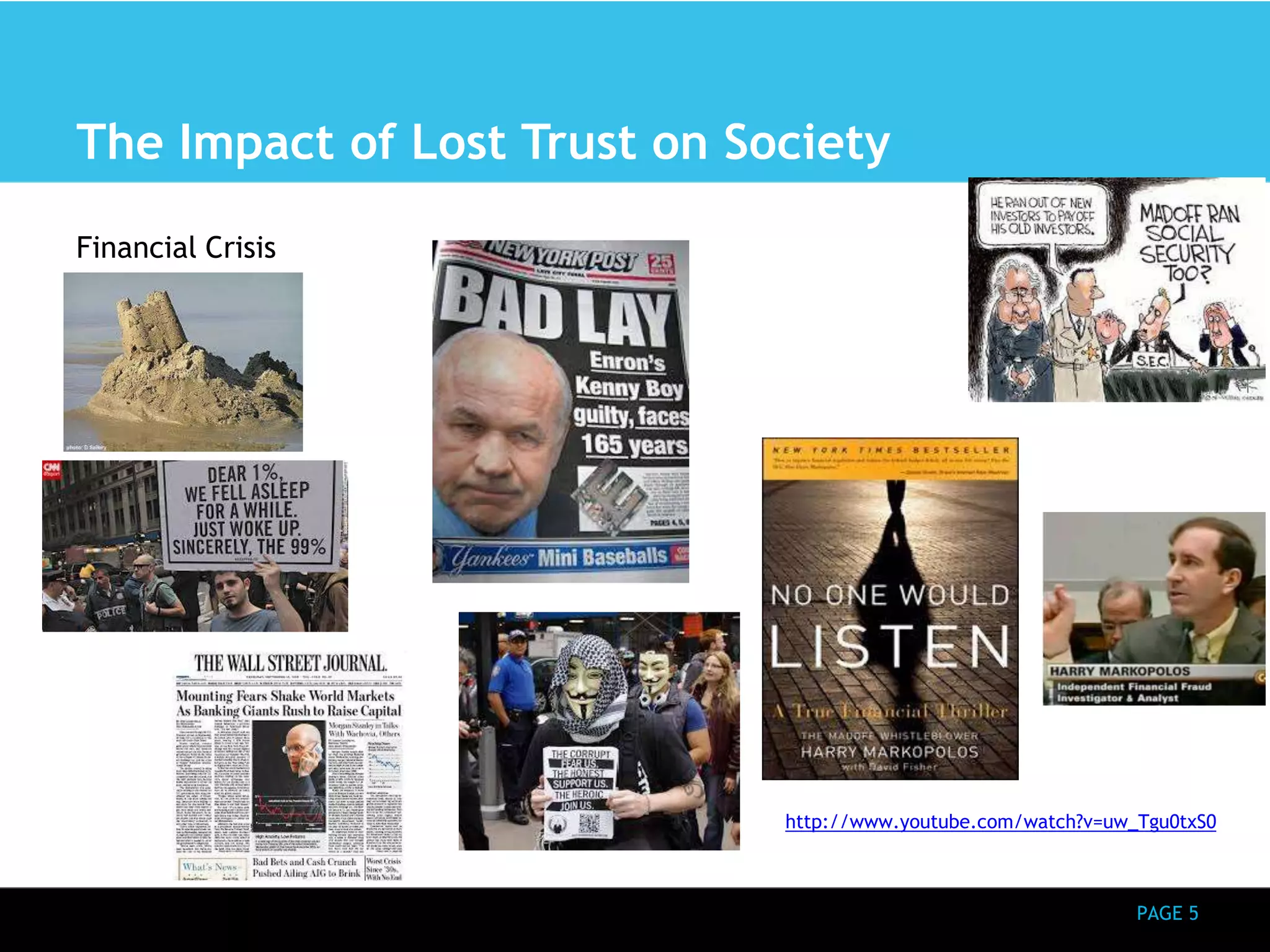
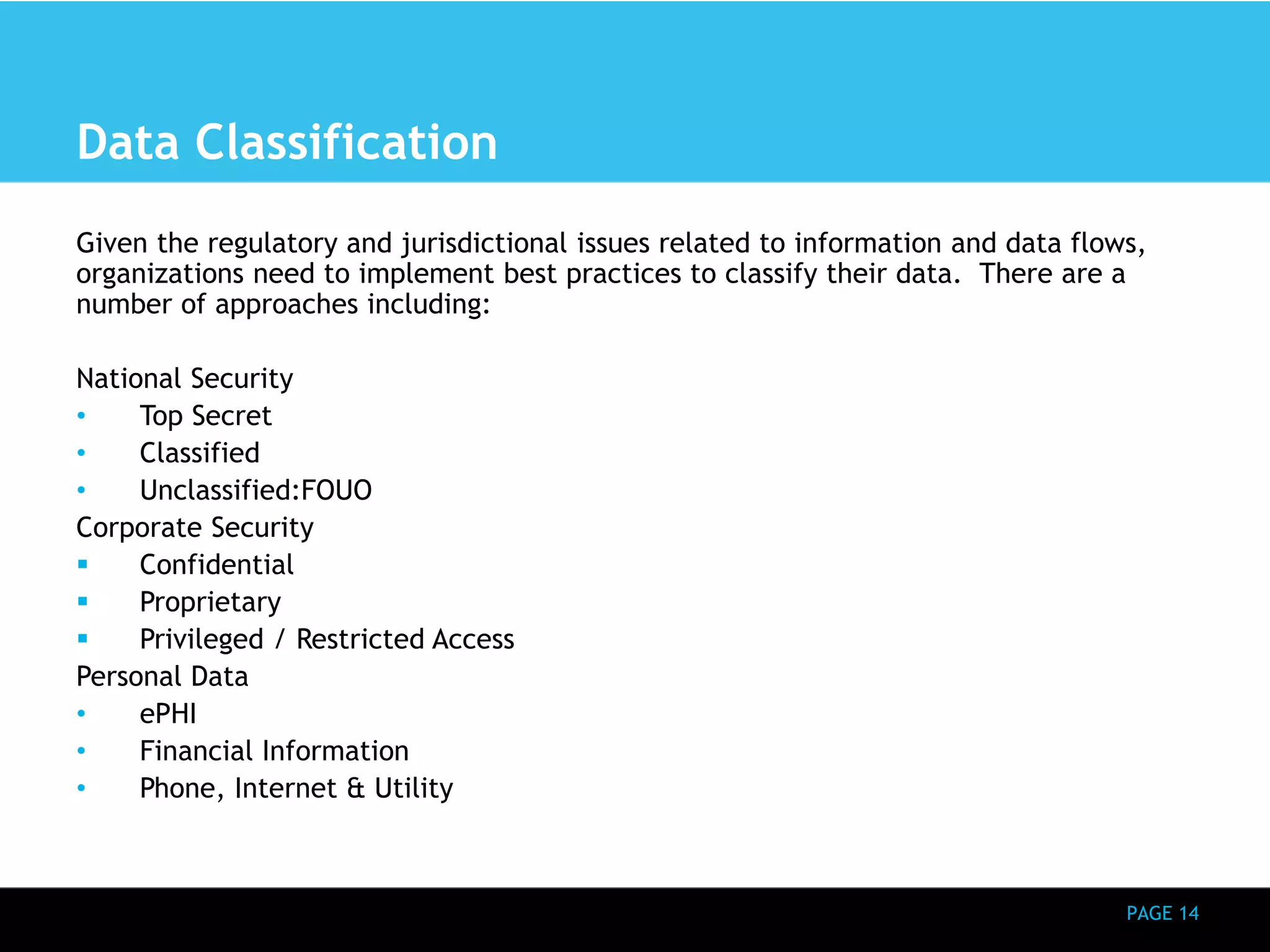
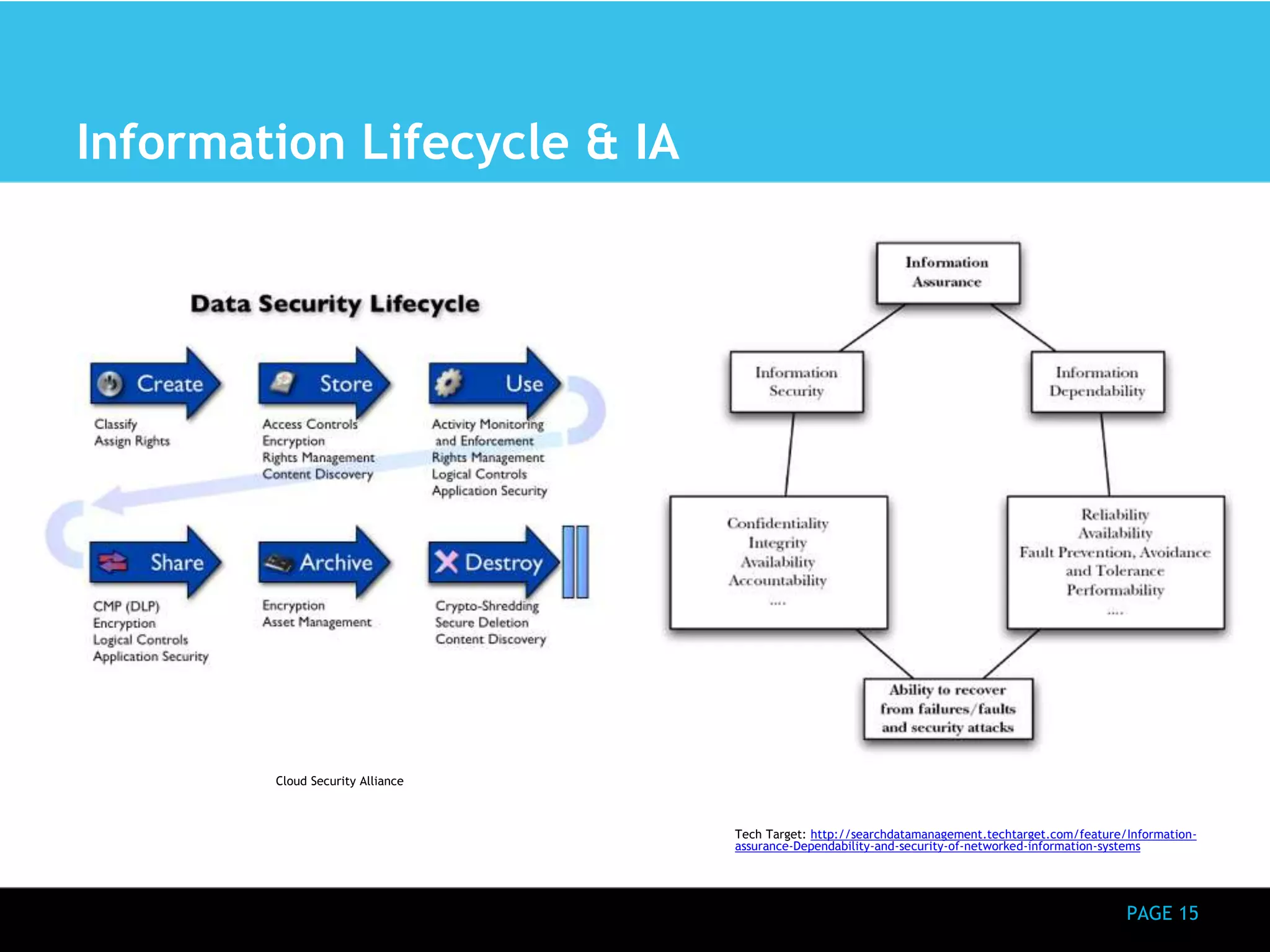
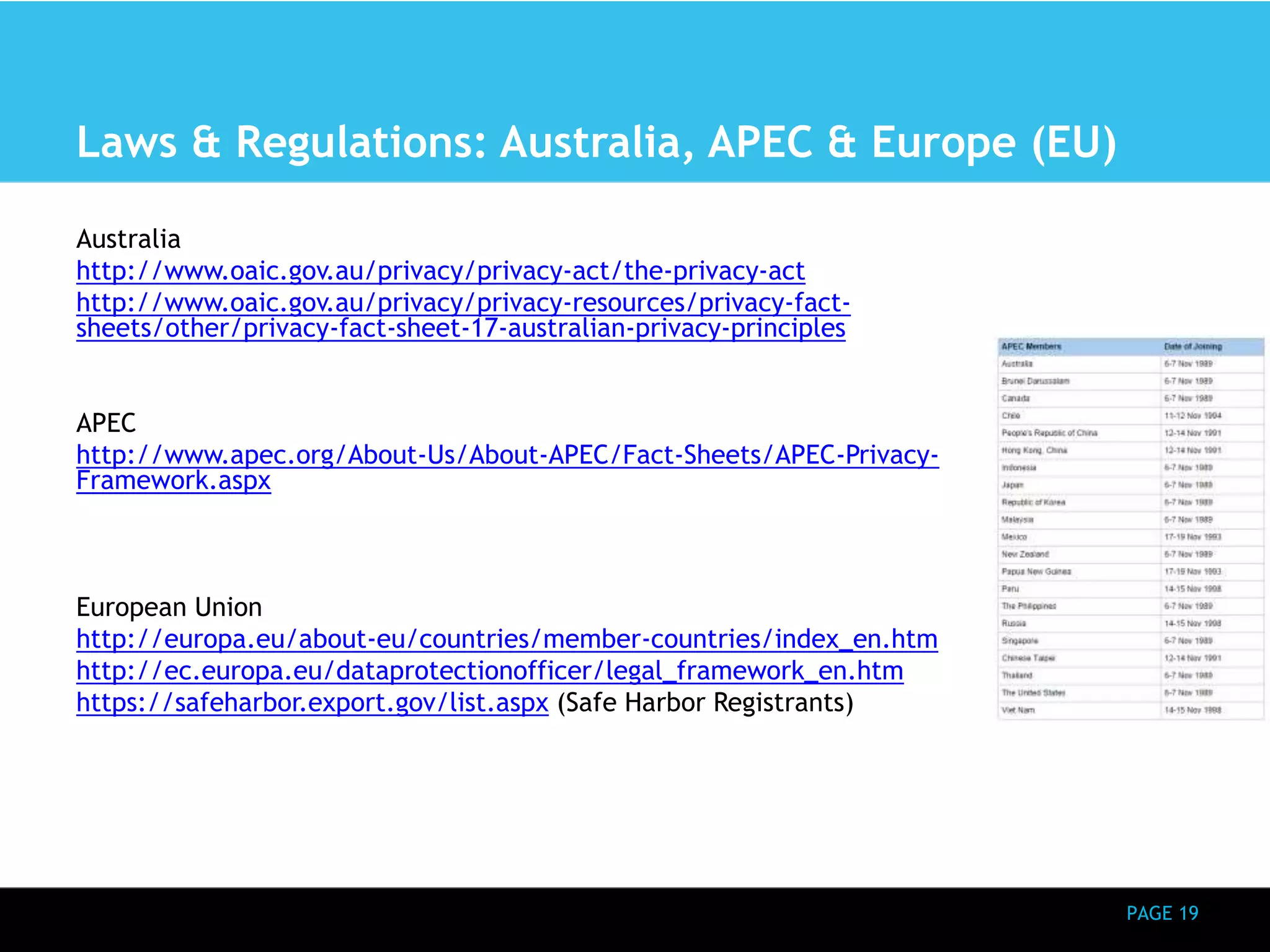
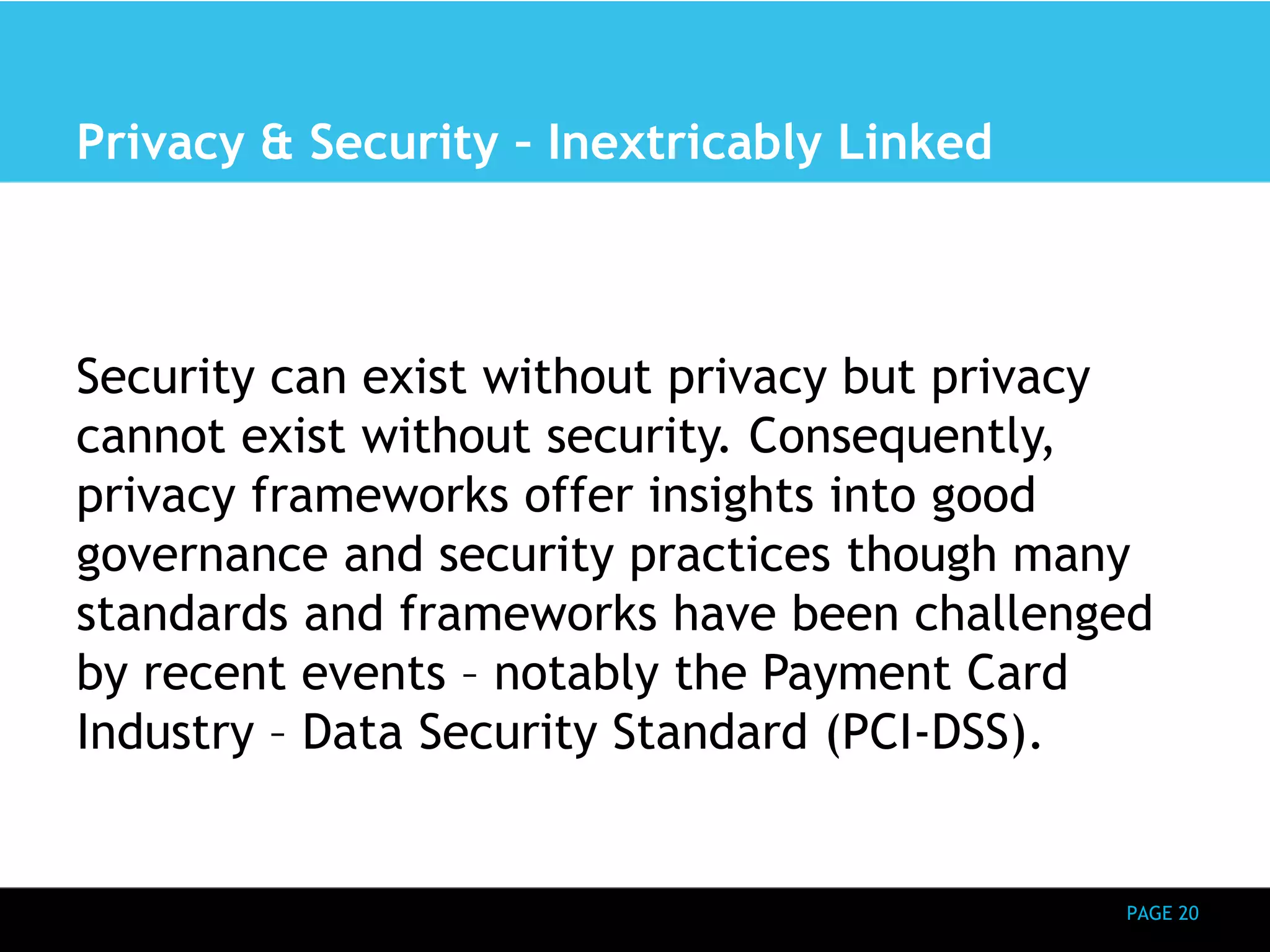
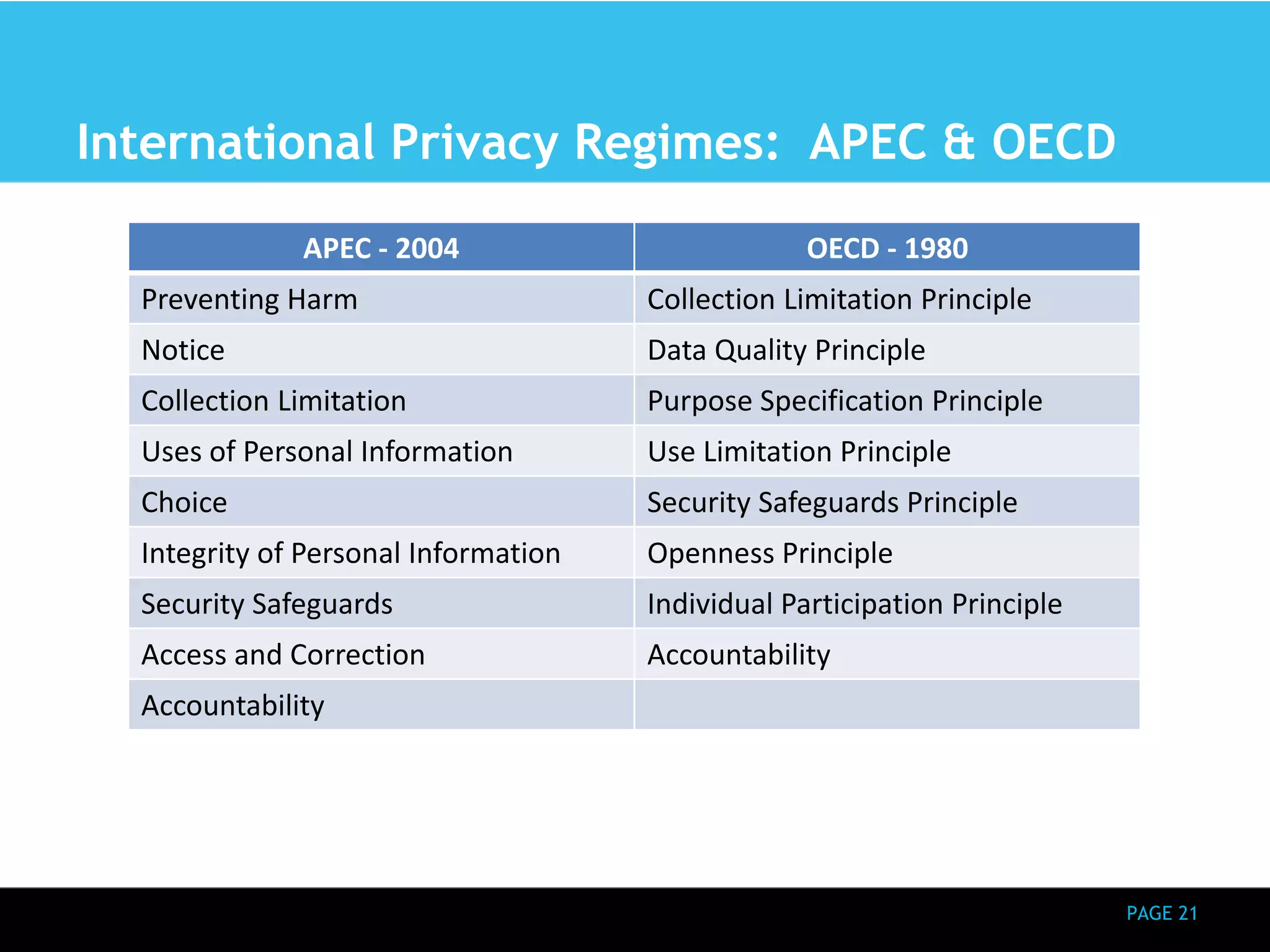
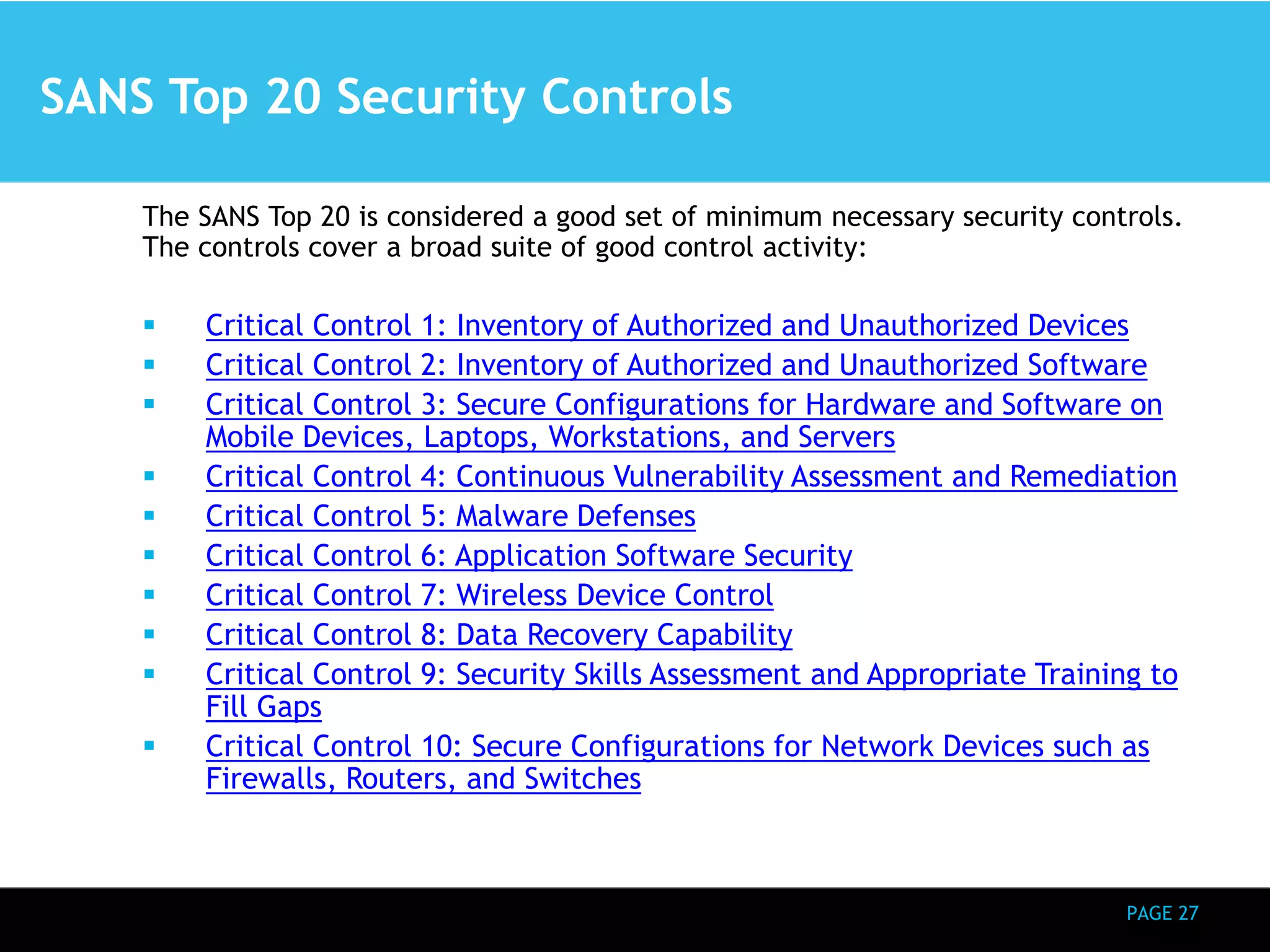
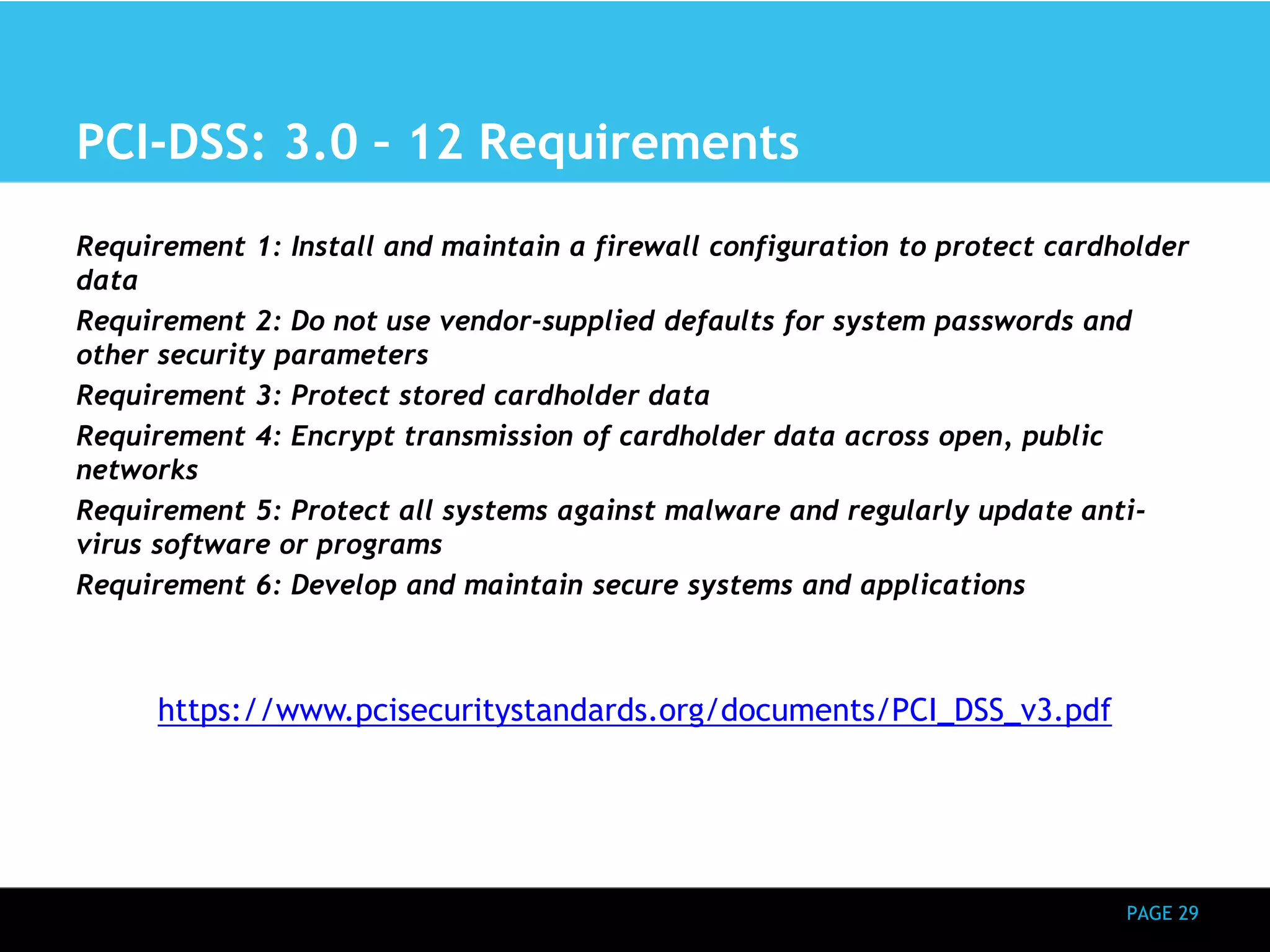
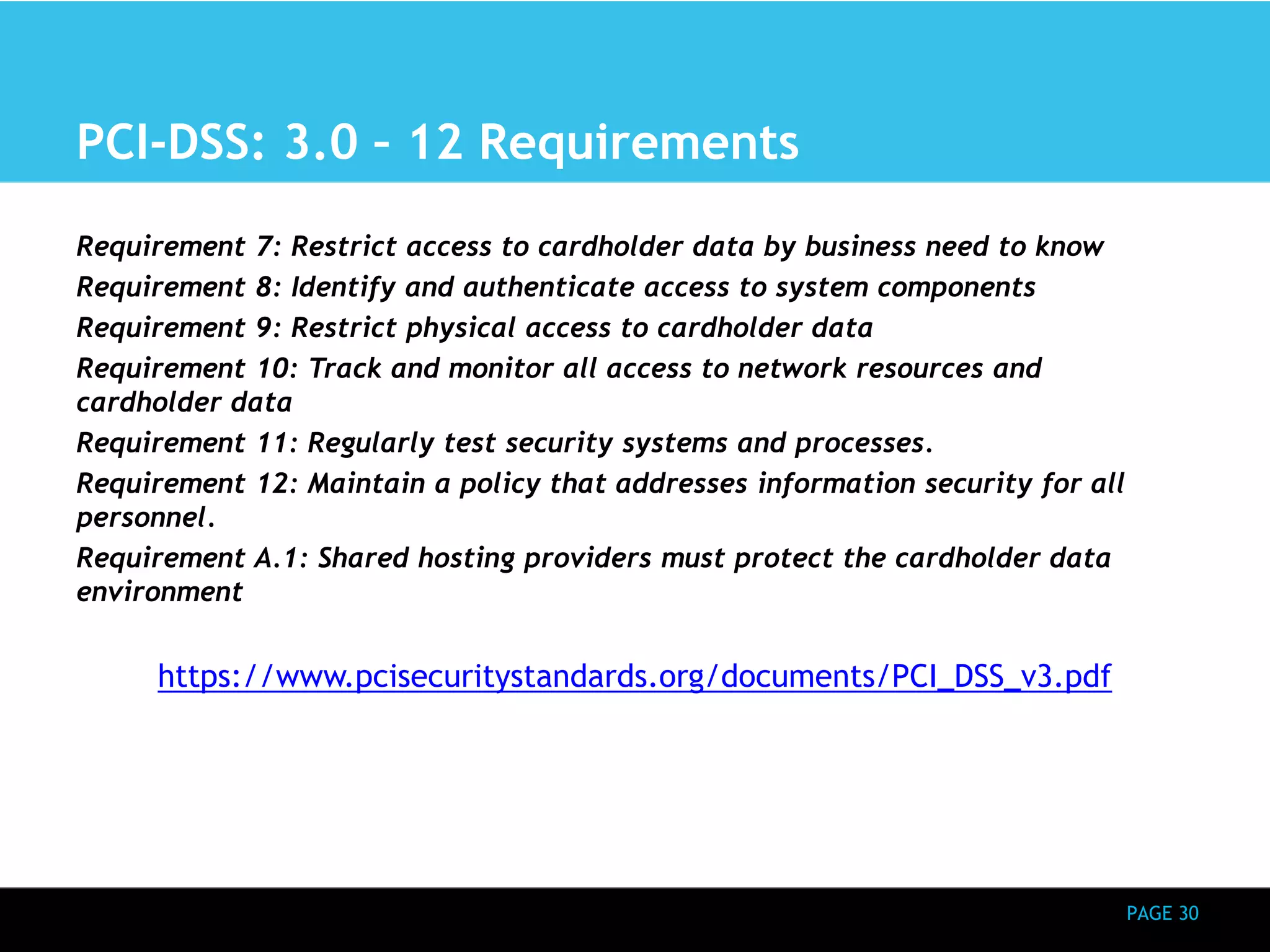
This document provides an overview of a presentation on information assurance in a global context. It discusses why information assurance matters given increasing dependencies on accurate data. It also covers definitions of security, privacy and information assurance. Additionally, it outlines regulatory requirements, frameworks, technologies like IoT and cloud computing, and lessons from cross-border regions. The presentation agenda is included which covers these topics over several pages in more depth.