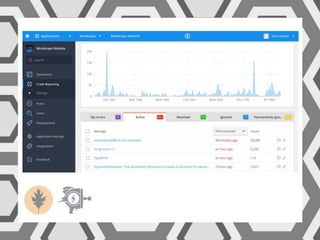
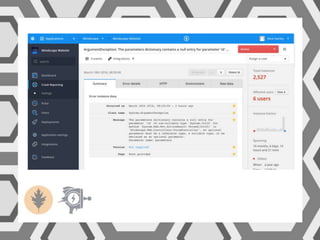
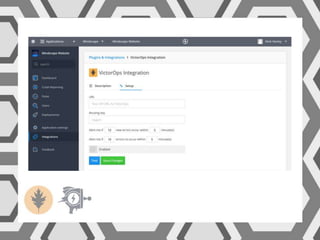
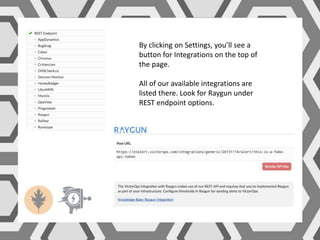
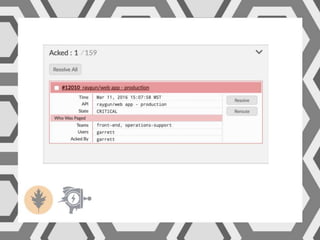
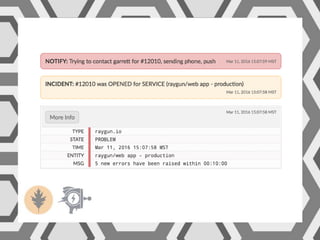
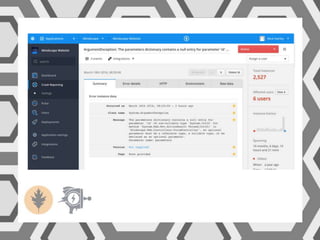
VictorOps assists teams in incident management by streamlining the resolution process from initial alert to final review, helping to resolve issues more quickly. Key features include reducing alert noise, annotating alerts with pertinent information, and routing alerts to appropriate personnel or teams. Users can access integrations such as Raygun through the settings menu on the platform.